-
-
[原创]Android一二三代壳实现
-
发表于:
2026-5-11 22:01
17147
-
落地壳 会将文件保存到本地
不落地壳,使用InMemoryDexClassLoader加载内存中dex,无需保存到本地
本壳参考了开源项目dpt-shell,对开源项目的分析可以参考我的其他文章
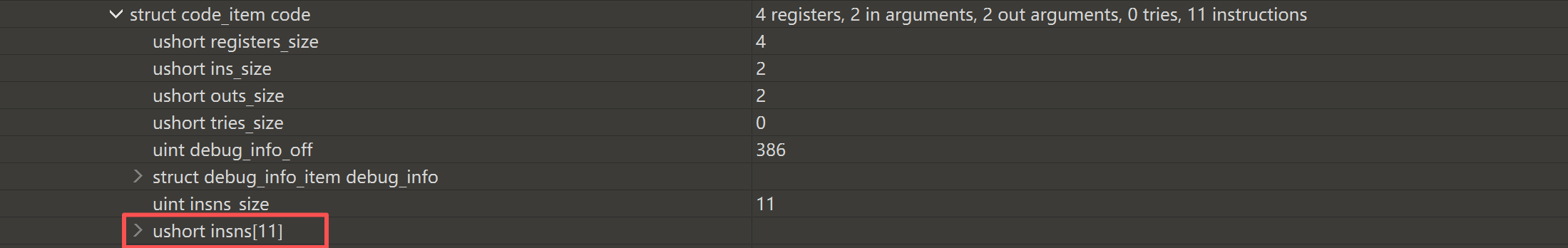
抽取指令就是将method->code_item->insns数组中的指令全部替换为0x00,这样反编译出的方法就为空
将抽取出的指令保存,准备运行时回填
这里我将抽出的指令保存到assets文件夹下,文件格式为:
dex数量(2字节)+ 每个dex偏移(4字节)+ 每个dex的指令结构
每个dex指令结构为:
该dex的方法数(2字节)+ codeItem
codeItem结构由每个函数的指令块组成:
方法id(4字节)+ insn大小(4字节)+ insns(insn大小)
结合代码中的结构体,让ai写了抽空dex和保存该文件结构的代码
原始activity如下
创建一个新的项目,包名为com.example.mysourceapp,MainActivity只写一个log语句,表明正确执行到此处
现在新建我们的壳项目
ProxyApplication.java
代理类没什么主要逻辑,主要逻辑放在native层中
native-lib.cpp
在代码中使用了一些工具类和函数
DexCode.cpp
这里需要和结合刚刚自定义的文件结构理解,代码比较简单
保存code指令以后,什么时候回填呢,为了实现运行时回填的效果,需要hook defineClass函数
传播安全知识、拓宽行业人脉——看雪讲师团队等你加入!
最后于 2026-5-17 15:56
被mb_wckjnnha编辑
,原因: