|
|
[推荐]推荐PARI和SAGE和MXGMA
环论符号: Symbol Description Category -------------------------------------------------- Z ring of integers RngInt Z/mZ ring of residue classes RngRes R[x] univariate poly. ring RngUPol F[x]/f(x) univ. poly. factor ring RngUPolRes R[x_1,...,x_m] multivariate poly. ring RngMPol R[[x]] power series ring RngSer O order in a number field RngOrd \Z_p p-adic ring RngPad R_m local ring RngLoc V valuation ring RngVal -------------------------------------------------- Q rational field FldRat F_q finite field FldFin F(x_1,...,x_m) rational function field FldFun F((x)) field of Laurent series FldPow Q(sqrt(D)) quadratic number field FldQuad Q(zeta_n) cyclotomic number field FldCyc Q(alpha) number field FldNum Q_p p-adic field FldPad Q_p(alpha) local field FldLoc R real field FldRe C complex field FldCom 整环里一个元素的环平凡环,单位环,零环,16进制可用elt Z := IntegerRing(); n := 12345678901111; n in Z; Q:=IntegerRing(); n1 := 12345678901111.111; n1 in Z; n1 in Q; R:= RingOfIntegers(); n1 in R; n1 in R; One(Z); Identity(Z) ; Zero(Z) ; Representative(Z); One(Q); Identity(Q) ; Zero(Q) ; Representative(Q); m := elt< Z | 12453 >; m; n:=elt< Z|0x12453 >; n; true false false false false 1 1 0 0 1 1 0 0 12453 74835 求环特征,判段整环到域之间的各种环:整环-欧式环,主理想环交换除环(体),非交换除环,赋值环,域 Z := IntegerRing(); n := 12345678901111; n in Z; Q:=IntegerRing(); n1 := 12345678901111.111; n1 in Z; n1 in Q; R:= RingOfIntegers(); n1 in R; n1 in R; One(Z); Identity(Z) ; Zero(Z) ; Representative(Z); One(Q); Identity(Q) ; Zero(Q) ; Representative(Q); m := elt< Z | 12453 >; m1 := elt< Z |74835 >; m; m1; n:=elt< Z|0x12453 >; n; m eq n; m1 eq n; n:Hex; k:=Eltseq(n); k; c:=Characteristic(Z); c; IsCommutative(Z) : RngInt -> BoolElt IsUnitary(Z) : RngInt -> BoolElt IsFinite(Z) : RngInt -> BoolElt IsOrdered(Z) : RngInt -> BoolElt IsField(Z) : RngInt -> BoolElt IsEuclideanDomain(Z) : RngInt -> BoolElt IsPID(Z) : RngInt -> BoolElt IsUFD(Z) : RngInt -> BoolElt IsDivisionRing(Z) : RngInt -> BoolElt IsEuclideanRing(Z) : RngInt -> BoolElt IsPrincipalIdealRing(Z) : RngInt -> BoolElt IsDomain(Z) : RngInt -> BoolElt 元素操作,环半直,积和环直积,和,在整数整环和整数域(非零)四则运算一样,高斯整环和复域四则运算一样,多项式环和在有理域四则运算一样,在模素数整数域和模素多项式域就不同了 + n : RngIntElt -> RngIntElt - n : RngIntElt -> RngIntElt m + n : RngIntElt, RngIntElt -> RngIntElt m - n : RngIntElt, RngIntElt -> RngIntElt m * n : RngIntElt, RngIntElt -> RngIntElt n ^ k : RngIntElt, RngIntElt -> RngIntElt m / n : RngIntElt, RngIntElt -> RngIntElt m +:= n : RngIntElt, RngIntElt -> RngIntElt m -:= n : RngIntElt, RngIntElt -> RngIntElt m *:= n : RngIntElt, RngIntElt -> RngIntElt m /:= n : RngIntElt, RngIntElt -> RngIntElt m ^:= k : RngIntElt, RngIntElt -> RngIntElt n div:= m : RngIntElt, RngIntElt -> RngIntElt n mod:= m : RngIntElt, RngIntElt -> RngIntElt n div m : RngIntElt, RngIntElt -> RngIntElt 环元素特征判断: IsZero(n); IsOne(n) ; IsMinusOne(n); IsNilpotent(n); IsIdempotent(n) ; IsUnit(n) ; IsZeroDivisor(n); IsRegular(n) ; IsIrreducible(n); IsPrime(n) ; IsEven(n) ; 0 true 87288 false false false false false false false true false false false 求共扼,在整数整环和四则运算一样,高斯整环和多项式环就看出不同了 Conjugate(-n) ; Conjugate(n); Conjugate(n) 0 -74835 74835 :3:常用数论函数在MAGMA中归类到整数整环里了:像求整函数 Truncate(n1) =12345678901111 AbsoluteValue(n) : RngIntElt -> RngIntElt Abs(n) : RngIntElt -> RngIntElt Absolute value of the integer n. Ilog2(n) : RngIntElt -> RngIntElt The integral part of the logarithm to the base two of the positive integer n. Ilog(b, n) : RngIntElt, RngIntElt -> RngIntElt The integral part of the logarithm to the base b of the positive integer n i.e., the largest integer k such that bk ≤n. The integer b must be greater than or equal to two. Quotrem(m, n) : RngIntElt, RngIntElt -> RngIntElt, RngIntElt Returns both the quotient q and remainder r obtained upon dividing the integer m by the integer n, that is, m = q.n + r, where 0 ≤r < n if n>0 and n<r≤0 if n<0. Valuation(x, p) : RngIntElt, RngIntElt -> RngIntElt, RngIntElt The valuation of the integer x at the prime p. This is the largest integer v for which pv divides x. If x = 0 then v = ∞. The optional second return value is the integer u such that x = pv u. Iroot(a, n) : RngIntElt, RngIntElt -> RngIntElt Given a positive integer a, return the integer b= ⌊root n of a⌋, i.e. the integral part of the n-th root of a. To obtain the actual root (as a real number), a must e coerced into a real field and the function Root applied. Sign(n) : RngIntElt -> RngIntElt Returns -1, 0 or 1 depending upon whether the integer n is negative, zero or positive, respectively. Ceiling(n) : RngIntElt -> RngIntElt The ceiling of the integer n, that is, n itself. Floor(n) : RngIntElt -> RngIntElt The floor of the integer n, that is, n itself. Round(n) : RngIntElt -> RngIntElt This function rounds the integer n to itself. Truncate(n) : RngIntElt -> RngIntElt This function returns the integer truncation of the integer n, that is, n itself. SquarefreeFactorization(n) : RngIntElt -> RngIntElt, RngIntElt Given a non-negative integer n, return a squarefree integer x as well as a positive integer y, such that n=xy2. Isqrt(n) : RngIntElt -> RngIntElt Lcm(s, t) : RngIntEltFact, RngIntEltFact -> RngIntEltFact Gcd(s, t) : RngIntEltFact, RngIntEltFact -> RngIntEltFact SquarefreeFactorization(f) : RngIntEltFact -> RngIntEltFact, RngIntEltFact MoebiusMu(f) : RngIntEltFact -> RngIntElt Divisors(f) : RngIntEltFact -> SeqEnum PrimeDivisors(f) : RngIntEltFact -> SeqEnum NumberOfDivisors(f) : RngIntEltFact -> RngIntElt SumOfDivisors(f) : RngIntEltFact -> RngIntElt IsOne(s) : RngIntEltFact -> BoolElt IsOdd(s) : RngIntEltFact -> BoolElt IsEven(s) : RngIntEltFact -> BoolElt IsUnit(s) : RngIntEltFact -> BoolElt IsPrime(s) : RngIntEltFact -> BoolElt IsPrimePower(s) : RngIntEltFact -> BoolElt IsSquare(s) : RngIntEltFact -> BoolElt IsSquarefree(s) : RngIntEltFact -> BoolElt Modexp(n, k, m) : RngIntElt, RngIntElt, RngIntElt -> RngIntElt The modular power nk mod m, where n is an integer, k is an integer and m is an integer greater than one. If k is negative, n must have an inverse i modulo m, and the result is then i - k mod m. The result is always an integer r with 0≤r< m. n mod m : RngIntElt, RngIntElt -> RngIntElt Remainder upon dividing the integer n by the integer m. The result always has the same sign as m. An error results if m is zero. Modinv(n, m) : RngIntElt, RngIntElt -> RngIntElt InverseMod(n, m) : RngIntElt, RngIntElt -> RngIntElt Given an integer n and a positive integer m, such that n and m are coprime, return an inverse u of n modulo m, that is, return an integer 1≤u<m such that u.n = 1 mod m. Modsqrt(n, m) : RngIntElt, RngIntElt -> BoolElt, RngIntElt Given an integer n and an integer m ≥2, this function returns an integer b such that 0 ≤b < m and b2 = n mod m if such b exists; an error results if no such root exists. Modorder(n, m) : RngIntElt, RngIntElt -> RngIntElt For integers n and m, m > 1, the function returns the least integer k ≥1 such that nk = 1 mod m, or zero if gcd(n, m) != 1. IsPrimitive(n, m) : RngIntElt, RngIntElt -> BoolElt Returns true if n is a primitive root for m, false otherwise (0 < n < m). PrimitiveRoot(m) : RngIntElt -> RngIntElt Given an integer m > 1, this function returns an integer value defined as follows: If Z/mZ has a primitive root and the function is successful in finding it, the root a is returned. If Z/mZ has a primitive root but the algorithm does not succeed in finding it, or Z/mZ does not possess a primitive root, then zero is returned. The Solution of Modular Equations The functions described here can be used if an occasional modular operation is required; the results are integers again. For more extensive modular arithmetic it is preferable to convert to residue class ring arithmetic. See section Residue Class Rings for details. Solution(a, b, m) : RngIntElt, RngIntElt, RngIntElt -> RngIntElt, RngIntElt If a solution exists to the linear congruence ax = b mod m, then returns x0, k such that x = x0 + i * k represents the complete set of solutions, where i can be any integer. Otherwise, returns -1. ChineseRemainderTheorem(X, N) : [RngIntElt], [RngIntElt] -> RngIntElt CRT(X, N) : [RngIntElt], [RngIntElt] -> RngIntElt Apply the Chinese Remainder Theorem to the integer sequences X and N. The sequences must have the same length, k say. The function returns the unique integer x in the range 0 ≤x < LCM(N[1].... .N[k]) such that x = X[i] mod N[i]. The elements of N must all be positive integers greater than one. If there is no solution, then -1 is returned. Solution(A, B, N) : [RngIntElt], [RngIntElt],[RngIntElt] -> RngIntElt Return a solution x to the system of simultaneous linear congruences defined by the integer sequences A, B and N. Each of these sequences must have the same number of terms, k say. The elements of N must all be positive integers greater than one. The i-th congruence is A[i] .x = B[i] mod N[i]. The solution x will satisfy 0 ≤x < LCM(N[1].... .N[k]). If no solution exists, -1 is returned. NormEquation(d, m) : RngIntElt, RngIntElt -> BoolElt, RngIntElt, RngIntElt NormEquation(d, m: parameters)) : RngIntElt, RngIntElt -> BoolElt, RngIntElt, RngIntElt Factorization: [<RngIntElt, RngIntElt>] Default: [ ]Given a positive integer d and a non-negative integer m, return true and two non-negative integers x and y, such that x2 + y2d = m, if such a solution exists. If such a solution does not exists only the value false is returned. If the factorization of m is known, it may be supplied as the value of the parameter Factorization to speed up the computation. Truncate(n1) 12345678901111 |
|
|
[分享][分享]数学主题分类表
是啊,那下拉列表里也是这些,每个分支够一辈子学 |
|
|
[推荐]推荐PARI和SAGE和MXGMA
有六个生成元在的生成元之间有很怪限制阿群结构的Z群同构:几种限制方式 G := AbelianGroup< h, i, j, k ,m,n| 7*h*i*n*3*m, k*6*i*m, 2*j, k*h ,m*j*i>; G; Abelian Group isomorphic to Z/12 + Z Defined on 2 generators Relations: 12*G.1 = 0 G2<h,i,g,k,m,s> := PolycyclicGroup<h,i,g,k,m,s| h^11=i^100=g^44=m^111=k^3=s>; G2; GrpGPC : G2 of infinite order on 6 PC-generators PC-Relations: h^11 = s, i^100 = s, g^44 = s, k^3 = s, m^111 = s Q<s,t,u,k,v,m>, h := Group< s, t, u, k,v,m| > t^2, u^7, s^2 = t^s = t, u^s = u^16, u^t = u ,m^111=k^3=v^1000>; > S := sub< Q | t*s^2, u^4, m^111,k^3,s,v>; S; Finitely presented group S on 6 generators Generators as words in group Q S.1 = t * s^2 S.2 = u^4 S.3 = m^111 S.4 = k^3 S.5 = s S.6 = v 给定限制的子群结构: G<[x]>, f := AbelianGroup< h, i, j, k ,m,n| 117*h*i*n*3*m, k*6*i*m, 19*j, k*h ,6*m*j*i>; G; > T, n := quo< G | x[1] + 2*x[1] + 24*x[2], 16*x[2] >; > T; n(x); n(sub< G | x[1] + x[2] + 110*x[1] >); Abelian Group isomorphic to Z/57 + Z Defined on 2 generators Relations: 57*x[1] = 0 Abelian Group isomorphic to Z/24 Defined on 1 generator Relations: 24*T.1 = 0 [ 8*T.1, 9*T.1 ] Abelian Group isomorphic to Z/8 Defined on 1 generator in supergroup T: $.1 = 3*T.1 Relations: 8*$.1 = 0 偶阶循环群和素阶循环群的子群结构对比: G1 := DihedralGroup(8); S1 := Subgroups(G1); S2:=DihedralGroup(7); S3 := Subgroups(S2); S1; S2; S3; Conjugacy classes of subgroups ------------------------------ [ 1] Order 1 Length 1 Permutation group acting on a set of cardinality 8 Order = 1 [ 2] Order 2 Length 1 Permutation group acting on a set of cardinality 8 Order = 2 (1, 5)(2, 6)(3, 7)(4, 8) [ 3] Order 2 Length 4 Permutation group acting on a set of cardinality 8 Order = 2 (1, 2)(3, 8)(4, 7)(5, 6) [ 4] Order 2 Length 4 Permutation group acting on a set of cardinality 8 Order = 2 (2, 8)(3, 7)(4, 6) [ 5] Order 4 Length 1 Permutation group acting on a set of cardinality 8 Order = 4 = 2^2 (1, 7, 5, 3)(2, 8, 6, 4) (1, 5)(2, 6)(3, 7)(4, 8) [ 6] Order 4 Length 2 Permutation group acting on a set of cardinality 8 Order = 4 = 2^2 (2, 8)(3, 7)(4, 6) (1, 5)(2, 6)(3, 7)(4, 8) [ 7] Order 4 Length 2 Permutation group acting on a set of cardinality 8 Order = 4 = 2^2 (1, 2)(3, 8)(4, 7)(5, 6) (1, 5)(2, 6)(3, 7)(4, 8) [ 8] Order 8 Length 1 Permutation group acting on a set of cardinality 8 Order = 8 = 2^3 (2, 8)(3, 7)(4, 6) (1, 7, 5, 3)(2, 8, 6, 4) (1, 5)(2, 6)(3, 7)(4, 8) [ 9] Order 8 Length 1 Permutation group acting on a set of cardinality 8 Order = 8 = 2^3 (1, 2)(3, 8)(4, 7)(5, 6) (1, 7, 5, 3)(2, 8, 6, 4) (1, 5)(2, 6)(3, 7)(4, 8) [10] Order 8 Length 1 Permutation group acting on a set of cardinality 8 Order = 8 = 2^3 (1, 2, 3, 4, 5, 6, 7, 8) (1, 7, 5, 3)(2, 8, 6, 4) (1, 5)(2, 6)(3, 7)(4, 8) [11] Order 16 Length 1 Permutation group acting on a set of cardinality 8 Order = 16 = 2^4 (2, 8)(3, 7)(4, 6) (1, 2, 3, 4, 5, 6, 7, 8) (1, 7, 5, 3)(2, 8, 6, 4) (1, 5)(2, 6)(3, 7)(4, 8) Permutation group S2 acting on a set of cardinality 7 Order = 14 = 2 * 7 (1, 2, 3, 4, 5, 6, 7) (1, 7)(2, 6)(3, 5) Conjugacy classes of subgroups ------------------------------ [1] Order 1 Length 1 Permutation group acting on a set of cardinality 7 Order = 1 [2] Order 2 Length 7 Permutation group acting on a set of cardinality 7 Order = 2 (1, 7)(2, 6)(3, 5) [3] Order 7 Length 1 Permutation group acting on a set of cardinality 7 Order = 7 (1, 6, 4, 2, 7, 5, 3) [4] Order 14 Length 1 Permutation group acting on a set of cardinality 7 Order = 14 = 2 * 7 (1, 7)(2, 6)(3, 5) (1, 6, 4, 2, 7, 5, 3) 一般线性群,子群和矩阵群,子群结构: K<w> := FiniteField(5); > GL1 := GeneralLinearGroup(7, K); GL1; H := MatrixGroup< 3, K | [1,w,0, 3,1,0, 1,w^2,1], [w,0,0, 0,1,0, 1,0,w] >; H; Order(GL1); Order(H); S4 := Subgroups(H); S4; GL(7, GF(5)) MatrixGroup(3, GF(5)) Generators: [1 1 0] [3 1 0] [1 1 1] [1 0 0] [0 1 0] [1 0 1] 13506266841692625000000000000000000 600 Conjugacy classes of subgroups ------------------------------ [ 1] Order 1 Length 1 MatrixGroup(3, GF(5)) of order 1 [ 2] Order 2 Length 25 MatrixGroup(3, GF(5)) of order 2 Generators: [4 0 0] [0 4 0] [0 0 1] [ 3] Order 3 Length 25 ................ ............. 酉距阵群子群结构: K1<w1> := FiniteField(9); G3 := SpecialUnitaryGroup(4, K1); G3; Order(G3); Order(G3); S5 := Subgroups(G3); S5; MatrixGroup(4, GF(3^2)) Generators: [ w1 0 0 0] [ 0 w1^7 0 0] [ 0 0 w1^3 0] [ 0 0 0 w1^5] [ 1 0 w1^2 0] [ 1 0 0 0] [ 0 w1^6 0 1] [ 0 w1^2 0 0] 13063680 13063680 Conjugacy classes of subgroups ------------------------------ [ 1] Order 1 Length 1 MatrixGroup(4, GF(3^2)) of order 1 [ 2] Order 2 Length 1 。。。。。。。。。。 。。。。。。。。。。。。。。 是那26个散单群吗? G := AbelianGroup< h, i, j, k ,m,n| 7*h*i*n*3*m, k*6*i*m, 2*j, k*h ,m*j*i>; G; IsAbelian(G); IsSimple(G); Abelian Group isomorphic to Z/12 + Z Defined on 2 generators Relations: 12*G.1 = 0 true false 生成西罗子群判断是否是单群或幂零群,可解群,导出群 G := AbelianGroup< h, i, j, k ,m,n| 7*h*i*n*3*m, k*6*i*m, 2*j, k*h ,m*j*i>; G; IsAbelian(G); IsSimple(G); S6 := SylowSubgroup(G, 11); S6; IsSimple(S6); IsNilpotent(S6); IsSoluble(S6); DerivedGroup(G); Abelian Group isomorphic to Z/12 + Z Defined on 2 generators Relations: 12*G.1 = 0 true false Abelian Group of order 1 false true true Abelian Group of order 1 导出群列 D := DerivedSeries(G); D1 := DerivedSeries(S6); D; D1; Abelian Group of order 1 [ Abelian Group isomorphic to Z/12 + Z Defined on 2 generators Relations: 12*G.1 = 0, Abelian Group of order 1 ] [ Abelian Group of order 1 正规子群列,判断是否是幂零的,阿群变量 ] S7 := SubnormalSeries(G, S6); S7; S8 := SubnormalSeries(S6, G); S8; AbelianInvariants(G) ; Invariants(G) ; AbelianInvariants(S6) ; [] [ Abelian Group isomorphic to Z/12 + Z Defined on 2 generators Relations: 12*G.1 = 0, Abelian Group of order 1 ] >> S8 := SubnormalSeries(S6, G); ^ Runtime error in 'SubnormalSeries': Argument is not a subgroup >> S8; ^ User error: Identifier 'S8' has not been declared or assigned [ 12, 0 ] 26个散单群里的铃木群阶: http://brauer.maths.qmul.ac.uk/Atlas/v3/spor/ Mathieu groups M11 M12 M22 M23 M24 Leech lattice groups HS J2 Co1 Co2 Co3 McL Suz Monster sections He HN Th Fi22 Fi23 Fi24' B M Pariahs J1 O'N J3 Ru J4 Ly Miscellaneous T F<w> := FiniteField(8); > V := VectorSpace(F, 4); > S9 := SuzukiGroup(V); > S9; Order(S9); MatrixGroup(4, GF(2^3)) Generators: [ 0 0 0 1] [ 0 0 1 0] [ 0 1 0 0] [ 1 0 0 0] [w^2 0 0 0] [ 0 w^6 0 0] [ 0 0 w 0] [ 0 0 0 w^5] [ 1 0 0 0] [w^2 1 0 0] [ 0 w 1 0] [w^5 w^3 w^2 1] 29120 CS := CharacteristicSubgroups(S9); 求特征子群代码: F<w> := FiniteField(8); > V := VectorSpace(F, 4); > G := SuzukiGroup(V); > G; Order(G); > CharacteristicSubgroups := function(G) > local A, outers, NS, CS; > A := AutomorphismGroup(G); > outers := [ a : a in Generators(A) | not IsInner(a) ]; > NS := NormalSubgroups(G); > CS := [n : n in NS | forall{a: a in outers| a(n`subgroup) eq n`subgroup }]; > return CS; > end function; > CS := CharacteristicSubgroups(DirectProduct(Alt(4),Alt(4))); > [c`order: c in CS]; [ 1, 16, 144 ] |
|
|
[讨论]考生必知的安全知识
没说清楚。。 考场外不都有平时见不到的装甲车停着,贴的就装甲车司机们裸照嘛。。。。 驾车破WIFI破网用软件现在挺流行,可这些司机们用硬件,只要你用电磁波,电脑电话电视对讲机全拿,一锅端! |
|
|
|
|
|
[推荐]老外用照相机拍芯片电磁信息
Soft TEMPEST技术简介--不用网线的木马 http://hi.baidu.com/nudt/blog/item/2acca5ec46f17d3826979130.html |
|
|
[推荐]老外用照相机拍芯片电磁信息
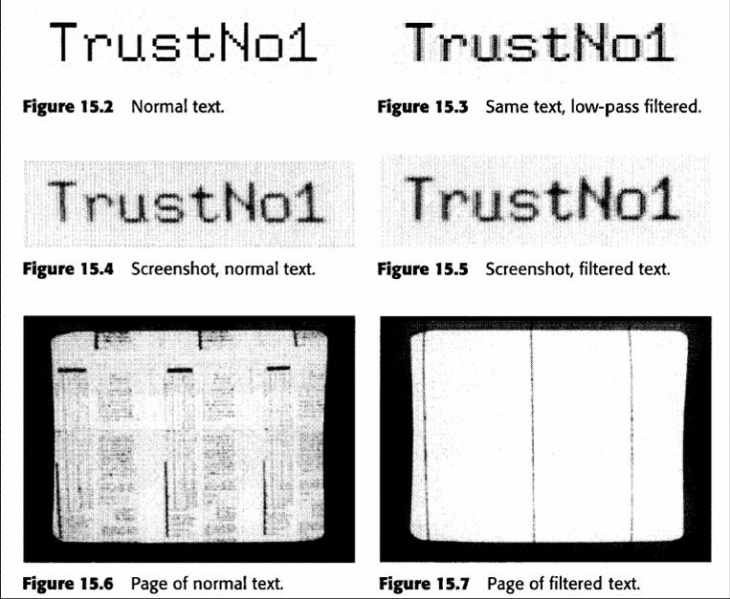
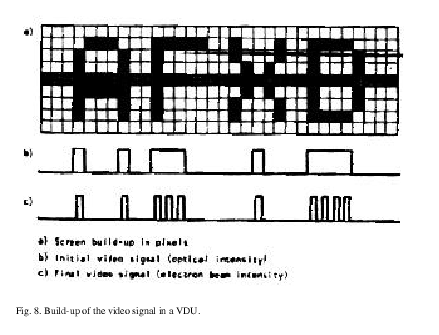
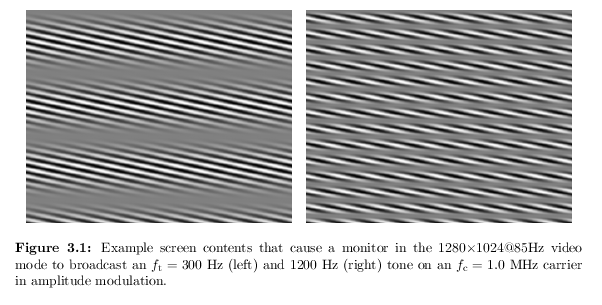
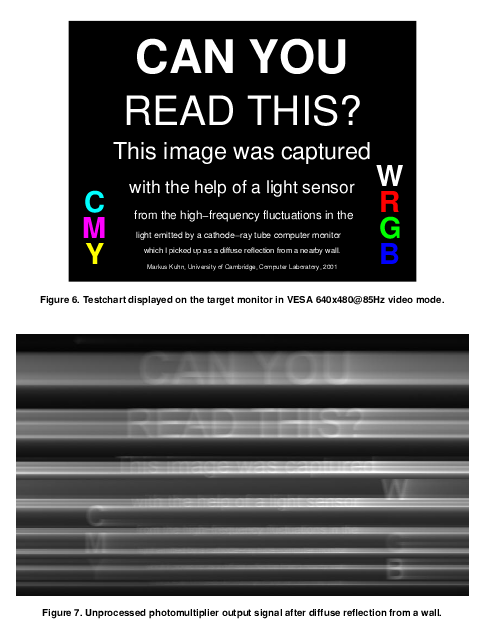
http://cryptome.org/tempest-time.htm http://blog.sina.com.cn/s/blog_536467600100fbjx.html TEMPEST技术,是取瞬态电磁辐射标准英文Transient Electromagnetic Pulse Emanation Standard的缩写;TEMPEST最早起源于美国国家安全局的一项绝密计划,它是控制电子设备泄密发射的代号。该项计划主要包括:电子设备中信息泄漏(电磁、声)信号的检测;信息泄露的抑制。 TEMPEST技术研究的主要内容包括:技术标准及规范研究;测试方法及测试仪器设备研究;防护及制造技术研究;服务、咨询及管理方法研究。 TEMPEST技术采用的主要措施包括:滤波、屏蔽、干扰、接地、隔离等措施,而且这些措施也可以结合起来使用。TEMPEST技术已历经三代:第一代,从1950年至1982年,以包容式TEMPEST计算机为代表;第二代,从1982年至1997年,以红黑分离式TEMPEST计算机为代表;第三代,从1997年开始,则是以SOFT-TEMPEST技术为代表。 SOFT-TEMPEST技术是由英国剑桥大学两位学者于1997年发明并推广应用的一项防信息泄漏新技术,其基本原理是通过给视频字符添加高频“噪声”并伴随发射伪字符,使敌方无法正确还原真实信息,而我方可正常显示,质量无变化,它替代了过去由硬件完成的抑制干扰功能,成本较低。采用TEMPEST技术的防护型TEMPEST计算机,使用软件来控制计算机机密信号的发射,同时加入了专用的攻击程序,当有人企图截获信息时系统能自动保护并进行自卫反击。 从计算机信息泄漏安全防护技术相关设备来说,国外加拿大EMCON公司、英国Rugged Systems公司和Candes Systems等公司都纷纷推出各自的防电磁信息泄漏计算机,配置了目前主流的Intel Pentium 4处理器和LCD液晶显示器等设备,电磁辐射都符合国外相关标准,如EMCON公司推出的SFFC TEMPEST计算机采用Intel Pentium 4处理器,17或19英寸显示器和其他外围设备,电磁泄漏符合NSTISSAM TEMPEST/1-92 Level 1和NATO AMSG 720B TEMPEST标准。 国内浪潮公司推出的低信息泄漏计算机,可与TEMPEST键盘、TEMPEST显示器等外设组成安全的防信息泄漏计算机系统。采用Intel P4 2.2GHz以上处理器,80G硬盘,17”显示器等设备,电磁泄漏符合GGBB1-1999 B级要求,电磁兼容符合GJB151A-97陆军地面设备类要求。 以美国为首的一些西方发达国家先后更新制定了一系列的信息安全标准,如美国1981年发布的主要有NACSIM5100和NACSIM5200系列,1991年美国推出了TEMPEST标准NSTISSAM TEMPEST/1-91,之后美国又推出了NSTISSAM TEMPEST/1-92标准。我国也在1999年推出了防信息泄漏标准GGBB1-1999《计算机信息系统设备电磁泄漏发射限值》,但由于技术保密原因,各国都对最新的制定的相关标准技术内容和数据参数进行了保密。 |
|
|
|
|
|
[推荐]推荐PARI和SAGE和MXGMA
群论文档初步贴这: 循环群结构分解,同阶或不同阶循环群和阿贝尔群之间同构关系: C18000:=CyclicGroup(18000); C18000; C15 := CyclicGroup(15); > C15; A15 := AbelianGroup([15]); > A15; iso11 := hom< C15 -> A15 | C15.1 -> 11*A15.1 >; A15 eq iso11(C15); A13 := AbelianGroup([13]); > A13; C13:=CyclicGroup(13); C13; iso11 := hom< C13 -> A13 | C13.1 -> 11*A13.1 >; A13 eq iso11(C13); iso11 := hom< C15 -> A13 | C15.1 -> 11*A13.1 >; A13 eq iso11(C15); Permutation group C18000 acting on a set of cardinality 18000 Order = 18000 = 2^4 * 3^2 * 5^3 Permutation group C15 acting on a set of cardinality 15 Order = 15 = 3 * 5 (1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12, 13, 14, 15) Abelian Group isomorphic to Z/15 Defined on 1 generator Relations: 15*A15.1 = 0 true Abelian Group isomorphic to Z/13 Defined on 1 generator Relations: 13*A13.1 = 0 Permutation group C13 acting on a set of cardinality 13 Order = 13 (1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12, 13) true true 可以从下面看自同构,陪集分解,分类关系,循环群生成元可映射到比群阶还大,从头再循环 C24:=CyclicGroup(24); C24; h := hom< C24 -> C24 | g :-> g^3 >; forall{ <c, d> : c, d in C24 | h(c * d) eq h(c) * h(d) }; im := h(C24); im; h := hom< C24 -> C24 | g :-> g^4 >; forall{ <c, d> : c, d in C24 | h(c * d) eq h(c) * h(d) }; im := h(C24); im; h := hom< C24 -> C24 | g :-> g^6 >; forall{ <c, d> : c, d in C24 | h(c * d) eq h(c) * h(d) }; im := h(C24); im; h := hom< C24 -> C24 | g :-> g^12 >; forall{ <c, d> : c, d in C24 | h(c * d) eq h(c) * h(d) }; im := h(C24); im; h := hom< C24 -> C24 | g :-> g^5 >; forall{ <c, d> : c, d in C24 | h(c * d) eq h(c) * h(d) }; im := h(C24); im; h := hom< C24 -> C24 | g :-> g^7 >; forall{ <c, d> : c, d in C24 | h(c * d) eq h(c) * h(d) }; im := h(C24); im; h := hom< C24 -> C24 | g :-> g^24 >; forall{ <c, d> : c, d in C24 | h(c * d) eq h(c) * h(d) }; im := h(C24); im; h := hom< C24 -> C24 | g :-> g^29 >; forall{ <c, d> : c, d in C24 | h(c * d) eq h(c) * h(d) }; im := h(C24); im; Permutation group C24 acting on a set of cardinality 24 Order = 24 = 2^3 * 3 (1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12, 13, 14, 15, 16, 17, 18, 19, 20, 21, 22, 23, 24) true Permutation group im acting on a set of cardinality 24 (1, 4, 7, 10, 13, 16, 19, 22)(2, 5, 8, 11, 14, 17, 20, 23)(3, 6, 9, 12, 15, 18, 21, 24) true Permutation group im acting on a set of cardinality 24 (1, 5, 9, 13, 17, 21)(2, 6, 10, 14, 18, 22)(3, 7, 11, 15, 19, 23)(4, 8, 12, 16, 20, 24) true Permutation group im acting on a set of cardinality 24 (1, 7, 13, 19)(2, 8, 14, 20)(3, 9, 15, 21)(4, 10, 16, 22)(5, 11, 17, 23)(6, 12, 18, 24) true Permutation group im acting on a set of cardinality 24 (1, 13)(2, 14)(3, 15)(4, 16)(5, 17)(6, 18)(7, 19)(8, 20)(9, 21)(10, 22)(11, 23)(12, 24) true Permutation group im acting on a set of cardinality 24 (1, 6, 11, 16, 21, 2, 7, 12, 17, 22, 3, 8, 13, 18, 23, 4, 9, 14, 19, 24, 5, 10, 15, 20) true Permutation group im acting on a set of cardinality 24 (1, 8, 15, 22, 5, 12, 19, 2, 9, 16, 23, 6, 13, 20, 3, 10, 17, 24, 7, 14, 21, 4, 11, 18) true Permutation group im acting on a set of cardinality 24 true Permutation group im acting on a set of cardinality 24 (1, 6, 11, 16, 21, 2, 7, 12, 17, 22, 3, 8, 13, 18, 23, 4, 9, 14, 19, 24, 5, 10, 15, 20) 对称群和结构,S5就要120个元素,手工计算就非常容易迷糊,下面是S7(元素5040个)的子群 的加减乘除,还能乘方,不知开方用哪个符号。。。象CycleStructure(x^y)也能算,这太离奇了。。 G19 := Sym(19); G19; C18000:=CyclicGroup(18000); C18000; S7 := Sym(7); S7; x := S7 ! (1,2,4)(5,6)(3,7); x; y := S7 ! (1,2,3,4,5)(6,7); y; x*y; x^-1; x^2; x^5*y^6; x / y^17; x^y; (x, y); x^3*y eq y*y^x; x^y^y CycleStructure(x^2*y); Degree(y^2); Order(x*y); CycleStructure(x^2*y); CycleStructure(x*y); CycleStructure(x^y); Symmetric group G19 acting on a set of cardinality 19 Order = 2^16 * 3^8 * 5^3 * 7^2 * 11 * 13 * 17 * 19 Permutation group C18000 acting on a set of cardinality 18000 Order = 18000 = 2^4 * 3^2 * 5^3 Symmetric group G7 acting on a set of cardinality 7 Order = 5040 = 2^4 * 3^2 * 5 * 7 (1, 2, 4)(3, 7)(5, 6) (1, 2, 3, 4, 5)(6, 7) (1, 3, 6)(2, 5, 7, 4) (1, 4, 2)(3, 7)(5, 6) (1, 4, 2) (1, 5, 6)(3, 7, 4) (1, 5, 7)(3, 6) (1, 7)(2, 3, 5)(4, 6) (1, 6, 2, 7, 5, 4, 3) false >> CycleStructure(x^2*y); ^ User error: bad syntax 5 12 [ <2, 3>, <1, 1> ] [ <4, 1>, <3, 1> ] [ <3, 1>, <2, 2> ] 最小的6阶二面体群CALEY表:在线能生成阶50的 > G := DihedralGroup(GrpPerm, 6); > f := NumberingMap(G); > [ [ f(x*y) : y in G ] : x in G ]; [ [ 1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12 ], [ 2, 3, 4, 5, 6, 1, 12, 7, 8, 9, 10, 11 ], [ 3, 4, 5, 6, 1, 2, 11, 12, 7, 8, 9, 10 ], [ 4, 5, 6, 1, 2, 3, 10, 11, 12, 7, 8, 9 ], [ 5, 6, 1, 2, 3, 4, 9, 10, 11, 12, 7, 8 ], [ 6, 1, 2, 3, 4, 5, 8, 9, 10, 11, 12, 7 ], [ 7, 8, 9, 10, 11, 12, 1, 2, 3, 4, 5, 6 ], [ 8, 9, 10, 11, 12, 7, 6, 1, 2, 3, 4, 5 ], [ 9, 10, 11, 12, 7, 8, 5, 6, 1, 2, 3, 4 ], [ 10, 11, 12, 7, 8, 9, 4, 5, 6, 1, 2, 3 ], [ 11, 12, 7, 8, 9, 10, 3, 4, 5, 6, 1, 2 ], [ 12, 7, 8, 9, 10, 11, 2, 3, 4, 5, 6, 1 ] ] 圈积:能生成很大的阶的新群 > G := WreathProduct( Sym(5), CyclicGroup(GrpPerm, 6)); > G; Order(G); Random(G); Random(G); Symmetric group acting on a set of cardinality 5 Order = 120 = 2^3 * 3 * 5 Permutation group acting on a set of cardinality 6 Order = 6 = 2 * 3 (1, 2, 3, 4, 5, 6) Permutation group G acting on a set of cardinality 30 Order = 2^19 * 3^7 * 5^6 (1, 6, 11, 16, 21, 26)(2, 7, 12, 17, 22, 27)(3, 8, 13, 18, 23, 28)(4, 9, 14, 19, 24, 29)(5, 10, 15, 20, 25, 30) (1, 2, 3, 4, 5) (1, 2) 17915904000000 (1, 11, 21, 5, 12, 23, 4, 14, 24)(2, 15, 22, 3, 13, 25)(6, 19, 28, 9, 18, 27)(7, 20, 29, 10, 16, 30)(8, 17, 26) (1, 15, 24)(2, 11, 25, 3, 12, 22, 4, 14, 23, 5, 13, 21)(6, 19, 26, 10, 18, 30, 9, 17, 28, 8, 20, 27)(7, 16, 29) 随机显示两个环结构 R := [ CycleStructure(Random(G)) : i in [1..2]]; > R; [ <9, 2>, <6, 1>, <3, 2> ], [ <8, 1>, <6, 2>, <4, 1>, <2, 3> ] ] |
|
|
[原创]magma,/PARI/GP中文文档ECC初步:
Example: Diffie-Hellman key exchange q := RandomPrime (160: Proof := false); q; Ilog2 (q); 2进制位数 repeat got_it, p := RandomPrime (1024, 1, q, 1000 : Proof := false); until got_it; > p; Ilog2 (p); 2进制位数 tmp := Random(p); exp := (p - 1) div q; > g := Modexp (tmp, exp, p); > g; Modexp (g, q, p); A_priv := Random (p-1); > A_pub := Modexp (g, A_priv, p); > B_priv := Random (p-1); > B_pub := Modexp (g, B_priv, p); > A_sec := Modexp (B_pub, A_priv, p); > B_sec := Modexp (A_pub, B_priv, p); A_sec eq B_sec; A_sec; 1442887065756557081811008885496150418808858816401 159 1651626359469589873102835252970210623774108012103316760123483790491795927792372\ 0911163345405386569084216526903485568850519787298376968456439442825925293266689\ 5321313697674085713119066460654757154900942213051543220536646001952121896818924\ 040862028079007349903890347825426890204440412990981184175301600052642601 1023 8396531707945536590388438602520909841199441225289405372543328552794730731140493\ 2359964273401131497951715591859147928675735938983332715282809702511549282280553\ 7257551736967439068907583093988590627324758408980681857356806656895703862655226\ 21592741188383919546746662841766547810852182714292042706175121823048920 1 true 5144176322605153756984581571117138785000992400326941258925591946874878623433746\ 0604279696565409179426210808910383200849384907133032735704943374046999690951643\ 2436947000024050385014162242822642019010522453269701147220601715739683999992133\ 82708798156652799536437768737718826497886878455615884529095508002441544 Hastad’s broadcast attack on RSA 一种广播攻击RSA,原理是孙子定理,M是明文 1024位的3个不同素因子密匙加密,密文只要三次出现在广播中,就能被还原为明文 函数都有,方便啊 孙子谁知道叫啥名? N1 := RSAModulus (1024, 3); N1; N2 := RSAModulus (1024, 3); > N2; N3 := RSAModulus (1024, 3); > N3; N1 lt N2; N2 lt N3; M := Random (N3); M; C1 := Modexp (M, 3, N1); C2 := Modexp (M, 3, N2); > C3 := Modexp (M, 3, N3); > C1; C2; C3; ciphertexts := [C1, C2, C3]; moduli := [N1, N2, N3]; > Cprime := CRT (ciphertexts, moduli); > Cprime; Iroot (Cprime, 3); 1191394973498639734758356886734022915243239449328167951285523220116137226774353\ 9176019504000834314079698783061932470536725623631410436123478027064344268960243\ 7364284793780727456801948423015783019014512753812345243506372098537224435020854\ 359848856524899561390988681729562607944000515285564642890387968646827499 1284091640527210186131874393840544095987650982828046236855841544838591571499173\ 1866298541100429948705032672190648692663519160856065108275130184865262172800857\ 3386565091923148415442237752544661929267855180513383588291450048199800697918748\ 507167493425580851595456232294309693917376008568189561641242801970999677 1079659736287944257378805435089043111076737452648956984975669952706815978980298\ 6622188200179949052343959127642578022293418583950295309545564738766859693242769\ 4693380883751647379784344459796750774988626755269852596427483690743738731140884\ 348140421109007063610908180910131454760258796787470341628217212597348237 true false 1065483725312210764607948804191105051984095256035964212419006647799252157478385\ 6334603416677964537633362076010548745454399657943033796697306916247944219685014\ 0939319424884142058105500815238082740397639628813948210482176247050158934106124\ 746653542454869790679475333470275013517239162467216886783299705473412909 1924084294474065804173347971493633606471329611790262546576596759680624764052803\ 5603855496570716546643207106535414986292485635347396779535480273771479179167217\ 3693328315426059122287765033711613884956437027782317188733396126117328636526178\ 56045629675048923525525556790596952847575213284810439009623226349241181 2376889508979652383834732793528970881037787915415560763427681345964168211539753\ 9459811216757749141242641330948276279731548487493134449049621818003288666629642\ 7107106879554253057484348013589960001869058474748052966098867953029654679461620\ 23532932526818702053588818851843636547054094394130454387535970722272602 9829945919241924969246733746114350726954659414719450874216585166522394276356794\ 2155581726235090790726244419011366315696252177358211842671261671704146797693032\ 4127009226220296583554431629646178702563947023823646933477546640724280367260704\ 60397221620150214727998193463203577893197619215531865820102008407048363 1209596332738531401730087906166277185149003439550896493434779023414176254956043\ 2315223272998309692796071291550238017300406144851952116784618699424318350163383\ 0623537152218766553695974915925794283159542108168794504904334776472147979805682\ 6758534588794554448343265778153818561455153300516738560092882314196842832629908\ 0893739204365221773895249374020378141139662196321124225421875676893136477652571\ 3686545436735346949304011400137889800182213384268514452639716065687280905474249\ 3802438205591679005814273361702058789755016475321682260206347613282853189661176\ 9660825254532364209370935104037356711766047967220791151295375750619273595873632\ 4374572156522931220632061230921514554158001662097184542577633122532256834871889\ 8076147371585186855569055341508199943243209040147941375606027322104397902862026\ 8383567305221626770449237160147609033402505962655670767253025758997906062878114\ 56219237300141333155757438706370370416335624953661405429 1065483725312210764607948804191105051984095256035964212419006647799252157478385\ 6334603416677964537633362076010548745454399657943033796697306916247944219685014\ 0939319424884142058105500815238082740397639628813948210482176247050158934106124\ 746653542454869790679475333470275013517239162467216886783299705473412909 ----------------------------- http://magma.maths.usyd.edu.au/magma/pdf/examples.pdf Chapter 28 Elliptic Curve Cryptography 28.5. EXAMPLE: ECDSA------------例子很易懂,但选安全曲线就难了 随机选一次系数a,常数b,X96-2荐a=-3,因为在常规表示和雅可比式变换中,有个表达式a=-3最方便,硬件计算快 p := RandomPrime (100); > K := GF(p); E := EllipticCurve ([Random(K), Random(K)]); E; p := RandomPrime (100); > K := GF(p); E := EllipticCurve ([-3, Random(K)]); E; 为了选安全曲线, repeat重复选: p := RandomPrime (100); > K := GF(p); > repeat repeat> E := EllipticCurve ([-3, Random(K)]); repeat> fo := FactoredOrder (E);---------------要大素数阶 repeat> n := fo[#fo][1]; repeat> until Ilog2 (n) ge 88; ------------------2进制位比域小 > Ilog2 (n); IsSupersingular(E);-------------------------------要非超奇异, P=100位,a随机选签名过程 Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 69611886555621063506166355926 over GF(157135449112378660707313000637) [ <2, 2>, <3, 1>, <7, 2>, <17, 1>, <181, 1>, <2099, 1>, <596447989, 1>, <69372018557, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 65388471706181964183230162768 over GF(157135449112378660707313000637) [ <73, 1>, <55079, 1>, <8304629, 1>, <4705925295986567, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 126592445929249859850032581477 over GF(157135449112378660707313000637) [ <5431, 1>, <7687, 1>, <3763894893517636036879, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 111827571730976256692740142243 over GF(157135449112378660707313000637) [ <2, 3>, <3, 1>, <17, 1>, <36583, 1>, <10527728854582845299309, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 147021577696058357454344453248 over GF(157135449112378660707313000637) [ <2, 1>, <3, 3>, <406169, 1>, <3777283, 1>, <1896680213262977, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 59756192161956097905575248378 over GF(157135449112378660707313000637) [ <2, 1>, <3, 1>, <151, 1>, <263, 1>, <617, 1>, <9941, 1>, <107516467533934661, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 55629840512052832330840836298 over GF(157135449112378660707313000637) [ <2, 2>, <7, 1>, <151, 1>, <37165432618821789909906481, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 151057113700827850188583571502 over GF(157135449112378660707313000637) [ <2, 2>, <11, 1>, <17, 1>, <29, 1>, <640740839, 1>, <11305562359133503, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 76416094973710013389958980325 over GF(157135449112378660707313000637) [ <2, 1>, <3, 2>, <7, 1>, <11093, 1>, <112422855763737340508257, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 139000244472820858413576632031 over GF(157135449112378660707313000637) [ <2, 2>, <3, 1>, <5, 1>, <37, 1>, <607, 1>, <12746273, 1>, <9148487302593389, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 66914405844156577851178843582 over GF(157135449112378660707313000637) [ <3, 1>, <7, 1>, <23, 1>, <8423, 1>, <38624266031016342385927, 1> ] Elliptic Curve defined by y^2 = x^3 + 157135449112378660707313000634*x + 143325094039473088283650924294 over GF(157135449112378660707313000637) [ <2, 1>, <3, 1>, <5, 2>, <1047569660749190309106427747, 1> ] 89 false 安全曲线重多,100位下就有上面这些,选好了安全曲线,下面就找了个基点,并求基点的阶,基点更多,安全曲线数*基点数*离散指数------大O,小O,ECC的安全指数可能真是指数级。。。 用的是下面曲线: y^2 = x^3 + 157135449112378660707313000634*x + 143325094039473088283650924294 over GF(157135449112378660707313000637) [ <2, 1>, <3, 1>, <5, 2>, <1047569660749190309106427747, 1> ] n;----------------------------------------------------E中n阶子循环群这 P := Random(E) * (Order(E) div n); -----找了个基点 P; Order(P) eq n; -------------------------------------基点的阶 d := Random(n); Q := d*P; 随机选的d<p,可能是密匙服务器生成 Q; M := Random(n); 甲方 要发的明文 > M; k := Random(n); 甲方随机选k<p kp_seq := ElementToSequence (k*P); 计算点乘k*P,表示成点 kp_seq; r := (IntegerRing()!kp_seq[1]) mod n; 不管k*P多大 都要mod n s := (Modinv (k, n) * (M + d*r)) mod n; 经过求模逆,模乘,模加,签好了 > s; r in [1..n-1]; s in [1..n-1]; w := Modinv (s, n); 下面是乙方验证,也要经过求点乘,模逆,模乘,模加 u1 := M*w mod n; u2 := r*w mod n; temp := u1*P + u2*Q; temp; temp_seq := ElementToSequence (temp); > v := (IntegerRing()!temp_seq[1]) mod n; > v; v eq r; 验证EQUAL,OK Elliptic Curve defined by y^2 = x^3 + 546406580005247203836151279129*x + 230151935666323598335959051729 over GF(966371258750148727567627105897) [ <3, 2>, <149, 1>, <720634793997127170564126541, 1> ]三个循环子群,,经过上面REPEAT选,已知攻击都被棑除,阶720634793997127170564126541的中的点安全,循环子群点阶如过恰=曲线阶,会被多项式级的同构攻击。不过恰=可能性太小了 89 false 720634793997127170564126541 (156817043070046010480672869099 : 138406249392994102180675488148 : 1)基点座标 true (823452749814859867769709264217 : 409839153103190558971036321686 : 1) 314368839904612579301554984 计算点乘d*P; [ 750750203409670127154353456215, 274010688382591384982046792082, 1 ] 337341060791448293483425930 明文,已被表示成曲线的点,明文,域元素,曲线点可互相转化。X9-62里有,有三种形式,不太难懂,这ElementToSequence函数一定包括了这功能 true true (750750203409670127154353456215 : 274010688382591384982046792082 : 1) 569382858660742597097727034 计算点乘 k*P true 下面P=100位,a=-3签名过程: Elliptic Curve defined by y^2 = x^3 + 344566048772404937900222995696*x + 122613265914087061833345770776 over GF(344566048772404937900222995699) [ <2, 4>, <173, 1>, <70009, 1>, <1778085018158714891237, 1> ] Elliptic Curve defined by y^2 = x^3 + 344566048772404937900222995696*x + 44333872090216421338353867400 over GF(344566048772404937900222995699) [ <108421, 1>, <189401, 1>, <16779414654143966807, 1> ] Elliptic Curve defined by y^2 = x^3 + 344566048772404937900222995696*x + 168372939479581669368060393010 over GF(344566048772404937900222995699) [ <2, 2>, <5, 1>, <41, 1>, <420202498502932494553451531, 1> ] 88 false 420202498502932494553451531 (19629684444028095682059018614 : 313332333218081159316329285802 : 1) true (185904318135579502698063049655 : 337526345404850851784130027470 : 1) 210595421815090177972701173 [ 71071577049370184377915299896, 30419639182367625537958244039, 1 ] 178411782669416518303895082 true true (71071577049370184377915299896 : 30419639182367625537958244039 : 1) 57354802374592798381991157 true 估记最少得把序,扩域多项式环搞透才能下面 http://magma.maths.usyd.edu.au/magma/pdf/examples.pdf 格攻击 Chapter 29 LLL and Lattice Based Ciphers 格密码 Chapter 33 Miscellaneous NTRU |
|
|
[原创]magma,/PARI/GP中文文档ECC初步:
求挠子群点,E1 := EllipticCurve([K1|0,-4,0,0,16])是SILVERMAN书上的,对照看看 K := FiniteField(47); E := EllipticCurve([K|0,0,0,7,8]); E; G, h := TorsionSubgroup(E); torsion_pts_E := [ h(g) : g in G ]; torsion_pts_E; K1 := FiniteField(17); E1 := EllipticCurve([K1|0,-4,0,0,16]); E1; G, h := TorsionSubgroup(E1); torsion_pts_E1 := [ h(g) : g in G ]; torsion_pts_E1; Elliptic Curve defined by y^2 = x^3 + 7*x + 8 over GF(47) [ (0 : 1 : 0), (22 : 0 : 1), (5 : 36 : 1), (44 : 30 : 1), (7 : 27 : 1), (25 : 43 : 1), (20 : 8 : 1), (21 : 43 : 1), (0 : 33 : 1), (39 : 2 : 1), (1 : 4 : 1), (4 : 10 : 1), (11 : 10 : 1), (9 : 1 : 1), (8 : 24 : 1), (42 : 41 : 1), (3 : 3 : 1), (12 : 38 : 1), (41 : 28 : 1), (32 : 10 : 1), (26 : 0 : 1), (46 : 0 : 1), (41 : 19 : 1), (32 : 37 : 1), (3 : 44 : 1), (12 : 9 : 1), (8 : 23 : 1), (42 : 6 : 1), (11 : 37 : 1), (9 : 46 : 1), (1 : 43 : 1), (4 : 37 : 1), (0 : 14 : 1), (39 : 45 : 1), (20 : 39 : 1), (21 : 4 : 1), (7 : 20 : 1), (25 : 4 : 1), (5 : 11 : 1), (44 : 17 : 1) ] Elliptic Curve defined by y^2 = x^3 + 13*x^2 + 16 over GF(17) [ (0 : 1 : 0), (2 : 12 : 1), (9 : 9 : 1), (14 : 15 : 1), (4 : 13 : 1), (11 : 9 : 1), (10 : 2 : 1), (1 : 8 : 1), (0 : 13 : 1), (15 : 3 : 1), (8 : 0 : 1), (15 : 14 : 1), (0 : 4 : 1), (1 : 9 : 1), (10 : 15 : 1), (11 : 8 : 1), (4 : 4 : 1), (14 : 2 : 1), (9 : 8 : 1), (2 : 5 : 1) ] MW, f := MordellWeilGroup(E); MW, f := MordellWeilGroup(E1); Elliptic Curve defined by y^2 = x^3 - 4*x^2 + 16 over Rational Field [ (0 : 1 : 0), (0 : 4 : 1), (4 : -4 : 1), (4 : 4 : 1), (0 : -4 : 1) ] Elliptic Curve defined by y^2 = x^3 - 4*x^2 + 16 over Rational Field [ (0 : 1 : 0), (0 : 4 : 1), (4 : -4 : 1), (4 : 4 : 1), (0 : -4 : 1) ] Abelian Group isomorphic to Z/5 Defined on 1 generator Relations: 5*MW.1 = 0 Elliptic Curve defined by y^2 = x^3 + 7*x + 8 over Rational Field [ (0 : 1 : 0), (-1 : 0 : 1) ] Abelian Group isomorphic to Z/2 + Z + Z Defined on 3 generators Relations: 2*MW.1 = 0 |
|
|
|
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值