|
|
|
|
|
[已解决]一个算法的汇编写法?
.386 .model flat,stdcall option casemap:none include windows.inc include kernel32.inc include user32.inc includelib kernel32.lib includelib user32.lib .data bTable db 97, 214, 212, 233, 221, 240, 251, 242, 91, 100, 53, 173, 183, 200, 25, 117, 236, 49, 43, 188 szOutBuffer db 256 dup(0) szTestScr db 'dbcdefghijklmnopqrstuvwxyz',0 .code GetPass proc uses esi edi ebx lpScr,lpOutBuffer mov edi,lpScr mov edx,lpOutBuffer xor eax,eax test edx,edx jnz @f ret @@: test edi,edi jnz @f ret @@: lea ebx,bTable mov ecx,sizeof bTable/2 xor esi,esi @@: movzx eax,BYTE ptr [edi+esi*2] ; 这里修改一下就行了 xor al,BYTE ptr [ebx+esi*2] mov BYTE ptr [edx+esi],al inc esi dec ecx jnz @b mov eax,edx ret GetPass endp start: invoke GetPass,offset szTestScr,offset szOutBuffer invoke MessageBox,0,offset szOutBuffer,NULL,MB_OK invoke ExitProcess,NULL ret end start |
|
|
[已解决]一个算法的汇编写法?
是的,如4楼所说,把你的字符编码首地址传过去就行。在汇编操作可视的字符和非可视的字符的ASCII码值没什么两样。都只是一个Byte类型的数值。 |
|
|
[已解决]一个算法的汇编写法?
.386 .model flat,stdcall option casemap:none include windows.inc include kernel32.inc include user32.inc includelib kernel32.lib includelib user32.lib .data bTable db 97, 214, 212, 233, 221, 240, 251, 242, 91, 100, 53, 173, 183, 200, 25, 117, 236, 49, 43, 188 szOutBuffer db 256 dup(0) szTestScr db 'dbcdefghijklmnopqrstuvwxyz',0 .code GetPass proc uses esi edi ebx lpScr,lpOutBuffer mov edi,lpScr mov edx,lpOutBuffer xor eax,eax test edx,edx jnz @f ret @@: test edi,edi jnz @f ret @@: lea ebx,bTable mov ecx,sizeof bTable/2 xor esi,esi @@: movzx eax,BYTE ptr [edi+esi] xor al,BYTE ptr [ebx+esi*2] mov BYTE ptr [edx+esi],al inc esi dec ecx jnz @b mov eax,edx ret GetPass endp start: invoke GetPass,offset szTestScr,offset szOutBuffer invoke MessageBox,0,offset szOutBuffer,NULL,MB_OK invoke ExitProcess,NULL ret end start |
|
|
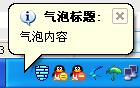
[已解决]汇编中托盘气球提示框的问题
我的也是2003的。 |
|
|
|
|
|
[求助]请帮忙看下代码那些地方错了- - !
; 有颜色部分的是要修改的 .386 .model flat,stdcall option casemap:none ;............................ include windows.inc include user32.inc includelib user32.lib include kernel32.inc includelib kernel32.lib ;............................ ICO_BIG equ 1000h ICO_SMALL equ 1100h IDM_MAIN equ 2000h IDA_MAIN equ 2000h IDM_EXIT equ 4001h IDM_XXZL equ 4004h IDM_CUR1 equ 4005h IDM_CUR2 equ 4006h IDM_BIG equ 4007h IDM_SMALL equ 4008h ;......................... .data? hInstance dd ? hWinMain dd ? hMenu dd ? hSubMenu dd ? hBIG dd ? HSMALL dd ? hcur1 dd ? hcur2 dd ? .const szClassName db 'myclass',0 szCaptionMain db '我的程序~- - !',0 szcursorfile1 db '1.ani',0 szcursorfile2 db '2.ani',0 ;...................................... .code ;.................................. _Quit proc invoke DestroyWindow,hWinMain invoke PostQuitMessage,NULL ret _Quit endp ;................................. _ProcWinMain proc uses ebx edi esi hWnd,uMsg,wParam,lParam mov eax,uMsg .if eax == WM_CREATE invoke LoadCursorFromFile,addr szcursorfile1 mov hcur1,eax invoke LoadCursorFromFile,addr szcursorfile2 mov hcur2,eax invoke SendMessage,hWnd,WM_SETICON,ICON_BIG,hBIG invoke SetClassLong,hWnd,GCL_HCURSOR,hcur1 ;......................................... .elseif eax == WM_COMMAND mov eax,wParam movzx eax,ax .if eax == IDM_EXIT call _Quit .elseif eax == IDM_BIG invoke SendMessage,hWnd,WM_SETICON,ICON_BIG,hBIG invoke CheckMenuRadioItem,hMenu,IDM_BIG,IDM_SMALL,IDM_BIG,MF_BYCOMMAND .elseif eax == IDM_SMALL invoke SendMessage,hWnd,WM_SETICON,ICON_BIG,HSMALL invoke CheckMenuRadioItem,hMenu,IDM_BIG,IDM_SMALL,IDM_SMALL,MF_BYCOMMAND .elseif eax == IDM_CUR1 invoke SetClassLong,hWnd,GCL_HCURSOR,hcur1 invoke CheckMenuRadioItem,hMenu,IDM_CUR1,IDM_CUR2,IDM_CUR1,MF_BYCOMMAND .elseif eax == IDM_CUR2 invoke SetClassLong,hWnd,GCL_HCURSOR,hcur2 invoke CheckMenuRadioItem,hMenu,IDM_CUR1,IDM_CUR2,IDM_CUR2,MF_BYCOMMAND .endif .elseif eax == WM_CLOSE call _Quit .else invoke DefWindowProc,hWnd,uMsg,wParam,lParam ret .endif xor eax,eax ret _ProcWinMain endp ; 你这里缺少一个_ProcWinMain endp ;................................... _WinMain proc local @stWndClass:WNDCLASSEX local @stMsg:MSG local @haccelerator invoke GetModuleHandle,NULL mov hInstance,eax invoke LoadMenu,hInstance,IDM_MAIN mov hMenu,eax invoke LoadAccelerators,hInstance,IDA_MAIN mov @haccelerator,eax ;.............................. invoke RtlZeroMemory,addr @stWndClass,sizeof @stWndClass invoke LoadIcon,hInstance,ICO_BIG mov hBIG,eax mov @stWndClass.hIcon,eax invoke LoadIcon,hInstance,ICO_SMALL mov HSMALL,eax mov @stWndClass.hIconSm,eax push hInstance pop @stWndClass.hInstance mov @stWndClass.cdSize,sizeof WNDCLASSEX ; 应该是cbSize mov @stWndClass.style,CS_HREDRAW or CS_VREDRAW mov @stWndClass.lpfnWndproc,offset _ProcWinMain ; 这里应该是lpfnWndProc(注意大小写) mov @stWndClass.lpszClassName,offset szClassName mov @stWndClass.hbrBackground,COLOR_BTNFACE + 1 ; 在这里替你添加了一下背景颜色 invoke RegisterClassEx,addr @stWndClass ;.................................. invoke CreateWindowEx,WS_EX_CLIENTEDGE,offset szClassName,offset szCaptionMain,WS_OVERLAPPEDWINDOW,\ 100,100,400,300,NULL,hMenu,hInstance,NULL mov hWinMain,eax invoke ShowWindow,hWinMain,SW_SHOWNORMAL invoke UpdateWindow,hWinMain ;................................. .while TRUE invoke GetMessage,addr @stMsg,NULL,0,0 .break .if eax == 0 invoke TranslateAccelerator,hWinMain,@haccelerator,addr @stMsg .if eax == 0 invoke TranslateMessage,addr @stMsg invoke DispatchMessage,addr @stMsg .endif .endw ret _winMain endp ; 这里应该是_WinMain(注意大小写) ;................................. start: call _WinMain invoke ExitProcess,NULL ;......................... end start |
|
|
[求助]帮我看个新手的C程序就几行代码
#include <stdio.h> // "stdio.h"改<stdio.h> int max(int x,int,y); // 要调用向后引用的函数时必须在前面声明一下。 main() { int a,b,c; scanf("%d,%d",&a,&b); c=max(a,b); printf("max=%d",c); } int max(int x,int,y) { int z; if(x>y) z=x; else z=y; return(z); } |
|
|
[求助]用vb如何取得某个dll的基地址?
hDllInst = GetModuleHandle(lpDllName); |
|
|
[求助]关于DEVICE_EXTENSION的定义?
看你所述,KTIMER和KDPC应该都是一个结构体变量,而不是一个结构体指针变量,所以你将结构体变量定义成结构体指针变量肯定是不行的。 |
|
|
[求助]怎么获得当前活动窗口的句柄
GetForegroundWindow |
|
|
[求助]请介绍几个专门讨论C + Win32API编程的网站,谢了先
请achillis兄弟注意一下用词语气,不要在论坛上挑起争执,谢谢合作。 |
|
|
[求助]请教 有什么工具 可以 将 二进制 代码 转为 汇编 代码
1、用记事本将你上面的数据"0x"和"\"替换删除后复制你上面的数据。 2、用OllyDBG随便打开一个程序。 3、在程序中随便找一个空白的位置选择一个和你上面的二进制数一样大小的选块。 4、将你上面的二进制数据粘贴进那个空白的位置。 5、在OllyDBG反汇编窗口中定位到那个空白地址上就可以看到反汇编后的代码了。 如下面是你上面数据用OD反汇编后的代码 00402000 /EB 10 jmp short 00402012 00402002 |5A pop edx 00402003 |4A dec edx 00402004 |33C9 xor ecx, ecx 00402006 |66:B9 3C01 mov cx, 13C 0040200A |80340A 99 xor byte ptr [edx+ecx], 99 0040200E ^|E2 FA loopd short 0040200A 00402010 |EB 05 jmp short 00402017 00402012 \E8 EBFFFFFF call 00402002 00402017 70 4C jo short 00402065 00402019 99 cdq 0040201A 99 cdq 0040201B 99 cdq 0040201C C3 retn 0040201D FD std 0040201E 38A9 99999912 cmp byte ptr [ecx+12999999], ch 00402024 D995 12E98534 fst dword ptr [ebp+3485E912] 0040202A 12D9 adc bl, cl 0040202C 91 xchg eax, ecx 0040202D 1241 12 adc al, byte ptr [ecx+12] 00402030 EA A512ED87 E19A jmp far 9AE1:87ED12A5 00402037 6A 12 push 12 00402039 E7 B9 out 0B9, eax 0040203B 9A 6212D78D AA74 call far 74AA:8DD71262 00402042 CF iretd 00402043 CE into 00402044 C8 12A69A enter 0A612, 9A 00402048 6212 bound edx, qword ptr [edx] 0040204A 6BF3 97 imul esi, ebx, -69 0040204D C06A 3F ED shr byte ptr [edx+3F], 0ED 00402051 91 xchg eax, ecx 00402052 C0C6 1A rol dh, 1A 00402055 5E pop esi 00402056 9D popfd 00402057 DC7B 70 fdivr qword ptr [ebx+70] 0040205A C0C6 C7 rol dh, 0C7 0040205D 125412 DF adc dl, byte ptr [edx+edx-21] 00402061 BD 9A5A4878 mov ebp, 78485A9A 00402066 9A 58AA50FF 1291 call far 9112:FF50AA58 0040206D 12DF adc bl, bh 0040206F 859A 5A58789B test dword ptr [edx+9B78585A], ebx 00402075 9A 5812999A 5A12 call far 125A:9A991258 0040207C 6312 arpl word ptr [edx], dx 0040207E 6E outs dx, byte ptr es:[edi] 0040207F 1A5F 97 sbb bl, byte ptr [edi-69] 00402082 1249 F3 adc cl, byte ptr [ecx-D] 00402085 9D popfd 00402086 C071 C9 99 sal byte ptr [ecx-37], 99 0040208A 99 cdq 0040208B 99 cdq 0040208C 1A5F 94 sbb bl, byte ptr [edi-6C] 0040208F CB retf 00402090 CF iretd 00402091 66:CE into 00402093 65:C3 retn 00402095 1241 F3 adc al, byte ptr [ecx-D] 00402098 98 cwde 00402099 C071 A4 99 sal byte ptr [ecx-5C], 99 0040209D 99 cdq 0040209E 99 cdq 0040209F 1A5F 8A sbb bl, byte ptr [edi-76] 004020A2 CF iretd 004020A3 DF19 fistp word ptr [ecx] 004020A5 A7 cmps dword ptr [esi], dword ptr es:[e> 004020A6 19EC sbb esp, ebp 004020A8 6319 arpl word ptr [ecx], bx 004020AA AF scas dword ptr es:[edi] 004020AB 19C7 sbb edi, eax 004020AD 1A75 B9 sbb dh, byte ptr [ebp-47] 004020B0 1245 F3 adc al, byte ptr [ebp-D] 004020B3 B9 CA66CE75 mov ecx, 75CE66CA 004020B8 5E pop esi 004020B9 9D popfd 004020BA 9A C5F8B7FC 5EDD call far DD5E:FCB7F8C5 004020C1 9A 9DE1FC99 99AA call far AA99:99FCE19D 004020C8 59 pop ecx 004020C9 C9 leave 004020CA C9 leave 004020CB CA CFC9 retf 0C9CF 004020CE 66:CE into 004020D0 65:1245 C9 adc al, byte ptr gs:[ebp-37] 004020D4 CA 66CE retf 0CE66 004020D7 69C9 66CE6DAA imul ecx, ecx, AA6DCE66 004020DD 59 pop ecx 004020DE 35 1C59EC60 xor eax, 60EC591C 004020E3 C8 CBCFCA enter 0CFCB, 0CA 004020E7 66:4B dec bx 004020E9 C3 retn 004020EA C032 7B sal byte ptr [edx], 7B 004020ED ^ 77 AA ja short 00402099 004020EF 59 pop ecx 004020F0 5A pop edx 004020F1 ^ 71 BF jno short 004020B2 004020F3 66: prefix datasize: 004020F4 66: prefix datasize: 004020F5 66:DEFC fdivp st(4), st 004020F8 ED in eax, dx 004020F9 C9 leave 004020FA ^ EB F6 jmp short 004020F2 004020FC FA cli 004020FD D8FD fdivr st, st(5) 004020FF FD std 00402100 ^ EB FC jmp short 004020FE 00402102 EA EA99DEFC EDCA jmp far CAED:FCDE99EA 00402109 ^ E0 EA loopdne short 004020F5 0040210B ED in eax, dx 0040210C FC cld 0040210D F4 hlt 0040210E DDF0 fsave eax ; 非法使用寄存器 00402110 ^ EB FC jmp short 0040210E 00402112 FA cli 00402113 ED in eax, dx 00402114 F6EB imul bl 00402116 ^ E0 D8 loopdne short 004020F0 00402118 99 cdq 00402119 CE into 0040211A F0:F7DC lock neg esp ; 不允许锁定前缀 0040211D ^ E1 FC loopde short 0040211B 0040211F FA cli 00402120 99 cdq 00402121 DCE1 fsubr st(1), st 00402123 F0:ED lock in eax, dx ; 不允许锁定前缀 00402125 CD F1 int 0F1 00402127 ^ EB FC jmp short 00402125 00402129 F8 clc 0040212A FD std 0040212B 99 cdq 0040212C D5 F6 aad 0F6 0040212E F8 clc 0040212F FD std 00402130 D5 F0 aad 0F0 00402132 FB sti 00402133 ^ EB F8 jmp short 0040212D 00402135 ^ EB E0 jmp short 00402117 00402137 D899 ECEBF5F4 fcomp dword ptr [ecx+F4F5EBEC] 0040213D F6F7 div bh 0040213F 99 cdq 00402140 CC int3 00402141 CB retf 00402142 D5 DD aad 0DD 00402144 F6EE imul dh 00402146 F7F5 div ebp 00402148 F6F8 idiv al 0040214A FD std 0040214B CD F6 int 0F6 0040214D DFF0 fcomip st, st 0040214F F5 cmc 00402150 FC cld 00402151 D899 00000000 fcomp dword ptr [ecx] |
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值