|
|
[求助]IDA反汇编后的问题
COMMAND/ C:\>edit 1.txt seg000:00000000 ; seg000:00000000 ; ╔═════════════════════════════════════════════════════════════ ════════════? seg000:00000000 ; ? This file is generated by The Interactive Disassembler (I DA) ? seg000:00000000 ; ? Copyright (c) 2006 by DataRescue sa/nv, <ida@datarescue.c om> ? seg000:00000000 ; ?Licensed to: Paul Ashton - Blue Lane Technologies (1-user Adv anced 03/2006) ?s seg000:00000000 ; ╚═════════════════════════════════════════════════════════════ ════════════? CMD EDIT C:\>type 1.txt seg000:00000000 ; seg000:00000000 ; ╔═════════════════════════════════════════════════════════════ ════════════? seg000:00000000 ; ? This file is generated by The Interactive Disassembler (I DA) ? seg000:00000000 ; ? Copyright (c) 2006 by DataRescue sa/nv, <ida@datarescue.c om> ? seg000:00000000 ; ?Licensed to: Paul Ashton - Blue Lane Technologies (1-user Adv anced 03/2006) ?s seg000:00000000 ; ╚═════════════════════════════════════════════════════════════ ════════════? |
|
|
[求助]IDA反汇编后的问题
CMD/EDIT 1.txt File Edit Search View Options Help ┌───────────── C:\Documents and Settings\Administrator\╫└├µ\1.txt ─────────────┐ │seg000:00000000 ; ↑ │seg000:00000000 ; ╔═══════════════════════════════════════════════════════════█ │seg000:00000000 ; ? This file is generated by The Interactive Disassembler █ │seg000:00000000 ; ? Copyright (c) 2006 by DataRescue sa/nv, <ida@datarescue█ │seg000:00000000 ; ?Licensed to: Paul Ashton - Blue Lane Technologies (1-user A█ │seg000:00000000 ; ╚═══════════════════════════════════════════════════════════█ │ COMMAND /EDIT 1.TXT C:\>type 1.txt seg000:00000000 ; seg000:00000000 ; ╔═════════════════════════════════════════════════════════════ ════════════? seg000:00000000 ; ? This file is generated by The Interactive Disassembler (I DA) ? seg000:00000000 ; ? Copyright (c) 2006 by DataRescue sa/nv, <ida@datarescue.c om> ? seg000:00000000 ; ?Licensed to: Paul Ashton - Blue Lane Technologies (1-user Adv anced 03/2006) ?s seg000:00000000 ; ╚═════════════════════════════════════════════════════════════ ════════════? █ |
|
|
[求助]看雪首页上的“登录论坛”按钮为什么进不了论坛?
是啊!为什么? |
|
|
[求助]IDA反汇编后的问题
 谢谢! 谢谢!也不知到在哪个环节用到IBM的扩展ASCII? 一般浏栏器和论坛都只用HTML的特殊字符的 c9 : É cd : Í 3f : ? seg000:00000000 ; seg000:00000000 ; 赏屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 ; ? This file is generated by The Interactive Disassembler (IDA) ? seg000:00000000 ; ? Copyright (c) 2006 by DataRescue sa/nv, <ida@datarescue.com> ? seg000:00000000 ; ?Licensed to: Paul Ashton - Blue Lane Technologies (1-user Advanced 03/2006) ?s seg000:00000000 ; 韧屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 ; seg000:00000000 ; Input MD5 : 32A0C9660FE3AC20151C3E98CD176C93 seg000:00000000 seg000:00000000 ; File Name : C:\Documents and Settings\Administrator\桌面\3.txt seg000:00000000 ; Format : Binary file seg000:00000000 ; Base Address: 0000h Range: 0000h - 0179h Loaded length: 0179h seg000:00000000 seg000:00000000 .686p seg000:00000000 .mmx seg000:00000000 .model flat seg000:00000000 seg000:00000000 ; 屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 seg000:00000000 ; Segment type: Pure code seg000:00000000 seg000 segment byte public 'CODE' use32 seg000:00000000 assume cs:seg000 seg000:00000000 assume es:nothing, ss:nothing, ds:nothing, fs:nothing, gs:nothing seg000:00000000 db 0C9h ; ? seg000:00000001 db 0CDh ; ? seg000:00000002 db 0CDh ; ? seg000:00000003 db 0CDh ; ? seg000:00000004 db 0CDh ; ? seg000:00000005 db 0CDh ; ? seg000:00000006 db 0CDh ; ? seg000:00000007 db 0CDh ; ? seg000:00000008 db 0CDh ; ? seg000:00000009 db 0CDh ; ? seg000:0000000A db 0CDh ; ? seg000:0000000B db 0CDh ; ? seg000:0000000C db 0CDh ; ? seg000:0000000D db 0CDh ; ? seg000:0000000E db 0CDh ; ? seg000:0000000F db 0CDh ; ? seg000:00000010 db 0CDh ; ? seg000:00000011 db 0CDh ; ? seg000:00000012 db 0CDh ; ? seg000:00000013 db 0CDh ; ? seg000:00000014 db 0CDh ; ? seg000:00000015 db 0CDh ; ? seg000:00000016 db 0CDh ; ? seg000:00000017 db 0CDh ; ? seg000:00000018 db 0CDh ; ? seg000:00000019 db 0CDh ; ? seg000:0000001A db 0CDh ; ? seg000:0000001B db 0CDh ; ? seg000:0000001C db 0CDh ; ? seg000:0000001D db 0CDh ; ? seg000:0000001E db 0CDh ; ? seg000:0000001F db 0CDh ; ? seg000:00000020 db 0CDh ; ? seg000:00000021 db 0CDh ; ? seg000:00000022 db 0CDh ; ? seg000:00000023 db 0CDh ; ? seg000:00000024 db 0CDh ; ? seg000:00000025 db 0CDh ; ? seg000:00000026 db 0CDh ; ? seg000:00000027 db 0CDh ; ? seg000:00000028 db 0CDh ; ? seg000:00000029 db 0CDh ; ? seg000:0000002A db 0CDh ; ? seg000:0000002B db 0CDh ; ? seg000:0000002C db 0CDh ; ? seg000:0000002D db 0CDh ; ? seg000:0000002E db 0CDh ; ? seg000:0000002F db 0CDh ; ? seg000:00000030 db 0CDh ; ? seg000:00000031 db 0CDh ; ? seg000:00000032 db 0CDh ; ? seg000:00000033 db 0CDh ; ? seg000:00000034 db 0CDh ; ? seg000:00000035 db 0CDh ; ? seg000:00000036 db 0CDh ; ? seg000:00000037 db 0CDh ; ? seg000:00000038 db 0CDh ; ? seg000:00000039 db 0CDh ; ? seg000:0000003A db 0CDh ; ? seg000:0000003B db 0CDh ; ? seg000:0000003C db 0CDh ; ? seg000:0000003D db 0CDh ; ? seg000:0000003E db 0CDh ; ? seg000:0000003F db 0CDh ; ? seg000:00000040 db 0CDh ; ? seg000:00000041 db 0CDh ; ? seg000:00000042 db 0CDh ; ? seg000:00000043 db 0CDh ; ? seg000:00000044 db 0CDh ; ? seg000:00000045 db 0CDh ; ? seg000:00000046 db 0CDh ; ? seg000:00000047 db 0CDh ; ? seg000:00000048 db 0CDh ; ? seg000:00000049 db 0CDh ; ? seg000:0000004A db 3Fh ; ? seg000:0000004B db 0Dh seg000:0000004C db 0Ah seg000:0000004D db 20h seg000:0000004E db 3Fh ; ? seg000:0000004F db 20h seg000:00000050 db 20h seg000:00000051 db 20h seg000:00000052 db 20h seg000:00000053 db 54h ; T seg000:00000054 db 68h ; h seg000:00000055 db 69h ; i seg000:00000056 db 73h ; s seg000:00000057 db 20h seg000:00000058 db 66h ; f seg000:00000059 db 69h ; i seg000:0000005A db 6Ch ; l seg000:0000005B db 65h ; e seg000:0000005C db 20h seg000:0000005D db 69h ; i seg000:0000005E db 73h ; s seg000:0000005F db 20h seg000:00000060 db 67h ; g seg000:00000061 db 65h ; e seg000:00000062 db 6Eh ; n seg000:00000063 db 65h ; e seg000:00000064 db 72h ; r seg000:00000065 db 61h ; a seg000:00000066 db 74h ; t seg000:00000067 db 65h ; e seg000:00000068 db 64h ; d seg000:00000069 db 20h seg000:0000006A db 62h ; b seg000:0000006B db 79h ; y seg000:0000006C db 20h seg000:0000006D db 54h ; T seg000:0000006E db 68h ; h seg000:0000006F db 65h ; e seg000:00000070 db 20h seg000:00000071 db 49h ; I seg000:00000072 db 6Eh ; n seg000:00000073 db 74h ; t seg000:00000074 db 65h ; e seg000:00000075 db 72h ; r seg000:00000076 db 61h ; a seg000:00000077 db 63h ; c seg000:00000078 db 74h ; t seg000:00000079 db 69h ; i seg000:0000007A db 76h ; v seg000:0000007B db 65h ; e seg000:0000007C db 20h seg000:0000007D db 44h ; D seg000:0000007E db 69h ; i seg000:0000007F db 73h ; s seg000:00000080 db 61h ; a seg000:00000081 db 73h ; s seg000:00000082 db 73h ; s seg000:00000083 db 65h ; e seg000:00000084 db 6Dh ; m seg000:00000085 db 62h ; b seg000:00000086 db 6Ch ; l seg000:00000087 db 65h ; e seg000:00000088 db 72h ; r seg000:00000089 db 20h seg000:0000008A db 28h ; ( seg000:0000008B db 49h ; I seg000:0000008C db 44h ; D seg000:0000008D db 41h ; A seg000:0000008E db 29h ; ) seg000:0000008F db 20h seg000:00000090 db 20h seg000:00000091 db 20h seg000:00000092 db 20h seg000:00000093 db 20h seg000:00000094 db 20h seg000:00000095 db 20h seg000:00000096 db 20h seg000:00000097 db 3Fh ; ? seg000:00000098 db 0Dh seg000:00000099 db 0Ah seg000:0000009A db 20h seg000:0000009B db 3Fh ; ? seg000:0000009C db 20h seg000:0000009D db 20h seg000:0000009E db 20h seg000:0000009F db 20h seg000:000000A0 db 43h ; C seg000:000000A1 db 6Fh ; o seg000:000000A2 db 70h ; p seg000:000000A3 db 79h ; y seg000:000000A4 db 72h ; r seg000:000000A5 db 69h ; i seg000:000000A6 db 67h ; g seg000:000000A7 db 68h ; h seg000:000000A8 db 74h ; t seg000:000000A9 db 20h seg000:000000AA db 28h ; ( seg000:000000AB db 63h ; c seg000:000000AC db 29h ; ) seg000:000000AD db 20h seg000:000000AE db 32h ; 2 seg000:000000AF db 30h ; 0 seg000:000000B0 db 30h ; 0 seg000:000000B1 db 36h ; 6 seg000:000000B2 db 20h seg000:000000B3 db 62h ; b seg000:000000B4 db 79h ; y seg000:000000B5 db 20h seg000:000000B6 db 44h ; D seg000:000000B7 db 61h ; a seg000:000000B8 db 74h ; t seg000:000000B9 db 61h ; a seg000:000000BA db 52h ; R seg000:000000BB db 65h ; e seg000:000000BC db 73h ; s seg000:000000BD db 63h ; c seg000:000000BE db 75h ; u seg000:000000BF db 65h ; e seg000:000000C0 db 20h seg000:000000C1 db 73h ; s seg000:000000C2 db 61h ; a seg000:000000C3 db 2Fh ; / seg000:000000C4 db 6Eh ; n seg000:000000C5 db 76h ; v seg000:000000C6 db 2Ch ; , seg000:000000C7 db 20h seg000:000000C8 db 3Ch ; < seg000:000000C9 db 69h ; i seg000:000000CA db 64h ; d seg000:000000CB db 61h ; a seg000:000000CC db 40h ; @ seg000:000000CD db 64h ; d seg000:000000CE db 61h ; a seg000:000000CF db 74h ; t seg000:000000D0 db 61h ; a seg000:000000D1 db 72h ; r seg000:000000D2 db 65h ; e seg000:000000D3 db 73h ; s seg000:000000D4 db 63h ; c seg000:000000D5 db 75h ; u seg000:000000D6 db 65h ; e seg000:000000D7 db 2Eh ; . seg000:000000D8 db 63h ; c seg000:000000D9 db 6Fh ; o seg000:000000DA db 6Dh ; m seg000:000000DB db 3Eh ; > seg000:000000DC db 20h seg000:000000DD db 20h seg000:000000DE db 20h seg000:000000DF db 20h seg000:000000E0 db 20h seg000:000000E1 db 20h seg000:000000E2 db 20h seg000:000000E3 db 20h seg000:000000E4 db 3Fh ; ? seg000:000000E5 db 0Dh seg000:000000E6 db 0Ah seg000:000000E7 db 20h seg000:000000E8 db 50h ; P seg000:000000E9 db 61h ; a seg000:000000EA db 75h ; u seg000:000000EB db 6Ch ; l seg000:000000EC db 20h seg000:000000ED db 41h ; A seg000:000000EE db 73h ; s seg000:000000EF db 68h ; h seg000:000000F0 db 74h ; t seg000:000000F1 db 6Fh ; o seg000:000000F2 db 6Eh ; n seg000:000000F3 db 20h seg000:000000F4 db 2Dh ; - seg000:000000F5 db 20h seg000:000000F6 db 42h ; B seg000:000000F7 db 6Ch ; l seg000:000000F8 db 75h ; u seg000:000000F9 db 65h ; e seg000:000000FA db 20h seg000:000000FB db 4Ch ; L seg000:000000FC db 61h ; a seg000:000000FD db 6Eh ; n seg000:000000FE db 65h ; e seg000:000000FF db 20h seg000:00000100 db 54h ; T seg000:00000101 db 65h ; e seg000:00000102 db 63h ; c seg000:00000103 db 68h ; h seg000:00000104 db 6Eh ; n seg000:00000105 db 6Fh ; o seg000:00000106 db 6Ch ; l seg000:00000107 db 6Fh ; o seg000:00000108 db 67h ; g seg000:00000109 db 69h ; i seg000:0000010A db 65h ; e seg000:0000010B db 73h ; s seg000:0000010C db 20h seg000:0000010D db 28h ; ( seg000:0000010E db 31h ; 1 seg000:0000010F db 2Dh ; - seg000:00000110 db 75h ; u seg000:00000111 db 73h ; s seg000:00000112 db 65h ; e seg000:00000113 db 72h ; r seg000:00000114 db 20h seg000:00000115 db 41h ; A seg000:00000116 db 64h ; d seg000:00000117 db 76h ; v seg000:00000118 db 61h ; a seg000:00000119 db 6Eh ; n seg000:0000011A db 63h ; c seg000:0000011B db 65h ; e seg000:0000011C db 64h ; d seg000:0000011D db 20h seg000:0000011E db 30h ; 0 seg000:0000011F db 33h ; 3 seg000:00000120 db 2Fh ; / seg000:00000121 db 32h ; 2 seg000:00000122 db 30h ; 0 seg000:00000123 db 30h ; 0 seg000:00000124 db 36h ; 6 seg000:00000125 db 29h ; ) seg000:00000126 db 20h seg000:00000127 db 3Fh ; ? seg000:00000128 db 73h ; s seg000:00000129 db 0Dh seg000:0000012A db 0Ah seg000:0000012B db 20h seg000:0000012C db 0C8h ; ? seg000:0000012D db 0CDh ; ? seg000:0000012E db 0CDh ; ? seg000:0000012F db 0CDh ; ? seg000:00000130 db 0CDh ; ? seg000:00000131 db 0CDh ; ? seg000:00000132 db 0CDh ; ? seg000:00000133 db 0CDh ; ? seg000:00000134 db 0CDh ; ? seg000:00000135 db 0CDh ; ? seg000:00000136 db 0CDh ; ? seg000:00000137 db 0CDh ; ? seg000:00000138 db 0CDh ; ? seg000:00000139 db 0CDh ; ? seg000:0000013A db 0CDh ; ? seg000:0000013B db 0CDh ; ? seg000:0000013C db 0CDh ; ? seg000:0000013D db 0CDh ; ? seg000:0000013E db 0CDh ; ? seg000:0000013F db 0CDh ; ? seg000:00000140 db 0CDh ; ? seg000:00000141 db 0CDh ; ? seg000:00000142 db 0CDh ; ? seg000:00000143 db 0CDh ; ? seg000:00000144 db 0CDh ; ? seg000:00000145 db 0CDh ; ? seg000:00000146 db 0CDh ; ? seg000:00000147 db 0CDh ; ? seg000:00000148 db 0CDh ; ? seg000:00000149 db 0CDh ; ? seg000:0000014A db 0CDh ; ? seg000:0000014B db 0CDh ; ? seg000:0000014C db 0CDh ; ? seg000:0000014D db 0CDh ; ? seg000:0000014E db 0CDh ; ? seg000:0000014F db 0CDh ; ? seg000:00000150 db 0CDh ; ? seg000:00000151 db 0CDh ; ? seg000:00000152 db 0CDh ; ? seg000:00000153 db 0CDh ; ? seg000:00000154 db 0CDh ; ? seg000:00000155 db 0CDh ; ? seg000:00000156 db 0CDh ; ? seg000:00000157 db 0CDh ; ? seg000:00000158 db 0CDh ; ? seg000:00000159 db 0CDh ; ? seg000:0000015A db 0CDh ; ? seg000:0000015B db 0CDh ; ? seg000:0000015C db 0CDh ; ? seg000:0000015D db 0CDh ; ? seg000:0000015E db 0CDh ; ? seg000:0000015F db 0CDh ; ? seg000:00000160 db 0CDh ; ? seg000:00000161 db 0CDh ; ? seg000:00000162 db 0CDh ; ? seg000:00000163 db 0CDh ; ? seg000:00000164 db 0CDh ; ? seg000:00000165 db 0CDh ; ? seg000:00000166 db 0CDh ; ? seg000:00000167 db 0CDh ; ? seg000:00000168 db 0CDh ; ? seg000:00000169 db 0CDh ; ? seg000:0000016A db 0CDh ; ? seg000:0000016B db 0CDh ; ? seg000:0000016C db 0CDh ; ? seg000:0000016D db 0CDh ; ? seg000:0000016E db 0CDh ; ? seg000:0000016F db 0CDh ; ? seg000:00000170 db 0CDh ; ? seg000:00000171 db 0CDh ; ? seg000:00000172 db 0CDh ; ? seg000:00000173 db 0CDh ; ? seg000:00000174 db 0CDh ; ? seg000:00000175 db 0CDh ; ? seg000:00000176 db 3Fh ; ? seg000:00000177 db 0Dh seg000:00000178 db 0Ah seg000:00000178 seg000 ends seg000:00000178 seg000:00000178 seg000:00000178 end |
|
|
[求助]IDA反汇编后的问题
c9 : É �xc9; seg000:00000000 ; seg000:00000000 ; 赏屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 ; ? This file is generated by The Interactive Disassembler (IDA) ? seg000:00000000 ; ? Copyright (c) 2006 by DataRescue sa/nv, <ida@datarescue.com> ? seg000:00000000 ; ?Licensed to: Paul Ashton - Blue Lane Technologies (1-user Advanced 03/2006) ?s seg000:00000000 ; 韧屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 ; seg000:00000000 ; Input MD5 : 32A0C9660FE3AC20151C3E98CD176C93 seg000:00000000 seg000:00000000 ; File Name : C:\Documents and Settings\Administrator\桌面\3.txt seg000:00000000 ; Format : Binary file seg000:00000000 ; Base Address: 0000h Range: 0000h - 0179h Loaded length: 0179h seg000:00000000 seg000:00000000 .686p seg000:00000000 .mmx seg000:00000000 .model flat seg000:00000000 seg000:00000000 ; 屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 seg000:00000000 ; Segment type: Pure code seg000:00000000 seg000 segment byte public 'CODE' use32 seg000:00000000 assume cs:seg000 seg000:00000000 assume es:nothing, ss:nothing, ds:nothing, fs:nothing, gs:nothing seg000:00000000 db 0C9h ; ? seg000:00000001 db 0CDh ; ? seg000:00000002 db 0CDh ; ? seg000:00000003 db 0CDh ; ? seg000:00000004 db 0CDh ; ? seg000:00000005 db 0CDh ; ? seg000:00000006 db 0CDh ; ? seg000:00000007 db 0CDh ; ? seg000:00000008 db 0CDh ; ? seg000:00000009 db 0CDh ; ? seg000:0000000A db 0CDh ; ? seg000:0000000B db 0CDh ; ? seg000:0000000C db 0CDh ; ? seg000:0000000D db 0CDh ; ? seg000:0000000E db 0CDh ; ? seg000:0000000F db 0CDh ; ? seg000:00000010 db 0CDh ; ? seg000:00000011 db 0CDh ; ? seg000:00000012 db 0CDh ; ? seg000:00000013 db 0CDh ; ? seg000:00000014 db 0CDh ; ? seg000:00000015 db 0CDh ; ? seg000:00000016 db 0CDh ; ? seg000:00000017 db 0CDh ; ? seg000:00000018 db 0CDh ; ? seg000:00000019 db 0CDh ; ? seg000:0000001A db 0CDh ; ? seg000:0000001B db 0CDh ; ? seg000:0000001C db 0CDh ; ? seg000:0000001D db 0CDh ; ? seg000:0000001E db 0CDh ; ? seg000:0000001F db 0CDh ; ? seg000:00000020 db 0CDh ; ? seg000:00000021 db 0CDh ; ? seg000:00000022 db 0CDh ; ? seg000:00000023 db 0CDh ; ? seg000:00000024 db 0CDh ; ? seg000:00000025 db 0CDh ; ? seg000:00000026 db 0CDh ; ? seg000:00000027 db 0CDh ; ? seg000:00000028 db 0CDh ; ? seg000:00000029 db 0CDh ; ? seg000:0000002A db 0CDh ; ? seg000:0000002B db 0CDh ; ? seg000:0000002C db 0CDh ; ? seg000:0000002D db 0CDh ; ? seg000:0000002E db 0CDh ; ? seg000:0000002F db 0CDh ; ? seg000:00000030 db 0CDh ; ? seg000:00000031 db 0CDh ; ? seg000:00000032 db 0CDh ; ? seg000:00000033 db 0CDh ; ? seg000:00000034 db 0CDh ; ? seg000:00000035 db 0CDh ; ? seg000:00000036 db 0CDh ; ? seg000:00000037 db 0CDh ; ? seg000:00000038 db 0CDh ; ? seg000:00000039 db 0CDh ; ? seg000:0000003A db 0CDh ; ? seg000:0000003B db 0CDh ; ? seg000:0000003C db 0CDh ; ? seg000:0000003D db 0CDh ; ? seg000:0000003E db 0CDh ; ? seg000:0000003F db 0CDh ; ? seg000:00000040 db 0CDh ; ? seg000:00000041 db 0CDh ; ? seg000:00000042 db 0CDh ; ? seg000:00000043 db 0CDh ; ? seg000:00000044 db 0CDh ; ? seg000:00000045 db 0CDh ; ? seg000:00000046 db 0CDh ; ? seg000:00000047 db 0CDh ; ? seg000:00000048 db 0CDh ; ? seg000:00000049 db 0CDh ; ? seg000:0000004A db 3Fh ; ? seg000:0000004B db 0Dh seg000:0000004C db 0Ah seg000:0000004D db 20h seg000:0000004E db 3Fh ; ? seg000:0000004F db 20h seg000:00000050 db 20h seg000:00000051 db 20h seg000:00000052 db 20h seg000:00000053 db 54h ; T seg000:00000054 db 68h ; h seg000:00000055 db 69h ; i seg000:00000056 db 73h ; s seg000:00000057 db 20h seg000:00000058 db 66h ; f seg000:00000059 db 69h ; i seg000:0000005A db 6Ch ; l seg000:0000005B db 65h ; e seg000:0000005C db 20h seg000:0000005D db 69h ; i seg000:0000005E db 73h ; s seg000:0000005F db 20h seg000:00000060 db 67h ; g seg000:00000061 db 65h ; e seg000:00000062 db 6Eh ; n seg000:00000063 db 65h ; e seg000:00000064 db 72h ; r seg000:00000065 db 61h ; a seg000:00000066 db 74h ; t seg000:00000067 db 65h ; e seg000:00000068 db 64h ; d seg000:00000069 db 20h seg000:0000006A db 62h ; b seg000:0000006B db 79h ; y seg000:0000006C db 20h seg000:0000006D db 54h ; T seg000:0000006E db 68h ; h seg000:0000006F db 65h ; e seg000:00000070 db 20h seg000:00000071 db 49h ; I seg000:00000072 db 6Eh ; n seg000:00000073 db 74h ; t seg000:00000074 db 65h ; e seg000:00000075 db 72h ; r seg000:00000076 db 61h ; a seg000:00000077 db 63h ; c seg000:00000078 db 74h ; t seg000:00000079 db 69h ; i seg000:0000007A db 76h ; v seg000:0000007B db 65h ; e seg000:0000007C db 20h seg000:0000007D db 44h ; D seg000:0000007E db 69h ; i seg000:0000007F db 73h ; s seg000:00000080 db 61h ; a seg000:00000081 db 73h ; s seg000:00000082 db 73h ; s seg000:00000083 db 65h ; e seg000:00000084 db 6Dh ; m seg000:00000085 db 62h ; b seg000:00000086 db 6Ch ; l seg000:00000087 db 65h ; e seg000:00000088 db 72h ; r seg000:00000089 db 20h seg000:0000008A db 28h ; ( seg000:0000008B db 49h ; I seg000:0000008C db 44h ; D seg000:0000008D db 41h ; A seg000:0000008E db 29h ; ) seg000:0000008F db 20h seg000:00000090 db 20h seg000:00000091 db 20h seg000:00000092 db 20h seg000:00000093 db 20h seg000:00000094 db 20h seg000:00000095 db 20h seg000:00000096 db 20h seg000:00000097 db 3Fh ; ? seg000:00000098 db 0Dh seg000:00000099 db 0Ah seg000:0000009A db 20h seg000:0000009B db 3Fh ; ? seg000:0000009C db 20h seg000:0000009D db 20h seg000:0000009E db 20h seg000:0000009F db 20h seg000:000000A0 db 43h ; C seg000:000000A1 db 6Fh ; o seg000:000000A2 db 70h ; p seg000:000000A3 db 79h ; y seg000:000000A4 db 72h ; r seg000:000000A5 db 69h ; i seg000:000000A6 db 67h ; g seg000:000000A7 db 68h ; h seg000:000000A8 db 74h ; t seg000:000000A9 db 20h seg000:000000AA db 28h ; ( seg000:000000AB db 63h ; c seg000:000000AC db 29h ; ) seg000:000000AD db 20h seg000:000000AE db 32h ; 2 seg000:000000AF db 30h ; 0 seg000:000000B0 db 30h ; 0 seg000:000000B1 db 36h ; 6 seg000:000000B2 db 20h seg000:000000B3 db 62h ; b seg000:000000B4 db 79h ; y seg000:000000B5 db 20h seg000:000000B6 db 44h ; D seg000:000000B7 db 61h ; a seg000:000000B8 db 74h ; t seg000:000000B9 db 61h ; a seg000:000000BA db 52h ; R seg000:000000BB db 65h ; e seg000:000000BC db 73h ; s seg000:000000BD db 63h ; c seg000:000000BE db 75h ; u seg000:000000BF db 65h ; e seg000:000000C0 db 20h seg000:000000C1 db 73h ; s seg000:000000C2 db 61h ; a seg000:000000C3 db 2Fh ; / seg000:000000C4 db 6Eh ; n seg000:000000C5 db 76h ; v seg000:000000C6 db 2Ch ; , seg000:000000C7 db 20h seg000:000000C8 db 3Ch ; < seg000:000000C9 db 69h ; i seg000:000000CA db 64h ; d seg000:000000CB db 61h ; a seg000:000000CC db 40h ; @ seg000:000000CD db 64h ; d seg000:000000CE db 61h ; a seg000:000000CF db 74h ; t seg000:000000D0 db 61h ; a seg000:000000D1 db 72h ; r seg000:000000D2 db 65h ; e seg000:000000D3 db 73h ; s seg000:000000D4 db 63h ; c seg000:000000D5 db 75h ; u seg000:000000D6 db 65h ; e seg000:000000D7 db 2Eh ; . seg000:000000D8 db 63h ; c seg000:000000D9 db 6Fh ; o seg000:000000DA db 6Dh ; m seg000:000000DB db 3Eh ; > seg000:000000DC db 20h seg000:000000DD db 20h seg000:000000DE db 20h seg000:000000DF db 20h seg000:000000E0 db 20h seg000:000000E1 db 20h seg000:000000E2 db 20h seg000:000000E3 db 20h seg000:000000E4 db 3Fh ; ? seg000:000000E5 db 0Dh seg000:000000E6 db 0Ah seg000:000000E7 db 20h seg000:000000E8 db 50h ; P seg000:000000E9 db 61h ; a seg000:000000EA db 75h ; u seg000:000000EB db 6Ch ; l seg000:000000EC db 20h seg000:000000ED db 41h ; A seg000:000000EE db 73h ; s seg000:000000EF db 68h ; h seg000:000000F0 db 74h ; t seg000:000000F1 db 6Fh ; o seg000:000000F2 db 6Eh ; n seg000:000000F3 db 20h seg000:000000F4 db 2Dh ; - seg000:000000F5 db 20h seg000:000000F6 db 42h ; B seg000:000000F7 db 6Ch ; l seg000:000000F8 db 75h ; u seg000:000000F9 db 65h ; e seg000:000000FA db 20h seg000:000000FB db 4Ch ; L seg000:000000FC db 61h ; a seg000:000000FD db 6Eh ; n seg000:000000FE db 65h ; e seg000:000000FF db 20h seg000:00000100 db 54h ; T seg000:00000101 db 65h ; e seg000:00000102 db 63h ; c seg000:00000103 db 68h ; h seg000:00000104 db 6Eh ; n seg000:00000105 db 6Fh ; o seg000:00000106 db 6Ch ; l seg000:00000107 db 6Fh ; o seg000:00000108 db 67h ; g seg000:00000109 db 69h ; i seg000:0000010A db 65h ; e seg000:0000010B db 73h ; s seg000:0000010C db 20h seg000:0000010D db 28h ; ( seg000:0000010E db 31h ; 1 seg000:0000010F db 2Dh ; - seg000:00000110 db 75h ; u seg000:00000111 db 73h ; s seg000:00000112 db 65h ; e seg000:00000113 db 72h ; r seg000:00000114 db 20h seg000:00000115 db 41h ; A seg000:00000116 db 64h ; d seg000:00000117 db 76h ; v seg000:00000118 db 61h ; a seg000:00000119 db 6Eh ; n seg000:0000011A db 63h ; c seg000:0000011B db 65h ; e seg000:0000011C db 64h ; d seg000:0000011D db 20h seg000:0000011E db 30h ; 0 seg000:0000011F db 33h ; 3 seg000:00000120 db 2Fh ; / seg000:00000121 db 32h ; 2 seg000:00000122 db 30h ; 0 seg000:00000123 db 30h ; 0 seg000:00000124 db 36h ; 6 seg000:00000125 db 29h ; ) seg000:00000126 db 20h seg000:00000127 db 3Fh ; ? seg000:00000128 db 73h ; s seg000:00000129 db 0Dh seg000:0000012A db 0Ah seg000:0000012B db 20h seg000:0000012C db 0C8h ; ? seg000:0000012D db 0CDh ; ? seg000:0000012E db 0CDh ; ? seg000:0000012F db 0CDh ; ? seg000:00000130 db 0CDh ; ? seg000:00000131 db 0CDh ; ? seg000:00000132 db 0CDh ; ? seg000:00000133 db 0CDh ; ? seg000:00000134 db 0CDh ; ? seg000:00000135 db 0CDh ; ? seg000:00000136 db 0CDh ; ? seg000:00000137 db 0CDh ; ? seg000:00000138 db 0CDh ; ? seg000:00000139 db 0CDh ; ? seg000:0000013A db 0CDh ; ? seg000:0000013B db 0CDh ; ? seg000:0000013C db 0CDh ; ? seg000:0000013D db 0CDh ; ? seg000:0000013E db 0CDh ; ? seg000:0000013F db 0CDh ; ? seg000:00000140 db 0CDh ; ? seg000:00000141 db 0CDh ; ? seg000:00000142 db 0CDh ; ? seg000:00000143 db 0CDh ; ? seg000:00000144 db 0CDh ; ? seg000:00000145 db 0CDh ; ? seg000:00000146 db 0CDh ; ? seg000:00000147 db 0CDh ; ? seg000:00000148 db 0CDh ; ? seg000:00000149 db 0CDh ; ? seg000:0000014A db 0CDh ; ? seg000:0000014B db 0CDh ; ? seg000:0000014C db 0CDh ; ? seg000:0000014D db 0CDh ; ? seg000:0000014E db 0CDh ; ? seg000:0000014F db 0CDh ; ? seg000:00000150 db 0CDh ; ? seg000:00000151 db 0CDh ; ? seg000:00000152 db 0CDh ; ? seg000:00000153 db 0CDh ; ? seg000:00000154 db 0CDh ; ? seg000:00000155 db 0CDh ; ? seg000:00000156 db 0CDh ; ? seg000:00000157 db 0CDh ; ? seg000:00000158 db 0CDh ; ? seg000:00000159 db 0CDh ; ? seg000:0000015A db 0CDh ; ? seg000:0000015B db 0CDh ; ? seg000:0000015C db 0CDh ; ? seg000:0000015D db 0CDh ; ? seg000:0000015E db 0CDh ; ? seg000:0000015F db 0CDh ; ? seg000:00000160 db 0CDh ; ? seg000:00000161 db 0CDh ; ? seg000:00000162 db 0CDh ; ? seg000:00000163 db 0CDh ; ? seg000:00000164 db 0CDh ; ? seg000:00000165 db 0CDh ; ? seg000:00000166 db 0CDh ; ? seg000:00000167 db 0CDh ; ? seg000:00000168 db 0CDh ; ? seg000:00000169 db 0CDh ; ? seg000:0000016A db 0CDh ; ? seg000:0000016B db 0CDh ; ? seg000:0000016C db 0CDh ; ? seg000:0000016D db 0CDh ; ? seg000:0000016E db 0CDh ; ? seg000:0000016F db 0CDh ; ? seg000:00000170 db 0CDh ; ? seg000:00000171 db 0CDh ; ? seg000:00000172 db 0CDh ; ? seg000:00000173 db 0CDh ; ? seg000:00000174 db 0CDh ; ? seg000:00000175 db 0CDh ; ? seg000:00000176 db 3Fh ; ? seg000:00000177 db 0Dh seg000:00000178 db 0Ah seg000:00000178 seg000 ends seg000:00000178 seg000:00000178 seg000:00000178 end |
|
|
[求助]IDA反汇编后的问题
c9 : É seg000:00000000 ; seg000:00000000 ; 赏屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 ; ? This file is generated by The Interactive Disassembler (IDA) ? seg000:00000000 ; ? Copyright (c) 2006 by DataRescue sa/nv, <ida@datarescue.com> ? seg000:00000000 ; ?Licensed to: Paul Ashton - Blue Lane Technologies (1-user Advanced 03/2006) ?s seg000:00000000 ; 韧屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 ; seg000:00000000 ; Input MD5 : 32A0C9660FE3AC20151C3E98CD176C93 seg000:00000000 seg000:00000000 ; File Name : C:\Documents and Settings\Administrator\桌面\3.txt seg000:00000000 ; Format : Binary file seg000:00000000 ; Base Address: 0000h Range: 0000h - 0179h Loaded length: 0179h seg000:00000000 seg000:00000000 .686p seg000:00000000 .mmx seg000:00000000 .model flat seg000:00000000 seg000:00000000 ; 屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 seg000:00000000 ; Segment type: Pure code seg000:00000000 seg000 segment byte public 'CODE' use32 seg000:00000000 assume cs:seg000 seg000:00000000 assume es:nothing, ss:nothing, ds:nothing, fs:nothing, gs:nothing seg000:00000000 db 0C9h ; ? seg000:00000001 db 0CDh ; ? seg000:00000002 db 0CDh ; ? seg000:00000003 db 0CDh ; ? seg000:00000004 db 0CDh ; ? seg000:00000005 db 0CDh ; ? seg000:00000006 db 0CDh ; ? seg000:00000007 db 0CDh ; ? seg000:00000008 db 0CDh ; ? seg000:00000009 db 0CDh ; ? seg000:0000000A db 0CDh ; ? seg000:0000000B db 0CDh ; ? seg000:0000000C db 0CDh ; ? seg000:0000000D db 0CDh ; ? seg000:0000000E db 0CDh ; ? seg000:0000000F db 0CDh ; ? seg000:00000010 db 0CDh ; ? seg000:00000011 db 0CDh ; ? seg000:00000012 db 0CDh ; ? seg000:00000013 db 0CDh ; ? seg000:00000014 db 0CDh ; ? seg000:00000015 db 0CDh ; ? seg000:00000016 db 0CDh ; ? seg000:00000017 db 0CDh ; ? seg000:00000018 db 0CDh ; ? seg000:00000019 db 0CDh ; ? seg000:0000001A db 0CDh ; ? seg000:0000001B db 0CDh ; ? seg000:0000001C db 0CDh ; ? seg000:0000001D db 0CDh ; ? seg000:0000001E db 0CDh ; ? seg000:0000001F db 0CDh ; ? seg000:00000020 db 0CDh ; ? seg000:00000021 db 0CDh ; ? seg000:00000022 db 0CDh ; ? seg000:00000023 db 0CDh ; ? seg000:00000024 db 0CDh ; ? seg000:00000025 db 0CDh ; ? seg000:00000026 db 0CDh ; ? seg000:00000027 db 0CDh ; ? seg000:00000028 db 0CDh ; ? seg000:00000029 db 0CDh ; ? seg000:0000002A db 0CDh ; ? seg000:0000002B db 0CDh ; ? seg000:0000002C db 0CDh ; ? seg000:0000002D db 0CDh ; ? seg000:0000002E db 0CDh ; ? seg000:0000002F db 0CDh ; ? seg000:00000030 db 0CDh ; ? seg000:00000031 db 0CDh ; ? seg000:00000032 db 0CDh ; ? seg000:00000033 db 0CDh ; ? seg000:00000034 db 0CDh ; ? seg000:00000035 db 0CDh ; ? seg000:00000036 db 0CDh ; ? seg000:00000037 db 0CDh ; ? seg000:00000038 db 0CDh ; ? seg000:00000039 db 0CDh ; ? seg000:0000003A db 0CDh ; ? seg000:0000003B db 0CDh ; ? seg000:0000003C db 0CDh ; ? seg000:0000003D db 0CDh ; ? seg000:0000003E db 0CDh ; ? seg000:0000003F db 0CDh ; ? seg000:00000040 db 0CDh ; ? seg000:00000041 db 0CDh ; ? seg000:00000042 db 0CDh ; ? seg000:00000043 db 0CDh ; ? seg000:00000044 db 0CDh ; ? seg000:00000045 db 0CDh ; ? seg000:00000046 db 0CDh ; ? seg000:00000047 db 0CDh ; ? seg000:00000048 db 0CDh ; ? seg000:00000049 db 0CDh ; ? seg000:0000004A db 3Fh ; ? seg000:0000004B db 0Dh seg000:0000004C db 0Ah seg000:0000004D db 20h seg000:0000004E db 3Fh ; ? seg000:0000004F db 20h seg000:00000050 db 20h seg000:00000051 db 20h seg000:00000052 db 20h seg000:00000053 db 54h ; T seg000:00000054 db 68h ; h seg000:00000055 db 69h ; i seg000:00000056 db 73h ; s seg000:00000057 db 20h seg000:00000058 db 66h ; f seg000:00000059 db 69h ; i seg000:0000005A db 6Ch ; l seg000:0000005B db 65h ; e seg000:0000005C db 20h seg000:0000005D db 69h ; i seg000:0000005E db 73h ; s seg000:0000005F db 20h seg000:00000060 db 67h ; g seg000:00000061 db 65h ; e seg000:00000062 db 6Eh ; n seg000:00000063 db 65h ; e seg000:00000064 db 72h ; r seg000:00000065 db 61h ; a seg000:00000066 db 74h ; t seg000:00000067 db 65h ; e seg000:00000068 db 64h ; d seg000:00000069 db 20h seg000:0000006A db 62h ; b seg000:0000006B db 79h ; y seg000:0000006C db 20h seg000:0000006D db 54h ; T seg000:0000006E db 68h ; h seg000:0000006F db 65h ; e seg000:00000070 db 20h seg000:00000071 db 49h ; I seg000:00000072 db 6Eh ; n seg000:00000073 db 74h ; t seg000:00000074 db 65h ; e seg000:00000075 db 72h ; r seg000:00000076 db 61h ; a seg000:00000077 db 63h ; c seg000:00000078 db 74h ; t seg000:00000079 db 69h ; i seg000:0000007A db 76h ; v seg000:0000007B db 65h ; e seg000:0000007C db 20h seg000:0000007D db 44h ; D seg000:0000007E db 69h ; i seg000:0000007F db 73h ; s seg000:00000080 db 61h ; a seg000:00000081 db 73h ; s seg000:00000082 db 73h ; s seg000:00000083 db 65h ; e seg000:00000084 db 6Dh ; m seg000:00000085 db 62h ; b seg000:00000086 db 6Ch ; l seg000:00000087 db 65h ; e seg000:00000088 db 72h ; r seg000:00000089 db 20h seg000:0000008A db 28h ; ( seg000:0000008B db 49h ; I seg000:0000008C db 44h ; D seg000:0000008D db 41h ; A seg000:0000008E db 29h ; ) seg000:0000008F db 20h seg000:00000090 db 20h seg000:00000091 db 20h seg000:00000092 db 20h seg000:00000093 db 20h seg000:00000094 db 20h seg000:00000095 db 20h seg000:00000096 db 20h seg000:00000097 db 3Fh ; ? seg000:00000098 db 0Dh seg000:00000099 db 0Ah seg000:0000009A db 20h seg000:0000009B db 3Fh ; ? seg000:0000009C db 20h seg000:0000009D db 20h seg000:0000009E db 20h seg000:0000009F db 20h seg000:000000A0 db 43h ; C seg000:000000A1 db 6Fh ; o seg000:000000A2 db 70h ; p seg000:000000A3 db 79h ; y seg000:000000A4 db 72h ; r seg000:000000A5 db 69h ; i seg000:000000A6 db 67h ; g seg000:000000A7 db 68h ; h seg000:000000A8 db 74h ; t seg000:000000A9 db 20h seg000:000000AA db 28h ; ( seg000:000000AB db 63h ; c seg000:000000AC db 29h ; ) seg000:000000AD db 20h seg000:000000AE db 32h ; 2 seg000:000000AF db 30h ; 0 seg000:000000B0 db 30h ; 0 seg000:000000B1 db 36h ; 6 seg000:000000B2 db 20h seg000:000000B3 db 62h ; b seg000:000000B4 db 79h ; y seg000:000000B5 db 20h seg000:000000B6 db 44h ; D seg000:000000B7 db 61h ; a seg000:000000B8 db 74h ; t seg000:000000B9 db 61h ; a seg000:000000BA db 52h ; R seg000:000000BB db 65h ; e seg000:000000BC db 73h ; s seg000:000000BD db 63h ; c seg000:000000BE db 75h ; u seg000:000000BF db 65h ; e seg000:000000C0 db 20h seg000:000000C1 db 73h ; s seg000:000000C2 db 61h ; a seg000:000000C3 db 2Fh ; / seg000:000000C4 db 6Eh ; n seg000:000000C5 db 76h ; v seg000:000000C6 db 2Ch ; , seg000:000000C7 db 20h seg000:000000C8 db 3Ch ; < seg000:000000C9 db 69h ; i seg000:000000CA db 64h ; d seg000:000000CB db 61h ; a seg000:000000CC db 40h ; @ seg000:000000CD db 64h ; d seg000:000000CE db 61h ; a seg000:000000CF db 74h ; t seg000:000000D0 db 61h ; a seg000:000000D1 db 72h ; r seg000:000000D2 db 65h ; e seg000:000000D3 db 73h ; s seg000:000000D4 db 63h ; c seg000:000000D5 db 75h ; u seg000:000000D6 db 65h ; e seg000:000000D7 db 2Eh ; . seg000:000000D8 db 63h ; c seg000:000000D9 db 6Fh ; o seg000:000000DA db 6Dh ; m seg000:000000DB db 3Eh ; > seg000:000000DC db 20h seg000:000000DD db 20h seg000:000000DE db 20h seg000:000000DF db 20h seg000:000000E0 db 20h seg000:000000E1 db 20h seg000:000000E2 db 20h seg000:000000E3 db 20h seg000:000000E4 db 3Fh ; ? seg000:000000E5 db 0Dh seg000:000000E6 db 0Ah seg000:000000E7 db 20h seg000:000000E8 db 50h ; P seg000:000000E9 db 61h ; a seg000:000000EA db 75h ; u seg000:000000EB db 6Ch ; l seg000:000000EC db 20h seg000:000000ED db 41h ; A seg000:000000EE db 73h ; s seg000:000000EF db 68h ; h seg000:000000F0 db 74h ; t seg000:000000F1 db 6Fh ; o seg000:000000F2 db 6Eh ; n seg000:000000F3 db 20h seg000:000000F4 db 2Dh ; - seg000:000000F5 db 20h seg000:000000F6 db 42h ; B seg000:000000F7 db 6Ch ; l seg000:000000F8 db 75h ; u seg000:000000F9 db 65h ; e seg000:000000FA db 20h seg000:000000FB db 4Ch ; L seg000:000000FC db 61h ; a seg000:000000FD db 6Eh ; n seg000:000000FE db 65h ; e seg000:000000FF db 20h seg000:00000100 db 54h ; T seg000:00000101 db 65h ; e seg000:00000102 db 63h ; c seg000:00000103 db 68h ; h seg000:00000104 db 6Eh ; n seg000:00000105 db 6Fh ; o seg000:00000106 db 6Ch ; l seg000:00000107 db 6Fh ; o seg000:00000108 db 67h ; g seg000:00000109 db 69h ; i seg000:0000010A db 65h ; e seg000:0000010B db 73h ; s seg000:0000010C db 20h seg000:0000010D db 28h ; ( seg000:0000010E db 31h ; 1 seg000:0000010F db 2Dh ; - seg000:00000110 db 75h ; u seg000:00000111 db 73h ; s seg000:00000112 db 65h ; e seg000:00000113 db 72h ; r seg000:00000114 db 20h seg000:00000115 db 41h ; A seg000:00000116 db 64h ; d seg000:00000117 db 76h ; v seg000:00000118 db 61h ; a seg000:00000119 db 6Eh ; n seg000:0000011A db 63h ; c seg000:0000011B db 65h ; e seg000:0000011C db 64h ; d seg000:0000011D db 20h seg000:0000011E db 30h ; 0 seg000:0000011F db 33h ; 3 seg000:00000120 db 2Fh ; / seg000:00000121 db 32h ; 2 seg000:00000122 db 30h ; 0 seg000:00000123 db 30h ; 0 seg000:00000124 db 36h ; 6 seg000:00000125 db 29h ; ) seg000:00000126 db 20h seg000:00000127 db 3Fh ; ? seg000:00000128 db 73h ; s seg000:00000129 db 0Dh seg000:0000012A db 0Ah seg000:0000012B db 20h seg000:0000012C db 0C8h ; ? seg000:0000012D db 0CDh ; ? seg000:0000012E db 0CDh ; ? seg000:0000012F db 0CDh ; ? seg000:00000130 db 0CDh ; ? seg000:00000131 db 0CDh ; ? seg000:00000132 db 0CDh ; ? seg000:00000133 db 0CDh ; ? seg000:00000134 db 0CDh ; ? seg000:00000135 db 0CDh ; ? seg000:00000136 db 0CDh ; ? seg000:00000137 db 0CDh ; ? seg000:00000138 db 0CDh ; ? seg000:00000139 db 0CDh ; ? seg000:0000013A db 0CDh ; ? seg000:0000013B db 0CDh ; ? seg000:0000013C db 0CDh ; ? seg000:0000013D db 0CDh ; ? seg000:0000013E db 0CDh ; ? seg000:0000013F db 0CDh ; ? seg000:00000140 db 0CDh ; ? seg000:00000141 db 0CDh ; ? seg000:00000142 db 0CDh ; ? seg000:00000143 db 0CDh ; ? seg000:00000144 db 0CDh ; ? seg000:00000145 db 0CDh ; ? seg000:00000146 db 0CDh ; ? seg000:00000147 db 0CDh ; ? seg000:00000148 db 0CDh ; ? seg000:00000149 db 0CDh ; ? seg000:0000014A db 0CDh ; ? seg000:0000014B db 0CDh ; ? seg000:0000014C db 0CDh ; ? seg000:0000014D db 0CDh ; ? seg000:0000014E db 0CDh ; ? seg000:0000014F db 0CDh ; ? seg000:00000150 db 0CDh ; ? seg000:00000151 db 0CDh ; ? seg000:00000152 db 0CDh ; ? seg000:00000153 db 0CDh ; ? seg000:00000154 db 0CDh ; ? seg000:00000155 db 0CDh ; ? seg000:00000156 db 0CDh ; ? seg000:00000157 db 0CDh ; ? seg000:00000158 db 0CDh ; ? seg000:00000159 db 0CDh ; ? seg000:0000015A db 0CDh ; ? seg000:0000015B db 0CDh ; ? seg000:0000015C db 0CDh ; ? seg000:0000015D db 0CDh ; ? seg000:0000015E db 0CDh ; ? seg000:0000015F db 0CDh ; ? seg000:00000160 db 0CDh ; ? seg000:00000161 db 0CDh ; ? seg000:00000162 db 0CDh ; ? seg000:00000163 db 0CDh ; ? seg000:00000164 db 0CDh ; ? seg000:00000165 db 0CDh ; ? seg000:00000166 db 0CDh ; ? seg000:00000167 db 0CDh ; ? seg000:00000168 db 0CDh ; ? seg000:00000169 db 0CDh ; ? seg000:0000016A db 0CDh ; ? seg000:0000016B db 0CDh ; ? seg000:0000016C db 0CDh ; ? seg000:0000016D db 0CDh ; ? seg000:0000016E db 0CDh ; ? seg000:0000016F db 0CDh ; ? seg000:00000170 db 0CDh ; ? seg000:00000171 db 0CDh ; ? seg000:00000172 db 0CDh ; ? seg000:00000173 db 0CDh ; ? seg000:00000174 db 0CDh ; ? seg000:00000175 db 0CDh ; ? seg000:00000176 db 3Fh ; ? seg000:00000177 db 0Dh seg000:00000178 db 0Ah seg000:00000178 seg000 ends seg000:00000178 seg000:00000178 seg000:00000178 end |
|
|
[求助]IDA反汇编后的问题
TRUETYPE造字程序坏了 在UNICODE表中总算找到”屯“了,应该肯定是UNICODE了 ================================ U+ 0 1 2 3 4 5 6 7 8 9 A B C D E F 5C00 尀 封 専 尃 射 尅 将 將 專 尉 尊 尋 尌 對 導 小 5C10 尐 少 尒 尓 尔 尕 尖 尗 尘 尙 尚 尛 尜 尝 尞 尟 5C20 尠 尡 尢 尣 尤 尥 尦 尧 尨 尩 尪 尫 尬 尭 尮 尯 5C30 尰 就 尲 尳 尴 尵 尶 尷 尸 尹 尺 尻 尼 尽 尾 尿 5C40 局 屁 层 屃 屄 居 屆 屇 屈 屉 届 屋 屌 屍 屎 屏 5C50 屐 屑 屒 屓 屔 展 屖 屗 屘 屙 屚 屛 屜 屝 属 屟 5C60 屠 屡 屢 屣 層 履 屦 屧 屨 屩 屪 屫 屬 屭 屮 屯 |
|
|
[求助]IDA反汇编后的问题
谢谢提醒!我还是钻出来吧,也不知IDA用的UNICODE还是ANSI还是UFT8,上面存成了ANSI了,又存成UNICODE变成下面样了。。。。, 0AED:0100 FF FE 4F 8D 6F 5C 6F 5C-6F 5C 6F 5C 6F 5C 6F 5C ..O.o\o\o\o\o\o\ 0AED:0110 6F 5C 6F 5C 6F 5C 6F 5C-6F 5C 6F 5C 6F 5C 6F 5C o\o\o\o\o\o\o\o\ 0AED:0120 6F 5C 6F 5C 6F 5C 6F 5C-6F 5C 6F 5C 6F 5C 6F 5C o\o\o\o\o\o\o\o\ 0AED:0130 6F 5C 6F 5C 6F 5C 6F 5C-6F 5C 6F 5C 6F 5C 6F 5C o\o\o\o\o\o\o\o\ 0AED:0140 6F 5C 6F 5C 6F 5C 6F 5C-6F 5C 6F 5C 3F 00 FA B4 o\o\o\o\o\o\?... 0AED:0150 3E CD 21 BA BC 98 B4 41-CD 21 C6 06 D1 96 00 E9 >.!....A.!...... 0AED:0160 57 FA E9 AE FE 24 0C 7A-10 50 24 08 A2 D4 99 58 W....$.z.P$....X 0AED:0170 24 04 A2 D8 99 08 06 D2-99 A0 D8 99 0A C0 C3 80 $............... - |
|
|
[求助]IDA反汇编后的问题
非常感谢! 如果是汉字“C9”怎麽成“赏”?“CD”怎麽成“屯”的,在UNICODE编码中汉字不是两字节吗? 刚用记事本把“赏屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯?”保存成.txt,又用IDA打开: seg000:00000000 ; 赏屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 ; ? This file is generated by The Interactive Disassembler (IDA) ? seg000:00000000 ; ? Copyright (c) 2006 by DataRescue sa/nv, <ida@datarescue.com> ? seg000:00000000 ; ?Licensed to: Paul Ashton - Blue Lane Technologies (1-user Advanced 03/2006) ?s seg000:00000000 ; 韧屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 ; seg000:00000000 ; Input MD5 : 2E05F30D14AB3E0CD05CD15018055CD6 seg000:00000000 seg000:00000000 ; File Name : C:\Documents and Settings\Administrator\My Documents\1.txt seg000:00000000 ; Format : Binary file seg000:00000000 ; Base Address: 0000h Range: 0000h - 004Bh Loaded length: 004Bh seg000:00000000 seg000:00000000 .686p seg000:00000000 .mmx seg000:00000000 .model flat seg000:00000000 seg000:00000000 ; 屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯? seg000:00000000 seg000:00000000 ; Segment type: Pure code seg000:00000000 seg000 segment byte public 'CODE' use32 seg000:00000000 assume cs:seg000 seg000:00000000 assume es:nothing, ss:nothing, ds:nothing, fs:nothing, gs:nothing seg000:00000000 db 0C9h ; ? seg000:00000001 db 0CDh ; ? seg000:00000002 db 0CDh ; ? seg000:00000003 db 0CDh ; ? seg000:00000004 db 0CDh ; ? seg000:00000005 db 0CDh ; ? seg000:00000006 db 0CDh ; ? seg000:00000007 db 0CDh ; ? seg000:00000008 db 0CDh ; ? seg000:00000009 db 0CDh ; ? seg000:0000000A db 0CDh ; ? seg000:0000000B db 0CDh ; ? seg000:0000000C db 0CDh ; ? seg000:0000000D db 0CDh ; ? seg000:0000000E db 0CDh ; ? seg000:0000000F db 0CDh ; ? seg000:00000010 db 0CDh ; ? seg000:00000011 db 0CDh ; ? seg000:00000012 db 0CDh ; ? seg000:00000013 db 0CDh ; ? seg000:00000014 db 0CDh ; ? seg000:00000015 db 0CDh ; ? seg000:00000016 db 0CDh ; ? seg000:00000017 db 0CDh ; ? seg000:00000018 db 0CDh ; ? seg000:00000019 db 0CDh ; ? seg000:0000001A db 0CDh ; ? seg000:0000001B db 0CDh ; ? seg000:0000001C db 0CDh ; ? seg000:0000001D db 0CDh ; ? seg000:0000001E db 0CDh ; ? seg000:0000001F db 0CDh ; ? seg000:00000020 db 0CDh ; ? seg000:00000021 db 0CDh ; ? seg000:00000022 db 0CDh ; ? seg000:00000023 db 0CDh ; ? seg000:00000024 db 0CDh ; ? seg000:00000025 db 0CDh ; ? seg000:00000026 db 0CDh ; ? seg000:00000027 db 0CDh ; ? seg000:00000028 db 0CDh ; ? seg000:00000029 db 0CDh ; ? seg000:0000002A db 0CDh ; ? seg000:0000002B db 0CDh ; ? seg000:0000002C db 0CDh ; ? seg000:0000002D db 0CDh ; ? seg000:0000002E db 0CDh ; ? seg000:0000002F db 0CDh ; ? seg000:00000030 db 0CDh ; ? seg000:00000031 db 0CDh ; ? seg000:00000032 db 0CDh ; ? seg000:00000033 db 0CDh ; ? seg000:00000034 db 0CDh ; ? seg000:00000035 db 0CDh ; ? seg000:00000036 db 0CDh ; ? seg000:00000037 db 0CDh ; ? seg000:00000038 db 0CDh ; ? seg000:00000039 db 0CDh ; ? seg000:0000003A db 0CDh ; ? seg000:0000003B db 0CDh ; ? seg000:0000003C db 0CDh ; ? seg000:0000003D db 0CDh ; ? seg000:0000003E db 0CDh ; ? seg000:0000003F db 0CDh ; ? seg000:00000040 db 0CDh ; ? seg000:00000041 db 0CDh ; ? seg000:00000042 db 0CDh ; ? seg000:00000043 db 0CDh ; ? seg000:00000044 db 0CDh ; ? seg000:00000045 db 0CDh ; ? seg000:00000046 db 0CDh ; ? seg000:00000047 db 0CDh ; ? seg000:00000048 db 0CDh ; ? seg000:00000049 db 0CDh ; ? seg000:0000004A db 3Fh ; ? seg000:0000004A seg000 ends seg000:0000004A seg000:0000004A seg000:0000004A end ------------------------- 用DEBUG打开成下面 -n 1.txt -l -d 0AED:0100 C9 CD CD CD CD CD CD CD-CD CD CD CD CD CD CD CD ................ 0AED:0110 CD CD CD CD CD CD CD CD-CD CD CD CD CD CD CD CD ................ 0AED:0120 CD CD CD CD CD CD CD CD-CD CD CD CD CD CD CD CD ................ 0AED:0130 CD CD CD CD CD CD CD CD-CD CD CD CD CD CD CD CD ................ 0AED:0140 CD CD CD CD CD CD CD CD-CD CD 3F 21 E9 6A FA B4 ..........?!.j.. |
|
|
[求助]IDA反汇编后的问题
用IDA反汇编后: 1 请问下面的汉字 赏屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯屯是哪来的? 2 ( 8208.)是甚麽? 3 下载IDA没让我输入 MD5,为何有 Input MD5 ? .idata:01001000 ; |
|
|
学习notepad.exe
NTSD PING: Microsoft (R) Windows Debugger Version 6.9.0003.113 X86 Copyright (c) Microsoft Corporation. All rights reserved. CommandLine: ping Symbol search path is: *** Invalid *** **************************************************************************** * Symbol loading may be unreliable without a symbol search path. * * Use .symfix to have the debugger choose a symbol path. * * After setting your symbol path, use .reload to refresh symbol locations. * **************************************************************************** Executable search path is: ModLoad: 01000000 01008000 ping.exe ModLoad: 7c920000 7c9b4000 ntdll.dll ModLoad: 7c800000 7c91d000 C:\WINDOWS\system32\kernel32.dll ModLoad: 77be0000 77c38000 C:\WINDOWS\system32\msvcrt.dll ModLoad: 77da0000 77e49000 C:\WINDOWS\system32\ADVAPI32.dll ModLoad: 77e50000 77ee2000 C:\WINDOWS\system32\RPCRT4.dll ModLoad: 77fc0000 77fd1000 C:\WINDOWS\system32\Secur32.dll ModLoad: 76d30000 76d48000 C:\WINDOWS\system32\iphlpapi.dll ModLoad: 77d10000 77da0000 C:\WINDOWS\system32\USER32.dll ModLoad: 77ef0000 77f37000 C:\WINDOWS\system32\GDI32.dll ModLoad: 71a20000 71a37000 C:\WINDOWS\system32\WS2_32.dll ModLoad: 71a10000 71a18000 C:\WINDOWS\system32\WS2HELP.dll (82c.d50): Break instruction exception - code 80000003 (first chance) eax=00191eb4 ebx=7ffde000 ecx=00000002 edx=00000004 esi=00191f48 edi=00191eb4 eip=7c921230 esp=0007fb20 ebp=0007fc94 iopl=0 nv up ei pl nz na po nc cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000202 *** ERROR: Symbol file could not be found. Defaulted to export symbols for ntdl l.dll - ntdll!DbgBreakPoint: 7c921230 cc int 3 0:000> g ModLoad: 5cc30000 5cc56000 C:\WINDOWS\system32\ShimEng.dll ModLoad: 58fb0000 5917a000 C:\WINDOWS\AppPatch\AcGenral.DLL ModLoad: 76b10000 76b3a000 C:\WINDOWS\system32\WINMM.dll ModLoad: 76990000 76acd000 C:\WINDOWS\system32\ole32.dll ModLoad: 770f0000 7717b000 C:\WINDOWS\system32\OLEAUT32.dll ModLoad: 77bb0000 77bc5000 C:\WINDOWS\system32\MSACM32.dll ModLoad: 77bd0000 77bd8000 C:\WINDOWS\system32\VERSION.dll ModLoad: 7d590000 7dd84000 C:\WINDOWS\system32\SHELL32.dll ModLoad: 77f40000 77fb6000 C:\WINDOWS\system32\SHLWAPI.dll ModLoad: 759d0000 75a7e000 C:\WINDOWS\system32\USERENV.dll ModLoad: 5adc0000 5adf7000 C:\WINDOWS\system32\UxTheme.dll ModLoad: 76300000 7631d000 C:\WINDOWS\system32\IMM32.DLL ModLoad: 62c20000 62c29000 C:\WINDOWS\system32\LPK.DLL ModLoad: 73fa0000 7400b000 C:\WINDOWS\system32\USP10.dll ModLoad: 77180000 77283000 C:\WINDOWS\WinSxS\x86_Microsoft.Windows.Common-Cont rols_6595b64144ccf1df_6.0.2600.2982_x-ww_ac3f9c03\comctl32.dll ModLoad: 5d170000 5d20a000 C:\WINDOWS\system32\comctl32.dll ModLoad: 00930000 00959000 C:\WINDOWS\system32\ClientMain.dll Usage: ping [-t] [-a] [-n count] [-l size] [-f] [-i TTL] [-v TOS] [-r count] [-s count] [[-j host-list] | [-k host-list]] [-w timeout] target_name Options: -t Ping the specified host until stopped. To see statistics and continue - type Control-Break; To stop - type Control-C. -a Resolve addresses to hostnames. -n count Number of echo requests to send. -l size Send buffer size. -f Set Don't Fragment flag in packet. -i TTL Time To Live. -v TOS Type Of Service. -r count Record route for count hops. -s count Timestamp for count hops. -j host-list Loose source route along host-list. -k host-list Strict source route along host-list. -w timeout Timeout in milliseconds to wait for each reply. eax=00000000 ebx=00000000 ecx=7c800000 edx=7c99c080 esi=7c92e88e edi=00000001 eip=7c92eb94 esp=0007f8e0 ebp=0007f9dc iopl=0 nv up ei pl zr na pe nc cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246 ntdll!KiFastSystemCallRet: 7c92eb94 c3 ret 0:000> ------------------------------ WINDBG PING INT3正好一个字符没显 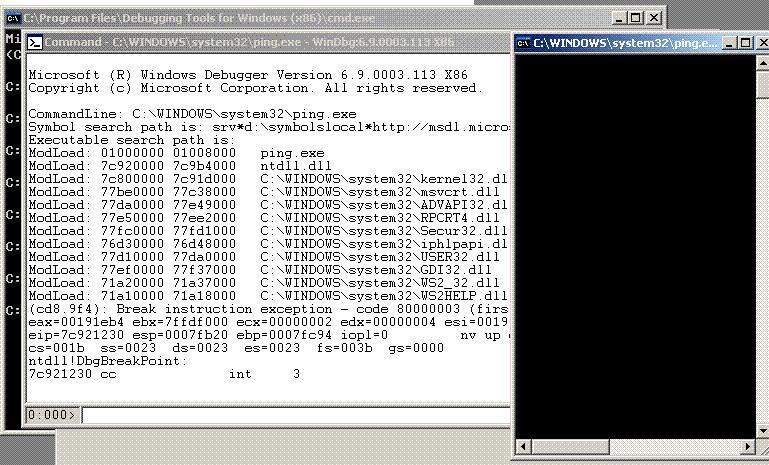 |
|
|
学习notepad.exe
confused: [/QUOTE][QUOTE=lilianjie;492429]用Dll函数查看器V2.0 WINDOWXP NTDLL.dll全部函数1315个! 0:000> wt Tracing ntdll!DbgBreakPoint to return address 7c941639 6 0 [ 0] ntdll!RtlInitializeSListHead...[/QUOTE]  |
|
|
学习notepad.exe
用Dll函数查看器V2.0 [I][QUOTE][/QUOTE]WINDOWXP NTDLL.dll[/I]全部函数1315个! 0:000> wt Tracing ntdll!DbgBreakPoint to return address 7c941639 6 0 [ 0] ntdll!RtlInitializeSListHead 16 0 [ 0] ntdll!RtlLookupElementGenericTable 10 0 [ 1] ntdll!RtlNtPathNameToDosPathName 31 0 [ 2] ntdll!RtlInitUnicodeString 19 31 [ 1] ntdll!RtlNtPathNameToDosPathName 3 0 [ 2] ntdll!LdrLoadDll 19 0 [ 3] ntdll!strchr 154 19 [ 2] ntdll!LdrLoadDll 12 0 [ 2] ntdll!RtlValidateUnicodeString 44 0 [ 3] ntdll!memmove 28 44 [ 2] ntdll!RtlValidateUnicodeString 31 0 [ 3] ntdll!RtlInitUnicodeString 37 75 [ 2] ntdll!RtlValidateUnicodeString 3 0 [ 3] ntdll!RtlValidateUnicodeString 19 0 [ 4] ntdll!strchr 135 19 [ 3] ntdll!RtlValidateUnicodeString 24 0 [ 4] ntdll!RtlFindActivationContextSectionString 24 0 [ 5] ntdll!RtlFormatCurrentUserKeyPath 41 24 [ 4] ntdll!RtlFindActivationContextSectionString 24 0 [ 5] ntdll!bsearch 30 0 [ 6] ntdll!bsearch 2 0 [ 6] ntdll!RtlQueryDepthSList 8 0 [ 6] ntdll!bsearch 51 0 [ 7] ntdll!bsearch 27 0 [ 8] ntdll!bsearch 13 0 [ 9] ntdll!bsearch 31 13 [ 8] ntdll!bsearch 2 0 [ 8] ntdll!RtlGetLongestNtPathLength 5 0 [ 8] ntdll!bsearch 75 51 [ 7] ntdll!bsearch 31 126 [ 6] ntdll!bsearch 29 189 [ 5] ntdll!bsearch 60 242 [ 4] ntdll!RtlFindActivationContextSectionString 35 0 [ 5] ntdll!RtlHashUnicodeString 190 0 [ 6] ntdll!RtlHashUnicodeString 44 190 [ 5] ntdll!RtlHashUnicodeString 2 0 [ 5] ntdll!RtlValidateUnicodeString 2 0 [ 5] ntdll!RtlHashUnicodeString 20 0 [ 5] ntdll!RtlValidateUnicodeString 22 0 [ 6] ntdll!bsearch 9 0 [ 7] ntdll!bsearch 3 0 [ 7] ntdll!RtlFindActivationContextSectionString 34 12 [ 6] ntdll!bsearch 24 46 [ 5] ntdll!RtlValidateUnicodeString 6 0 [ 5] ntdll!RtlHashUnicodeString 73 556 [ 4] ntdll!RtlFindActivationContextSectionString 27 0 [ 5] ntdll!RtlHashUnicodeString 41 0 [ 6] ntdll!bsearch 51 0 [ 7] ntdll!bsearch 28 0 [ 8] ntdll!bsearch 13 0 [ 9] ntdll!bsearch 32 13 [ 8] ntdll!bsearch 2 0 [ 8] ntdll!RtlGetLongestNtPathLength 5 0 [ 8] ntdll!bsearch 75 52 [ 7] ntdll!bsearch 65 127 [ 6] ntdll!bsearch 29 192 [ 5] ntdll!RtlHashUnicodeString 6 0 [ 5] ntdll!RtlValidateUnicodeString 8 0 [ 6] ntdll!RtlAddRefActivationContext 10 8 [ 5] ntdll!RtlValidateUnicodeString 3 0 [ 5] ntdll!RtlHashUnicodeString 75 798 [ 4] ntdll!RtlFindActivationContextSectionString 2 0 [ 4] ntdll!RtlValidateUnicodeString 14 0 [ 4] ntdll!RtlFindActivationContextSectionString 122 0 [ 5] ntdll!RtlHashUnicodeString 27 122 [ 4] ntdll!RtlFindActivationContextSectionString 27 0 [ 5] ntdll!RtlHashUnicodeString 32 0 [ 6] ntdll!bsearch 2 0 [ 6] ntdll!RtlGetLongestNtPathLength 5 0 [ 6] ntdll!bsearch 32 39 [ 5] ntdll!RtlHashUnicodeString 37 193 [ 4] ntdll!RtlFindActivationContextSectionString 147 1124 [ 3] ntdll!RtlValidateUnicodeString 10 0 [ 4] ntdll!RtlUpcaseUnicodeChar 164 1134 [ 3] ntdll!RtlValidateUnicodeString 93 0 [ 4] ntdll!RtlEqualUnicodeString 166 1227 [ 3] ntdll!RtlValidateUnicodeString 3 0 [ 3] ntdll!RtlPushFrame 10 0 [ 3] ntdll!RtlValidateUnicodeString 68 0 [ 4] ntdll!RtlEqualUnicodeString 12 68 [ 3] ntdll!RtlValidateUnicodeString 3 0 [ 3] ntdll!RtlPushFrame 10 0 [ 3] ntdll!RtlValidateUnicodeString 93 0 [ 4] ntdll!RtlEqualUnicodeString 12 93 [ 3] ntdll!RtlValidateUnicodeString 7 0 [ 3] ntdll!RtlPushFrame 5 0 [ 3] ntdll!RtlValidateUnicodeString 5 0 [ 4] ntdll!wcslen 6 5 [ 3] ntdll!RtlValidateUnicodeString 9 0 [ 4] ntdll!strchr 7 14 [ 3] ntdll!RtlValidateUnicodeString 49 1687 [ 2] ntdll!RtlValidateUnicodeString 3 0 [ 3] ntdll!snwprintf 19 0 [ 4] ntdll!strchr 12 19 [ 3] ntdll!snwprintf 3 0 [ 4] ntdll!snwprintf 144 22 [ 3] ntdll!snwprintf 35 0 [ 4] ntdll!LdrQueryImageFileExecutionOptions 3 0 [ 5] ntdll!snwprintf 39 3 [ 4] ntdll!LdrQueryImageFileExecutionOptions 31 0 [ 5] ntdll!RtlInitUnicodeString 56 34 [ 4] ntdll!LdrQueryImageFileExecutionOptions 24 0 [ 5] ntdll!RtlFindActivationContextSectionString 24 0 [ 6] ntdll!RtlFormatCurrentUserKeyPath 41 24 [ 5] ntdll!RtlFindActivationContextSectionString 24 0 [ 6] ntdll!bsearch 30 0 [ 7] ntdll!bsearch 2 0 [ 7] ntdll!RtlQueryDepthSList 8 0 [ 7] ntdll!bsearch 51 0 [ 8] ntdll!bsearch 27 0 [ 9] ntdll!bsearch 13 0 [ 10] ntdll!bsearch 31 13 [ 9] ntdll!bsearch 2 0 [ 9] ntdll!RtlGetLongestNtPathLength 5 0 [ 9] ntdll!bsearch 75 51 [ 8] ntdll!bsearch 31 126 [ 7] ntdll!bsearch 29 189 [ 6] ntdll!bsearch 60 242 [ 5] ntdll!RtlFindActivationContextSectionString 35 0 [ 6] ntdll!RtlHashUnicodeString 190 0 [ 7] ntdll!RtlHashUnicodeString 44 190 [ 6] ntdll!RtlHashUnicodeString 2 0 [ 6] ntdll!RtlValidateUnicodeString 2 0 [ 6] ntdll!RtlHashUnicodeString 20 0 [ 6] ntdll!RtlValidateUnicodeString 22 0 [ 7] ntdll!bsearch 9 0 [ 8] ntdll!bsearch 3 0 [ 8] ntdll!RtlFindActivationContextSectionString 34 12 [ 7] ntdll!bsearch 24 46 [ 6] ntdll!RtlValidateUnicodeString 6 0 [ 6] ntdll!RtlHashUnicodeString 73 556 [ 5] ntdll!RtlFindActivationContextSectionString 27 0 [ 6] ntdll!RtlHashUnicodeString 41 0 [ 7] ntdll!bsearch 51 0 [ 8] ntdll!bsearch 28 0 [ 9] ntdll!bsearch 13 0 [ 10] ntdll!bsearch 32 13 [ 9] ntdll!bsearch 2 0 [ 9] ntdll!RtlGetLongestNtPathLength 5 0 [ 9] ntdll!bsearch 75 52 [ 8] ntdll!bsearch 65 127 [ 7] ntdll!bsearch 29 192 [ 6] ntdll!RtlHashUnicodeString 6 0 [ 6] ntdll!RtlValidateUnicodeString 8 0 [ 7] ntdll!RtlAddRefActivationContext 10 8 [ 6] ntdll!RtlValidateUnicodeString 3 0 [ 6] ntdll!RtlHashUnicodeString 75 798 [ 5] ntdll!RtlFindActivationContextSectionString 2 0 [ 5] ntdll!RtlValidateUnicodeString 14 0 [ 5] ntdll!RtlFindActivationContextSectionString 122 0 [ 6] ntdll!RtlHashUnicodeString 27 122 [ 5] ntdll!RtlFindActivationContextSectionString 27 0 [ 6] ntdll!RtlHashUnicodeString 32 0 [ 7] ntdll!bsearch 2 0 [ 7] ntdll!RtlGetLongestNtPathLength 5 0 [ 7] ntdll!bsearch 32 39 [ 6] ntdll!RtlHashUnicodeString 37 193 [ 5] ntdll!RtlFindActivationContextSectionString 70 1139 [ 4] ntdll!LdrQueryImageFileExecutionOptions 21 0 [ 5] ntdll!snwprintf 3 0 [ 6] ntdll!RtlAllocateHeap 19 0 [ 7] ntdll!strchr 14 19 [ 6] ntdll!RtlAllocateHeap 4 0 [ 6] ntdll!wcsncat 3 0 [ 7] ntdll!wcsncat 19 0 [ 8] ntdll!strchr 13 19 [ 7] ntdll!wcsncat 6 0 [ 7] ntdll!RtlInitializeSListHead 3 0 [ 8] ntdll!RtlpNtMakeTemporaryKey 19 0 [ 9] ntdll!strchr 17 19 [ 8] ntdll!RtlpNtMakeTemporaryKey 14 0 [ 9] ntdll!RtlUnicodeToMultiByteSize 39 33 [ 8] ntdll!RtlpNtMakeTemporaryKey 11 0 [ 9] ntdll!RtlEnterCriticalSection 44 44 [ 8] ntdll!RtlpNtMakeTemporaryKey 15 0 [ 9] ntdll!RtlpNtMakeTemporaryKey 10 0 [ 10] ntdll!RtlpNtMakeTemporaryKey 27 10 [ 9] ntdll!RtlpNtMakeTemporaryKey 48 81 [ 8] ntdll!RtlpNtMakeTemporaryKey 3 0 [ 9] ntdll!wcsncat 19 0 [ 10] ntdll!strchr 13 19 [ 9] ntdll!wcsncat 2 0 [ 9] ntdll!RtlInitializeSListHead 55 0 [ 9] ntdll!wcsncat 18 0 [ 9] ntdll!RtlSetUserValueHeap 7 0 [ 9] ntdll!wcsncat 7 0 [ 9] ntdll!RtlSetUserValueHeap 15 0 [ 9] ntdll!wcsncat 17 0 [ 10] ntdll!wcsncpy 25 17 [ 9] ntdll!wcsncat 10 0 [ 9] ntdll!RtlInitializeSListHead 3498 0 [ 10] ntdll!RtlCompareMemoryUlong 14 3498 [ 9] ntdll!RtlInitializeSListHead 32 0 [ 9] ntdll!wcsncat 6 0 [ 9] ntdll!RtlSetUserValueHeap 7 0 [ 9] ntdll!RtlInitializeSListHead |
|
|
学习notepad.exe
用NTSD 符号表不行? NTSD 的lm命令 0:000> lm start end module name 01000000 01013000 notepad (deferred) 72f70000 72f96000 WINSPOOL (deferred) 76320000 76367000 comdlg32 (deferred) 77180000 77283000 COMCTL32 (deferred) 77be0000 77c38000 msvcrt (deferred) 77d10000 77da0000 USER32 (deferred) 77da0000 77e49000 ADVAPI32 (deferred) 77e50000 77ee2000 RPCRT4 (deferred) 77ef0000 77f37000 GDI32 (deferred) 77f40000 77fb6000 SHLWAPI (deferred) 77fc0000 77fd1000 Secur32 (deferred) 7c800000 7c91d000 kernel32 (deferred) 7c920000 7c9b4000 ntdll (export symbols) C:\WINDOWS\system32\ntdll. dll 7d590000 7dd84000 SHELL32 (deferred) ======================= WINDBG的lm命令: 0:000> lm start end module name 01000000 01013000 notepad (pdb symbols) d:\symbolslocal\notepad.pdb\F679AEF8BE1F44CAB4CBC4B52D77241B1\notepad.pdb 72f70000 72f96000 WINSPOOL (pdb symbols) d:\symbolslocal\winspool.pdb\97A6ECC94EA7450CA7D375BD9DFFCA5E2\winspool.pdb 76320000 76367000 comdlg32 (pdb symbols) d:\symbolslocal\comdlg32.pdb\4FCBEAD63D7345998C1F92D8DBB0DC272\comdlg32.pdb 77180000 77283000 COMCTL32 (pdb symbols) d:\symbolslocal\MicrosoftWindowsCommon-Controls-6.0.2600.2982-comctl32.pdb\C0A72EE9578847AAB7770CF02FFED0941\MicrosoftWindowsCommon-Controls-6.0.2600.2982-comctl32.pdb 77be0000 77c38000 msvcrt (pdb symbols) d:\symbolslocal\msvcrt.pdb\A678F3C30DED426B839032B996987E381\msvcrt.pdb 77d10000 77da0000 USER32 (pdb symbols) d:\symbolslocal\user32.pdb\F049F32D0C8948C0B48F7A065FC5C1B12\user32.pdb 77da0000 77e49000 ADVAPI32 (pdb symbols) d:\symbolslocal\advapi32.pdb\455D6C5F184D45BBB5C5F30F829751142\advapi32.pdb 77e50000 77ee2000 RPCRT4 (pdb symbols) d:\symbolslocal\rpcrt4.pdb\2D7278066B8B4F0AAA1AB3E4F8CEA0DA2\rpcrt4.pdb 77ef0000 77f37000 GDI32 (pdb symbols) d:\symbolslocal\gdi32.pdb\9B3E80DB35BB40DB80025720CB72CF012\gdi32.pdb 77f40000 77fb6000 SHLWAPI (pdb symbols) d:\symbolslocal\shlwapi.pdb\C3BC8438C9E7452F871D9BF14476F7F62\shlwapi.pdb 77fc0000 77fd1000 Secur32 (pdb symbols) d:\symbolslocal\secur32.pdb\85DD72BF4CAD42EFB989699A8B082F1D2\secur32.pdb 7c800000 7c91d000 kernel32 (pdb symbols) d:\symbolslocal\kernel32.pdb\006D2240474D414087FF801C64935DDD2\kernel32.pdb 7c920000 7c9b4000 ntdll (pdb symbols) d:\symbolslocal\ntdll.pdb\36515FB5D04345E491F672FA2E2878C02\ntdll.pdb 7d590000 7dd84000 SHELL32 (pdb symbols) d:\symbolslocal\shell32.pdb\9A8D69139E21498F9FFDA33E5E27AE622\shell32.pdb wt命令好厉害: 0:000> wt Tracing ntdll!DbgBreakPoint to return address 7c941639 6 0 [ 0] ntdll!RtlInitializeSListHead 16 0 [ 0] ntdll!RtlLookupElementGenericTable 10 0 [ 1] ntdll!RtlNtPathNameToDosPathName 31 0 [ 2] ntdll!RtlInitUnicodeString 19 31 [ 1] ntdll!RtlNtPathNameToDosPathName 3 0 [ 2] ntdll!LdrLoadDll 19 0 [ 3] ntdll!strchr 154 19 [ 2] ntdll!LdrLoadDll 12 0 [ 2] ntdll!RtlValidateUnicodeString 44 0 [ 3] ntdll!memmove 28 44 [ 2] ntdll!RtlValidateUnicodeString 31 0 [ 3] ntdll!RtlInitUnicodeString 37 75 [ 2] ntdll!RtlValidateUnicodeString 3 0 [ 3] ntdll!RtlValidateUnicodeString 19 0 [ 4] ntdll!strchr 135 19 [ 3] ntdll!RtlValidateUnicodeString 24 0 [ 4] ntdll!RtlFindActivationContextSectionString 24 0 [ 5] ntdll!RtlFormatCurrentUserKeyPath 41 24 [ 4] ntdll!RtlFindActivationContextSectionString 24 0 [ 5] ntdll!bsearch 30 0 [ 6] ntdll!bsearch 2 0 [ 6] ntdll!RtlQueryDepthSList 8 0 [ 6] ntdll!bsearch 51 0 [ 7] ntdll!bsearch 27 0 [ 8] ntdll!bsearch 13 0 [ 9] ntdll!bsearch 31 13 [ 8] ntdll!bsearch 2 0 [ 8] ntdll!RtlGetLongestNtPathLength 5 0 [ 8] ntdll!bsearch 75 51 [ 7] ntdll!bsearch 31 126 [ 6] ntdll!bsearch 29 189 [ 5] ntdll!bsearch 60 242 [ 4] ntdll!RtlFindActivationContextSectionString 35 0 [ 5] ntdll!RtlHashUnicodeString 190 0 [ 6] ntdll!RtlHashUnicodeString 44 190 [ 5] ntdll!RtlHashUnicodeString 2 0 [ 5] ntdll!RtlValidateUnicodeString 2 0 [ 5] ntdll!RtlHashUnicodeString 20 0 [ 5] ntdll!RtlValidateUnicodeString 22 0 [ 6] ntdll!bsearch 9 0 [ 7] ntdll!bsearch 3 0 [ 7] ntdll!RtlFindActivationContextSectionString 34 12 [ 6] ntdll!bsearch 24 46 [ 5] ntdll!RtlValidateUnicodeString 6 0 [ 5] ntdll!RtlHashUnicodeString 73 556 [ 4] ntdll!RtlFindActivationContextSectionString 27 0 [ 5] ntdll!RtlHashUnicodeString 41 0 [ 6] ntdll!bsearch 51 0 [ 7] ntdll!bsearch 28 0 [ 8] ntdll!bsearch 13 0 [ 9] ntdll!bsearch 32 13 [ 8] ntdll!bsearch 2 0 [ 8] ntdll!RtlGetLongestNtPathLength 5 0 [ 8] ntdll!bsearch 75 52 [ 7] ntdll!bsearch 65 127 [ 6] ntdll!bsearch 29 192 [ 5] ntdll!RtlHashUnicodeString 6 0 [ 5] ntdll!RtlValidateUnicodeString 8 0 [ 6] ntdll!RtlAddRefActivationContext 10 8 [ 5] ntdll!RtlValidateUnicodeString 3 0 [ 5] ntdll!RtlHashUnicodeString 75 798 [ 4] ntdll!RtlFindActivationContextSectionString 2 0 [ 4] ntdll!RtlValidateUnicodeString 14 0 [ 4] ntdll!RtlFindActivationContextSectionString 122 0 [ 5] ntdll!RtlHashUnicodeString 27 122 [ 4] ntdll!RtlFindActivationContextSectionString 27 0 [ 5] ntdll!RtlHashUnicodeString 32 0 [ 6] ntdll!bsearch 2 0 [ 6] ntdll!RtlGetLongestNtPathLength 5 0 [ 6] ntdll!bsearch 32 39 [ 5] ntdll!RtlHashUnicodeString 37 193 [ 4] ntdll!RtlFindActivationContextSectionString 147 1124 [ 3] ntdll!RtlValidateUnicodeString 10 0 [ 4] ntdll!RtlUpcaseUnicodeChar 164 1134 [ 3] ntdll!RtlValidateUnicodeString 93 0 [ 4] ntdll!RtlEqualUnicodeString 166 1227 [ 3] ntdll!RtlValidateUnicodeString 3 0 [ 3] ntdll!RtlPushFrame 10 0 [ 3] ntdll!RtlValidateUnicodeString 68 0 [ 4] ntdll!RtlEqualUnicodeString 12 68 [ 3] ntdll!RtlValidateUnicodeString 3 0 [ 3] ntdll!RtlPushFrame 10 0 [ 3] ntdll!RtlValidateUnicodeString 93 0 [ 4] ntdll!RtlEqualUnicodeString 12 93 [ 3] ntdll!RtlValidateUnicodeString 7 0 [ 3] ntdll!RtlPushFrame 5 0 [ 3] ntdll!RtlValidateUnicodeString 5 0 [ 4] ntdll!wcslen 6 5 [ 3] ntdll!RtlValidateUnicodeString 9 0 [ 4] ntdll!strchr 7 14 [ 3] ntdll!RtlValidateUnicodeString 49 1687 [ 2] ntdll!RtlValidateUnicodeString 3 0 [ 3] ntdll!snwprintf 19 0 [ 4] ntdll!strchr 12 19 [ 3] ntdll!snwprintf 3 0 [ 4] ntdll!snwprintf 144 22 [ 3] ntdll!snwprintf 35 0 [ 4] ntdll!LdrQueryImageFileExecutionOptions 3 0 [ 5] ntdll!snwprintf 39 3 [ 4] ntdll!LdrQueryImageFileExecutionOptions 31 0 [ 5] ntdll!RtlInitUnicodeString 56 34 [ 4] ntdll!LdrQueryImageFileExecutionOptions 24 0 [ 5] ntdll!RtlFindActivationContextSectionString 24 0 [ 6] ntdll!RtlFormatCurrentUserKeyPath 41 24 [ 5] ntdll!RtlFindActivationContextSectionString 24 0 [ 6] ntdll!bsearch 30 0 [ 7] ntdll!bsearch 2 0 [ 7] ntdll!RtlQueryDepthSList 8 0 [ 7] ntdll!bsearch 51 0 [ 8] ntdll!bsearch 27 0 [ 9] ntdll!bsearch 13 0 [ 10] ntdll!bsearch 31 13 [ 9] ntdll!bsearch 2 0 [ 9] ntdll!RtlGetLongestNtPathLength 5 0 [ 9] ntdll!bsearch 75 51 [ 8] ntdll!bsearch 31 126 [ 7] ntdll!bsearch 29 189 [ 6] ntdll!bsearch 60 242 [ 5] ntdll!RtlFindActivationContextSectionString 35 0 [ 6] ntdll!RtlHashUnicodeString 190 0 [ 7] ntdll!RtlHashUnicodeString 44 190 [ 6] ntdll!RtlHashUnicodeString 2 0 [ 6] ntdll!RtlValidateUnicodeString 2 0 [ 6] ntdll!RtlHashUnicodeString 20 0 [ 6] ntdll!RtlValidateUnicodeString 22 0 [ 7] ntdll!bsearch 9 0 [ 8] ntdll!bsearch 3 0 [ 8] ntdll!RtlFindActivationContextSectionString 34 12 [ 7] ntdll!bsearch 24 46 [ 6] ntdll!RtlValidateUnicodeString 6 0 [ 6] ntdll!RtlHashUnicodeString 73 556 [ 5] ntdll!RtlFindActivationContextSectionString 27 0 [ 6] ntdll!RtlHashUnicodeString 41 0 [ 7] ntdll!bsearch 51 0 [ 8] ntdll!bsearch 28 0 [ 9] ntdll!bsearch 13 0 [ 10] ntdll!bsearch 32 13 [ 9] ntdll!bsearch 2 0 [ 9] ntdll!RtlGetLongestNtPathLength 5 0 [ 9] ntdll!bsearch 75 52 [ 8] ntdll!bsearch 65 127 [ 7] ntdll!bsearch 29 192 [ 6] ntdll!RtlHashUnicodeString 6 0 [ 6] ntdll!RtlValidateUnicodeString 8 0 [ 7] ntdll!RtlAddRefActivationContext 10 8 [ 6] ntdll!RtlValidateUnicodeString 3 0 [ 6] ntdll!RtlHashUnicodeString 75 798 [ 5] ntdll!RtlFindActivationContextSectionString 2 0 [ 5] ntdll!RtlValidateUnicodeString 14 0 [ 5] ntdll!RtlFindActivationContextSectionString 122 0 [ 6] ntdll!RtlHashUnicodeString 27 122 [ 5] ntdll!RtlFindActivationContextSectionString 27 0 [ 6] ntdll!RtlHashUnicodeString 32 0 [ 7] ntdll!bsearch 2 0 [ 7] ntdll!RtlGetLongestNtPathLength 5 0 [ 7] ntdll!bsearch 32 39 [ 6] ntdll!RtlHashUnicodeString 37 193 [ 5] ntdll!RtlFindActivationContextSectionString 70 1139 [ 4] ntdll!LdrQueryImageFileExecutionOptions 21 0 [ 5] ntdll!snwprintf 3 0 [ 6] ntdll!RtlAllocateHeap 19 0 [ 7] ntdll!strchr 14 19 [ 6] ntdll!RtlAllocateHeap 4 0 [ 6] ntdll!wcsncat 3 0 [ 7] ntdll!wcsncat 19 0 [ 8] ntdll!strchr 13 19 [ 7] ntdll!wcsncat 6 0 [ 7] ntdll!RtlInitializeSListHead 3 0 [ 8] ntdll!RtlpNtMakeTemporaryKey 19 0 [ 9] ntdll!strchr 17 19 [ 8] ntdll!RtlpNtMakeTemporaryKey 14 0 [ 9] ntdll!RtlUnicodeToMultiByteSize 39 33 [ 8] ntdll!RtlpNtMakeTemporaryKey 11 0 [ 9] ntdll!RtlEnterCriticalSection 44 44 [ 8] ntdll!RtlpNtMakeTemporaryKey 15 0 [ 9] ntdll!RtlpNtMakeTemporaryKey 10 0 [ 10] ntdll!RtlpNtMakeTemporaryKey 27 10 [ 9] ntdll!RtlpNtMakeTemporaryKey 48 81 [ 8] ntdll!RtlpNtMakeTemporaryKey 3 0 [ 9] ntdll!wcsncat 19 0 [ 10] ntdll!strchr 13 19 [ 9] ntdll!wcsncat 2 0 [ 9] ntdll!RtlInitializeSListHead 55 0 [ 9] ntdll!wcsncat 18 0 [ 9] ntdll!RtlSetUserValueHeap 7 0 [ 9] ntdll!wcsncat 7 0 [ 9] ntdll!RtlSetUserValueHeap 15 0 [ 9] ntdll!wcsncat 17 0 [ 10] ntdll!wcsncpy 25 17 [ 9] ntdll!wcsncat 10 0 [ 9] ntdll!RtlInitializeSListHead 3498 0 [ 10] ntdll!RtlCompareMemoryUlong 14 3498 [ 9] ntdll!RtlInitializeSListHead 32 0 [ 9] ntdll!wcsncat 6 0 [ 9] ntdll!RtlSetUserValueHeap 7 0 [ 9] ntdll!RtlInitializeSListHead 。。。。。。。。。。。。。。。。 。。。。。。。。。。。。。。 。。。。。。。。。。。。 kernel32!lstrcmpW 188 2 93 38 kernel32!lstrcmpiW 160 22 22 22 kernel32!lstrcpyW 87 12 12 12 kernel32!lstrcpyn 10 1 8 3 kernel32!lstrcpynW 3 5 331 186 kernel32!lstrlenW 45 12 12 12 msvcrt!_STRINGTOLD 2 4 8 6 msvcrt!__unguarded_readlc_active_add_func 3 4 30 16 msvcrt!_crtCompareStringA 1 141 141 141 msvcrt!_crtLCMapStringA 2 1654 1667 1660 msvcrt!_crtLCMapStringW 1 11 11 11 msvcrt!_dllonexit 162 2 46 14 msvcrt!_getmainargs 3 6 69 29 msvcrt!_p__winver 1 8 8 8 msvcrt!_threadhandle 1 31 31 31 msvcrt!_unDNameEx 1 5 5 5 msvcrt!beginthreadex 1 330 330 330 msvcrt!bsearch 1 4197 4197 4197 msvcrt!c_exit 5 8 16 14 msvcrt!calloc 3 4 92 46 msvcrt!clock 1 24 24 24 msvcrt!control87 1 24 24 24 msvcrt!controlfp 1 12 12 12 msvcrt!expand 3 21 32 26 msvcrt!fpreset 2 36 47 41 msvcrt!free 259 4 31 14 msvcrt!get_sbh_threshold 120 16 475 31 msvcrt!getenv 2 4 16 10 msvcrt!initterm 11 24 2082 231 msvcrt!lock 269 10 14674 68 msvcrt!malloc 41 12 15 12 msvcrt!mbsnbicoll 1 24 24 24 msvcrt!modf 6 5 13 7 msvcrt!msize 162 4 29 16 msvcrt!operator delete 15 5 5 5 msvcrt!operator new 35 10 10 10 msvcrt!realloc 4 4 399 131 msvcrt!set_sbh_threshold 77 121 280 217 msvcrt!setlocale 2 66 66 66 msvcrt!setmbcp 3 4 3691 1233 msvcrt!strerror 739 4 4116 17 msvcrt!unlock 259 8 8 8 msvcrt!wcscat 1 212 212 212 msvcrt!wcscpy 31 16 440 137 msvcrt!wcsicmp 1 448 448 448 msvcrt!wcslen 24 64 279 125 msvcrt!wcsncpy 4 38 198 95 msvcrt!write 5 4 3572 1011 msvcrt!wsplitpath 1 418 418 418 msvcrt!yn 2 12 36 24 ntdll!CsrAllocateCaptureBuffer 3 35 38 37 ntdll!CsrAllocateMessagePointer 36 2 304 55 ntdll!CsrCaptureMessageMultiUnicodeStringsInPla 6 28 91 49 ntdll!CsrCaptureMessageString 4 35 35 35 ntdll!CsrClientCallServer 174 6 231 30 ntdll!CsrClientConnectToServer 1 82 82 82 ntdll!CsrFreeCaptureBuffer 6 9 28 16 ntdll!DbgPrintEx 8 12 12 12 ntdll!KiFastSystemCall 979 2 2 2 ntdll!KiUserCallbackDispatcher 1 5 5 5 ntdll!LdrAccessOutOfProcessResource 1 21 21 21 ntdll!LdrAccessResource 77 4 6 5 ntdll!LdrAlternateResourcesEnabled 41 4 11 10 ntdll!LdrCreateOutOfProcessImage 1 40 40 40 ntdll!LdrDestroyOutOfProcessImage 1 24 24 24 ntdll!LdrDisableThreadCalloutsForDll 32 3 29 17 ntdll!LdrEnumerateLoadedModules 1 49 49 49 ntdll!LdrFindCreateProcessManifest 2 5 37 21 ntdll!LdrFindResourceDirectory_U 143 1 289 29 ntdll!LdrFindResourceEx_U 1 11 11 11 ntdll!LdrFindResource_U 36 11 11 11 ntdll!LdrGetDllHandle 21 11 11 11 ntdll!LdrGetDllHandleEx 54 3 372 95 ntdll!LdrGetProcedureAddress 4573 3 1139 87 ntdll!LdrInitializeThunk 22 16 16 16 ntdll!LdrLoadAlternateResourceModule 38 22 22 22 ntdll!LdrLoadDll 88 3 1284 64 ntdll!LdrLockLoaderLock 16 26 26 26 ntdll!LdrQueryImageFileExecutionOptions 395 3 3796 180 ntdll!LdrUnloadAlternateResourceModule 1 6 6 6 ntdll!LdrUnloadDll 4 8 8 8 ntdll!LdrUnlockLoaderLock 16 12 12 12 ntdll!NtAddAtom 2 1 3 2 ntdll!NtCallbackReturn 1 3 3 3 ntdll!NtClose 226 1 3 2 ntdll!NtCreateFile 14 1 3 2 ntdll!NtCreateKey 10 1 3 2 ntdll!NtCreateSection 34 1 3 2 ntdll!NtCreateSemaphore 10 1 3 2 ntdll!NtDeviceIoControlFile 2 1 3 2 ntdll!NtDuplicateObject 22 1 3 2 ntdll!NtFlushInstructionCache 98 1 3 2 ntdll!NtFreeVirtualMemory 2 1 3 2 ntdll!NtOpenDirectoryObject 2 1 3 2 ntdll!NtOpenFile 40 1 3 2 ntdll!NtOpenKey 218 1 3 2 ntdll!NtOpenProcessToken 6 1 3 2 ntdll!NtOpenSection 22 1 3 2 ntdll!NtOpenThreadTokenEx 14 1 3 2 ntdll!NtQueryAttributesFile 36 1 3 2 ntdll!NtQueryDebugFilterState 16 1 3 2 ntdll!NtQueryDefaultUILanguage 6 1 3 2 ntdll!NtQueryInformationFile 6 1 3 2 ntdll!NtQueryKey 20 1 3 2 ntdll!NtQueryPerformanceCounter 6 1 3 2 ntdll!NtQuerySystemInformation 46 1 3 2 ntdll!NtQueryTimerResolution 2 1 3 2 ntdll!NtRequestWaitReplyPort 6 1 3 2 ntdll!NtUnmapViewOfSection 18 1 3 2 ntdll!RtlAcquirePebLock 155 14 14 14 ntdll!RtlAcquireResourceExclusive 2 11 27 19 ntdll!RtlActivateActivationContext 8 22 58 38 ntdll!RtlActivateActivationContextEx 9 8 273 128 ntdll!RtlActivateActivationContextUnsafeFast 160 20 20 20 ntdll!RtlAddAccessAllowedAce 7 12 12 12 ntdll!RtlAddAce 1 29 29 29 ntdll!RtlAddRefActivationContext 253 2 8 7 ntdll!RtlAddressInSectionTable 3 16 16 16 ntdll!RtlAllocateAndInitializeSid 16 8 42 30 ntdll!RtlAllocateHandle 2 8 11 9 ntdll!RtlAllocateHeap 1760 3 22 14 ntdll!RtlAnsiCharToUnicodeChar 8 34 34 34 ntdll!RtlAnsiStringToUnicodeString 695 8 1067 85 ntdll!RtlAppendPathElement 12 3 11 7 ntdll!RtlAppendUnicodeStringToString 99 40 40 40 ntdll!RtlAppendUnicodeToString 65 43 43 43 ntdll!RtlCharToInteger 2 8 13 10 ntdll!RtlCompareMemory 190 18 18 18 ntdll!RtlCompareMemoryUlong 666 11 7782 707 ntdll!RtlCompareUnicodeString 372 2 319 56 ntdll!RtlConvertSidToUnicodeString 49 63 470 163 ntdll!RtlCopySid 7 16 16 16 ntdll!RtlCopyUnicodeString 7 57 57 57 ntdll!RtlCreateAcl 4 24 24 24 ntdll!RtlCreateActivationContext 4 62 112 87 ntdll!RtlCreateHeap 92 2 1055 138 ntdll!RtlCreateSecurityDescriptor 4 19 19 19 ntdll!RtlCreateUnicodeStringFromAsciiz 6 18 18 18 ntdll!RtlDeactivateActivationContext 4 60 60 60 ntdll!RtlDeactivateActivationContextUnsafeFast 160 15 15 15 ntdll!RtlDecodePointer 2 5 5 5 ntdll!RtlDeleteCriticalSection 373 5 27 12 ntdll!RtlDetermineDosPathNameType_U 516 2 1724 148 ntdll!RtlDoesFileExists_U 119 2 23 6 ntdll!RtlDosApplyFileIsolationRedirection_Ustr 475 7 182 132 ntdll!RtlDosPathNameToNtPathName_U 133 2 30 14 ntdll!RtlDosSearchPath_U 41 23 737 160 ntdll!RtlDosSearchPath_Ustr 4 2 92 25 ntdll!RtlDowncaseUnicodeString 429 2 43 13 ntdll!RtlEncodePointer 4 15 15 15 ntdll!RtlEncodeSystemPointer 158 7 7 7 ntdll!RtlEnterCriticalSection 1514 11 12 11 ntdll!RtlEqualUnicodeString 891 18 1583 88 ntdll!RtlExpandEnvironmentStrings_U 18 2 6639 2947 ntdll!RtlFillMemoryUlong 1064 8 7779 472 ntdll!RtlFindActivationContextSectionString 714 3 75 41 ntdll!RtlFindCharInUnicodeString 255 7 127 90 ntdll!RtlFindClearBits 31 5 98 47 ntdll!RtlFindClearBitsAndSet 17 19 19 19 ntdll!RtlFirstFreeAce 17 11 69 38 ntdll!RtlFormatCurrentUserKeyPath 287 24 90 34 ntdll!RtlFreeAnsiString 516 11 17 11 ntdll!RtlFreeHeap 374 2 20 11 ntdll!RtlFreeSid 7 15 15 15 ntdll!RtlGetActiveActivationContext 114 2 329 95 ntdll!RtlGetCurrentDirectory_U 1 34 34 34 ntdll!RtlGetFrame 4 2 14 8 ntdll!RtlGetFullPathName_U 29 4 22 14 ntdll!RtlGetLastWin32Error 133 3 3 3 ntdll!RtlGetLengthWithoutLastFullDosOrNtPathEle 6 10 304 109 ntdll!RtlGetLongestNtPathLength 1010 2 23 6 ntdll!RtlGetNtGlobalFlags 1552 4 4 4 ntdll!RtlGetNtProductType 15 12 94 44 ntdll!RtlGetNtVersionNumbers 10 2 18 6 ntdll!RtlGetVersion 12 47 67 62 ntdll!RtlHashUnicodeString 2766 2 469 47 ntdll!RtlImageDirectoryEntryToData 1053 2 23 21 ntdll!RtlImageNtHeader 289 5 5 5 ntdll!RtlImageRvaToSection 62 3 507 177 ntdll!RtlImageRvaToVa 12 2 2 2 ntdll!RtlInitAnsiString 285 9 80 30 ntdll!RtlInitCodePageTable 3 33 126 86 ntdll!RtlInitString 92 26 55 35 ntdll!RtlInitUnicodeString 505 9 211 39 ntdll!RtlInitUnicodeStringEx 142 23 23 23 ntdll!RtlInitializeCriticalSection 385 2 43 10 ntdll!RtlInitializeCriticalSectionAndSpinCount 324 16 35 25 ntdll!RtlInitializeGenericTable 2 22 22 22 ntdll!RtlInitializeHandleTable 57 3 4152 77 ntdll!RtlInitializeResource 2 62 62 62 ntdll!RtlInitializeSListHead 4196 2 567 15 ntdll!RtlInitializeSid 9 23 81 29 ntdll!RtlIsDosDeviceName_U 1 16 16 16 ntdll!RtlIsValidHandle 991 3 20 10 ntdll!RtlLeaveCriticalSection 1514 6 8 7 ntdll!RtlLengthSid 7 8 8 8 ntdll!RtlLockHeap 20 25 25 25 ntdll!RtlLogStackBackTrace 162 9 9 9 ntdll!RtlLookupElementGenericTable 1 70 70 70 ntdll!RtlMultiAppendUnicodeStringBuffer 400 2 600 45 ntdll!RtlMultiByteToUnicodeN 488 6 10 8 ntdll!RtlMultiByteToUnicodeSize 444 3 7 5 ntdll!RtlNtPathNameToDosPathName 2 32 100 66 ntdll!RtlNtStatusToDosError 132 14 14 14 ntdll!RtlNtStatusToDosErrorNoTeb 137 5 540 142 ntdll!RtlOemStringToUnicodeSize 222 14 14 14 ntdll!RtlOpenCurrentUser 7 37 37 37 ntdll!RtlPrefixUnicodeString 4 13 46 30 ntdll!RtlPushFrame 134 2 121 5 ntdll!RtlQueryDepthSList 244 2 2 2 ntdll!RtlQueryEnvironmentVariable_U 41 7 118 36 ntdll!RtlQueueWorkItem 154 2 27 14 ntdll!RtlReAllocateHeap 66 2 109 46 ntdll!RtlReadMemoryStream 6 7 7 7 ntdll!RtlReadOutOfProcessMemoryStream 1 24 24 24 ntdll!RtlReleaseActivationContext 1 21 21 21 ntdll!RtlReleasePebLock 155 5 5 5 ntdll!RtlReleaseResource 2 5 10 7 ntdll!RtlRestoreLastWin32Error 139 8 8 8 ntdll!RtlSetBits 31 6 26 18 ntdll!RtlSetDaclSecurityDescriptor 4 25 25 25 ntdll!RtlSetGroupSecurityDescriptor 2 21 21 21 ntdll!RtlSetOwnerSecurityDescriptor 2 21 21 21 ntdll!RtlSetUserValueHeap 2067 2 784 13 ntdll!RtlSubAuthorityCountSid 29 2 6 2 ntdll!RtlSubAuthoritySid 224 2 2 2 ntdll!RtlTimeToSecondsSince1980 25 4 8 6 ntdll!RtlTimeToTimeFields 580 4 402 48 ntdll!RtlUnicodeStringToAnsiString 158 8 35 13 ntdll!RtlUnicodeStringToInteger 2 145 145 145 ntdll!RtlUnicodeToMultiByteN 108 6 10 8 ntdll!RtlUnicodeToMultiByteSize 821 4 14 12 ntdll!RtlUnlockHeap 20 25 25 25 ntdll!RtlUpcaseUnicodeChar 361 10 12 10 ntdll!RtlValidAcl 11 3 30 20 ntdll!RtlValidSid 28 7 22 18 ntdll!RtlValidateUnicodeString 1819 2 166 23 ntdll!RtlZeroHeap 190 27 27 27 ntdll!RtlpApplyLengthFunction 2 44 44 44 ntdll!RtlpNtMakeTemporaryKey 3936 3 96 27 ntdll!RtlxUnicodeStringToOemSize 54 14 14 14 ntdll!ZwAccessCheck 4 1 3 2 ntdll!ZwAllocateVirtualMemory 60 1 3 2 ntdll!ZwCreateEvent 10 1 3 2 ntdll!ZwCreateMutant 2 1 3 2 ntdll!ZwEnumerateValueKey 110 1 3 2 ntdll!ZwMapViewOfSection 44 1 3 2 ntdll!ZwOpenEvent 2 1 3 2 ntdll!ZwOpenProcessTokenEx 14 1 3 2 ntdll!ZwProtectVirtualMemory 196 1 3 2 ntdll!ZwQueryDefaultLocale 76 1 3 2 ntdll!ZwQueryInformationProcess 14 1 3 2 ntdll!ZwQueryInformationToken 16 1 3 2 ntdll!ZwQueryInstallUILanguage 2 1 3 2 ntdll!ZwQuerySection 16 1 3 2 ntdll!ZwQueryValueKey 254 1 3 2 ntdll!ZwQueryVirtualMemory 8 1 3 2 ntdll!ZwSetInformationObject 2 1 3 2 ntdll!aulldvrm 3 31 31 31 ntdll!bsearch 4087 5 75 30 ntdll!iswdigit 1466 2 68 19 ntdll!mbstowcs 2 12 69 40 ntdll!memmove 362 26 99 43 ntdll!snwprintf 203 3 270 31 ntdll!strchr 10675 9 80 14 ntdll!strcmpi 135 49 130 67 ntdll!strncmp 322 28 38 36 ntdll!strnicmp 31 20 113 49 ntdll!swprintf 2 31 31 31 ntdll!towlower 6402 3 399 63 ntdll!vDbgPrintExWithPrefix 8 23 23 23 ntdll!wcscat 15 2 196 97 ntdll!wcschr 68 2 28 6 ntdll!wcscpy 108 40 520 283 ntdll!wcsicmp 38 31 469 58 ntdll!wcslen 1904 5 983 35 ntdll!wcslwr 1 117 117 117 ntdll!wcsncat 6032 2 5168 27 ntdll!wcsncmp 119 19 62 32 ntdll!wcsncpy 1802 2 331 21 ntdll!wcsnicmp 252 16 250 52 ntdll!wcsrchr 12 204 252 239 ntdll!wcsstr 10 2 229 70 ntdll!wcstol 13 3 5 3 ole32 5 24 24 24 ole32!CoRevokeClassObject 130 1 115 16 ole32!CoTaskMemAlloc 17 4 29 10 ole32!ComPs_NdrDllCanUnloadNow 45 4 19 10 979 system calls were executed Calls System Call 979 ntdll!KiFastSystemCall eax=00000000 ebx=00000000 ecx=00009308 edx=0007fa6e esi=7ffdd000 edi=7ffdf000 eip=7c941639 esp=0007fcb0 ebp=0007fd1c iopl=0 nv up ei pl zr na pe nc cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246 ntdll!RtlLookupElementGenericTable+0x80: 7c941639 8bf8 mov edi,eax 0:000> |
|
|
学习notepad.exe
Microsoft (R) Windows Debugger Version 6.9.0003.113 X86 Copyright (c) Microsoft Corporation. All rights reserved. CommandLine: notepad.exe Symbol search path is: *** Invalid *** **************************************************************************** * Symbol loading may be unreliable without a symbol search path. * * Use .symfix to have the debugger choose a symbol path. * * After setting your symbol path, use .reload to refresh symbol locations. * **************************************************************************** Executable search path is: ModLoad: 01000000 01013000 notepad.exe ModLoad: 7c920000 7c9b4000 ntdll.dll ModLoad: 7c800000 7c91d000 C:\WINDOWS\system32\kernel32.dll ModLoad: 76320000 76367000 C:\WINDOWS\system32\comdlg32.dll ModLoad: 77f40000 77fb6000 C:\WINDOWS\system32\SHLWAPI.dll ModLoad: 77da0000 77e49000 C:\WINDOWS\system32\ADVAPI32.dll ModLoad: 77e50000 77ee2000 C:\WINDOWS\system32\RPCRT4.dll ModLoad: 77fc0000 77fd1000 C:\WINDOWS\system32\Secur32.dll ModLoad: 77ef0000 77f37000 C:\WINDOWS\system32\GDI32.dll ModLoad: 77d10000 77da0000 C:\WINDOWS\system32\USER32.dll ModLoad: 77be0000 77c38000 C:\WINDOWS\system32\msvcrt.dll ModLoad: 77180000 77283000 C:\WINDOWS\WinSxS\x86_Microsoft.Windows.Common-Cont rols_6595b64144ccf1df_6.0.2600.2982_x-ww_ac3f9c03\COMCTL32.dll ModLoad: 7d590000 7dd84000 C:\WINDOWS\system32\SHELL32.dll ModLoad: 72f70000 72f96000 C:\WINDOWS\system32\WINSPOOL.DRV (9a4.c58): Break instruction exception - code 80000003 (first chance) eax=001a1eb4 ebx=7ffdd000 ecx=00000007 edx=00000080 esi=001a1f48 edi=001a1eb4 eip=7c921230 esp=0007fb20 ebp=0007fc94 iopl=0 nv up ei pl nz na po nc cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000202 *** ERROR: Symbol file could not be found. Defaulted to export symbols for ntdl l.dll - ntdll!DbgBreakPoint: 7c921230 cc int 3 0:000> |
|
|
学习notepad.exe
ntdll.dll ====WINXP 的,用NOTEPAD.exe打开,1000多个API? CsrAllocateCaptureBuffer CsrAllocateMessagePointer CsrCaptureMessageBuffer CsrCaptureMessageMultiUnicodeStringsInPlace CsrCaptureMessageString CsrCaptureTimeout CsrClientCallServer CsrClientConnectToServer CsrFreeCaptureBuffer CsrGetProcessId CsrIdentifyAlertableThread CsrNewThread CsrProbeForRead CsrProbeForWrite CsrSetPriorityClass DbgBreakPoint DbgPrint DbgPrintEx DbgPrintReturnControlC DbgPrompt DbgQueryDebugFilterState DbgSetDebugFilterState DbgUiConnectToDbg DbgUiContinue DbgUiConvertStateChangeStructure DbgUiDebugActiveProcess DbgUiGetThreadDebugObject DbgUiIssueRemoteBreakin DbgUiRemoteBreakin DbgUiSetThreadDebugObject DbgUiStopDebugging DbgUiWaitStateChange DbgUserBreakPoint KiFastSystemCall KiFastSystemCallRet KiIntSystemCall KiRaiseUserExceptionDispatcher KiUserApcDispatcher KiUserCallbackDispatcher KiUserExceptionDispatcher LdrAccessOutOfProcessResource LdrAccessResource LdrAddRefDll LdrAlternateResourcesEnabled LdrCreateOutOfProcessImage LdrDestroyOutOfProcessImage LdrDisableThreadCalloutsForDll LdrEnumResources LdrEnumerateLoadedModules LdrFindCreateProcessManifest LdrFindEntryForAddress LdrFindResourceDirectory_U LdrFindResourceEx_U LdrFindResource_U LdrFlushAlternateResourceModules LdrGetDllHandle LdrGetDllHandleEx LdrGetProcedureAddress LdrHotPatchRoutine LdrInitShimEngineDynamic LdrInitializeThunk LdrLoadAlternateResourceModule LdrLoadDll LdrLockLoaderLock LdrProcessRelocationBlock LdrQueryImageFileExecutionOptions LdrQueryProcessModuleInformation LdrSetAppCompatDllRedirectionCallback LdrSetDllManifestProber LdrShutdownProcess LdrShutdownThread LdrUnloadAlternateResourceModule LdrUnloadDll LdrUnlockLoaderLock LdrVerifyImageMatchesChecksum NlsAnsiCodePage NlsMbCodePageTag NlsMbOemCodePageTag NtAcceptConnectPort NtAccessCheck NtAccessCheckAndAuditAlarm NtAccessCheckByType NtAccessCheckByTypeAndAuditAlarm NtAccessCheckByTypeResultList NtAccessCheckByTypeResultListAndAuditAlarm NtAccessCheckByTypeResultListAndAuditAlarmByHandle NtAddAtom NtAddBootEntry NtAdjustGroupsToken NtAdjustPrivilegesToken NtAlertResumeThread NtAlertThread NtAllocateLocallyUniqueId NtAllocateUserPhysicalPages NtAllocateUuids NtAllocateVirtualMemory NtAreMappedFilesTheSame NtAssignProcessToJobObject NtCallbackReturn NtCancelDeviceWakeupRequest NtCancelIoFile NtCancelTimer NtClearEvent NtClose NtCloseObjectAuditAlarm NtCompactKeys NtCompareTokens NtCompleteConnectPort NtCompressKey NtConnectPort NtContinue NtCreateDebugObject NtCreateDirectoryObject NtCreateEvent NtCreateEventPair NtCreateFile NtCreateIoCompletion NtCreateJobObject NtCreateJobSet NtCreateKey NtCreateKeyedEvent NtCreateMailslotFile NtCreateMutant NtCreateNamedPipeFile NtCreatePagingFile NtCreatePort NtCreateProcess NtCreateProcessEx NtCreateProfile NtCreateSection NtCreateSemaphore NtCreateSymbolicLinkObject NtCreateThread NtCreateTimer NtCreateToken NtCreateWaitablePort NtCurrentTeb NtDebugActiveProcess NtDebugContinue NtDelayExecution NtDeleteAtom NtDeleteBootEntry NtDeleteFile NtDeleteKey NtDeleteObjectAuditAlarm NtDeleteValueKey NtDeviceIoControlFile NtDisplayString NtDuplicateObject NtDuplicateToken NtEnumerateBootEntries NtEnumerateKey NtEnumerateSystemEnvironmentValuesEx NtEnumerateValueKey NtExtendSection NtFilterToken NtFindAtom NtFlushBuffersFile NtFlushInstructionCache NtFlushKey NtFlushVirtualMemory NtFlushWriteBuffer NtFreeUserPhysicalPages NtFreeVirtualMemory NtFsControlFile NtGetContextThread NtGetDevicePowerState NtGetPlugPlayEvent NtGetWriteWatch NtImpersonateAnonymousToken NtImpersonateClientOfPort NtImpersonateThread NtInitializeRegistry NtInitiatePowerAction NtIsProcessInJob NtIsSystemResumeAutomatic NtListenPort NtLoadDriver NtLoadKey NtLoadKey2 NtLockFile NtLockProductActivationKeys NtLockRegistryKey NtLockVirtualMemory NtMakePermanentObject NtMakeTemporaryObject NtMapUserPhysicalPages NtMapUserPhysicalPagesScatter NtMapViewOfSection NtModifyBootEntry NtNotifyChangeDirectoryFile NtNotifyChangeKey NtNotifyChangeMultipleKeys NtOpenDirectoryObject NtOpenEvent NtOpenEventPair NtOpenFile NtOpenIoCompletion NtOpenJobObject NtOpenKey NtOpenKeyedEvent NtOpenMutant NtOpenObjectAuditAlarm NtOpenProcess NtOpenProcessToken NtOpenProcessTokenEx NtOpenSection NtOpenSemaphore NtOpenSymbolicLinkObject NtOpenThread NtOpenThreadToken NtOpenThreadTokenEx NtOpenTimer NtPlugPlayControl NtPowerInformation NtPrivilegeCheck NtPrivilegeObjectAuditAlarm NtPrivilegedServiceAuditAlarm NtProtectVirtualMemory NtPulseEvent NtQueryAttributesFile NtQueryBootEntryOrder NtQueryBootOptions NtQueryDebugFilterState NtQueryDefaultLocale NtQueryDefaultUILanguage NtQueryDirectoryFile NtQueryDirectoryObject NtQueryEaFile NtQueryEvent NtQueryFullAttributesFile NtQueryInformationAtom NtQueryInformationFile NtQueryInformationJobObject NtQueryInformationPort NtQueryInformationProcess NtQueryInformationThread NtQueryInformationToken NtQueryInstallUILanguage NtQueryIntervalProfile NtQueryIoCompletion NtQueryKey NtQueryMultipleValueKey NtQueryMutant NtQueryObject NtQueryOpenSubKeys NtQueryPerformanceCounter NtQueryPortInformationProcess NtQueryQuotaInformationFile NtQuerySection NtQuerySecurityObject NtQuerySemaphore NtQuerySymbolicLinkObject NtQuerySystemEnvironmentValue NtQuerySystemEnvironmentValueEx NtQuerySystemInformation NtQuerySystemTime NtQueryTimer NtQueryTimerResolution NtQueryValueKey NtQueryVirtualMemory NtQueryVolumeInformationFile NtQueueApcThread NtRaiseException NtRaiseHardError NtReadFile NtReadFileScatter NtReadRequestData NtReadVirtualMemory NtRegisterThreadTerminatePort NtReleaseKeyedEvent NtReleaseMutant NtReleaseSemaphore NtRemoveIoCompletion NtRemoveProcessDebug NtRenameKey NtReplaceKey NtReplyPort NtReplyWaitReceivePort NtReplyWaitReceivePortEx NtReplyWaitReplyPort NtRequestDeviceWakeup NtRequestPort NtRequestWaitReplyPort NtRequestWakeupLatency NtResetEvent NtResetWriteWatch NtRestoreKey NtResumeProcess NtResumeThread NtSaveKey NtSaveKeyEx NtSaveMergedKeys NtSecureConnectPort NtSetBootEntryOrder NtSetBootOptions NtSetContextThread NtSetDebugFilterState NtSetDefaultHardErrorPort NtSetDefaultLocale NtSetDefaultUILanguage NtSetEaFile NtSetEvent NtSetEventBoostPriority NtSetHighEventPair NtSetHighWaitLowEventPair NtSetInformationDebugObject NtSetInformationFile NtSetInformationJobObject NtSetInformationKey NtSetInformationObject NtSetInformationProcess NtSetInformationThread NtSetInformationToken NtSetIntervalProfile NtSetIoCompletion NtSetLdtEntries NtSetLowEventPair NtSetLowWaitHighEventPair NtSetQuotaInformationFile NtSetSecurityObject NtSetSystemEnvironmentValue NtSetSystemEnvironmentValueEx NtSetSystemInformation NtSetSystemPowerState NtSetSystemTime NtSetThreadExecutionState NtSetTimer NtSetTimerResolution NtSetUuidSeed NtSetValueKey NtSetVolumeInformationFile NtShutdownSystem NtSignalAndWaitForSingleObject NtStartProfile NtStopProfile NtSuspendProcess NtSuspendThread NtSystemDebugControl NtTerminateJobObject NtTerminateProcess NtTerminateThread NtTestAlert NtTraceEvent NtTranslateFilePath NtUnloadDriver NtUnloadKey NtUnloadKeyEx NtUnlockFile NtUnlockVirtualMemory NtUnmapViewOfSection NtVdmControl NtWaitForDebugEvent NtWaitForKeyedEvent NtWaitForMultipleObjects NtWaitForSingleObject NtWaitHighEventPair NtWaitLowEventPair NtWriteFile NtWriteFileGather NtWriteRequestData NtWriteVirtualMemory NtYieldExecution PfxFindPrefix PfxInitialize PfxInsertPrefix PfxRemovePrefix PropertyLengthAsVariant RtlAbortRXact RtlAbsoluteToSelfRelativeSD RtlAcquirePebLock RtlAcquireResourceExclusive RtlAcquireResourceShared RtlActivateActivationContext RtlActivateActivationContextEx RtlActivateActivationContextUnsafeFast RtlAddAccessAllowedAce RtlAddAccessAllowedAceEx RtlAddAccessAllowedObjectAce RtlAddAccessDeniedAce RtlAddAccessDeniedAceEx RtlAddAccessDeniedObjectAce RtlAddAce RtlAddActionToRXact RtlAddAtomToAtomTable RtlAddAttributeActionToRXact RtlAddAuditAccessAce RtlAddAuditAccessAceEx RtlAddAuditAccessObjectAce RtlAddCompoundAce RtlAddRange RtlAddRefActivationContext RtlAddRefMemoryStream RtlAddVectoredExceptionHandler RtlAddressInSectionTable RtlAdjustPrivilege RtlAllocateAndInitializeSid RtlAllocateHandle RtlAllocateHeap RtlAnsiCharToUnicodeChar RtlAnsiStringToUnicodeSize RtlAnsiStringToUnicodeString RtlAppendAsciizToString RtlAppendPathElement RtlAppendStringToString RtlAppendUnicodeStringToString RtlAppendUnicodeToString RtlApplicationVerifierStop RtlApplyRXact RtlApplyRXactNoFlush RtlAreAllAccessesGranted RtlAreAnyAccessesGranted RtlAreBitsClear RtlAreBitsSet RtlAssert RtlAssert2 RtlCancelTimer RtlCaptureContext RtlCaptureStackBackTrace RtlCaptureStackContext RtlCharToInteger RtlCheckForOrphanedCriticalSections RtlCheckProcessParameters RtlCheckRegistryKey RtlClearAllBits RtlClearBits RtlCloneMemoryStream RtlCommitMemoryStream RtlCompactHeap RtlCompareMemory RtlCompareMemoryUlong RtlCompareString RtlCompareUnicodeString RtlCompressBuffer RtlComputeCrc32 RtlComputeImportTableHash RtlComputePrivatizedDllName_U RtlConsoleMultiByteToUnicodeN RtlConvertExclusiveToShared RtlConvertLongToLargeInteger RtlConvertPropertyToVariant RtlConvertSharedToExclusive RtlConvertSidToUnicodeString RtlConvertToAutoInheritSecurityObject RtlConvertUiListToApiList RtlConvertUlongToLargeInteger RtlConvertVariantToProperty RtlCopyLuid RtlCopyLuidAndAttributesArray RtlCopyMemoryStreamTo RtlCopyOutOfProcessMemoryStreamTo RtlCopyRangeList RtlCopySecurityDescriptor RtlCopySid RtlCopySidAndAttributesArray RtlCopyString RtlCopyUnicodeString RtlCreateAcl RtlCreateActivationContext RtlCreateAndSetSD RtlCreateAtomTable RtlCreateBootStatusDataFile RtlCreateEnvironment RtlCreateHeap RtlCreateProcessParameters RtlCreateQueryDebugBuffer RtlCreateRegistryKey RtlCreateSecurityDescriptor RtlCreateSystemVolumeInformationFolder RtlCreateTagHeap RtlCreateTimer RtlCreateTimerQueue RtlCreateUnicodeString RtlCreateUnicodeStringFromAsciiz RtlCreateUserProcess RtlCreateUserSecurityObject RtlCreateUserThread RtlCustomCPToUnicodeN RtlCutoverTimeToSystemTime RtlDeNormalizeProcessParams RtlDeactivateActivationContext RtlDeactivateActivationContextUnsafeFast RtlDebugPrintTimes RtlDecodePointer RtlDecodeSystemPointer RtlDecompressBuffer RtlDecompressFragment RtlDefaultNpAcl RtlDelete RtlDeleteAce RtlDeleteAtomFromAtomTable RtlDeleteCriticalSection RtlDeleteElementGenericTable RtlDeleteElementGenericTableAvl RtlDeleteNoSplay RtlDeleteOwnersRanges RtlDeleteRange RtlDeleteRegistryValue RtlDeleteResource RtlDeleteSecurityObject RtlDeleteTimer RtlDeleteTimerQueue RtlDeleteTimerQueueEx RtlDeregisterWait RtlDeregisterWaitEx RtlDestroyAtomTable RtlDestroyEnvironment RtlDestroyHandleTable RtlDestroyHeap RtlDestroyProcessParameters RtlDestroyQueryDebugBuffer RtlDetermineDosPathNameType_U RtlDllShutdownInProgress RtlDnsHostNameToComputerName RtlDoesFileExists_U RtlDosApplyFileIsolationRedirection_Ustr RtlDosPathNameToNtPathName_U RtlDosSearchPath_U RtlDosSearchPath_Ustr RtlDowncaseUnicodeChar RtlDowncaseUnicodeString RtlDumpResource RtlDuplicateUnicodeString RtlEmptyAtomTable RtlEnableEarlyCriticalSectionEventCreation RtlEncodePointer RtlEncodeSystemPointer RtlEnlargedIntegerMultiply RtlEnlargedUnsignedDivide RtlEnlargedUnsignedMultiply RtlEnterCriticalSection RtlEnumProcessHeaps RtlEnumerateGenericTable RtlEnumerateGenericTableAvl RtlEnumerateGenericTableLikeADirectory RtlEnumerateGenericTableWithoutSplaying RtlEnumerateGenericTableWithoutSplayingAvl RtlEqualComputerName RtlEqualDomainName RtlEqualLuid RtlEqualPrefixSid RtlEqualSid RtlEqualString RtlEqualUnicodeString RtlEraseUnicodeString RtlExitUserThread RtlExpandEnvironmentStrings_U RtlExtendHeap RtlExtendedIntegerMultiply RtlExtendedLargeIntegerDivide RtlExtendedMagicDivide RtlFillMemory RtlFillMemoryUlong RtlFinalReleaseOutOfProcessMemoryStream RtlFindActivationContextSectionGuid RtlFindActivationContextSectionString RtlFindCharInUnicodeString RtlFindClearBits RtlFindClearBitsAndSet RtlFindClearRuns RtlFindLastBackwardRunClear RtlFindLeastSignificantBit RtlFindLongestRunClear RtlFindMessage RtlFindMostSignificantBit RtlFindNextForwardRunClear RtlFindRange RtlFindSetBits RtlFindSetBitsAndClear RtlFirstEntrySList RtlFirstFreeAce RtlFlushSecureMemoryCache RtlFormatCurrentUserKeyPath RtlFormatMessage RtlFreeAnsiString RtlFreeHandle RtlFreeHeap RtlFreeOemString RtlFreeRangeList RtlFreeSid RtlFreeThreadActivationContextStack RtlFreeUnicodeString RtlFreeUserThreadStack RtlGUIDFromString RtlGenerate8dot3Name RtlGetAce RtlGetActiveActivationContext RtlGetCallersAddress RtlGetCompressionWorkSpaceSize RtlGetControlSecurityDescriptor RtlGetCurrentDirectory_U RtlGetCurrentPeb RtlGetDaclSecurityDescriptor RtlGetElementGenericTable RtlGetElementGenericTableAvl RtlGetFirstRange RtlGetFrame RtlGetFullPathName_U RtlGetGroupSecurityDescriptor RtlGetLastNtStatus RtlGetLastWin32Error RtlGetLengthWithoutLastFullDosOrNtPathElement RtlGetLengthWithoutTrailingPathSeperators RtlGetLongestNtPathLength RtlGetNativeSystemInformation RtlGetNextRange RtlGetNtGlobalFlags RtlGetNtProductType RtlGetNtVersionNumbers RtlGetOwnerSecurityDescriptor RtlGetProcessHeaps RtlGetSaclSecurityDescriptor RtlGetSecurityDescriptorRMControl RtlGetSetBootStatusData RtlGetUnloadEventTrace RtlGetUserInfoHeap RtlGetVersion RtlHashUnicodeString RtlIdentifierAuthoritySid RtlImageDirectoryEntryToData RtlImageNtHeader RtlImageRvaToSection RtlImageRvaToVa RtlImpersonateSelf RtlInitAnsiString RtlInitCodePageTable RtlInitMemoryStream RtlInitNlsTables RtlInitOutOfProcessMemoryStream RtlInitString RtlInitUnicodeString RtlInitUnicodeStringEx RtlInitializeAtomPackage RtlInitializeBitMap RtlInitializeContext RtlInitializeCriticalSection RtlInitializeCriticalSectionAndSpinCount RtlInitializeGenericTable RtlInitializeGenericTableAvl RtlInitializeHandleTable RtlInitializeRXact RtlInitializeRangeList RtlInitializeResource RtlInitializeSListHead RtlInitializeSid RtlInitializeStackTraceDataBase RtlInsertElementGenericTable RtlInsertElementGenericTableAvl RtlInt64ToUnicodeString RtlIntegerToChar RtlIntegerToUnicodeString RtlInterlockedFlushSList RtlInterlockedPopEntrySList RtlInterlockedPushEntrySList RtlInterlockedPushListSList RtlInvertRangeList RtlIpv4AddressToStringA RtlIpv4AddressToStringExA RtlIpv4AddressToStringExW RtlIpv4AddressToStringW RtlIpv4StringToAddressA RtlIpv4StringToAddressExA RtlIpv4StringToAddressExW RtlIpv4StringToAddressW RtlIpv6AddressToStringA RtlIpv6AddressToStringExA RtlIpv6AddressToStringExW RtlIpv6AddressToStringW RtlIpv6StringToAddressA RtlIpv6StringToAddressExA RtlIpv6StringToAddressExW RtlIpv6StringToAddressW RtlIsActivationContextActive RtlIsDosDeviceName_U RtlIsGenericTableEmpty RtlIsGenericTableEmptyAvl RtlIsNameLegalDOS8Dot3 RtlIsRangeAvailable RtlIsTextUnicode RtlIsThreadWithinLoaderCallout RtlIsValidHandle RtlIsValidIndexHandle RtlLargeIntegerAdd RtlLargeIntegerArithmeticShift RtlLargeIntegerDivide RtlLargeIntegerNegate RtlLargeIntegerShiftLeft RtlLargeIntegerShiftRight RtlLargeIntegerSubtract RtlLargeIntegerToChar RtlLeaveCriticalSection RtlLengthRequiredSid RtlLengthSecurityDescriptor RtlLengthSid RtlLocalTimeToSystemTime RtlLockBootStatusData RtlLockHeap RtlLockMemoryStreamRegion RtlLogStackBackTrace RtlLookupAtomInAtomTable RtlLookupElementGenericTable RtlLookupElementGenericTableAvl RtlMakeSelfRelativeSD RtlMapGenericMask RtlMapSecurityErrorToNtStatus RtlMergeRangeLists RtlMoveMemory RtlMultiAppendUnicodeStringBuffer RtlMultiByteToUnicodeN RtlMultiByteToUnicodeSize RtlNewInstanceSecurityObject RtlNewSecurityGrantedAccess RtlNewSecurityObject RtlNewSecurityObjectEx RtlNewSecurityObjectWithMultipleInheritance RtlNormalizeProcessParams RtlNtPathNameToDosPathName RtlNtStatusToDosError RtlNtStatusToDosErrorNoTeb RtlNumberGenericTableElements RtlNumberGenericTableElementsAvl RtlNumberOfClearBits RtlNumberOfSetBits RtlOemStringToUnicodeSize RtlOemStringToUnicodeString RtlOemToUnicodeN RtlOpenCurrentUser RtlPcToFileHeader RtlPinAtomInAtomTable RtlPopFrame RtlPrefixString RtlPrefixUnicodeString RtlProtectHeap RtlPushFrame RtlQueryAtomInAtomTable RtlQueryDepthSList RtlQueryEnvironmentVariable_U RtlQueryHeapInformation RtlQueryInformationAcl RtlQueryInformationActivationContext RtlQueryInformationActiveActivationContext RtlQueryInterfaceMemoryStream RtlQueryProcessBackTraceInformation RtlQueryProcessDebugInformation RtlQueryProcessHeapInformation RtlQueryProcessLockInformation RtlQueryRegistryValues RtlQuerySecurityObject RtlQueryTagHeap RtlQueryTimeZoneInformation RtlQueueApcWow64Thread RtlQueueWorkItem RtlRaiseException RtlRaiseStatus RtlRandom RtlRandomEx RtlReAllocateHeap RtlReadMemoryStream RtlReadOutOfProcessMemoryStream RtlRealPredecessor RtlRealSuccessor RtlRegisterSecureMemoryCacheCallback RtlRegisterWait RtlReleaseActivationContext RtlReleaseMemoryStream RtlReleasePebLock RtlReleaseResource RtlRemoteCall RtlRemoveVectoredExceptionHandler RtlResetRtlTranslations RtlRestoreLastWin32Error RtlRevertMemoryStream RtlRunDecodeUnicodeString RtlRunEncodeUnicodeString RtlSecondsSince1970ToTime RtlSecondsSince1980ToTime RtlSeekMemoryStream RtlSelfRelativeToAbsoluteSD RtlSelfRelativeToAbsoluteSD2 RtlSetAllBits RtlSetAttributesSecurityDescriptor RtlSetBits RtlSetControlSecurityDescriptor RtlSetCriticalSectionSpinCount RtlSetCurrentDirectory_U RtlSetCurrentEnvironment RtlSetDaclSecurityDescriptor RtlSetEnvironmentVariable RtlSetGroupSecurityDescriptor RtlSetHeapInformation RtlSetInformationAcl RtlSetIoCompletionCallback RtlSetLastWin32Error RtlSetLastWin32ErrorAndNtStatusFromNtStatus RtlSetMemoryStreamSize RtlSetOwnerSecurityDescriptor RtlSetProcessIsCritical RtlSetSaclSecurityDescriptor RtlSetSecurityDescriptorRMControl RtlSetSecurityObject RtlSetSecurityObjectEx RtlSetThreadIsCritical RtlSetThreadPoolStartFunc RtlSetTimeZoneInformation RtlSetTimer RtlSetUnicodeCallouts RtlSetUserFlagsHeap RtlSetUserValueHeap RtlSizeHeap RtlSplay RtlStartRXact RtlStatMemoryStream RtlStringFromGUID RtlSubAuthorityCountSid RtlSubAuthoritySid RtlSubtreePredecessor RtlSubtreeSuccessor RtlSystemTimeToLocalTime RtlTimeFieldsToTime RtlTimeToElapsedTimeFields RtlTimeToSecondsSince1970 RtlTimeToSecondsSince1980 RtlTimeToTimeFields RtlTraceDatabaseAdd RtlTraceDatabaseCreate RtlTraceDatabaseDestroy RtlTraceDatabaseEnumerate RtlTraceDatabaseFind RtlTraceDatabaseLock RtlTraceDatabaseUnlock RtlTraceDatabaseValidate RtlTryEnterCriticalSection RtlUlongByteSwap RtlUlonglongByteSwap RtlUnhandledExceptionFilter RtlUnhandledExceptionFilter2 RtlUnicodeStringToAnsiSize RtlUnicodeStringToAnsiString RtlUnicodeStringToCountedOemString RtlUnicodeStringToInteger RtlUnicodeStringToOemSize RtlUnicodeStringToOemString RtlUnicodeToCustomCPN RtlUnicodeToMultiByteN RtlUnicodeToMultiByteSize RtlUnicodeToOemN RtlUniform RtlUnlockBootStatusData RtlUnlockHeap RtlUnlockMemoryStreamRegion RtlUnwind RtlUpcaseUnicodeChar RtlUpcaseUnicodeString RtlUpcaseUnicodeStringToAnsiString RtlUpcaseUnicodeStringToCountedOemString RtlUpcaseUnicodeStringToOemString RtlUpcaseUnicodeToCustomCPN RtlUpcaseUnicodeToMultiByteN RtlUpcaseUnicodeToOemN RtlUpdateTimer RtlUpperChar RtlUpperString RtlUsageHeap RtlUshortByteSwap RtlValidAcl RtlValidRelativeSecurityDescriptor RtlValidSecurityDescriptor RtlValidSid RtlValidateHeap RtlValidateProcessHeaps RtlValidateUnicodeString RtlVerifyVersionInfo RtlWalkFrameChain RtlWalkHeap RtlWriteMemoryStream RtlWriteRegistryValue RtlZeroHeap RtlZeroMemory RtlZombifyActivationContext RtlpApplyLengthFunction RtlpEnsureBufferSize RtlpNotOwnerCriticalSection RtlpNtCreateKey RtlpNtEnumerateSubKey RtlpNtMakeTemporaryKey RtlpNtOpenKey RtlpNtQueryValueKey RtlpNtSetValueKey RtlpUnWaitCriticalSection RtlpWaitForCriticalSection RtlxAnsiStringToUnicodeSize RtlxOemStringToUnicodeSize RtlxUnicodeStringToAnsiSize RtlxUnicodeStringToOemSize VerSetConditionMask ZwAcceptConnectPort ZwAccessCheck ZwAccessCheckAndAuditAlarm ZwAccessCheckByType ZwAccessCheckByTypeAndAuditAlarm ZwAccessCheckByTypeResultList ZwAccessCheckByTypeResultListAndAuditAlarm ZwAccessCheckByTypeResultListAndAuditAlarmByHandle ZwAddAtom ZwAddBootEntry ZwAdjustGroupsToken ZwAdjustPrivilegesToken ZwAlertResumeThread ZwAlertThread ZwAllocateLocallyUniqueId ZwAllocateUserPhysicalPages ZwAllocateUuids ZwAllocateVirtualMemory ZwAreMappedFilesTheSame ZwAssignProcessToJobObject ZwCallbackReturn ZwCancelDeviceWakeupRequest ZwCancelIoFile ZwCancelTimer ZwClearEvent ZwClose ZwCloseObjectAuditAlarm ZwCompactKeys ZwCompareTokens ZwCompleteConnectPort ZwCompressKey ZwConnectPort ZwContinue ZwCreateDebugObject ZwCreateDirectoryObject ZwCreateEvent ZwCreateEventPair ZwCreateFile ZwCreateIoCompletion ZwCreateJobObject ZwCreateJobSet ZwCreateKey ZwCreateKeyedEvent ZwCreateMailslotFile ZwCreateMutant ZwCreateNamedPipeFile ZwCreatePagingFile ZwCreatePort ZwCreateProcess ZwCreateProcessEx ZwCreateProfile ZwCreateSection ZwCreateSemaphore ZwCreateSymbolicLinkObject ZwCreateThread ZwCreateTimer ZwCreateToken ZwCreateWaitablePort ZwDebugActiveProcess ZwDebugContinue ZwDelayExecution ZwDeleteAtom ZwDeleteBootEntry ZwDeleteFile ZwDeleteKey ZwDeleteObjectAuditAlarm ZwDeleteValueKey ZwDeviceIoControlFile ZwDisplayString ZwDuplicateObject ZwDuplicateToken ZwEnumerateBootEntries ZwEnumerateKey ZwEnumerateSystemEnvironmentValuesEx ZwEnumerateValueKey ZwExtendSection ZwFilterToken ZwFindAtom ZwFlushBuffersFile ZwFlushInstructionCache ZwFlushKey ZwFlushVirtualMemory ZwFlushWriteBuffer ZwFreeUserPhysicalPages ZwFreeVirtualMemory ZwFsControlFile ZwGetContextThread ZwGetDevicePowerState ZwGetPlugPlayEvent ZwGetWriteWatch ZwImpersonateAnonymousToken ZwImpersonateClientOfPort ZwImpersonateThread ZwInitializeRegistry ZwInitiatePowerAction ZwIsProcessInJob ZwIsSystemResumeAutomatic ZwListenPort ZwLoadDriver ZwLoadKey ZwLoadKey2 ZwLockFile ZwLockProductActivationKeys ZwLockRegistryKey ZwLockVirtualMemory ZwMakePermanentObject ZwMakeTemporaryObject ZwMapUserPhysicalPages ZwMapUserPhysicalPagesScatter ZwMapViewOfSection ZwModifyBootEntry ZwNotifyChangeDirectoryFile ZwNotifyChangeKey ZwNotifyChangeMultipleKeys ZwOpenDirectoryObject ZwOpenEvent ZwOpenEventPair ZwOpenFile ZwOpenIoCompletion ZwOpenJobObject ZwOpenKey ZwOpenKeyedEvent ZwOpenMutant ZwOpenObjectAuditAlarm ZwOpenProcess ZwOpenProcessToken ZwOpenProcessTokenEx ZwOpenSection ZwOpenSemaphore ZwOpenSymbolicLinkObject ZwOpenThread ZwOpenThreadToken ZwOpenThreadTokenEx ZwOpenTimer ZwPlugPlayControl ZwPowerInformation ZwPrivilegeCheck ZwPrivilegeObjectAuditAlarm ZwPrivilegedServiceAuditAlarm ZwProtectVirtualMemory ZwPulseEvent ZwQueryAttributesFile ZwQueryBootEntryOrder ZwQueryBootOptions ZwQueryDebugFilterState ZwQueryDefaultLocale ZwQueryDefaultUILanguage ZwQueryDirectoryFile ZwQueryDirectoryObject ZwQueryEaFile ZwQueryEvent ZwQueryFullAttributesFile ZwQueryInformationAtom ZwQueryInformationFile ZwQueryInformationJobObject ZwQueryInformationPort ZwQueryInformationProcess ZwQueryInformationThread ZwQueryInformationToken ZwQueryInstallUILanguage ZwQueryIntervalProfile ZwQueryIoCompletion ZwQueryKey ZwQueryMultipleValueKey ZwQueryMutant ZwQueryObject ZwQueryOpenSubKeys ZwQueryPerformanceCounter ZwQueryPortInformationProcess ZwQueryQuotaInformationFile ZwQuerySection ZwQuerySecurityObject ZwQuerySemaphore ZwQuerySymbolicLinkObject ZwQuerySystemEnvironmentValue ZwQuerySystemEnvironmentValueEx ZwQuerySystemInformation ZwQuerySystemTime ZwQueryTimer ZwQueryTimerResolution ZwQueryValueKey ZwQueryVirtualMemory ZwQueryVolumeInformationFile ZwQueueApcThread ZwRaiseException ZwRaiseHardError ZwReadFile ZwReadFileScatter ZwReadRequestData ZwReadVirtualMemory ZwRegisterThreadTerminatePort ZwReleaseKeyedEvent ZwReleaseMutant ZwReleaseSemaphore ZwRemoveIoCompletion ZwRemoveProcessDebug ZwRenameKey ZwReplaceKey ZwReplyPort ZwReplyWaitReceivePort ZwReplyWaitReceivePortEx ZwReplyWaitReplyPort ZwRequestDeviceWakeup ZwRequestPort ZwRequestWaitReplyPort ZwRequestWakeupLatency ZwResetEvent ZwResetWriteWatch ZwRestoreKey ZwResumeProcess ZwResumeThread ZwSaveKey ZwSaveKeyEx ZwSaveMergedKeys ZwSecureConnectPort ZwSetBootEntryOrder ZwSetBootOptions ZwSetContextThread ZwSetDebugFilterState ZwSetDefaultHardErrorPort ZwSetDefaultLocale ZwSetDefaultUILanguage ZwSetEaFile ZwSetEvent ZwSetEventBoostPriority ZwSetHighEventPair ZwSetHighWaitLowEventPair ZwSetInformationDebugObject ZwSetInformationFile ZwSetInformationJobObject ZwSetInformationKey ZwSetInformationObject ZwSetInformationProcess ZwSetInformationThread ZwSetInformationToken ZwSetIntervalProfile ZwSetIoCompletion ZwSetLdtEntries ZwSetLowEventPair ZwSetLowWaitHighEventPair ZwSetQuotaInformationFile ZwSetSecurityObject ZwSetSystemEnvironmentValue ZwSetSystemEnvironmentValueEx ZwSetSystemInformation ZwSetSystemPowerState ZwSetSystemTime ZwSetThreadExecutionState ZwSetTimer ZwSetTimerResolution ZwSetUuidSeed ZwSetValueKey ZwSetVolumeInformationFile ZwShutdownSystem ZwSignalAndWaitForSingleObject ZwStartProfile ZwStopProfile ZwSuspendProcess ZwSuspendThread ZwSystemDebugControl ZwTerminateJobObject ZwTerminateProcess ZwTerminateThread ZwTestAlert ZwTraceEvent ZwTranslateFilePath ZwUnloadDriver ZwUnloadKey ZwUnloadKeyEx ZwUnlockFile ZwUnlockVirtualMemory ZwUnmapViewOfSection ZwVdmControl ZwWaitForDebugEvent ZwWaitForKeyedEvent ZwWaitForMultipleObjects ZwWaitForSingleObject ZwWaitHighEventPair ZwWaitLowEventPair ZwWriteFile ZwWriteFileGather ZwWriteRequestData ZwWriteVirtualMemory ZwYieldExecution _CIcos _CIlog _CIpow _CIsin _CIsqrt __isascii __iscsym __iscsymf __toascii _alldiv _alldvrm _allmul _alloca_probe _allrem _allshl _allshr _atoi64 _aulldiv _aulldvrm _aullrem _aullshr _chkstk _fltused _ftol _i64toa _i64tow _itoa _itow _lfind _ltoa _ltow _memccpy _memicmp _snprintf _snwprintf _splitpath _strcmpi _stricmp _strlwr _strnicmp _strupr _tolower _toupper _ui64toa _ui64tow _ultoa _ultow _vsnprintf _vsnwprintf _wcsicmp _wcslwr _wcsnicmp _wcsupr _wtoi _wtoi64 _wtol abs atan atoi atol bsearch ceil cos fabs floor isalnum isalpha iscntrl isdigit isgraph islower isprint ispunct isspace isupper iswalpha iswctype iswdigit iswlower iswspace iswxdigit isxdigit labs log mbstowcs memchr memcmp memcpy memmove memset pow qsort sin sprintf sqrt sscanf strcat strchr strcmp strcpy strcspn strlen strncat strncmp strncpy strpbrk strrchr strspn strstr strtol strtoul swprintf tan tolower toupper towlower towupper vDbgPrintEx vDbgPrintExWithPrefix vsprintf wcscat wcschr wcscmp wcscpy wcscspn wcslen wcsncat wcsncmp wcsncpy wcspbrk wcsrchr wcsspn wcsstr wcstol wcstombs wcstoul |
|
|
学习notepad.exe
打开NTDLL.dll,惊奇的发现原来CRT的许多基本函数居然都是在这里实现的!甚至包括qsort,ceil这样的函数,还有臭名昭著的strcpy(严格来讲,这只能怪使用者不当心)。堆的释放,进城管理,似乎都是在这。于是,我决定,仔细察看以下它,这1410个函数是做什么的 用户模式的代码在调用系统内核函数的时候,首先把一个叫做system call number的数放在EAX中,把参数放在其它的寄存器中了。然后调用INT 2E中断。但是大部分应用程序并不需要直接这么做。通常都是在调用kernel32.dll等时由他们来调用INT 2E. 内核模式的代码,做法稍微有点不同。他们通常调用由NTOSKRNL.EXE导出的NTDLL.dll中Zw开头的那一系列函数,比如ZwWaitForSingleObject, 反之,如果是用户级代码需要调用内核,就会利用INT 2E调用WaitForSingleObject.对于许多函数的批量调用,你会明显发现 Zw族要比Rtl族效率高很多。 可惜ntdll.dll中的大部分函数都是undocumented. 对于一部分得知其定义形式的函数,可以这样调用: 1.先将NTDLL.DLL读入 LoadLibrary(TEXT("NTDLL.dll")) 2.利用GetProcAddress 获取其函数入口地址 3.利用得到的函数指针调用 但是可以大致的分为几类吧 1 PropertyLengthAsVariant 它被排在了第一号,但是我就是不明白它是做什么的 2 Csr(configuration status register? Command and Status Register?)系列 CsrAllocateCaptureBuffer CsrAllocateMessagePointer CsrCaptureMessageBuffer CsrCaptureMessageMultiUnicodeStringsInPlace CsrCaptureMessageString CsrCaptureTimeout CsrClientCallServer CsrClientConnectToServer CsrFreeCaptureBuffer CsrGetProcessId CsrIdentifyAlertableThread CsrNewThread CsrProbeForRead CsrProbeForWrite CsrSetPriorityClass 3 Dbg系列 调试函数 DbgBreakPoint DbgPrint DbgPrintEx DbgPrintReturnControlC DbgPrompt DbgQueryDebugFilterState DbgSetDebugFilterState DbgUiConnectToDbg DbgUiContinue DbgUiConvertStateChangeStructure DbgUiDebugActiveProcess DbgUiGetThreadDebugObject DbgUiIssueRemoteBreakin DbgUiRemoteBreakin DbgUiSetThreadDebugObject DbgUiStopDebugging DbgUiWaitStateChange DbgUserBreakPoint 4 ki系列 KiRaiseUserExceptionDispatcher KiUserApcDispatcher KiUserCallbackDispatcher KiUserExceptionDispatcher 5 Ldr系列 Loader APIs,共34个 API NTDLL APIs LoadResource LdrAccessResource LdrAlternateResourcesEnabled DisableThreadLibraryCalls LdrDisableThreadCalloutsForDll LdrEnumResources LdrFindAppCompatVariableInfo LdrFindEntryForAddress EnumResourceTypesW LdrFindResourceDirectory_U FindResourceExA LdrFindResource_U LdrFlushAlternateResourceModules LdrGetAlternateResourceModuleHandle GetModuleHandleForUnicodeString LdrGetDllHandle GetProcAddress LdrGetProcedureAddress LdrInitializeThunk LoadLibraryEx (LOAD_LIBRARY_AS_DATAFILE) LdrLoadAlternateResourceModule LoadLibrary LdrLoadDll LdrProcessRelocationBlock LdrQueryApplicationCompatibilityGoo LdrQueryImageFileExecutionOptions LdrQueryProcessModuleInformation LdrRelocateImage ExitProcess LdrShutdownProcess ExitThread LdrShutdownThread LdrUnloadAlternateResourceModule FreeLibrary LdrUnloadDll LdrVerifyImageMatchesChecksum LdrVerifyMappedImageMatchesChecksum 6 Nls(National Language Support)系列 代码页管理 NlsAnsiCodePage NlsMbCodePageTag NlsMbOemCodePageTag 7 Nt系列 共285个,大部分都是kernel32.dll,user32.dll等的核心实现 NtCreateFile, NtOpenFile, NtClose, NtWaitForSingleObject 是kernel32.dll中许多用户级代码的核心实现。 NTSTATUS NtClose( HANDLE Handle); 竟然是CloseHandle 的原身!唯一的缺点是该函数并没有导出库,如果要调用,就必须使用GetProcAddress 来获得其函数指针然后调用。 NtCreateFile 可以说是DDK的核心 RtlUnwind initiates an unwind of procedure call frames 结构化异常(Structured Exception Handling, SEH )的 核心。 NTSTATUS NtWaitForSingleObject( HANDLE Handle, BOOLEAN Alertable, PLARGE_INTEGER Timeout); Waits until the specified object attains a state of signaled 我想,信号同步等,应该与之有莫大的联系吧 8 pfx 不明白 PfxFindPrefix PfxInitialize PfxInsertPrefix PfxRemovePrefix 9 RestoreEm87Context SaveEm87Context 10 rtl系列 共506个。我想,rtl应该是runtime library的缩写吧。一个很庞大的函数族,里面包含像 RtlCreateUserProcess 这样的一些很基本的函数,通常供内核模式的driver等调用 下面是一部分示例 APIs Forwarded to NTDLL API Destination DeleteCriticalSection Forwarded to NTDLL.RtlDeleteCriticalSection EnterCriticalSection Forwarded to NTDLL.RtlEnterCriticalSection HeapAlloc Forwarded to NTDLL.RtlAllocateHeap HeapFree Forwarded to NTDLL.RtlFreeHeap HeapReAlloc Forwarded to NTDLL.RtlReAllocateHeap HeapSize Forwarded to NTDLL.RtlSizeHeap LeaveCriticalSection Forwarded to NTDLL.RtlLeaveCriticalSection RtlFillMemory Forwarded to NTDLL.RtlFillMemory RtlMoveMemory Forwarded to NTDLL.RtlMoveMemory RtlUnwind Forwarded to NTDLL.RtlUnwind RtlZeroMemory Forwarded to NTDLL.RtlZeroMemory SetCriticalSectionSpinCount Forwarded to NTDLL.RtlSetCriticalSection- SpinCount TryEnterCriticalSection Forwarded to NTDLL.RtlTryEnterCriticalSection VerSetConditionMask Forwarded to NTDLL.VerSetConditionMask 11 VerSetConditionMask 用于确认系统信息 The VerSetConditionMask function sets the bits of a 64-bit value to indicate the comparison operator to use for a specified operating system version attribute. This function is used to build the dwlConditionMask parameter of the VerifyVersionInfo function. 12 Zw系列 共284个。前面已经说过,为可执行性系统服务提供内核模式的入口, 为NTOSKRNL.EXE 提供实现。由于是内核模式,所以在执行的时候并不检查用户是否有执行权限 13 内部函数 共116个。具体作用不明,很底层的东西。无法查到任何相关资料。无法得知与其相关的任何信息。 _CIcos _CIlog _CIpow _CIsin _CIsqrt __eCommonExceptions __eEmulatorInit __eF2XM1 __eFABS __eFADD32 __eFADD64 __eFADDPreg __eFADDreg __eFADDtop __eFCHS __eFCOM __eFCOM32 __eFCOM64 __eFCOMP __eFCOMP32 __eFCOMP64 __eFCOMPP __eFCOS __eFDECSTP __eFDIV32 __eFDIV64 __eFDIVPreg __eFDIVR32 __eFDIVR64 __eFDIVRPreg __eFDIVRreg __eFDIVRtop __eFDIVreg __eFDIVtop __eFFREE __eFIADD16 __eFIADD32 __eFICOM16 __eFICOM32 __eFICOMP16 __eFICOMP32 __eFIDIV16 __eFIDIV32 __eFIDIVR16 __eFIDIVR32 __eFILD16 __eFILD32 __eFILD64 __eFIMUL16 __eFIMUL32 __eFINCSTP __eFINIT __eFIST16 __eFIST32 __eFISTP16 __eFISTP32 __eFISTP64 __eFISUB16 __eFISUB32 __eFISUBR16 __eFISUBR32 __eFLD1 __eFLD32 __eFLD64 __eFLD80 __eFLDCW __eFLDENV __eFLDL2E __eFLDLN2 __eFLDPI __eFLDZ __eFMUL32 __eFMUL64 __eFMULPreg __eFMULreg __eFMULtop __eFPATAN __eFPREM __eFPREM1 __eFPTAN __eFRNDINT __eFRSTOR __eFSAVE __eFSCALE __eFSIN __eFSQRT __eFST __eFST32 __eFST64 __eFSTCW __eFSTENV __eFSTP __eFSTP32 __eFSTP64 __eFSTP80 __eFSTSW __eFSUB32 __eFSUB64 __eFSUBPreg __eFSUBR32 __eFSUBR64 __eFSUBRPreg __eFSUBRreg __eFSUBRtop __eFSUBreg __eFSUBtop __eFTST __eFUCOM __eFUCOMP __eFUCOMPP __eFXAM __eFXCH __eFXTRACT __eFYL2X __eFYL2XP1 __eGetStatusWord 14 一些CRT的基本函数 共131个 主要是字符串管理,还有些基本的数学函数 __isascii __iscsym __iscsymf __toascii _alldiv _alldvrm _allmul _alloca_probe _allrem _allshl _allshr _atoi64 _aulldiv _aulldvrm _aullrem _aullshr _chkstk _fltused _ftol _i64toa _i64tow _itoa _itow _lfind _ltoa _ltow _memccpy _memicmp _snprintf _snwprintf _splitpath _strcmpi _stricmp _strlwr _strnicmp _strupr _tolower _toupper _ui64toa _ui64tow _ultoa _ultow _vsnprintf _vsnwprintf _wcsicmp _wcslwr _wcsnicmp _wcsupr _wtoi _wtoi64 _wtol abs atan atoi atol bsearch ceil cos fabs floor isalnum isalpha iscntrl isdigit isgraph islower isprint ispunct isspace isupper iswalpha iswctype iswdigit iswlower iswspace iswxdigit isxdigit labs log mbstowcs memchr memcmp memcpy memmove memset pow qsort sin sprintf sqrt sscanf strcat strchr strcmp strcpy strcspn strlen strncat strncmp strncpy strpbrk strrchr strspn strstr strtol strtoul swprintf tan tolower toupper towlower towupper vDbgPrintEx vDbgPrintExWithPrefix vsprintf wcscat wcschr wcscmp wcscpy wcscspn wcslen wcsncat wcsncmp wcsncpy wcspbrk wcsrchr wcsspn wcsstr wcstol wcstombs wcstoul ================塞纳河畔 |
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值