|
|
|
|
|
[分享]Beginners Guide to NFS factoring using GGNFS and MSIEVE
CYGWIN下起来真慢啊。。。 |
|
|
[求助]过年了,各位大N和extile来看看这什么算法加密的
为何每次下论坛的有些上传文件时,总是解压不了?以前就碰见好几次了,有些能解压,也要跳出个框。。。。。文件里有情况!? PART1解压后三个文挡有个是:,不知何意?ARSWP在GOOGLE里是清理助手?! [STRING] LanguageCode=1028|3076|4100 LanguageName=Chinese Trad MainCaption=Windows清理助手 ExitAtpSwp=退出 ShowHideMainWnd=顯示/隱藏主窗口 AboutAtpSwp=關於... Version_Content=標準版:%s(%s)-%s(%d.%d)-%d-%d RunPathError=\n不建議在壓縮包(或臨時目錄)中直接運行本程序!\n建議將本程序放置到其他目錄中運行!\n\n要繼續運行本程序麼? SelfVerifyError=\n程序數字簽名驗證失敗,可能是感染了病毒!\n\n要繼續運行本程序麼? NeedAdministratorRights=請以管理員權限運行本程序! NotSupportX64=對不起,請運行本程序的X64版本! NotifyUserBeforeLoadDriver=\n為檢測和徹底清理惡意程序,需加載內核模塊獲取系統控制權.\n\n此操作可能被某些安全類軟件報警,屬正常現象.\n\n如果安全類軟件彈出警告窗口,請選擇'允許'和'信任'即可.\n NotDisableScriptDebugger=\n系統當前未禁用腳本調試,這可能導致本程序運行不穩定.\n\n要恢復到系統默認值後穩定運行麼?\n NeedResetHosts=檢測到HOSTS中arswp域名被劫持,是否重置HOSTS? ResetHostsErrorInfo=重置HOSTS失敗,部分網絡功能將受到嚴重影響! |
|
|
[求助]椭圆曲线数字签名中基点的阶的问题
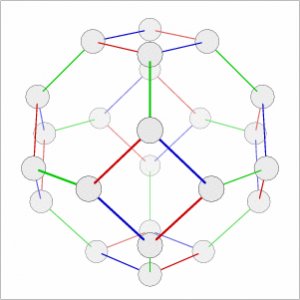
找到两条: y^2=(x^3+28*x+82)MOD113和y^2=(x^3+28*x+31)MOD113还是两曲线同构 [0, 46] [0, 67] [1, 26] [1, 87] [4, 22] [4, 91] [5, 11] [5, 102] [6, 50] [6, 63] [7, 13] [7, 100] [11, 34] [11, 79] [12, 15] [12, 98] [13, 48] [13, 65] [16, 28] [16, 85] [19, 44] [19, 69] [21, 10] [21, 103] [23, 24] [23, 89] [24, 1] [24, 112] [25, 19] [25, 94] [28, 52] [28, 61] [30, 24] [30, 89] [32, 33] [32, 80] [33, 52] [33, 61] [36, 25] [36, 88] [38, 14] [38, 99] [40, 1] [40, 112] [41, 54] [41, 59] [42, 38] [42, 75] [43, 26] [43, 87] [44, 36] [44, 77] [46, 31] [46, 82] [47, 40] [47, 73] [49, 1] [49, 112] [51, 16] [51, 97] [52, 52] [52, 61] [56, 46] [56, 67] [57, 46] [57, 67] [58, 56] [58, 57] [59, 53] [59, 60] [60, 24] [60, 89] [63, 4] [63, 109] [64, 29] [64, 84] [65, 4] [65, 109] [68, 40] [68, 73] [69, 26] [69, 87] [70, 36] [70, 77] [73, 29] [73, 84] [74, 37] [74, 76] [75, 9] [75, 104] [77, 45] [77, 68] [89, 29] [89, 84] [92, 8] [92, 105] [94, 6] [94, 107] [96, 2] [96, 111] [98, 4] [98, 109] [100, 32] [100, 81] [101, 3 9] [101, 74] [102, 5] [102, 108] [111, 40] [111, 73] [112, 36] [112, 77] [0, 12] [0, 101] [1, 25] [1, 88] [2, 35] [2, 78] [11, 38] [11, 75] [12, 20] [12, 93] [13, 28] [13, 85] [15, 53] [15, 60] [17, 30] [17, 83] [19, 23] [19, 90] [21, 7] [21, 106] [24, 17] [24, 96] [36, 3] [36, 110] [38, 22] [38, 91] [39, 10] [39, 103] [40, 17] [40, 96] [43, 25] [43, 88] [44, 51] [44, 62] [45, 35] [45, 78] [48, 53] [48, 60] [49, 17] [49, 96] [50, 53] [50, 60] [53, 21] [53, 92] [54, 4] [54, 109] [55, 49] [55, 64] [56, 12] [56, 101] [57, 12] [57, 101] [61, 11] [61, 102] [62, 14] [62, 99] [ 64, 15] [64, 98] [66, 35] [66, 78] [67, 13] [67, 100] [69, 25] [69, 88] [70, 51] [70, 62] [71, 5] [71, 108] [72, 19] [72, 94] [73, 15] [73, 98] [75, 16] [75, 97] [77, 36] [77, 77] [80, 11] [80, 102] [81, 43] [81, 70] [83, 21] [83, 92] [85, 11] [85, 102] [88, 54] [88, 59] [89, 15] [89, 98] [90, 21] [90, 92] [92, 37] [92, 76] [94, 18] [94, 95] [97, 32] [97, 81] [100, 42] [100, 71] [101, 1] [101, 112] [102, 55] [102, 58] [106, 31] [ 106, 82] [107, 41] [107, 72] [108, 52] [108, 61] [109, 9] [109, 104] [112 , 51] [112, 62] y^2=(x^3+28*x+31)MOD113图:  |
|
|
[讨论]芜湖量子政务网有上过的吗?
去注册了,问问题还要审察。。。。。。。。。上学还是坐牢? http://www.ustc-edu.cn/forumdisplay.php?fid=211 http://www.ustc-edu.cn/my.php?item=threads |
|
|
[讨论]芜湖量子政务网有上过的吗?
GOOGLE.COM 芜湖市科技局、招商局、经贸局、总工会和质监局等市政机关及芜湖市电信大楼8个用户,设置了4个全通主网节点和三个子网用户节点以及1个用于攻击检测的节点,长15公里。 另据了解,中国科大中科院量子信息重点实验室郭光灿研究团队早在2004年即在北京与天津之间实现了世界上最远距离的125公里商用光纤的量子密匙分配,有力地推进了量子密码技术的实用化。2007年,郭光灿研究团队在北京商用光纤上实现了40公里范围内四用户的城域量子通信网络,完成了世界上首个无中转、任意互通的量子密码通信网络,并在国际上首先在实际地下光缆中进行了诱骗态量子密匙分配实验,安全通信距离达到32公里。 http://lqcc.ustc.edu.cn/news/?column=21 城域量子通信网络,可能是局域网吧,实验用的, 量子光学研究组 量子密码与量子器件研究组 冷原子物理研究组 低维光学体系研究组 量子输运与量子计算研究组 表面等离子体与量子传输研究组 介质微腔研究组 量子信息理论研究组 |
|
|
|
|
|
[讨论]有听说旋转明文密码的吗?
群论的反演? For the method I'll be using here, the cleartext should be a square number of letters. For example, one flew over the cuckoo's nest To prevent the cipher from being too easy to crack, you need to change the cleartext in a reversible manner. My method, rotating it, involves writing the cleartext in columns and then reading it in a spiral. Once done, you can add a random letter at every prime numbered space, or some other pattern that's easy to remember and hard to crack. In this example I started from the middle of the left side, and reversed direction for the second loop of the spiral Choose keyword The most important thing to remember is that the keyword is the security of your message. if you choose one that's too short, it can be cracked extremely easily. However, if you choose one that's too long relative to the cleartext, it can get dicey. Usually a keyword of 6-10 letters is decent. For the sake of the demonstration I'll use abcdefghi as the keyword Rotating Cleartext Flaw 1: the rotating cleartext algorithm. There is no such thing. There is an addition to the Vigenère cipher which is called "autokey" and uses the cleartext to expand the key instead of repeating the key. As soon as the key is exhausted it appends the cleartext. But it's breakable too. If you haven't shared the cleartext in advance, you can tack it on the end of the coded message, but for that you have to hide it. you could do the same thing you did with the cleartext in step 2. Give to a friend who knows the protocol and you're finished http://lucumr.pocoo.org/2007/4/19/digital-fortress-stranger-than-fiction/   |
|
|
[讨论]有听说旋转明文密码的吗?
跑书店专门翻了英文版,是rotating-cleartext ,发现英文版星际争霸五本和DABLO8本,魔獣7本,每本都66块 GOOGLE。COM: http://www.instructables.com/id/Vigenere-cipher-with-rotating-cleartext/ Dan Brown - Digital Fortress book Andre Amorim decouk at gmail.com Wed Jan 14 17:12:07 CET 2009 Previous message: Dan Brown - Digital Fortress book Next message: Dan Brown - Digital Fortress book Messages sorted by: [ date ] [ thread ] [ subject ] [ author ] -------------------------------------------------------------------------------- >concept of rotating-cleartext ever existed.[1] >Charly Avital Thanks Charly Avital for explanations. I know, I'd had read his others books firstly... and yes... I read like Dan as who is reading comics books, no worrys. The thing that really catch my attention was the concept of rotating-cleartext thing. But I think the book is good in the sense that it's encourage those who are not expert in the subject to know more about. Thats why I'm here asking. [s] -AA 2009/1/14 Charly Avital <shavital at mac.com>: > Andre Amorim wrote the following on 1/14/09 9:49 AM: >> Hi all, >> >> Anyone knows what's is fact (real) and what is fiction in Dan Brown >> novel, Digital Fortress ? >> >> Kind Regards, >> [s] > > > I read it years ago. I believe it's the worst book ever written by Dan > Brown. > > Some excerpts from: <http://en.wikipedia.org/wiki/Digital_Fortress>. I > believe the following list of Mr. Brown's errors (or delusions) is not > exclusive, to say the least. > > Still, it's my opinion, only. > > Charly > > ---------- > "Although the book's website cites reviews lauding Digital Fortress for > being extremely realistic, the book contains a number of technical > errors and misunderstandings in computers, math and technology. > > * Brown mentions a Hungarian mathematician, Josef Harne, who in 1987 > proposed an encryption algorithm that, in addition to encrypting, > shifted decrypted cleartext over a time variant. However, neither Harne > nor the concept of rotating-cleartext ever existed.[1] > * Brown says the atomic bomb dropped on Nagasaki was fueled by the > uranium isotope U-238. The Fat Man bomb dropped on Nagasaki was fueled > by plutonium 239, and U-238 is not an easily fissionable isotope of > uranium (needing a fusion reaction to initiate fission in the U-238). > * Brown also inaccurately portrays the leadership of the NSA. As > part of the Department of Defense, the NSA director - by law - must be a > three-star Lieutenant General or Vice Admiral. > * Brown confuses bits with bytes, describing a 64bit string as > containing 64 alphanumeric characters. In fact it would be just 8 > assuming the most basic 8bit character encoding, each character being a > byte or 8 bits. > * Brown suggests that TRANSLTR, a machine capable of breaking a > 64bit key in 10 minutes would take just an hour to break a 10,000 bit > key. This is a gross misunderstanding of the relationship between key > lengths and the time required to brute force them. Such a machine would > take over 80,000 years to break a 96-bit key and over 350,000 billion > years (nearly 30,000 times the current age of the universe) to break a > 128-bit key. The number of years it would take to break a 10,000 bit key > isn't even practical to write down - it has 2,987 digits. > * Brown repeatedly confuses storage or processing of data with > execution. For example, TRANSLTR is threatened because it has tried to > crack Digital Fortress, which is actually a virus, and the database is > similarly threatened because Digital Fortress is sent to it by TRANSLTR. > Databases and password crackers do not execute the information presented > to them, so it wouldn't matter that Digital Fortress contains harmful > instructions. > * Characters who are supposedly experts in cryptography seem to > think there is no such thing as an unbreakable encryption scheme. See > one-time pad." > ---------- > -- Andre Amorim GnuPG KEY ID: 0x587B1970 FingerPrint: 42AE C929 4D91 4591 4E75 430F 78D9 53B4 587B 1970 Download: http://pgp.mit.edu:11371/pks/lookup?op=get&search=0x587B1970 -------------------------------------------------------------------------------- Previous message: Dan Brown - Digital Fortress book Next message: Dan Brown - Digital Fortress book Messages sorted by: [ date ] [ thread ] [ subject ] [ author ] -------------------------------------------------------------------------------- More information about the Gnupg-users mailing list |
|
|
[求助]椭圆曲线数字签名中基点的阶的问题
b 0----20的也传在这,没113的 找到两小点的: Y^2=x^3+3x+6mod13 [1, 6] [1, 7] [3, 4] [3, 9] [4, 2] [4, 11] [5, 4] [5, 9] [8, 3] [8, 10] [10, 3] [10, 10] {1, {1, 6}, 2, {8, 10}, 3, {3, 4}, 4, {10, 3}, 5, {5, 4}, 6, {4, 2}, 7, {4, 11}, 8, {5, 9}, 9, {10, 10}, 10, {3, 9}, 11, { 8, 3}, 12, {1, 7}, 13, {infinity, infinity} 用Y^2=X^3+5MOD37 [6, 6] [6, 31] [8, 6] [8, 31] [11, 2] [11, 35] [14, 14] [14, 23] [17, 16] [17, 21] [18, 18] [18, 19] [21, 4] [21, 33] [22, 16] [22, 21] [23, 6] [23, 31] [24, 18] [24, 19] [25, 4] [25, 33] [27, 2] [27, 35] [28, 4] [28, 33] [29, 14] [29, 23] [31, 14] [31, 23] [32, 18] [32, 19] [35, 16] [35, 21] [36, 2] [36, 35] {1, {6, 6}, 2, {32, 19}, 3, {27, 2}, 4, {11, 2}, 5, {31, 14}, 6, {21, 4}, 7, {36, 35}, 8, {25, 4}, 9, {22, 21}, 10, {8, 6}, 11, {23, 31}, 12, {35, 21}, 13, {29, 14}, 14, {28, 33}, 15, {24, 19}, 16, {17, 21}, 17, {18, 18}, 18, {14, 23}, 19, {14, 14}, 20, {18, 19}, 21, {17, 16}, 22, {24, 18}, 23, {28, 4}, 24, {29, 23}, 25, {35, 16}, 26, {23, 6}, 27, {8, 31}, 28, {22, 16}, 29, {25, 33}, 30, {36, 2}, 31, {21, 33}, 32, {31, 23}, 33, {11, 35}, 34, {27, 35}, 35, {32, 18}, 36, {6, 31}, 37, {infinity, infinity} |
|
|
[求助]椭圆曲线数字签名中基点的阶的问题
仔细看了看书,|F|=如果等于点阶,会被同构攻击,不过等于点阶的的CURVE 不多,用p=113试了下面,好象都是偶数点阶,哪天找到=113的,将建同构试下 Y^2=X^3+31x+b0MOD113 从左往右,b=82,83..........90 每列等于该b的|F|,都是偶数 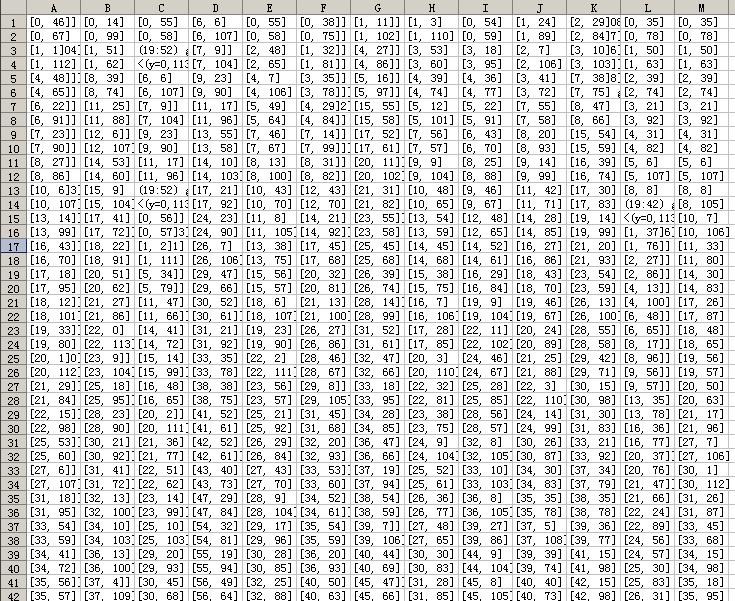   |
|
|
|
|
|
[分享]s3/s4群表
http://sourceforge.net/apps/trac/groupexplorer/wiki/The%20First%20Five%20Symmetric%20Groups http://www.gap-system.org/Download/WinInst.html |
|
|
|
|
|
|
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值