|
|
[求助]RSA C算法实现
/*
* rsatest.c
*/
#include <stdio.h>
#include <stdlib.h>
#include "mrsa.h"
void
main(int i, char **v) {
NN m,c,d;
rsa_key key;
char s[NSIZE*4+2];
if(i==4) {
hn(c,v[1]);
hn(d,v[2]);
hn(m,v[3]);
em(c,d,m);
nh(s,c); puts(s);
exit(EXIT_SUCCESS);
}
if(i!=3) {
puts("Usage: mtest [hex_pseed] [hex_qseed]");
exit(EXIT_FAILURE);
}
hn(key.p,v[1]);
hn(key.q,v[2]);
puts("Generating key...");
if(!rsa_gen(&key)) {
puts("Failed, try other seed values.");
exit(EXIT_FAILURE);
}
puts("Done, key components: pq,e,d,p,q,dp,dq,qp");
printf("bits = %u\n",key.b);
nh(s,key.pq); puts(s);
nh(s,key.e); puts(s);
nh(s,key.d); puts(s);
nh(s,key.p); puts(s);
nh(s,key.q); puts(s);
nh(s,key.dp); puts(s);
nh(s,key.dq); puts(s);
nh(s,key.qp); puts(s);
puts("testing, msg,cip,dec1,dec2");
cl(m);
randomize(m, key.b-2);
nh(s,m); puts(s);
cp(c,m); rsa_enc(c,&key);
nh(s,c); puts(s);
cp(d,c); em(d,key.d,key.pq); /* slow way */
nh(s,d); puts(s);
cp(d,c); rsa_dec(d,&key); /* faster way */
nh(s,d); puts(s);
exit(EXIT_SUCCESS);
}
/*
* mrsa.c -- portable multiprecision math and RSA library
* 1993 Risto Paasivirta, paasivir@jyu.fi
* Public Domain, no warranty.
*/
#define MRSA_C 1
#include "mrsa.h"
/*
* math library stuff
*/
/*
* sign = ts(N a) -- test signed, returns 1, 0 or -1
*/
PRIVATE int
ts(N a)
{
ULONG i = NSIZE;
if (a[NSIZE - 1] & SIGN_BIT)
return -1;
while (i--)
if (*a++)
return 1;
return 0;
}
/*
* carry = ng(N a) -- negate, returns carry
*/
PRIVATE ULONG
ng(N a)
{
ULONG c = 0, i = NSIZE;
while (i--) {
c = 0 - *a - c;
*a++ = c;
c = (c >> UNIT_BITS) & 1;
} return c;
}
/*
* cl(N a) -- clear value, a = 0
*/
PRIVATE void
cl(N a)
{
ULONG i = 0;
while (i++ < NSIZE)
*a++ = 0;
}
/*
* cp(N a, N b) -- copy, a = b
*/
PRIVATE void
cp(N a, N b)
{
ULONG i = NSIZE;
while (i--)
*a++ = *b++;
}
/*
* flag = cu(a, b) -- compare unsigned, returns <0 if a<b, 0 if a==b, >0 if a>b
*/
PRIVATE int
cu(N a, N b)
{
ULONG i = NSIZE;
a += NSIZE;
b += NSIZE;
while (i--)
if (*--a - *--b)
return (int) *a - (int) *b;
return 0;
}
/*
* carry = ad(N a, N b) -- add, a += b
*/
PRIVATE ULONG
ad(N a, N b)
{
ULONG c = 0, i = NSIZE;
while (i--) {
c = *b++ + *a + c;
*a++ = c;
c >>= UNIT_BITS;
}
return c;
}
/*
* carry = sb(N a, N b) -- substract, a -= b
*/
PRIVATE ULONG
sb(N a, N b)
{
ULONG c = 0, i = NSIZE;
while (i--) {
c = *a - *b++ - c;
*a++ = c;
c = (c >> UNIT_BITS) & 1;
}
return c;
}
/*
* carry = sr(N a) -- shift right, a >>= 1
*/
PRIVATE ULONG
sr(N a)
{
ULONG c = 0, i = NSIZE;
a += NSIZE;
while (i--) {
c |= *--a;
*a = c >> 1;
c = (c & 1) << UNIT_BITS;
}
return c;
}
/*
* carry = sl(N a) -- shift left, a <<= 1
*/
PRIVATE ULONG
sl(N a)
{
ULONG c = 0, i = NSIZE;
while (i--) {
c |= (ULONG) * a << 1;
*a++ = c;
c = (c >> UNIT_BITS) & 1;
}
return c;
}
/*
* dm(N a, N b, N c) -- divide-modulo unsigned, a = a / b, c = a % b
*/
PRIVATE void
dm(N a, N b, N c)
{
ULONG i = NSIZE * UNIT_BITS;
cl(c);
while (i--) {
sl(c);
*c |= sl(a);
if (sb(c, b)) {
ad(c, b);
} else {
*a |= 1;
}
}
}
/*
* remainder = di(N a, int n) -- divide by integer
*/
PRIVATE ULONG
di(N a, ULONG t)
{
ULONG c = 0, i = NSIZE;
while (i--) {
c = (c << UNIT_BITS) | a[i];
a[i] = c / t;
c = c % t;
}
return c;
}
/*
* mu(N a, N b) -- multiply unsigned, a *= b
*/
PRIVATE void
mu(N a, N b)
{
ULONG i = NSIZE * UNIT_BITS;
NN c;
cl(c);
while (i--) {
sl(c);
if (sl(a))
ad(c, b);
}
cp(a, c);
}
/*
* mm(N a, N b, N m) -- modular multiply, a = a * b mod m
*/
PRIVATE void
mm(N a, N b, N m)
{
ULONG i = NSIZE * UNIT_BITS;
NN c;
cl(c);
while (i--) {
sl(c);
if (sb(c, m))
ad(c, m);
if (sl(a))
ad(c, b);
if (sb(c, m))
ad(c, m);
}
cp(a, c);
}
/*
* pmm(N a, N b, N m, ULONG p) -- internal modmul w/precision for modexp
*/
#ifndef AMIGA
static void
pmm(N aa, N b, N m, ULONG p)
{
ULONG k, c, j = UNIT_BITS, i;
NN v;
N a;
i = p;
cl(v);
a = aa + p;
while (!*--a
&& i)
i--;
if (i) {
while (!(*a & (1 << j)) && j)
j--;
cp(v, b);
} while (i--) {
while (j--) {
for (k = 0, c = 0; k < p; k++) {
c |= (ULONG) v[k] << 1;
v
[k] = c;
c >>= UNIT_BITS;
} for (k = 0, c = 0; k < p; k++) {
c = v[k] - m[k] - c;
v[k] = c;
c = (c >> UNIT_BITS) & 1;
} if (c)
for (k = 0, c = 0; k < p; k++) {
c = v[k] + m[k] + c;
v[k] = c;
c >>= UNIT_BITS;
} if (*a & (1 << j)) {
for (k = 0, c = 0; k < p; k++) {
c = v[k] + b[k] + c;
v[k] = c;
c >>= UNIT_BITS;
} for (k = 0, c = 0; k < p; k++) {
c = v[k] - m[k] - c;
v[k] = c;
c = (c >> UNIT_BITS) & 1;
} if (c)
for (k = 0, c = 0; k < p; k++) {
c = v[k] + m[k] + c;
v[k] = c;
c >>= UNIT_BITS;
}
}
}
a--;
j = UNIT_BITS;
}
cp(aa, v);
}
#endif
/*
* em(N a, N b, N m) -- modular exponentation, a = a^b mod n
*/
PRIVATE void
em(N a, N e, N m)
{
ULONG i = NSIZE, j = UNIT_BITS, p = NSIZE;
NN c;
N mp;
cl(c);
*c = 1;
e += NSIZE;
while (!*--e && i)
i--;
if (i) {
while (!(*e & (1 << j)))
j--;
cp(c, a);
}
mp = m + NSIZE;
while (!*--mp && p)
p--;
if (*mp & SIGN_BIT && p < NSIZE)
p++;
while (i--) {
while (j--) {
pmm(c, c, m, p);
if (*e & (1 << j))
pmm(c, a, m, p);
}
e--;
j = UNIT_BITS;
}
cp(a, c);
}
/*
* gd(N a, N b) -- a = greatest common divisor(a,b)
*/
PRIVATE void
gd(N a, N bb)
{
NN r, b;
cp(b, bb);
while (ts(b)) {
dm(a, b, r);
cp(a, b);
cp(b, r);
}
}
/*
* iv(N a, N b) -- multiplicative inverse, a = a^{-1} mod b
*/
PRIVATE void
iv(N a, N b)
{
NN c, d, e, f, g, y;
cp(c, b);
cl(e);
cl(f);
*f = 1;
while (ts(a)) {
cp(y, c);
dm(y, a, d);
if (f[NSIZE - 1] & SIGN_BIT) {
ng(f);
mu(y, f);
ng(f);
ng(y);
} else
mu(y, f);
cp(g, e);
sb(g, y);
cp(c, a);
cp(a, d);
cp(e, f);
cp(f, g);
}
if (e[NSIZE - 1] & SIGN_BIT)
ad(e, b);
cp(a, e);
}
/*
* nh(char *a, N b) -- convert value to a hex string (use for debugging)
*/
PRIVATE void
nh(char *a, N b)
{
char *d = "0123456789abcdef";
NN c;
ULONG i = NSIZE * sizeof(UWORD) * 2; /* 2 digits/byte! */
cp(c, b);
a += NSIZE * sizeof(UWORD) * 2;
*a = 0;
while (i--) {
*--a = d[*c & 15];
sr(c);
sr(c);
sr(c);
sr(c);
}
}
/*
* hn(N a, char *b) -- lower-case hex string to value (use for constants)
*/
PRIVATE void
hn(N a, char *b)
{
cl(a);
while (*b) {
sl(a);
sl(a);
sl(a);
sl(a);
*a += *b < 'a' ? *b - '0' : *b - ('a' - 10);
b++;
}
}
/*
* integer = ri() -- generate weak pseudorandom integer (range 0-65535)
*/
PRIVATE ULONG
ri(void)
{
static ULONG s = 27182;
s = (s * 31421 + 6927) & 0xffff;
return s;
}
/*
* prime generation and RSA stuff
*/
/*
* randomize(N n, ULONG bits) -- pseudorandomize n, limit to value to
* range 2^bits to 2^(bits+1)-1. This function eors n with weak random
* generator, n should be initialized with at least bits-bit strong random
* value before call.
* (XXX check portablility when converting to >16-bit UWORD machine)
*/
void
randomize(N a, ULONG b)
{
ULONG i;
NN c;
N d = c;
cp(c,a);
cl(a);
if(b>UNIT_BITS*NSIZE-2) {
i = NSIZE-1;
b = UNIT_BITS-2;
} else {
i = b / UNIT_BITS;
b = b % UNIT_BITS;
}
while (i--)
*a++ = *d++ ^ ri();
*a = ((*d ^ ri()) & ((1 << b) - 1)) | (1 << b);
}
/*
* const sp[PRIMES], PRIMES -- table of small primes, number of primes in table
*/
static unsigned char sp[PRIMES] = {
2, 3, 5, 7, 11, 13, 17, 19, 23, 29, 31, 37, 41, 43, 47, 53,
59, 61, 67, 71, 73, 79, 83, 89, 97,101,103,107,109,113,127,131,
137,139,149,151,157,163,167,173,179,181,191,193,197,199,211,223,
227,229,233,239,241,251
};
/*
* divisor = sieve_prime(N n) -- try to find divisor of n by sieving
* with small integers returns divisor or 0 if no divisor found.
*/
ULONG
sieve_prime(N n)
{
ULONG i;
NN a;
for(i=0;i<PRIMES;i++) {
cp(a,n);
if(!di(a,sp[i]))
return ((ULONG)sp[i]);
}
return (0);
}
/*
* flag = prob_prime(N n) -- test if 2^(n-1) mod n == 1. Returns 0 if
* test failed, !0 if success. Large n which passes this test is a
* probable prime. This test does not work well with small value of n.
* Because this test is slow, you should first try sieving n.
*/
int
prob_prime(N m)
{
ULONG i = NSIZE, j = UNIT_BITS, p = NSIZE;
NN c, ee;
N mp, e = ee + NSIZE;
cl(c);
*c = 1;
cp(ee, m);
sb(ee, c);
while (!*--e && i)
i--;
if (i) {
while (!(*e & (1 << j)))
j--;
*c = 2;
}
mp = m + NSIZE;
while (!*--mp && p)
p--;
if (*mp & SIGN_BIT && p < NSIZE)
p++;
while (i--) {
while (j--) {
pmm(c, c, m, p);
if (*e & (1 << j)) {
sl(c);
if(sb(c, m)) ad(c, m);
}
}
e--;
j = UNIT_BITS;
}
cl(ee);
*ee = 1;
return (!cu(c,ee));
}
#ifndef THINK_SILENTLY
/*
* tw() -- indicate working when checking/generating primes
*/
#include <stdio.h> /* only for tw() */
static void
tw(void)
{
static ULONG j = 0;
putchar("/-\\|"[j & 3]);
j++;
putchar('\b');
fflush(stdout);
}
#endif /* THINK_SILENTLY */
/*
* next_prime(N a) -- find next probable prime >= a
*/
void
next_prime(N a)
{
NN b;
*a |= 1;
cl(b); *b = 2;
for (;;) {
#ifndef THINK_SILENTLY
tw();
#endif /* THINK_SILENTLY */
if (!sieve_prime(a)) {
if (prob_prime(a))
return;
}
ad(a, b);
}
}
/*
* bits rsa_gen(rsa_key *key) -- generate a RSA key from key->p and key->q
* Initialize key->p and key->q either with primes or strong random
* integers of apporopriate size. Returns number of bits in modulus key->pq
* or 0 if key generation failed.
*/
ULONG
rsa_gen(rsa_key *k)
{
NN p1, q1, pq1, f, g, t;
next_prime(k->p);
next_prime(k->q);
if (cu(k->p, k->q) < 0) {
cp(t, k->p);
cp(k->p, k->q);
cp(k->q, t);
}
hn(t, "1");
cp(p1, k->p);
sb(p1, t);
cp(q1, k->q);
sb(q1, t);
cp(g, p1);
gd(g, q1);
hn(t, "ff");
if (cu(t, g) < 0)
return 0;
cp(k->pq, k->p);
mu(k->pq, k->q);
cp(pq1, p1);
mu(pq1, q1);
cp(f, pq1);
dm(f, g, t);
hn(k->e, "3");
hn(k->qp, "1");
cp(t, pq1);
gd(t, k->e);
if (cu(t, k->qp)) {
hn(k->e, "10001");
cp(t, pq1);
gd(t, k->e);
if (cu(t, k->qp))
return 0;
}
cp(k->d, k->e);
iv(k->d, f);
cp(t, k->d);
dm(t, p1, k->dp);
cp(t, k->d);
dm(t, q1, k->dq);
cp(k->qp, k->q);
iv(k->qp, k->p);
cp(t, k->pq);
for(k->b = 0; ts(t); sr(t), k->b++)
; /* VOID */
return (k->b);
}
/*
* rsa_dec(N m, rsa_key *key) -- low level rsa decryption. Result undefined
* (ie. wrong) if key is not private rsa key.
*/
void
rsa_dec(N m, rsa_key * k)
{
NN mp, mq, t;
cp(t, m);
dm(t, k->p, mp);
cp(t, m);
dm(t, k->q,
mq);
em(mp, k->dp, k->p);
em(mq, k->dq, k->q);
if (sb(mp, mq))
ad(mp, k->p);
mm(mp, k->qp,
k->p);
mu(mp, k->q);
ad(mp, mq);
cp(m, mp);
}
/*
* rsa_enc(N m, rsa_key *k) -- low level rsa encryption
*/
void
rsa_enc(N m, rsa_key * k)
{
em(m, k->e, k->pq);
}
/*
* len = n_to_b(unsigned char *buf, N a) -- convert a to bytes, most
* significant byte first. Returns number of bytes written to buf. buf
* should be large enough to hold sizeof(NN) bytes. (Note that number
* is handled as unsigned, negative value converts to sizeof(NN) bytes.)
* (XXX check portablility when converting to not-16/32 bit machine)
*/
ULONG
n_to_b(unsigned char *b, N a)
{
ULONG i = NSIZE - 1, l = 1;
a += NSIZE;
while (!*--a && i)
i--;
if (*a > 255) {
*b++ = *a >> 8;
l++;
}
*b++ = *a;
while (i--) {
*b++ = *--a >> 8;
*b++ = *a;
l += 2;
}
return (l);
}
/*
* b_to_n(N a, unsigned char *buf,ULONG len) -- convert len bytes from
* buf to value a. Conversion is unsigned, most significant byte first.
* (XXX check portablility when converting to not-16/32 bit machine)
*/
void
b_to_n(N a, unsigned char *b, ULONG l)
{
ULONG i;
if (l > NSIZE * sizeof(UWORD))
l = NSIZE * sizeof(UWORD);
b += l;
cl(a);
i = l / 2;
while (i--) {
*a = *--b;
*a++ |= (ULONG) *--b << 8;
}
if (l & 1)
*a = *--b;
}
/*
* mrsa.h -- Multiprecision math and RSA public key crypt library
* 1993 Risto Paasivirta, paasivir@jyu.fi
* Public Domain, no warranty. Use as you wish.
*/
#ifndef MRSA_H
#define MRSA_H 1
#ifndef NSIZE
/* #define NSIZE 32 for max 512 (actually 511) bit modulus */
#define NSIZE 16
#endif
/*
* unsigned 16 and 32 -bit types (other sizes may need some porting)
*/
#ifndef UWORD
typedef unsigned short UWORD;
#endif
#ifndef ULONG
typedef unsigned long ULONG;
#endif
typedef UWORD *N, NN[NSIZE];
typedef struct rsa_key {
ULONG b;
NN pq,e,d,p,q,dp,dq,qp;
} rsa_key;
#if !defined(RSA_ONLY) || defined(MRSA_C)
#define UNIT_BITS 16 /* unit bits */
#define SIGN_BIT (1<<15) /* top bit of unit */
#define PRIMES 54 /* number of primes in prime table */
#ifdef RSA_ONLY /* define RSA_ONLY if math stuff not needed */
#define PRIVATE static
#else
#define PRIVATE
#endif
int ts(N a); /* test signed, returns -1, 0 or 1 */
ULONG ng(N a); /* negate, return carry*/
void cl(N a); /* clear */
void cp(N a,N b); /* copy, a = b */
int cu(N a,N b); /* compare unsigned, returns, -1 0 or 1 */
ULONG ad(N a,N b); /* add, a += b */
ULONG sb(N a,N b); /* substract, a -= b */
ULONG sr(N a); /* shift right, a >>= 1, return carry */
ULONG sl(N a); /* shift left, a <<= 1, return carry */
void dm(N a,N b,N c); /* div-mod unsigned, a /= b, c = a % b */
void mu(N a,N b); /* multiply unsigned, a *= b */
void mm(N a,N b,N m); /* modular multiply, a = a * b mod m */
void em(N a,N e,N m); /* modular exponentiation, a = a^e mod m */
void gd(N a,N b); /* greatst common divisor, a = ***(a,b) */
void iv(N a,N b); /* multiplicative inverse, a = a^{-1} mod p */
void nh(char *a,N b); /* convert number to hex string */
void hn(N a,char *b); /* convert lowercase hex string to number */
ULONG ri(); /* weak pseudorandom integer */
#if defined(AMIGA) && defined(MRSA_C)
__stdargs pmm(N aa, N b, N m, ULONG p); /* assembler modmul (SAS 6.2) */
#endif
#endif /* RSA_C */
void randomize(N a, ULONG bits);
ULONG sieve_prime(N);
int prob_prime(N);
void next_prime(N);
ULONG rsa_gen(rsa_key *);
void rsa_enc(N,rsa_key *);
void rsa_dec(N,rsa_key *);
ULONG n_to_b(unsigned char *,N);
void b_to_n(N,unsigned char *,ULONG);
#endif /* MRSA_H */
|
|
|
|
|
|
求助,如何创建一个连续的文件
是的。 這樣理解是沒錯。 不過,當 diskette 為 一個 empty storage 時,可以達成 logical mapping physical 為完美的连续情況,這樣的理論可以實現。 估且不考慮 motor 的 speed rate 為何,對於 read / write 時,真正要注意的是在 INT 25h/INT 26h 的控制。為了要達到 "连续性",performance 多少會被拉下來地。 |
|
|
|
|
|
如何判断一个exe程序是用什么语言写的啊?谢谢
O 大在 6 樓,及 N 大在 8 樓都有提到, "特徵",除了透過 一些 tools 之外,還需要 "經驗"。 大家講的方法都是解決樓主的答案之一。 透過 unassembly 或是 disassembly 來判斷及分析原來是用哪一個 compiler 去 compiled 成 exe 的方法,是眾多方法中最佳的方案,這點無庸致疑地。 對於 common user 來說,B 大及t 大的方法簡單而直接。 |
|
|
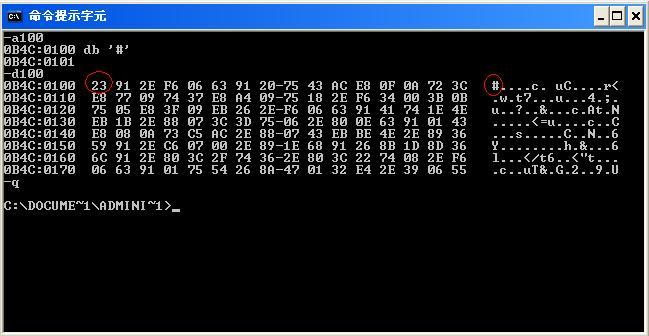
#对应的16进制数是多少
樓主賺到了,花 10k 可以獲得很多方法,學習了。 |
|
|
如何判断一个exe程序是用什么语言写的啊?谢谢
[QUOTE=blueapplez;752710]膜拜R大,看明白是什么意思了, 但是我有一个问题 这个“残余”的信息,是否会在网络传输过程中完全的丢失掉呢? 我认为是的,期待不同的答案![/QUOTE] 是的。 B 大見解正確。 其實,一個 file ,當它被 copy 的次數越多,这个“残余”的信息,lose rate 也就越高。 有時, hacker/cracker 就是從这个“残余”的信息來判斷 Owner (user)的電腦裡有什麼 "東西"。 不繼續探討下去的主因.....是....會模糊了原樓主的原本的問題。 |
|
|
[推荐]Safengine 市场信心之作 , 10万求破解 ,牛人们快试试啊
果然同名同姓的人不少,所以驗證碰撞理論。 |
|
|
求助,如何创建一个连续的文件
有,二、三十年前,有一種硬件叫做“tape”,這種 storage 可以滿足 lxcsyh 的要求。 若在 foramt 當下不寫入任何 data, diskette 當然是一个物理连续的 space. 還有第三種情況,若 data zise < 物理上连续的 space size,那也可以滿足 lxcsyh 的要求。 為什麼 lxcsyh 的問題這樣困難? 其實很容易理解,因為現在的 files access 都是採用 “ random access file ”模式。 |
|
|
[分享][IEEE WCNIS2010] Special issue on network coding---deadline Jan. 1st.
Dear Friend, the submission deadline to IEEE 2010 international conference on Wireless Communications, Networking and Information Security has been extended to Feb 10th, 2010. Please submit by checking the website www.ieee-wcnis.org |
|
|
[推荐]Safengine 市场信心之作 , 10万求破解 ,牛人们快试试啊
10年前有人說 ECC 將有取代 RSA 的區趨勢,成為主流。 自 1999 - 2009 年來看,似乎真的是這樣。 可是現在也有人在懷疑 ECC 是不是真的夠安全!? 如果我有像 Lenstra 教授那樣的 Super Computer,我相信用劉尊全教授的方法來計算 RSA 2048 將如吃飯一樣不難。 (以上假設為純數學計算,無關軟件安全漏洞與破解) S 大不入地獄誰入地獄。~ 阿門~ |
|
|
|
|
|
[推荐]Safengine 市场信心之作 , 10万求破解 ,牛人们快试试啊
聽說這樣的內容已經在友台吵翻天了。 果然只有左派跟右派兩邊。 在台灣,小S 跟大S 可是沒人敢圍攻的,可憐的 S 大。 我為您默哀三分鐘。 |
|
|
如何判断一个exe程序是用什么语言写的啊?谢谢
File System ( FS , 檔案系統) : 就是 Linux, OS/2 及 MS DOS/ Windows XP 所需要用到的檔案格式。 譬如, FAT 16, FAT 32, NTFS 等,就是 File System. Sector (磁區): 一個磁軌 ( track) 包函若干個磁區( sector). EOF (End of File): 指檔案的結尾,一個檔案(file)不一定是連續儲存在一起,何時表示檔案是最後一個 byte時,就要借助 eof 這個 symbol 來辨認,當然這也要與 partition table 及 root directories 搭配比較精確。 sorry~~我這個內容~~是20幾年前的舊東西,請見諒。 |
|
|
[求助]求组密码学概论可替换的教材
http://d.download.csdn.net/down/167963/liuyanzan  http://bbs.bovii.com/thread-73002-1-1.html 
|
|
|
[求助]求组密码学概论可替换的教材
密码编码学与网络安全-- 原理与实践(第三版).pdf 請將究點。 http://www.verycd.com/files/b5b143b2f2b5d69397b99618d3dd254482877173 
|
|
|
|
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值