-
-
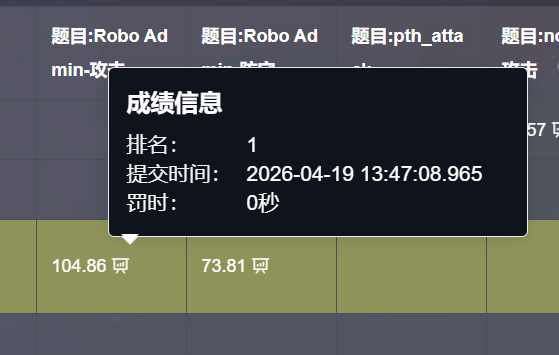
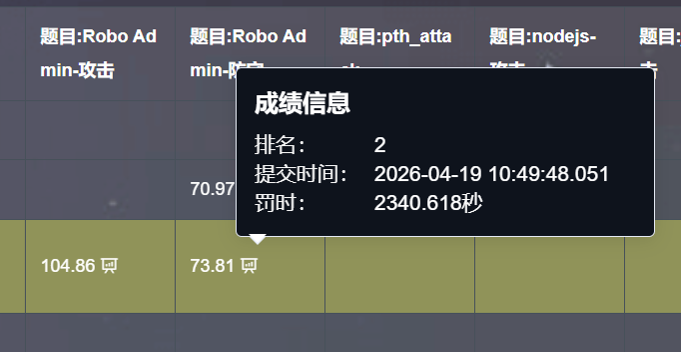
[原创]2026 软件系统安全赛Robo Admin题解
-
发表于:
2026-4-20 22:53
4605
-
[原创]2026 软件系统安全赛Robo Admin题解
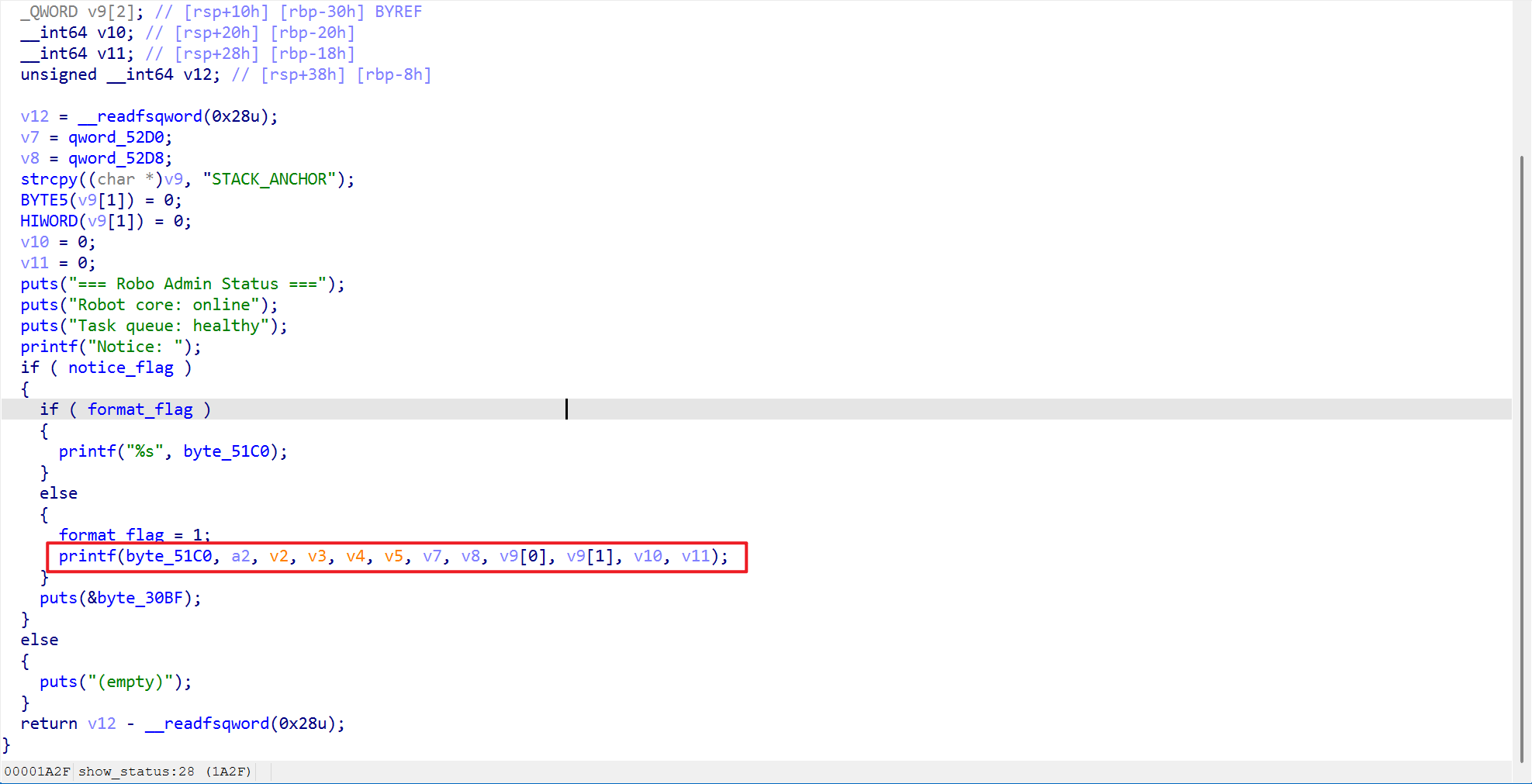
这个位置存在格式化字符串漏洞,同时按照要求增加解码后的判断逻辑即可
没做出来的师傅们可能没有好好读题,题目里面指定了需要审计set_notice函数和show_status函数,所以会有以下三种情况
因此我们需要在修复格式化字符串的同时,利用汇编添加第二条的逻辑,至于第二层菜单的off by one甚至都不用修复就可以通过check
通过格式化字符串泄露信息,同时泄露password经过login的认证,随后进入主菜单
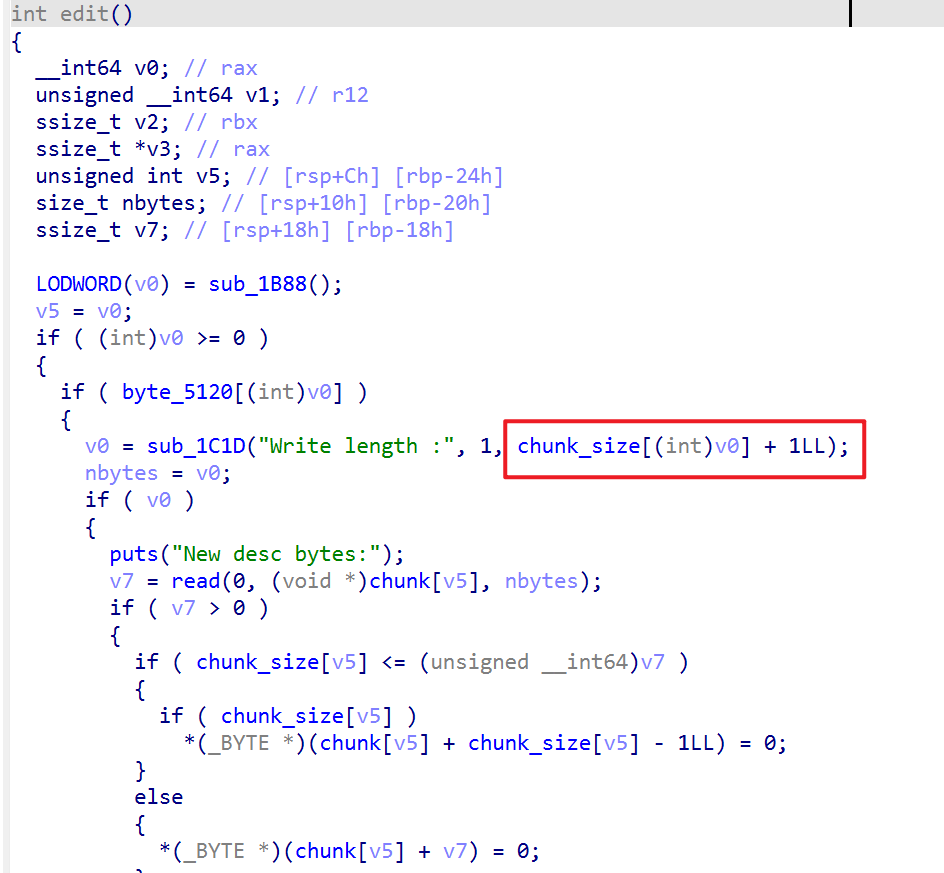
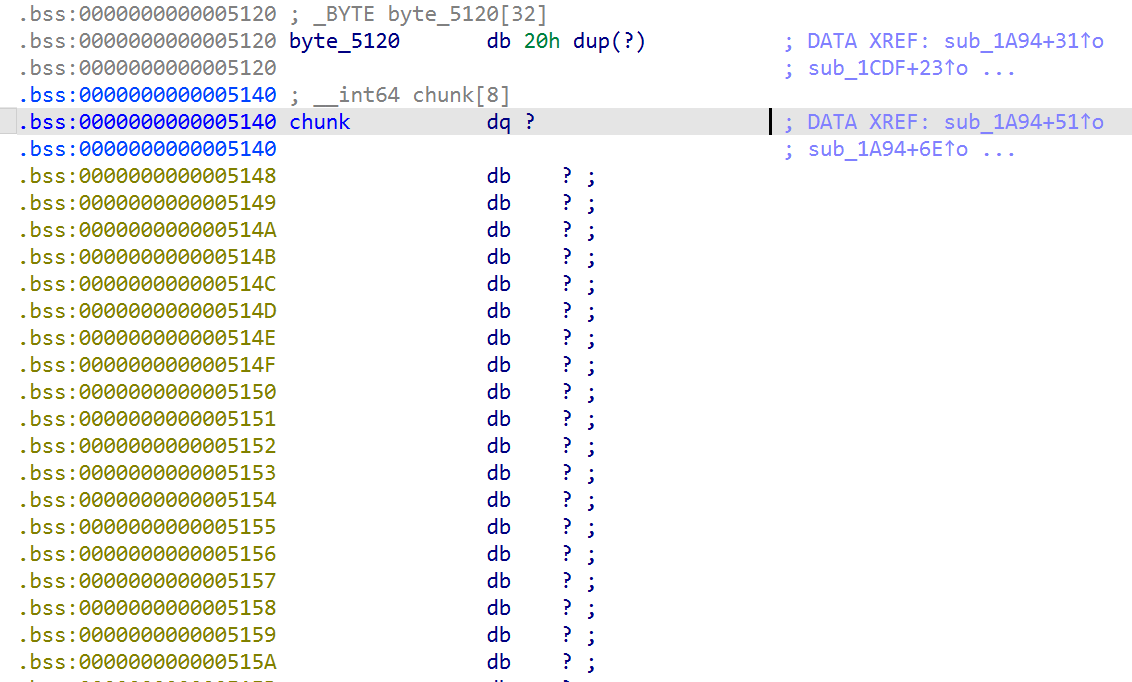
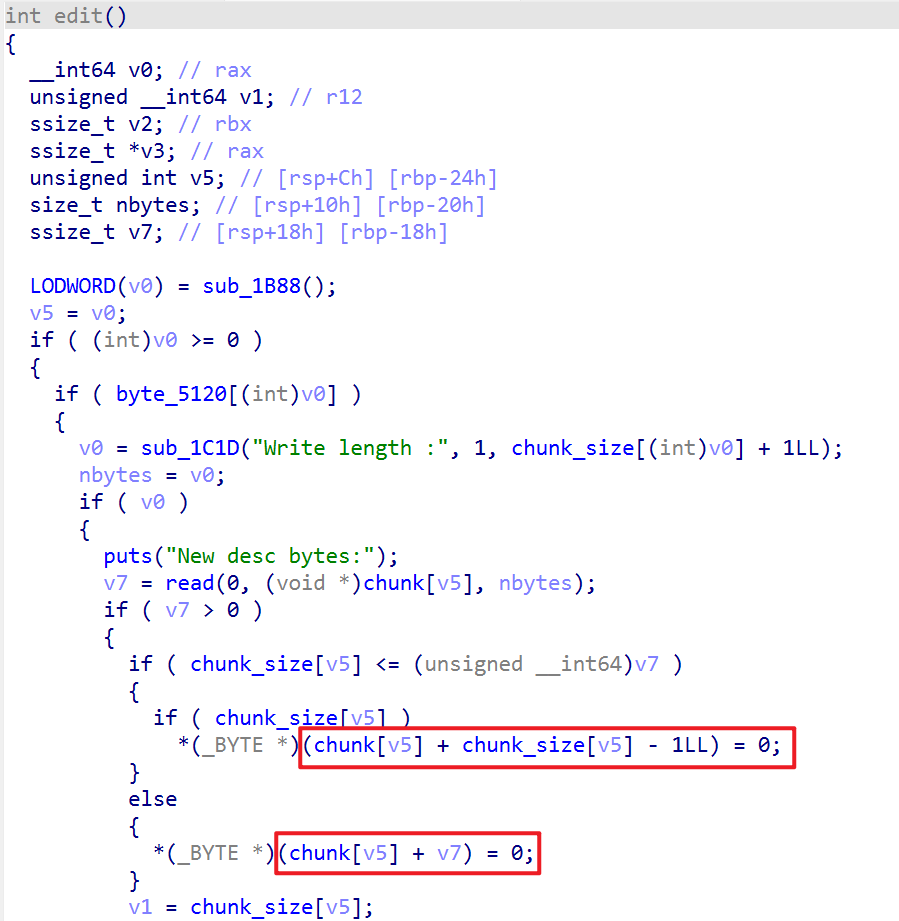
这个位置存在一个off by one,可以先通过这个off by one修改后一个堆块的size,随后通过后一个堆块覆盖之后的内存,实现堆重叠,随后打unlink就可以直接控制堆块管理内存的权限
随后可以泄露堆的地址,修改_IO_list_all,打house of apple2即可
其实在打unlink之前,一直在尝试通过堆重叠直接篡改fd,由于是glibc 2.35,因此存在异或加密,需要先泄露一个堆地址。由于编辑堆块的时候会在堆块的末尾添加空字符,而show功能利用的是printf,因此很难通过edit + show的方式泄露堆地址,尝试半天后最终选择unlink。我们通过之前的格式化字符串可以泄露出ELF基地址,同时存在溢出写,满足打unlink的条件
[培训]《冰与火的战歌:Windows内核攻防实战》!从零到实战,融合AI与Windows内核攻防全技术栈,打造具备自动化能力的内核开发高手。