|
|
|
|
|
|
|
|
如何判断一个exe程序是用什么语言写的啊?谢谢
這樣說好了。
#include <iostream.h>
#include <stdio.h>
#include <windows.h>
#include <stdlib.h>
#include <math.h>
int main()
{
int a;
printf("Hello World!");
system("PAUSE");
return 0;
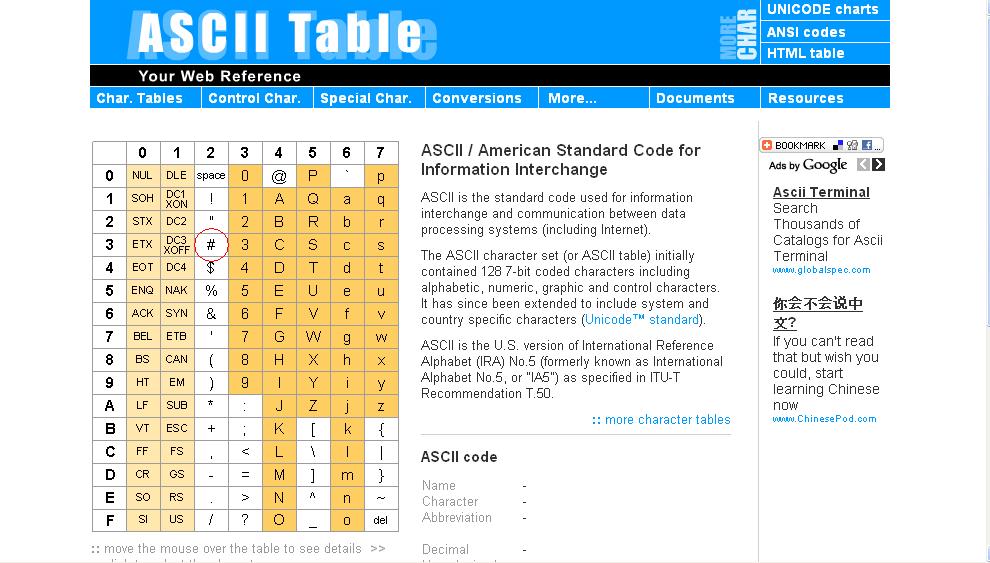
}分別透過 DEV C++ 4.01 版 及 Mscrosoft Visuall C++ 6.0 版進行 compiled. (在附件可見) 然後透過 file dump 或是其他的 hex editor 去看看這個 exe file 的內容。 我們可以得到初步的結果: 1) 對於 DEV C++ 所產生的 exe file 來說,裡面沒辦法直接的看到 DEV 等字樣的 information. 2) 對於 Microsoft Visuall C++ 6.0 版所 compiled 的 exe file 來說,比較容易 search 到 " Microsoft Visuall C++ " 這個字樣。 當然,這方法只是簡易地,在你沒有任何像 PEiD這類的 tools 在手邊時,你得想辦法用其它的方法達到目的。 以上是直接 view file 的 contents. 3) 第三種是, “殘餘”。 什麼是 tail of remainder? For example, test.ex_.DEVC401.txt 是 21.5 KB (22,016 bytes),這是這個 file 的 size, 但,在電腦上,並不是這樣。 22016/ 2048 = 10.75 一個 sector 可以儲存 2048 bytes. 那 22016 bytes 則需要 10.75 個 sectors. 又,你的 PC 會用 11 個 sectors 來放 這個 file. 所以,最後的那個 sector (也就是第 11 個 sector),只存放 1536 bytes. 那還有 512 個unavailable bytes,這個 512 bytes 就叫 "殘餘"。 殘餘並沒辦法用來當做 available disk space,那這 512 會放什麼 contents? Good question! 沒人知道。 可能....如.... 1) 當你 read/write file 時,尤其在 compiling 階段所產生 exe file 時,PC 就 "隨手" 把 memory 某一個 fragmentation segment 的內容給 "填補" 進去。講白話文叫 " 湊整數"。 2) 其它。 ※ 以上描述的很雜亂,請見諒。如有興趣者,請自己去 try try 看,体驗一次就會明白。 |
|
|
如何判断一个exe程序是用什么语言写的啊?谢谢
因為你只看見你看懂的,你沒仔細理解我所說的。 |
|
|
如何判断一个exe程序是用什么语言写的啊?谢谢
有時候得看運氣。 舉例來說: 當 我 compiled 一個 exe file,然後我 send 給你時,在 tail 的 sector 上會有 " 殘餘" 的 information. 當這個 file 轉手很多人之後,這個 " 殘餘" 會隨之降低。 這個關係是與轉手次數成反比遞減。 |
|
|
如何判断一个exe程序是用什么语言写的啊?谢谢
To adairs, 所謂的 eof, 指的就是檔案的尾巴。 為什麼要去找檔案的尾巴? 因為....這涉及到 FS (file system) 及 diskette 的設計原理。 這個方法對所有的 file 都適用,不一定只有 exe file. |
|
|
[分享]真是利害。
z 大真有求知精神。 |
|
|
如何判断一个exe程序是用什么语言写的啊?谢谢
除了眾版友的方法外,還有一個更簡單的方法。 去查看 eof 的那個 sector. 什麼叫 eof 的 sector? 簡單來說,就是查看那個 exe file 的磁區(sector),通常在 eof( end of file)後,會有 "空著" (available)的一些 information,而這些 information 都是以 "plaintext" 的 ascii 方式呈現出來的。 有時後運氣好,可以直接看見這些 information,譬如那一種 compiler 及 version. 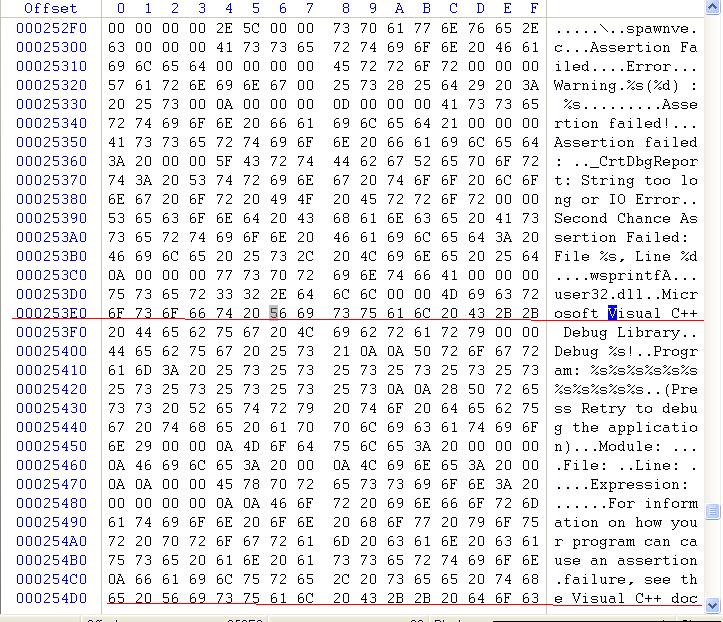
|
|
|
|
|
|
|
|
|
大家快来围观---刷KX!!!
建議 lin 版獎勵 zapline 。 |
|
|
[分享]真是利害。
沒人買邀請碼給她啊,我給的兩組都失效。 |
|
|
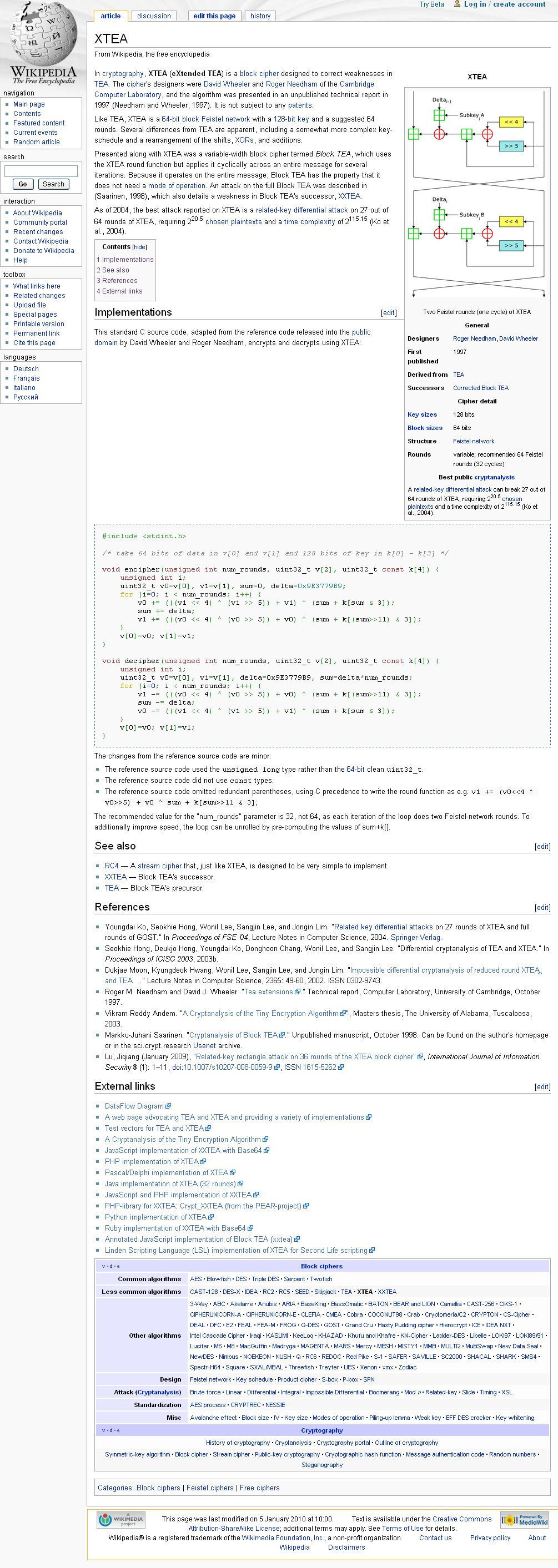
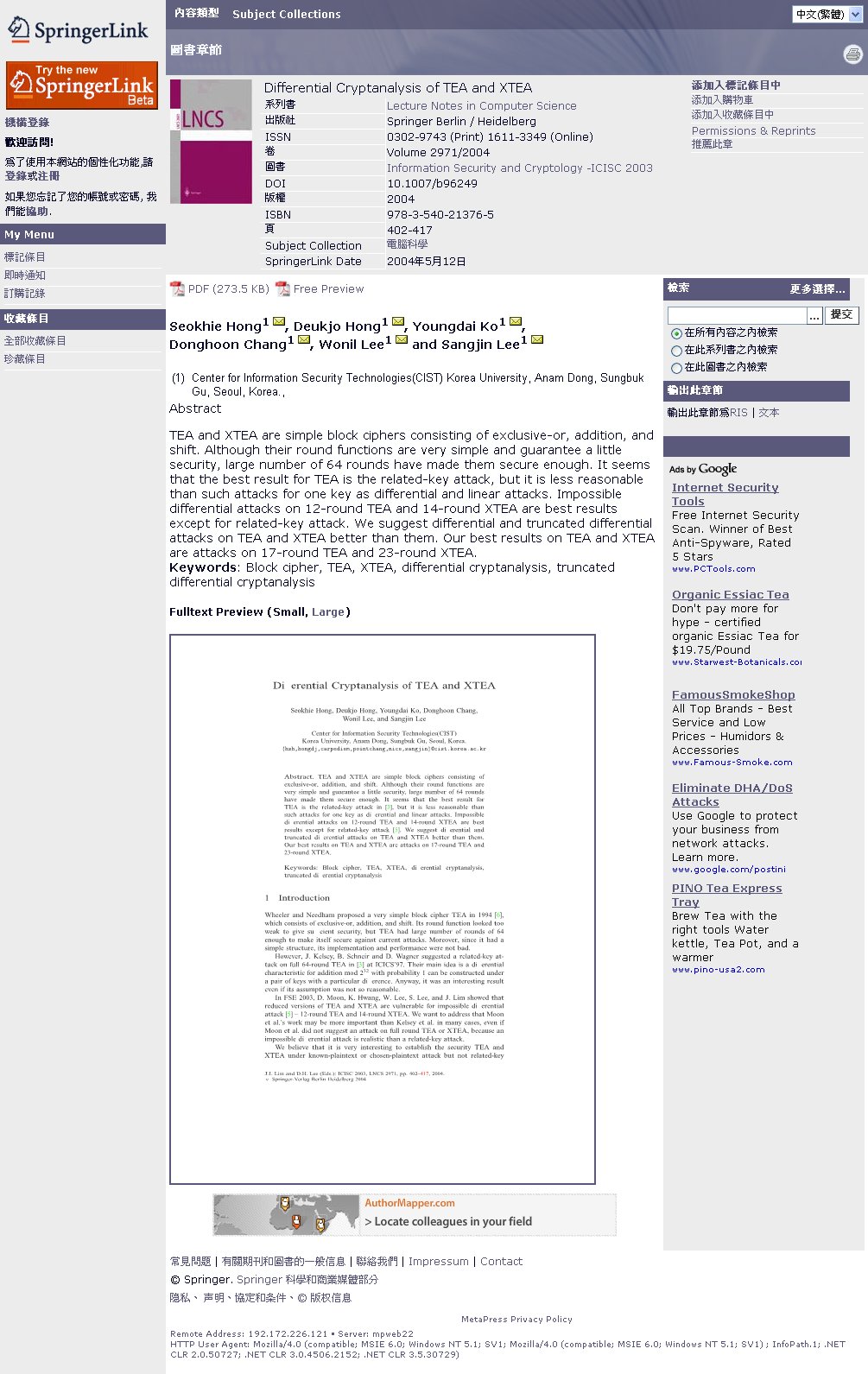
[求助]爆破XTEA的KEY
就等你寫出來呀,自然就會有人去驗證。 |
|
|
[分享][GC'10] To submit your Tutorial/Workshop proposals
Dear friends, I am writing to invite you to submit your papers to IEEE GLOBECOM 2010 (at Miami) before the paper submission deadline of March 15, 2010. Please check out the GC10 website: (http://www.ieee-globecom.org/2010/), and review the following highlights at GC10: (1) 25+ world renowned scientists will deliver Plenary Speeches in Featured Talks and Plenary Forums; (2) First-time FREE tutorial program open to all GC10 attendees (with 12 high-quality tutorials selected from 150 proposals); (3) 23 engaged workshops to cover the latest industry and academic advancements; (4) Local information introduction to beautiful Miami & Florida, as well as the wonderful conference venue. Thanks. Please let me know if you have any questions. Haohong Wang TPC Chair, IEEE GLOBECOM 2010 http://www.ieee-globecom.org/2010/ |
|
|
|
|
|
[求助]爆破XTEA的KEY
從 3 F 至 7F 的文章階轉載自 http://143.53.36.235:8080/source.htm,希望樓主多花點時間找找看,會找得到。 研究之後若有心得,歡迎再分享給大眾。 謝謝。 |
|
|
[求助]爆破XTEA的KEY
16-bit x86 (New Variant) ;; ;; An implementation of the XTEA algorithm in 16-bit 80x86 assembly ;; language. This should work on any processor in the 80x86 family ;; but works best with the 16-bit members of the family (80x86 for ;; x <= 2). This assembly language is suitable for use with linux-86 ;; and the as86 assembler, but should be fairly trivial to convert ;; so it will assemble with some other assembler easily. It has been ;; tested with 16-bit objects for Linux-8086 (ELKS), and should work ;; under DOS with the tiny and small memory models. To make it ;; work with the large and huge memory models, it will probably be ;; necessary to reset the parameters (bp+4 becomes bp+6 and so on), ;; and segment loads may need to be done as well (les and lds). ;; ;; Wasn't so easy to write because the number of registers available ;; on the 80x86 is kinda small...and they're 16-bit registers too! ;; ;; Placed in the Public Domain by Rafael R. Sevilla ;; ;; .text export _xtea_encipher_asm _xtea_encipher_asm: push bp mov bp,sp sub sp,#14 ; space for y, z, sum, and n push si push di ;; bp+8 = pointer to key information ;; bp+6 = pointer to ciphertext to return to caller ;; bp+4 = pointer to plaintext ;; bp+2 = return address from caller ;; bp = pushed bp ;; bp-2 = y high word ;; bp-4 = y low word ;; bp-6 = z high word ;; bp-8 = z low word ;; bp-10 = sum high word ;; bp-12 = sum low word ;; bp-14 = n ;; bp-16 = pushed si ;; bp-18 = pushed di mov bx,[bp+4] ; get address of plaintext mov ax,[bx] ; low word of first dword of plaintext mov [bp-4],ax mov ax,[bx+2] ; high word mov [bp-2],ax mov ax,[bx+4] ; second dword of plaintext (low) mov [bp-8],ax mov ax,[bx+6] ; (high) mov [bp-6],ax xor ax,ax ; zero the sum initially mov [bp-10],ax mov [bp-12],ax mov byte ptr [bp-14],#32 ; set n (just 8 bits), # rounds ;; begin encryption encipher_rounds: ;; compute new y mov ax,[bp-8] ; low word z mov bx,[bp-6] ; high word z mov cx,ax ; copy to the rest of the registers mov dx,bx mov si,ax mov di,bx ;; (z<<4) ^ (z>>5) shl ax,#1 ; shift left once rcl bx,#1 shl ax,#1 ; shift twice rcl bx,#1 shl ax,#1 ; shift three times rcl bx,#1 shl ax,#1 ; shift four times rcl bx,#1 shr dx,#1 ; shift right once rcr cx,#1 shr dx,#1 ; shift right twice rcr cx,#1 shr dx,#1 ; shift right three times rcr cx,#1 shr dx,#1 ; shift right four times rcr cx,#1 shr dx,#1 ; shift right five times rcr cx,#1 xor ax,cx ; combine xor dx,bx ; dx:ax has result xor si,[bp-12] ; combine to sum xor di,[bp-10] add ax,si ; add them together adc dx,di mov bx,[bp-12] ; get low word of sum (all we need for this) and bx,#3 ; get low two bits (modulo 4) shl bx,#1 ; convert to dword offset shl bx,#1 add bx,[bp+8] ; add to base address of key info add ax,[bx] ; low word of key adc dx,[bx+2] ; high word of key add [bp-4],ax ; add back to y adc [bp-2],dx ;; update sum mov ax,#0x79b9 ; low word of delta add [bp-12],ax mov ax,#0x9e37 ; high word of delta adc [bp-10],ax ;; compute new z mov ax,[bp-4] ; low word of y mov bx,[bp-2] ; high word of y mov cx,ax ; copy to the rest of the registers mov dx,bx mov si,ax mov di,bx ;; (y<<4) ^ (y>>5) shl ax,#1 ; shift left once rcl bx,#1 shl ax,#1 ; shift twice rcl bx,#1 shl ax,#1 ; shift three times rcl bx,#1 shl ax,#1 ; shift four times rcl bx,#1 shr dx,#1 ; shift right once rcr cx,#1 shr dx,#1 ; shift right twice rcr cx,#1 shr dx,#1 ; shift right three times rcr cx,#1 shr dx,#1 ; shift right four times rcr cx,#1 shr dx,#1 ; shift right five times rcr cx,#1 xor ax,cx ; combine xor dx,bx ; dx:ax has result xor si,[bp-12] ; combine to sum xor di,[bp-10] add ax,si ; add them together adc dx,di mov bx,[bp-12] ; get sum low word mov cx,[bp-10] ; get sum high word shr cx,#1 ; shift right once rcr bx,#1 shr cx,#1 ; shift right twice rcr bx,#1 shr cx,#1 ; shift right three times rcr bx,#1 shr cx,#1 ; shift right four times rcr bx,#1 shr cx,#1 ; shift right five times rcr bx,#1 shr cx,#1 ; shift right six times rcr bx,#1 shr cx,#1 ; shift right seven times rcr bx,#1 shr cx,#1 ; shift right eight times rcr bx,#1 shr cx,#1 ; shift right nine times rcr bx,#1 shr cx,#1 ; shift right ten times rcr bx,#1 shr cx,#1 ; shift right eleven times rcr bx,#1 and bx,#3 shl bx,#1 ; convert to dword offset shl bx,#1 add bx,[bp+8] ; add to base address of key add ax,[bx] ; low word of key adc dx,[bx+2] ; high word of key add [bp-8],ax ; add back to z adc [bp-6],dx dec byte ptr [bp-14] ; decrement rounds counter jz finish_encipher jmp near encipher_rounds finish_encipher: mov bx,[bp+6] ; get address of ciphertext storage mov ax,[bp-4] ; y, low word mov [bx],ax mov ax,[bp-2] ; y, high word mov [bx+2],ax mov ax,[bp-8] ; z, low word mov [bx+4],ax mov ax,[bp-6] ; z, high word mov [bx+6],ax pop di pop si add sp,#14 ; discard local vars pop bp ret export _xtea_decipher_asm _xtea_decipher_asm: push bp mov bp,sp sub sp,#14 ; space for y, z, sum, and n push si push di ;; bp+8 = pointer to key information ;; bp+6 = pointer to plaintext to return to caller ;; bp+4 = pointer to ciphertext ;; bp+2 = return address from caller ;; bp = pushed bp ;; bp-2 = y high word ;; bp-4 = y low word ;; bp-6 = z high word ;; bp-8 = z low word ;; bp-10 = sum high word ;; bp-12 = sum low word ;; bp-14 = n ;; bp-16 = pushed si ;; bp-18 = pushed di mov bx,[bp+4] ; get address of ciphertext mov ax,[bx] ; low word of first dword of ciphertext mov [bp-4],ax mov ax,[bx+2] ; high word mov [bp-2],ax mov ax,[bx+4] ; second dword of ciphertext (low) mov [bp-8],ax mov ax,[bx+6] ; (high) mov [bp-6],ax mov ax,#0x3720 ; low word of initial sum mov [bp-12],ax mov ax,#0xc6ef mov [bp-10],ax mov byte ptr [bp-14],#32 ; set n (just 8 bits), # rounds ;; begin decryption decipher_rounds: mov ax,[bp-4] ; low word of y mov bx,[bp-2] ; high word of y mov cx,ax ; copy to the rest of the registers mov dx,bx mov si,ax mov di,bx ;; (y<<4) ^ (y>>5) shl ax,#1 ; shift left once rcl bx,#1 shl ax,#1 ; shift twice rcl bx,#1 shl ax,#1 ; shift three times rcl bx,#1 shl ax,#1 ; shift four times rcl bx,#1 shr dx,#1 ; shift right once rcr cx,#1 shr dx,#1 ; shift right twice rcr cx,#1 shr dx,#1 ; shift right three times rcr cx,#1 shr dx,#1 ; shift right four times rcr cx,#1 shr dx,#1 ; shift right five times rcr cx,#1 xor ax,cx ; combine xor dx,bx ; dx:ax has result xor si,[bp-12] ; combine to sum xor di,[bp-10] add ax,si ; add them together adc dx,di mov bx,[bp-12] ; get sum low word mov cx,[bp-10] ; get sum high word shr cx,#1 ; shift right once rcr bx,#1 shr cx,#1 ; shift right twice rcr bx,#1 shr cx,#1 ; shift right three times rcr bx,#1 shr cx,#1 ; shift right four times rcr bx,#1 shr cx,#1 ; shift right five times rcr bx,#1 shr cx,#1 ; shift right six times rcr bx,#1 shr cx,#1 ; shift right seven times rcr bx,#1 shr cx,#1 ; shift right eight times rcr bx,#1 shr cx,#1 ; shift right nine times rcr bx,#1 shr cx,#1 ; shift right ten times rcr bx,#1 shr cx,#1 ; shift right eleven times rcr bx,#1 and bx,#3 shl bx,#1 ; convert to dword offset shl bx,#1 add bx,[bp+8] ; add to base address of key add ax,[bx] ; low word of key adc dx,[bx+2] ; high word of key sub [bp-8],ax ; subtract from z sbb [bp-6],dx ;; update sum mov ax,#0x79b9 ; low word of delta sub [bp-12],ax mov ax,#0x9e37 ; high word of delta sbb [bp-10],ax ;; compute new y mov ax,[bp-8] ; low word z mov bx,[bp-6] ; high word z mov cx,ax ; copy to the rest of the registers mov dx,bx mov si,ax mov di,bx ;; (z<<4) ^ (z>>5) shl ax,#1 ; shift left once rcl bx,#1 shl ax,#1 ; shift twice rcl bx,#1 shl ax,#1 ; shift three times rcl bx,#1 shl ax,#1 ; shift four times rcl bx,#1 shr dx,#1 ; shift right once rcr cx,#1 shr dx,#1 ; shift right twice rcr cx,#1 shr dx,#1 ; shift right three times rcr cx,#1 shr dx,#1 ; shift right four times rcr cx,#1 shr dx,#1 ; shift right five times rcr cx,#1 xor ax,cx ; combine xor dx,bx ; dx:ax has result xor si,[bp-12] ; combine to sum xor di,[bp-10] add ax,si ; add them together adc dx,di mov bx,[bp-12] ; get low word of sum (all we need for this) and bx,#3 ; get low two bits (modulo 4) shl bx,#1 ; convert to dword offset shl bx,#1 add bx,[bp+8] ; add to base address of key info add ax,[bx] ; low word of key adc dx,[bx+2] ; high word of key sub [bp-4],ax ; subtract from y sbb [bp-2],dx dec byte ptr [bp-14] ; decrement rounds counter jz finish_decipher jmp near decipher_rounds finish_decipher: mov bx,[bp+6] ; get address of ciphertext storage mov ax,[bp-4] ; y, low word mov [bx],ax mov ax,[bp-2] ; y, high word mov [bx+2],ax mov ax,[bp-8] ; z, low word mov [bx+4],ax mov ax,[bp-6] ; z, high word mov [bx+6],ax pop di pop si add sp,#14 ; discard local vars pop bp ret |
|
|
[求助]爆破XTEA的KEY
ANSI C (New Variant) void encipher(const unsigned long *const v,unsigned long *const w,
const unsigned long * const k)
{
register unsigned long y=v[0],z=v[1],sum=0,delta=0x9E3779B9,n=32;
while(n-->0)
{
y += (z << 4 ^ z >> 5) + z ^ sum + k[sum&3];
sum += delta;
z += (y << 4 ^ y >> 5) + y ^ sum + k[sum>>11 & 3];
}
w[0]=y; w[1]=z;
}
void decipher(const unsigned long *const v,unsigned long *const w,
const unsigned long * const k)
{
register unsigned long y=v[0],z=v[1],sum=0xC6EF3720,
delta=0x9E3779B9,n=32;
/* sum = delta<<5, in general sum = delta * n */
while(n-->0)
{
z -= (y << 4 ^ y >> 5) + y ^ sum + k[sum>>11 & 3];
sum -= delta;
y -= (z << 4 ^ z >> 5) + z ^ sum + k[sum&3];
}
w[0]=y; w[1]=z;
}
|
|
|
[求助]爆破XTEA的KEY
Motorola 680x0 (Metrowerks CodeWarrior style) asm void encipher(const unsigned long* const v,unsigned long* const w,
const unsigned long* const k)
{
fralloc
movem.l d3-d7/a2,-(a7)
/* load initial registers
d0: y = v[0]
d1: z = v[1]
d2: a = k[0]
d3: b = k[1]
d4: c = k[2]
d5: loop counter (k[3] in a2)
d6: scratch register 1
d7: scratch register 2
a0: sum
a1: delta = 0x9E3779B9;
a2: d = k[3] */
move.l v,a0
move.l (a0),d0
move.l 4(a0),d1
move.l k,a0
move.l (a0),d2
move.l 4(a0),d3
move.l 8(a0),d4
move.l 12(a0),a2
move.l #0x9E3779B9,a0
move.l #0x9E3779B9,a1
moveq.l #15,d5 // sixteen rounds
// d6 = (z<<4)+a
loop: move.l d1,d6
lsl.l #4,d6
add.l d2,d6
// d7 = z+sum
move.l d1,d7
add.l a0,d7
// d7 = ((z<<4)+a)^(z+sum)
eor.l d6,d7
// d6 = (z>>5)+b
move.l d1,d6
lsr.l #5,d6
add.l d3,d6
// d7 = ((z<<4)+a)^(z+sum)^((z>>5)+b)
eor.l d6,d7
// add back into y
add.l d7,d0
// d6 = (y<<4)+c
move.l d0,d6
lsl.l #4,d6
add.l d4,d6
// d7 = y+sum
move.l d0,d7
add.l a0,d7
// d7 = ((y<<4)+c)^(y+sum)
eor.l d6,d7
// d6 = (y>>5)+d
move.l d0,d6
lsr.l #5,d6
add.l a2,d6
// d7 = ((y<<4)+c)^(y+sum)^((y>>5)+d)
eor.l d6,d7
// add back into z
add.l d7,d1
// sum+=delta
adda.l a1,a0
// branch back and do it again
dbra d5,loop
// place the result back into w
move.l w,a0
move.l d0,(a0)
move.l d1,4(a0)
movem.l (a7)+,d3-d7/a2
frfree
rts
}
asm void decipher(const unsigned long *const v,unsigned long *const w,
const unsigned long *const k)
{
fralloc
movem.l d3-d7/a2,-(a7)
/* load initial registers
d0: y = v[0]
d1: z = v[1]
d2: a = k[0]
d3: b = k[1]
d4: c = k[2]
d5: loop counter (k[3] in a2)
d6: scratch register 1
d7: scratch register 2
a0: sum = 0xE3779B90 (delta * 16)
a1: delta = 0x9E3779B9;
a2: d = k[3] */
move.l v,a0
move.l (a0),d0
move.l 4(a0),d1
move.l k,a0
move.l (a0),d2
move.l 4(a0),d3
move.l 8(a0),d4
move.l 12(a0),a2
move.l #0xE3779B90,a0
move.l #0x9E3779B9,a1
moveq.l #15,d5 // sixteen rounds
// d6 = (y<<4)+c
loop: move.l d0,d6
lsl.l #4,d6
add.l d4,d6
// d7 = y+sum
move.l d0,d7
add.l a0,d7
// d7 = ((y<<4)+c)^(y+sum)
eor.l d6,d7
// d6 = (y>>5)+d
move.l d0,d6
lsr.l #5,d6
add.l a2,d6
// d7 = ((y<<4)+c)^(y+sum)^((y>>5)+d)
eor.l d6,d7
// subtract from z
sub.l d7,d1
// d6 = (z<<4)+a
move.l d1,d6
lsl.l #4,d6
add.l d2,d6
// d7 = z+sum
move.l d1,d7
add.l a0,d7
// d7 = ((z<<4)+a)^(z+sum)
eor.l d6,d7
// d6 = (z>>5)+b
move.l d1,d6
lsr.l #5,d6
add.l d3,d6
// d7 = ((z<<4)+a)^(z+sum)^((z>>5)+b)
eor.l d6,d7
// subtract from y
sub.l d7,d0
// sum-=delta
suba.l a1,a0
// branch back and do it again
dbra d5,loop
// place the result back into w
move.l w,a0
move.l d0,(a0)
move.l d1,4(a0)
movem.l (a7)+,d3-d7/a2
frfree
rts
}
|
|
|
[求助]爆破XTEA的KEY
Motorola PowerPC (Metrowerks CodeWarrior Style) asm void encipher(register const unsigned long * const v,
register unsigned long * const w,
register const unsigned long * const k)
{
// On entry, v = r3, w = r4, k = r5
// use r3 and r5 as scratch
// r0 = v[0]
// r6 = v[1]
// r7 - r10 = k[0] - k[3]
// r11 = sum
// r12 = delta
li r11,0 // sum = 0
li r12,0x79B9 // delta =0x9E3779B9
addis r12,r12,0x9E37
li r0,16 // loop counter into count register
mtctr r0
lwz r0,0(r3) // put the contents of v and k into the registers
lwz r6,4(r3)
lwz r7,0(r5)
lwz r8,4(r5)
lwz r9,8(r5)
lwz r10,12(r5)
loop: add r11,r11,r12 // sum += delta
slwi r5,r6,4 // z << 4
add r5,r5,r7 // (z << 4) + a
add r3,r6,r11 // z + sum
xor r3,r5,r3 // ((z << 4) + a) ^ (z + sum)
srwi r5,r6,5 // z >> 5
add r5,r5,r8 // (z >> 5) + b
xor r3,r5,r3 // ((z << 4)+a)^(z+sum)^((z >> 5)+b);
add r0,r0,r3 // y += result
slwi r5,r0,4 // y << 4
add r5,r5,r9 // (y << 4) +c
add r3,r0,r11 // y + sum
xor r3,r5,r3 // ((y << 4) +c) ^ (y + sum)
srwi r5,r0,5 // y >> 5
add r5,r5,r10 // (y >> 5) + d
xor r3,r5,r3 // ((y << 4)+c)^(y+sum)^((y >> 5)+d);
add r6,r6,r3 // z += result
bdnz+ loop // decrement CTR and branch
stw r0,0(r4) // store result back in w
stw r6,4(r4)
blr
}
asm void decipher(register const unsigned long * const v,
register unsigned long * const w,
register const unsigned long * const k)
{
// On entry, v = r3, w = r4, k = r5
// use r3 and r5 as scratch
// r0 = v[0]
// r6 = v[1]
// r7 - r10 = k[0] - k[3]
// r11 = sum
// r12 = delta
li r11,0x9B90; // sum =0xE3779B90
addis r11,r11,0xE378;
li r12,0x79B9 // delta =0x9E3779B9
addis r12,r12,0x9E37
li r0,16 // loop counter into count register
mtctr r0
lwz r0,0(r3) // put the contents of v and k into the registers
lwz r6,4(r3)
lwz r7,0(r5)
lwz r8,4(r5)
lwz r9,8(r5)
lwz r10,12(r5)
loop: slwi r5,r0,4 // y << 4
add r5,r5,r9 // (y << 4) + c
add r3,r0,r11 // y + sum
xor r3,r5,r3 // ((y << 4) + c) ^ (y + sum)
srwi r5,r0,5 // y >> 5
add r5,r5,r10 // (y >> 5) + d
xor r3,r5,r3 // ((y << 4)+c)^(y+sum)^((y >> 5)+d)
sub r6,r6,r3 // z -= result
slwi r5,r6,4 // z << 4
add r5,r5,r7 // (z << 4) + a
add r3,r6,r11 // z + sum
xor r3,r5,r3 // ((z << 4) + a) ^ (z + sum)
srwi r5,r6,5 // z >> 5
add r5,r5,r8 // (z >> 5) + b
xor r3,r5,r3 // ((z << 4)+a)^(z+sum)^((z >> 5)+b);
sub r0,r0,r3 // y -= result
sub r11,r11,r12 // sum -= delta
bdnz+ loop // decrement CTR and branch
stw r0,0(r4) // store result back in w
stw r6,4(r4)
blr
}
|
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值