|
|
[求助]Android apk中lib/.so檔分析
SO不一定都会有符号的,可以去掉,而且节是给链接器用的,可以测底抹掉,段才是给加载器用的。所以没办法修回去的。 |
|
|
VC有对输入表的编译设定吗?
可以的,你自己改个lib,丢上去,就能做到。 |
|
|
[下载]detours_Version 3.0 Build_306 x86 x64 ia64 arm 完整版
这个太给力了,一致觉得微软这个hook还不错。 |
|
|
[求助]Android apk中lib/.so檔分析
自己给elf写个模板,就可以
template "ELF file format"
description "ELF file format"
applies_to file
fixed_start 0
requires 0x00 "7F 45 4C 46"
begin
section "ELF Header"
read-only char[16] "e_ident"
read-only hexadecimal uint16 "e_type"
read-only hexadecimal uint16 "e_machine"
read-only hexadecimal uint32 "e_version"
read-only hexadecimal uint32 "e_entry"
read-only hexadecimal uint32 "e_phoff"
hexadecimal uint32 "e_shoff"
read-only hexadecimal uint32 "e_flags"
read-only hexadecimal uint16 "e_ehsize"
read-only hexadecimal uint16 "e_phentsize"
read-only hexadecimal uint16 "e_phnum"
read-only hexadecimal uint16 "e_shentsize"
uint16 "e_shnum"
uint16 "e_shstrndx"
goto "e_phoff"
{
section "Program header #~"
hexadecimal uint32 "p_type"
hexadecimal uint32 "p_offset"
hexadecimal uint32 "p_vaddr"
hexadecimal uint32 "p_paddr"
hexadecimal uint32 "p_filesz"
hexadecimal uint32 "p_memsz"
hexadecimal uint32 "p_flags"
hexadecimal uint32 "p_align"
}[e_phnum]
end
|
|
|
[求助]Android apk中lib/.so檔分析
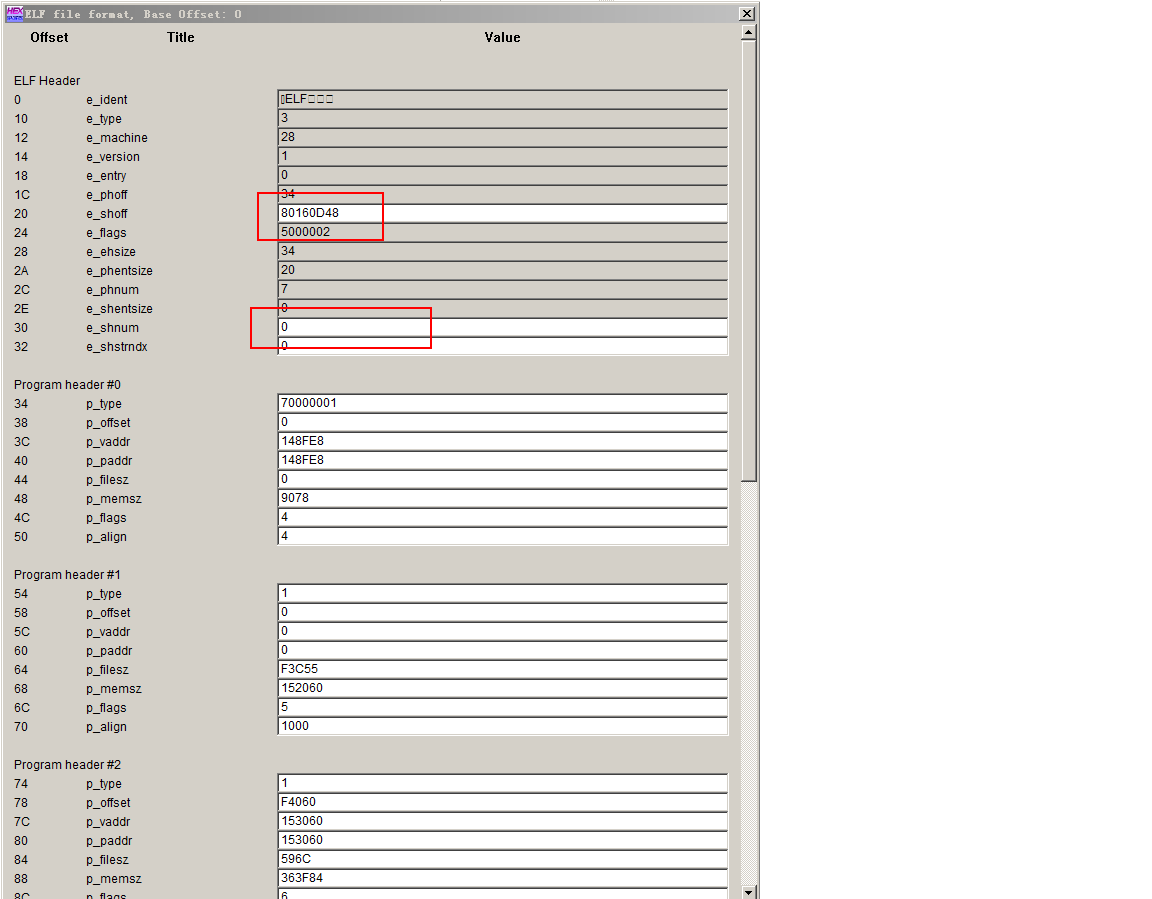 主要是标红的字段是错的。你可以把第一个填成0. 如果要修复的话,你得找到原始的位置(ps:比较难,如果他没抹掉的话)。如果要IDA不提示,你直接把第一个改成0. |
|
|
Xuetr的MBR检测和MBR重置
去PE下面,恢复就好了。。 |
|
|
[原创]基于winpcap的NDIS在IE浏览器,360安全浏览器hack"www.360.cn"
囧,看完代码,感觉你的代码,没办法拦截数据包,貌似只是捕获数据包。 |
|
|
[求助]获取调用API的进程
栈回溯,找返回地址。 |
|
|
[注意]测试你的肺活量,按住键盘0,憋气,看你能有多少行,男人不做假!
0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 |
|
|
[求助]HOOK SSDT,执行MmBuildMdlNonePagePool就蓝屏
你都说了是CPP,你改成.C文件 |
|
|
[新手]如何知道inject程序修改了宿主程序的哪些地址的内容
XT可以扫描到修改的地方。 |
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值


