|
|
|
|
|
[求助指导下UPX变异壳linux脱壳
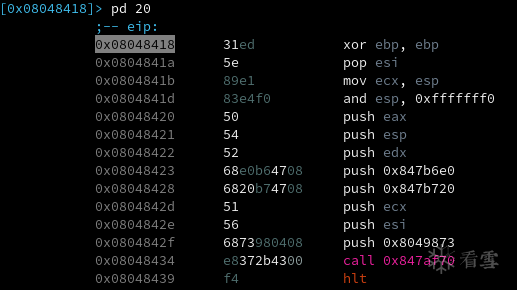
这个程序对于初学破解的人不友好! 跟踪到入口后,发现 [0x08048000]> pf.elf_header
ident :
struct<elf_ident>
magic : 0x08048000 = "\x7fELF"
class : 0x08048004 = class (enum elf_class) = 0x1 ; ELFCLASS32
data : 0x08048005 = data (enum elf_data) = 0x1 ; ELFDATA2LSB
version : 0x08048006 = version (enum elf_hdr_version) = 0x1 ; EV_CURRENT
type : 0x08048010 = type (enum elf_type) = 0x2 ; ET_EXEC
machine : 0x08048012 = machine (enum elf_machine) = 0x3 ; EM_386
version : 0x08048014 = version (enum elf_obj_version) = 0x1 ; EV_CURRENT
entry : 0x08048018 = 0x4c725ee6 # 真实的入口为 0x8048418
phoff : 0x0804801c = 0x00000034
shoff : 0x08048020 = 0x006983fc
flags : 0x08048024 = 0x00000000
ehsize : 0x08048028 = 0x0034
phentsize : 0x0804802a = 0x0020
phnum : 0x0804802c = 0x0005
shentsize : 0x0804802e = 0x0028
shnum : 0x08048030 = 0x001a
shstrndx : 0x08048032 = 0x0019
再看看 [0x08048000]> pf 5? (elf_phdr)elf.phdr @ $$+0x34!0x100
0x08048034 [0] {
elf.phdr :
struct<elf_phdr>
type : 0x08048034 = type (enum elf_p_type) = 0x1 ; PT_LOAD
offset : 0x08048038 = 0x00000000
vaddr : 0x0804803c = 0x08048000
paddr : 0x08048040 = 0x08048000
filesz : 0x08048044 = 0x00683b88
memsz : 0x08048048 = 0x00683b88
flags : 0x0804804c = flags (enum elf_p_flags) = 0x5 ; PF_Read_Exec
align : 0x08048050 = 0x00001000
}
0x08048054 [1] {
elf.phdr :
struct<elf_phdr>
type : 0x08048054 = type (enum elf_p_type) = 0x1 ; PT_LOAD
offset : 0x08048058 = 0x00683b88
vaddr : 0x0804805c = 0x086ccb88
paddr : 0x08048060 = 0x086ccb88
filesz : 0x08048064 = 0x0001042c
memsz : 0x08048068 = 0x001633d0
flags : 0x0804806c = flags (enum elf_p_flags) = 0x6 ; PF_Read_Write
align : 0x08048070 = 0x00001000
}
0x08048074 [2] {
elf.phdr :
struct<elf_phdr>
type : 0x08048074 = type (enum elf_p_type) = 0x4 ; PT_NOTE
offset : 0x08048078 = 0x000000d4
vaddr : 0x0804807c = 0x080480d4
paddr : 0x08048080 = 0x080480d4
filesz : 0x08048084 = 0x00000020
memsz : 0x08048088 = 0x00000020
flags : 0x0804808c = flags (enum elf_p_flags) = 0x4 ; PF_Read
align : 0x08048090 = 0x00000004
}
0x08048094 [3] {
elf.phdr :
struct<elf_phdr>
type : 0x08048094 = type (enum elf_p_type) = 0x7
offset : 0x08048098 = 0x00683b88
vaddr : 0x0804809c = 0x086ccb88
paddr : 0x080480a0 = 0x086ccb88
filesz : 0x080480a4 = 0x00000014
memsz : 0x080480a8 = 0x00000034
flags : 0x080480ac = flags (enum elf_p_flags) = 0x4 ; PF_Read
align : 0x080480b0 = 0x00000004
}
0x080480b4 [4] {
elf.phdr :
struct<elf_phdr>
type : 0x080480b4 = type (enum elf_p_type) = 0x6474e551
offset : 0x080480b8 = 0x00000000
vaddr : 0x080480bc = 0x00000000
paddr : 0x080480c0 = 0x00000000
filesz : 0x080480c4 = 0x00000000
memsz : 0x080480c8 = 0x00000000
flags : 0x080480cc = flags (enum elf_p_flags) = 0x6 ; PF_Read_Write
align : 0x080480d0 = 0x00000010
}
段地址没有对齐且错误
最后于 2019-10-23 16:20
被采臣·宁编辑
,原因:
|
|
|
|
|
|
[求助]gdb在调试so文件的时候怎么确定so文件中函数的虚拟地址?
以下断点在 libc.so 中的 printf 为例找到 libc.so 在你程序中的加载基址用gdb载入程序并运行到入口点,用 pwndbg> libs
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
0x400000 0x401000 r--p 1000 0 /home/crackwiki/test/test
0x401000 0x402000 r-xp 1000 1000 /home/crackwiki/test/test
0x402000 0x403000 r--p 1000 2000 /home/crackwiki/test/test
0x403000 0x404000 r--p 1000 2000 /home/crackwiki/test/test
0x404000 0x405000 rw-p 1000 3000 /home/crackwiki/test/test
**0x7ffff7deb000** 0x7ffff7e0d000 r--p 22000 0 /usr/lib64/libc-2.29.so
0x7ffff7e0d000 0x7ffff7f5a000 r-xp 14d000 22000 /usr/lib64/libc-2.29.so
0x7ffff7f5a000 0x7ffff7fa6000 r--p 4c000 16f000 /usr/lib64/libc-2.29.so
0x7ffff7fa6000 0x7ffff7fa7000 ---p 1000 1bb000 /usr/lib64/libc-2.29.so
0x7ffff7fa7000 0x7ffff7fab000 r--p 4000 1bb000 /usr/lib64/libc-2.29.so
0x7ffff7fab000 0x7ffff7fad000 rw-p 2000 1bf000 /usr/lib64/libc-2.29.so
0x7ffff7deb000 就是 libc.so 在程序中的加载基址 找到 printf 在 libc.so 中的虚拟地址我使用radare2来反汇编, 如下所示: [0x00053220]> pd 10 sym.printf
;-- printf:
;-- .annobin_printf.c:
;-- __printf:
/ (fcn) sym._IO_printf 204
| sym._IO_printf (int32_t arg11, int32_t arg10, int32_t arg9, int32_t arg8, int32_t arg7, int32_t arg6, int32_t arg5, int32_t arg1, int32_t arg2, int32_t arg3, int32_t arg4, int32_t arg_e0h);
| bp: 0 (vars 0, args 0)
| sp: 19 (vars 18, args 1)
| rg: 11 (vars 0, args 11)
| 0x00053220 f30f1efa endbr64
| 0x00053224 4881ecd80000. sub rsp, 0xd8
| 0x0005322b 4989fa mov r10, rdi ; arg1
| 0x0005322e 4889742428 mov qword [var_28h], rsi ; arg2
| 0x00053233 4889542430 mov qword [var_30h], rdx ; arg3
| 0x00053238 48894c2438 mov qword [var_38h], rcx ; arg4
| 0x0005323d 4c89442440 mov qword [var_40h], r8 ; arg5
| 0x00053242 4c894c2448 mov qword [var_48h], r9 ; arg6
| 0x00053247 84c0 test al, al
| ,=< 0x00053249 7437 je 0x53282
printf 函数在libc.so中的虚拟地址为: 0x00053220 下断点在 printf断点地址 = 基址 + 虚拟地址 = 0x7ffff7deb000 + 0x00053220 pwndbg> x /10i 0x7ffff7deb000+0x53220 0x7ffff7e3e220 <__printf>: endbr64 0x7ffff7e3e224 <__printf+4>: sub rsp,0xd8 0x7ffff7e3e22b <__printf+11>: mov r10,rdi 0x7ffff7e3e22e <__printf+14>: mov QWORD PTR [rsp+0x28],rsi 0x7ffff7e3e233 <__printf+19>: mov QWORD PTR [rsp+0x30],rdx 0x7ffff7e3e238 <__printf+24>: mov QWORD PTR [rsp+0x38],rcx 0x7ffff7e3e23d <__printf+29>: mov QWORD PTR [rsp+0x40],r8 0x7ffff7e3e242 <__printf+34>: mov QWORD PTR [rsp+0x48],r9 0x7ffff7e3e247 <__printf+39>: test al,al 0x7ffff7e3e249 <__printf+41>: je 0x7ffff7e3e282 <__printf+98> gdb下断点:
最后于 2019-8-30 15:34
被采臣·宁编辑
,原因:
|
|
|
|
|
|
【爆】除了谷歌安卓断供,ARM也断供华为,那X86架构呢?
当中国人不容易,人多地少,生活压力太大。所以,我们男人都要有备胎计划,万一失业了怎么办?能不能养活一家老小。万一老婆不让干了怎么办?二老婆能不能顶上。
最后于 2019-5-23 11:46
被采臣·宁编辑
,原因:
|
|
|
[求助]求教如何把函数地址的符号字符串。写出来
X64dbgPy插件,在python脚本中引入r2pipe包来获取函数名和地址。 |
|
|
[求助]求教如何把函数地址的符号字符串。写出来
君子动口不动手,纸上谈兵我可以,用radare2脚本可以很快解决,例如判断下图中的 0x18000b7ef 地址是在哪个导出函数中: 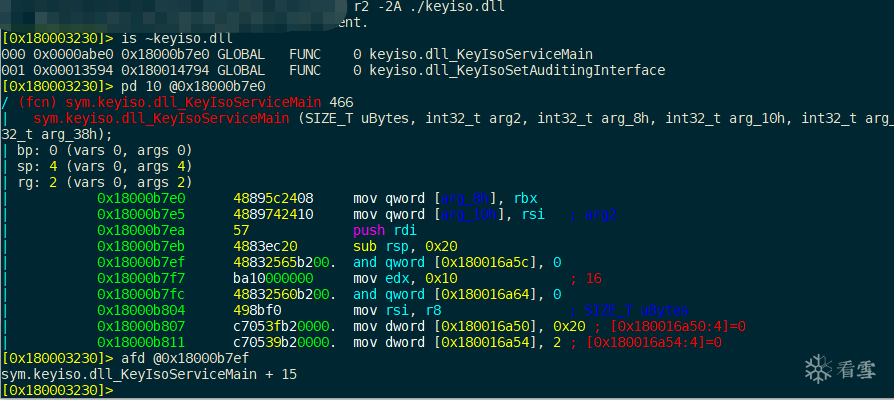
最后于 2019-5-21 17:39
被采臣·宁编辑
,原因:
|
|
|
|
|
|
[求助]求教如何把函数地址的符号字符串。写出来
我想了想,两种方法:一种是恢复push ebp; mov ebp,esp;修改为正确的函数地址。另一种是:反汇编所有的导出函数,再判断地址在哪个函数区间就行了。 |
|
|
[注意]我还活着
小朋友 |
|
|
|
|
|
[讨论]逆向是青春饭的行业吗
逆向只能当兴趣,当行业的话,只有那么顶尖的一小部分人才可以吧!就投入时间和收益比,哪个行业都比逆向挣钱。卖菜开杂货店开小吃店都比逆向强。 |
|
|
[求助]求教如何把函数地址的符号字符串。写出来
我的想法是,先遍历目标进程所有载入的DLL,再根据7600DB0B这个地址获取到底是哪个DLL的函数,减去DLL载入基址后,再找导出函数表。有现成的库,好象叫titan什么的。 |
|
|
|
|
|
[求助]Xposed框架开发的大佬有没有研究过怎么让微信自动下载图片啊!
android上有一个APP叫 微痕迹,能实现这种功能。原理就是微信会把所有的图片和视频都会保存在本地。 |
|
|
|
|
|
[注意]测试你的肺活量,按住键盘0,憋气,看你能有多少行,男人不做假!
0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 |
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值