|
|
[分享]公钥密码芯片整体框架图
http://www.doc88.com/p-01493734882.html 密钥分散算法简称Diversify,是指将一个双长度的密钥MK,对分散数据进行处理,推导出一个双长度的密钥DK。 推到DK左半部分的方法是: 1、将分散数据的最右8个字节作为输入数据; 2、将MK作为加密密钥; 3、用MK对输入数据进行3DES运算; 推到DK右半部分的方法是: 1、将分散数据的最右8个字节求反,作为输入数据; 2、将MK作为加密密钥; 3、用MK对输入数据进行3DES运算; 在密钥管理方面,智能卡根据注入其中的客户端ID号,利用Diversify密钥分散算法生成客户端主密钥。在与密码服务器进行通信时,服务器取得其ID号,同样利用密钥分散算法生成客户端主密钥,再利用客户端主密钥加密附带工作密钥的签到回应报文传回客户端,客户端的智能卡解密得到工作密钥,利用工作密钥调用相应算法完成加解密及消息完整性验证 http://download.csdn.net/detail/sonahri/3858113 http://www.atsec.com/us/cryptographic-algorithm-validation-certificates.html 密码算法测评 atsec所提供的服务 atsec在NIST密码算法验证体系(Cryptographic Algorithm Validation Scheme)下提供如下算法测评 对称密钥加密算法: AES;Triple(三倍) DES;Skipjack 非对称密钥加密算法: DSA; RSA (ANSI X9.31, PKCS#1 v2.1); Elliptic Curve DSA (ANSI X9.62) 安全哈希算法标准 (SHA-1, SHA-224, SHA-256, SHA-384, SHA-512) 随机数发生器(RNG:Random Number Generator)算法: FIPS 186-2 附录 3.1 和 3.2 ;ANSI X9.31 附录 A.2.4 ,ANSI X9.62,附录 A.4 消息认证算法: CCM;HMAC-SHA1,-SHA256,-SHA384,-SHA512 - RC4 atsec实验室提供以下非FIPS认可的算法的测试: (未经过NIST验证的) RC4 CRC DES MAC Blowfish |
|
|
[求助]密钥容器安全 可以想像一个有向的数图-------序节点都可能有密钥容器,密钥容器设计的私钥加密要和全部节点密钥容器在产生,加密,传输,销毁等10几个环节不冲突,在加密私钥这一环节,就是随机数-----软件产生也好,硬件产生也好---都是随机数 硬件产生随机数有这样一个环节,商密局下有认证单位,认证单位在加密私钥----做IC卡,各种令牌,SIM卡。。。社保卡等智能卡,私钥加密肯定被弄这里面,智能卡就一小电脑了,因为认证单位要用商密局的硬件加密机,还有公私钥注入这些过程,硬件加密机就不是甚磨系统时钟产生随机数了,用混沌噪声之类的前沿技术 很多公务员电脑界面就两空格,NAME/PASSWORD 用智能卡/U盘开机,一个警员的加密私钥智能卡和一个警监加密私钥智能卡加密强度不一样,假定一个警监能从公安网库连金融网库看科级干部帐户,但不能看处长的,公安部长能看处长的,看不了部长的,都用的智能卡----指纹,声纹,虹膜,静脉。。。 警员用口令这都知道,不过最大公安网库就一个,警员用的就象一终端 私钥分加密文件和会话,会话私钥可能内存读出,据说新电脑在网上不能活过20分钟,木马/病毒别说,芯片那麽复杂,说不定有甚麽一通电主动发出内存芯片信息但有民用专业设备测不出的功能 介质访问控制也就换一新名词,但内容多了,再加上3网合一,国标列出很多项,但看现在天气颗粒国标,就知差距了 物理隔绝和人最难 看现实生活中,万能钥匙,干扰器,解码器到处都是,可还有老被偷的,楼主设计也是为了交差,给差主一个他不知道的开源软件就OK了 http://tv.video.sina.com.cn/play/117558.html http://video.sina.com.cn/v/b/64380646-2440170097.html 同态加密我只知道点: RSA: F1=x^e mod N F2=y^e mod N 存在同态:F1(x)*F2(y)==F(x*y), mod 基本性质 进而扩到R3--------Rn空间都没问题 两例: a:=688^79 mod 3337; a; b:=232^79 mod 3337; b; s:=a*b mod 3337; s; c:=688*232; c; d:=c ^79 mod 3337; d; s eq d; aa:=123456789^765 mod 1871111111111111; aa; bb:=987654321^765 mod 1871111111111111; bb; kk:=134583423333333333444444438899^765 mod 1871111111111111; kk; ss:=aa*bb*kk mod 1871111111111111; ss; cc:=(123456789*987654321*134583423333333333444444438899)^765 mod 1871111111111111; cc; ss eq cc; 1570 2756 2168 159616 2168 true 485561081123793 669161212878456 675491482966609 116188570804015 116188570804015 true : ELG-------DH F(x)=(G^k,x*H^k); F(y)=(G^t,y*H^t); 存在同态 F(x)*F(y)=(G^k,x*H^k)*(G^t,y*H^t)=(G^(k+t),(x*y)*H^(k+t))=F(x*y) 指数运算基本性质就能证 也能扩到Rn空间 p:=NextPrime (10^190); p; G1:=123; x:=7; k:=13; H1:=123^7 mod p; H1; FXL:=123^13 mod p; FXL; FXR:=(7*123^91) mod p; FXR; y:=5; t:=15; H2:=123^5; H2; FYL:=123^15 mod p; FYR:=5*123^75 mod p; M1:=(FXL*FYL) mod p; M1; M2:=(FXR*FYR) mod p; M2; FL:=123^(13+15)mod p; FL; FR:=(35*123^(7*13+5*15) )mod p; FR; M1 eq FL; M2 eq FR; 1000000000000000000000000000000000000000000000000000000000000000000000000000000\ 0000000000000000000000000000000000000000000000000000000000000000000000000000000\ 000000000000000000000000000000253 425927596977747 1474913153392179474539944683 6282847404652813906496253446785419040720653273406315409432010114217508488644385\ 1863620392072691277634998427489940552351189451093601211622471670847358193016763\ 39729443316038999820139141797459 28153056843 32911154727235295990812286024229248664613968343565853528081 3944047802741087976232295379906625025039873061149207698175450509593267819265697\ 8180566367107058835348734856337259496144512671005247056783395886175117800252193\ 10532598833922006022762544181720 32911154727235295990812286024229248664613968343565853528081 3944047802741087976232295379906625025039873061149207698175450509593267819265697\ 8180566367107058835348734856337259496144512671005247056783395886175117800252193\ 10532598833922006022762544181720 true true http://domino.research.ibm.com/comm/research_projects.nsf/pages/security.homoenc.html/$FILE/stocdhe.pdf 椭圆曲线同态/自同态 椭圆曲线同态主要就是同种:两EC中1000点对100点满射,或1000点一些同阶点对100点同阶点满射。。。都可能同态,同种这种同态要求点阶一样而成的同态 In mathematics, an isogeny is a morphism of varieties between two abelian varieties (e.g. elliptic curves) that is surjective and has a finite kernel. Every isogeny is automatically a group homomorphism between the groups of k-valued points of A and B, for any field k over which f is defined. Contents 1 Etymology 2 Case of elliptic curves 3 See also 4 References [edit] Etymology From the Greek (iso-) and Latin (genus), the term isogeny means "equal origins", a reference to the geometrical fact that an isogeny sends the point at infinity (the origin) of the source elliptic curve to the point at infinity of the target elliptic curve. [edit] Case of elliptic curves For elliptic curves, this notion can also be formulated as follows: Let E1 and E2 be elliptic curves over a field k. An isogeny between E1 and E2 is a surjective morphism of varieties that preserves basepoints (i.e. f maps the infinite point on E1 to that on E2). Two elliptic curves E1 and E2 are called isogenous if there is an isogeny . This is an equivalence relation, symmetry being due to the existence of the dual isogeny. As above, every isogeny induces homomorphisms of the groups of the k-valued points of the elliptic curves. 椭圆曲线自同态《信息安全中的数学方法与技术》冯登国书里举了4个例子 1: p mod4==1,iy的i要求是4阶点,随机验了5个点都没问题: y^2=x^3+21x f: (x,y)------>(-x,iy) -x^3-21x = i^2*y^2=-y^2 p:=NextPrime (13); p; pp:=p mod 4; pp; K := FiniteField(p); K; E := EllipticCurve([K|0,0,0,21,0]); E; v:=# E; v; FactoredOrder(E) ; Trace(E); TraceOfFrobenius(E); r1:=Random(E); r1; r2:=Random(E); r2; Points(E); r1+r2; m1:=Points(E, 451); m1; m2:=Points(E, -451); m2; IsPoint(E, 451); h:=12^3+4*12 ; h; hh:= 5^2 ; hh; (h mod p) eq (hh mod p); g:=(-12^3+4*(-12) )mod p; g; z1:=E![5,3]; z2:=E![2,13]; z3:=E![6,11]; z4:=E![11,7]; z5:=E![15,16]; gg:=5 * z1 ; gg; gg eq z1; ggg:=5 * z2 ; ggg; ggg eq z2; gggg:=5 * z3; gggg; gggg eq z3; ggggg:= 5 *z4; ggggg; gggggg:=5 *z5; gggggg eq z5; Order(r1); Order(r2); 17 1 Finite field of size 17 Elliptic Curve defined by y^2 = x^3 + 4*x over GF(17) 16 [ <2, 4> ] 2 2 (12 : 5 : 1) (2 : 13 : 1) {@ (0 : 1 : 0), (0 : 0 : 1), (2 : 4 : 1), (2 : 13 : 1), (5 : 3 : 1), (5 : 14 : 1), (6 : 6 : 1), (6 : 11 : 1), (8 : 0 : 1), (9 : 0 : 1), (11 : 7 : 1), (11 : 10 : 1), (12 : 5 : 1), (12 : 12 : 1), (15 : 1 : 1), (15 : 16 : 1) @} (5 : 3 : 1) [ (9 : 0 : 1) ] [ (8 : 0 : 1) ] true (9 : 0 : 1) 1776 25 true 9 (5 : 3 : 1) true (2 : 13 : 1) true (6 : 11 : 1) true (11 : 7 : 1) true 4 4 2: p mod 3 要找3阶元乘横座标 f: (x,y)------>(kx,y) 特征:f^2+f+1=0的根为ω,ω^3=1,ω^2=1-ω ω^3*x^3+5=x^3+5=y^2 p:=NextPrime (17); p; pp:=p mod 3; pp; K := FiniteField(p); K; E := EllipticCurve([K|0,0,0,0,5]); E; v:=# E; v; FactoredOrder(E) ; Trace(E); TraceOfFrobenius(E); r1:=Random(E); r1; r2:=Random(E); r2; Points(E); z1:=E![8,17]; z1; gg:=18*z1; gg ; ggg:=16*z1; ggg; gggg:=7*z1; gggg; ggggg:=6*z1; ggggg; gggggg:=10*z1; gggggg; ggggggg:=12*z1; ggggggg; gggggggg:=1*z1; gggggggg; ggggggggg:=0*z1; ggggggggg; Order(r1); Order(r2); 19 1 Finite field of size 19 Elliptic Curve defined by y^2 = x^3 + 5 over GF(19) 27 [ <3, 3> ] -7 -7 (1 : 14 : 1) (12 : 17 : 1) {@ (0 : 1 : 0), (0 : 9 : 1), (0 : 10 : 1), (1 : 5 : 1), (1 : 14 : 1), (5 : 4 : 1), (5 : 15 : 1), (7 : 5 : 1), (7 : 14 : 1), (8 : 2 : 1), (8 : 17 : 1), (10 : 6 : 1), (10 : 13 : 1), (11 : 5 : 1), (11 : 14 : 1), (12 : 2 : 1), (12 : 17 : 1), (13 : 6 : 1), (13 : 13 : 1), (15 : 6 : 1), (15 : 13 : 1), (16 : 4 : 1), (16 : 15 : 1), (17 : 4 : 1), (17 : 15 : 1), (18 : 2 : 1), (18 : 17 : 1) @} (8 : 17 : 1) (0 : 1 : 0) (8 : 17 : 1) (8 : 17 : 1) (0 : 1 : 0) (8 : 17 : 1) (0 : 1 : 0) (8 : 17 : 1) (0 : 1 : 0)9 3 3 f:(x,y)---->f(x^q,y^q) 特征:f^2-t*x+q=0,t为FrobeniusMap迹,f^2-t*x+q=0的根为[-t+(t^2-4q)^(1/2)]/2和[-t-(t^2-4q)^(1/2)]/2 一个很难的定理:Frobenius映射叠代定理得出: x^(3q)+a*x^q+b=y^3 K := FiniteField(2,101); // finite field of size 2^101 > E := EllipticCurve([K!1,0,0,0,1]); E; # E; NumberOfGenerators(E); AutomorphismGroup(E); FactoredOrder(E) ; FrobeniusMap(E); FrobeniusMap(E, 3); Trace(E); E1 := EllipticCurve([ GF(23) | 1, 1 ]); > E2 := EllipticCurve([ GF(29, 2) | 1, 1 ]); f := map<E1 -> E2 | P :-> 2*P>;f; 不同域之间,只要a,b同就可能找出同态 Elliptic Curve defined by y^2 + x*y = x^3 + 1 over GF(2^101) 2535301200456455833701195805484 1 Abelian Group isomorphic to Z/2 Defined on 1 generator Relations: 2*$.1 = 0 Mapping from: Abelian Group isomorphic to Z/2 Defined on 1 generator Relations: 2*$.1 = 0 to Power Structure of MapSch given by a rule [no inverse] [ <2, 2>, <1211597, 1>, <523132114155213291569143, 1> ] Elliptic curve isogeny from: CrvEll: E to Elliptic Curve defined by y^2 + x*y = x^3 + 1 over GF(2^101) taking (x : y : 1) to (x^2 : y^2 : 1) Elliptic Curve defined by y^2 + x*y = x^3 + 1 over GF(2^101) Elliptic curve isogeny from: CrvEll: E to Elliptic Curve defined by y^2 + x*y = x^3 + 1 over GF(2^101) taking (x : y : 1) to (x^8 : y^8 : 1) Elliptic Curve defined by y^2 + x*y = x^3 + 1 over GF(2^101) 2969292210605269 Mapping from: CrvEll: E1 to CrvEll: E2 given by a rule [no inverse] http://jpkc.szpt.edu.cn/2007/sznk/UploadFile/ziliao/wenzhang/smartcard/ECC%D4%DA%D6%C7%C4%DC%BF%A8%C9%CF%B5%C4%CA%B5%CF%D6.PDF http://www.math.uga.edu/~pete/SC1-endomorphisms.pdf Computing the endomorphism ring of an ordinary elliptic curve |
|
|
[推荐]英国情报机构GCHQ推出“破密码招特工”活动
对着答案理解啊,你也行 |
|
|
[推荐]英国情报机构GCHQ推出“破密码招特工”活动
贴着慢慢看。。。 第1关:RC4被绕了过去: 15b436de1f9107f3778aad525e5d0b20.js https://apply.gchq-careers.co.uk/15b436de1f9107f3778aad525e5d0b20.js 第2关 PYTHON CODE.GOOGLE.COM.API IE9 第3关 密码: Pr0t3ct!on#cyber_security@12*12.2011+ 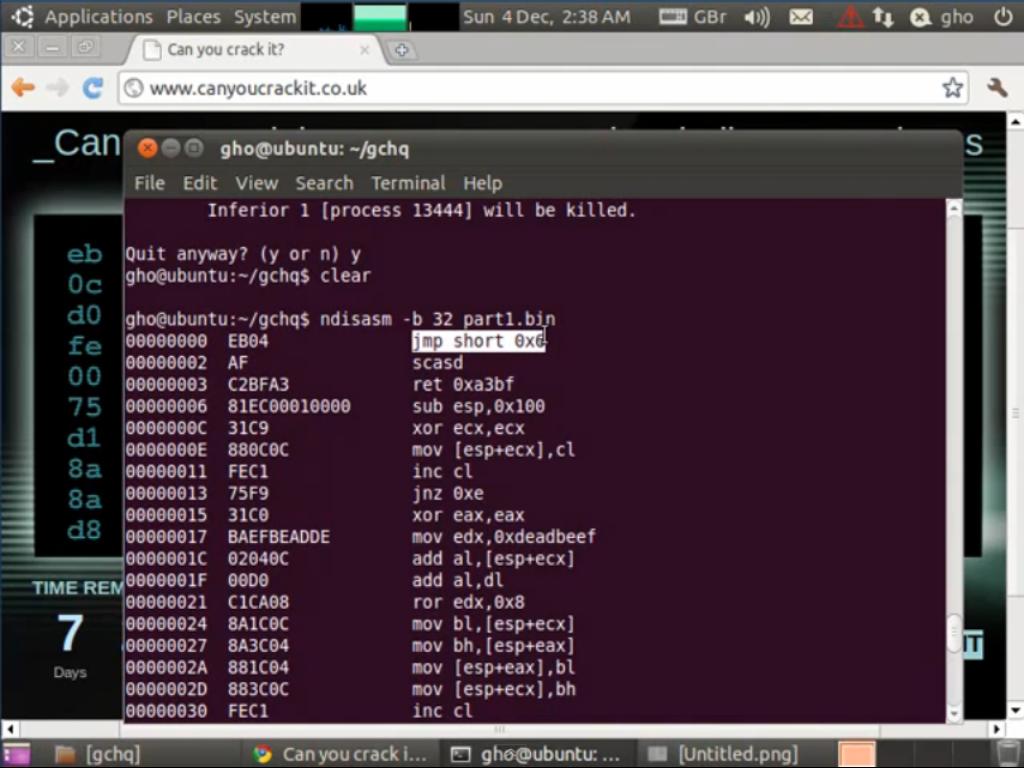 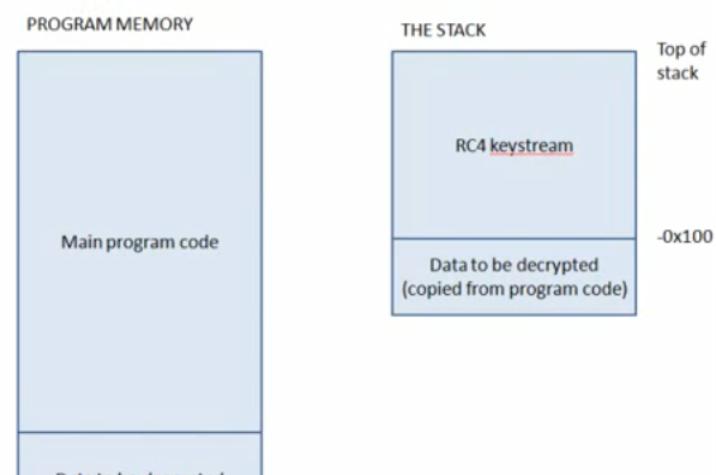   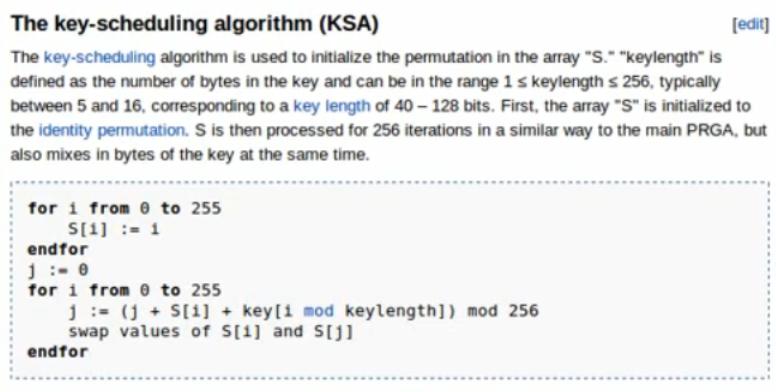 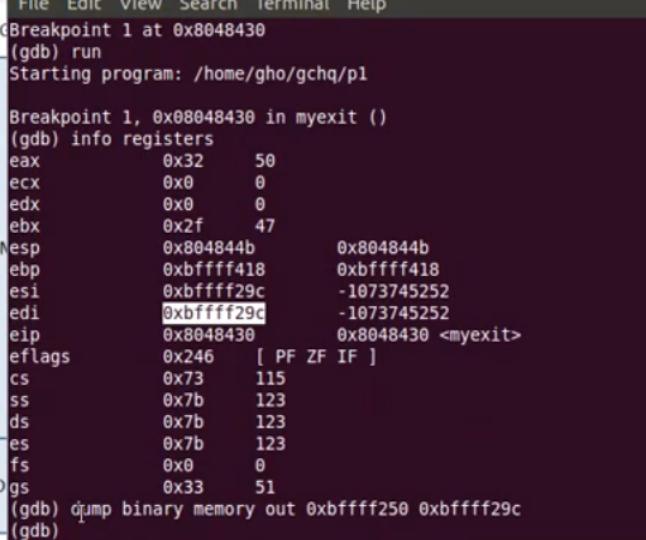 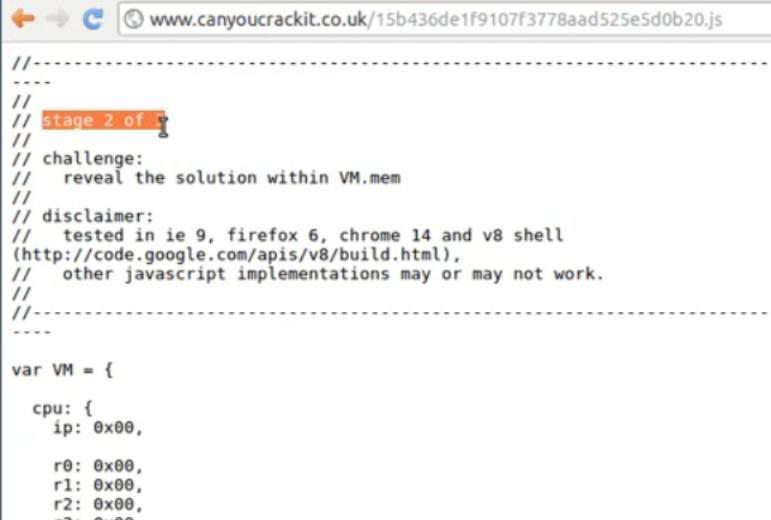 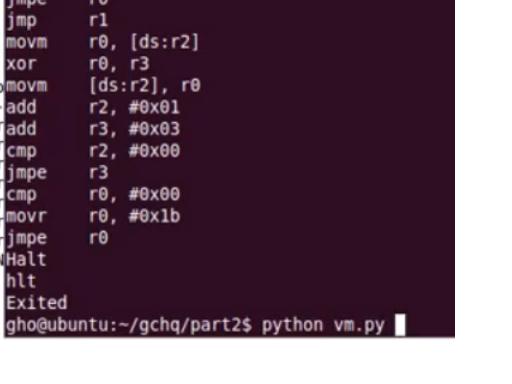 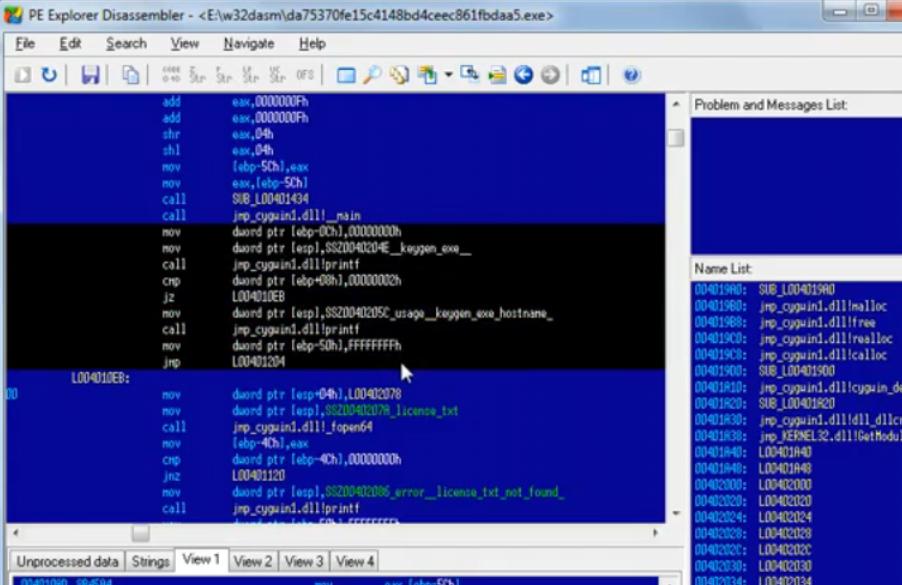 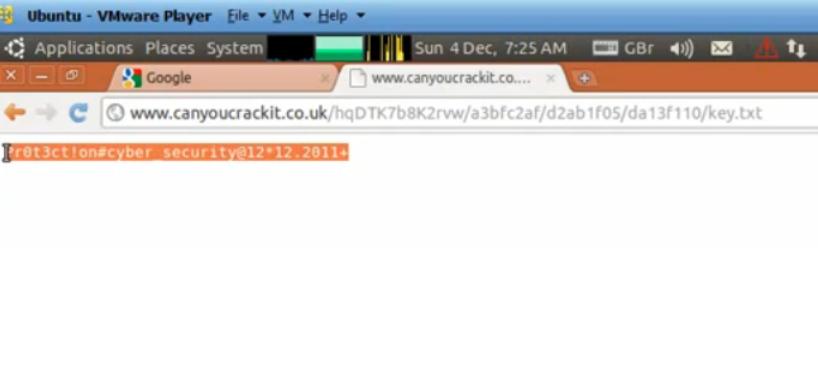 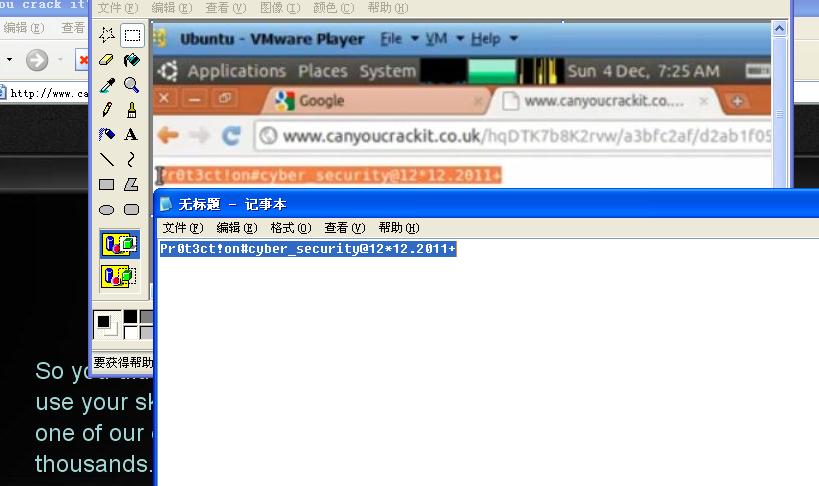 |
|
|
[推荐]英国情报机构GCHQ推出“破密码招特工”活动
camoList VPN: supports all websites and programs, unlimited bandwidth, no ads, no logs, and much more! Shortcuts Facebook YouTube Twitter MySpaceMySpace mobile Yahoo! Mail Google MSNAIMYahooGoogle TalkMySpace IMICQ GCHQ CanYouCrackIt Solution explained Sunday, 4 December 2011How to solve the GCHQ challenge Tweet NEWS AGENCIES: Click here for press release text. Below are three videos demonstrating how to solve the GCHQ challenge by Dr Gareth Owen at the School of Engineering, University of Greenwich, England. Stage 1 is arguably the most difficult, followed by stage 3 and finally stage 2 as the easiest. Stage 1 To enlarge videos, click play and then press the Youtube button at bottom of video. Files to download: p1-complete.asm (this one prints the decrypted data to the screen - no need to use debugger) Stage 2 Files to download: PHP VM Implementation (by me) Explanation of VM code (by me) Conversion of VM code to C (by me) There isn't anything further hidden in Stage 2 - GCHQ have confirmed to me. Despite the appearance in the second decrypter (the erroneous jmp); allegedly this is a left over relic because they simplified the puzzle for fear it was too difficult. Stage 3 GCHQ kindly wrote to me to say the fscanf bug was deliberate - so that you could override the crypt check; seems I took a short cut! Files to download: C representation of executable Press release text Please feel free to use or modify the following text in your story. The British spy agency GCHQ recently published a puzzle on www.canyoucrackit.co.uk, just a few days later Dr Gareth Owen, an academic at the University of Greenwich in England has posted a full video explanation of the puzzle. The puzzle has three stages and is not at all simple — likely to challenge even the best computer science graduates. The first stage is to convert the code on the screen to computer code, which turns out to be a decryption algorithm. The data to be decrypted is hidden in the image on the web site (the image of the numbers). The second stage asks you to build a virtual computer to run a series of codes - which when run produce the link to the third stage. The third stage gives you a program to run which requires a licence key - the problem is finding the licence key which requires decoding the program and seeing how it works. Then you have to find three hidden numbers from the first two stages and plug them in to get the web address for the final answer. There has been some speculation that there is a fourth stage hidden in stage 2, although GCHQ have contacted Gareth and guaranteed there isn't. Click here for solution videos Posted by Dr Gareth Owen at 03:32 Email ThisBlogThis!Share to TwitterShare to Facebook23 comments: radical said... This post has been removed by the author. 4 December 2011 11:39 radical said... The password that generates the hash for stage3 is: cyberwin Quite simple to find with John the Ripper given the weak DES hashing algorithm used. Hence you can construct the license.txt file: "gchqcyberwin" followed by the dwords from the previos stages. Obviously this is not really needed, but it's nice to know :) 4 December 2011 11:42 dougie said... Such a shame it's written in the wrong assembler language for me. S/370 would have been much more fun. I must get round to learning 586/686 assembler some time. Thanks for the explanation. 4 December 2011 12:41 Ralph Corderoy said... I'm more at home with ARM than x86 but are you sure the "sub esp, 0x100 ; 4096 bytes" is correct? Is it not gaining 256 bytes ready for the following loop to fill with [0, 255]? 4 December 2011 17:10 David Glance said... Hi Gareth, Great explanation and videos. Are you getting your undergrads to do this exercise? I was wondering how many of them would understand it all? 4 December 2011 22:54 Dr Gareth Owen said... Ralph you're correct - someone else spotted the mistake too and I've amended the video. David - I won't be giving it to the undergrads no as we don't teach low level assembly in our department but I'll no doubt show them the videos. 5 December 2011 00:06 J. Sadir Vanderloot said... What an amazing presentation, thank you very much. 5 December 2011 05:25 kwdiaper said... This was pretty epic, I would think a lot of computer science students would find this extremely challenging, however it's a good eye opening puzzle. I have to say I would of taken a long time to even clue into the fact that the 0xEF was a jump instruction but after you pointed it out it made sense. 5 December 2011 07:17 Dr Atomic said... Man, u r 7337 haxx0r! 5 December 2011 15:10 mesh3altest said... it's all about assembly? i wonder what exactly your resources in order to understand all this stuffs, another meaning, what books you read to understand x86 assembly? could you recommend some? Thanks for the great demonstration 5 December 2011 15:51 jitsuki said... Well done and thanks for the brilliant explanation. However, like you say, a rather disappointing end for quite a lot of work! 6 December 2011 04:56 shep said... Dr Owen, As a CIT undergrad in the US, I found this extremely challenging compared to traditional war-games such as smash the stack, over the wire, etc... Thanks for the contribution! 6 December 2011 06:56 Edi MacCohen said... Nicely presented exposition of the challenge. The problem with the challenge itself is that it contains no real fundamental test of the would-be solver's raw logico-algorithmic thinking capacity or originality. Instead, it concentrates on a mechanical familiarity with interrelationships of various mid-to-low-level hardware and software frameworks. In that sense, it is more of an orienteering challenge than of cryptanalytic insightfulness. 6 December 2011 08:33 Anon79EzapU9 said... Hello Gareth! How many more students do you think these videos have recruited? If this doesn't act as a good advert for you department ( http://www.gre.ac.uk/schools/engineering/departments/c_and_c ) what does? 6 December 2011 09:47 Summerm00n said... All that brain power and the salary is £31k!! 6 December 2011 09:54 b198111a-204b-11e1-87bc-000bcdcb2996 said... Thank you for the videos. I work in IT but never finished my degree this just motivated me in to getting it done so i would be able to do alot of this sort of thing my self as i find it very intresting 6 December 2011 12:49 Joe said... Excellent videos. The skills that you've demonstrated are sadly very rare these days - I know many IT professionals who wouldn't have a clue what you did here, and (correct me if i wrong) i doubt they even teach this stuff any more at University. Sadly computers have become like cars - 99% of users have no idea about the inner workings, yet they drive them every day :( 6 December 2011 14:23 Phil Rogers said... That was an amazing piece of detective work! As I'm unfamiliar with that particular machine code, I wouldn't have recognised it as code. Nor would I have recognised the BASE64 encoding. Well done. 6 December 2011 14:41 Etienne de L'Amour said... Thanks Gareth, Bit disappointed at the challenge, in a way. Was hoping it might offer a number of different routes, with differing resultant keywords, to make it more inter-disciplinary and to sort out the high fliers from the 99.9% of candidates who -- like me -- were "also rans". Was hoping that the exe itself would manipulate the "supposed" keyword sent in the clear ... Nada. 7 December 2011 01:33 Dr Gareth Owen said... Etienne, there's speculation there's more to the puzzle than meets the eye :-) 7 December 2011 03:54 Etienne de L'Amour said... Hope so, Gareth. I don't know why I hadn't even thought of writing my own VM in php or js, and not at all happy about using other folks' code. Will have a go in php and see if I can get a better understanding of what's going on. Regards ~ ET. 7 December 2011 04:05 Tim S said... Great work, and a very clear and entertaining explanation of the solution. Many thanks for sharing it Gareth. 7 December 2011 04:25 jojoid said... Your PHP vm does not calculate instruction length correctly for untaken jmpes -- you were lucky the code only uses short ones. 8 December 2011 04:07 Post a Comment Home Subscribe to: Post Comments (Atom) Followers Blog Archive ▼ 2011 (1) ▼ December (1) How to solve the GCHQ challenge About Me Dr Gareth Owen View my complete profile Awesome Inc. template. Powered by Blogger. |
|
|
[推荐]英国情报机构GCHQ推出“破密码招特工”活动
http://www.canyoucrackit.co.uk/ http://www.theregister.co.uk/2011/12/05/gchq_code_breaking_puzzle_solved/ http://gchqchallenge.blogspot.com/ http://blog.jgc.org/2011/12/is-there-another-gchq-code-challenge.html Is there another GCHQ Code Challenge? Update: The answer is Yes, sort of. Last week GCHQ issued a 'code challenge' as a way of attracting candidates via a web site called Can You Crack It?. I did the challenge, which actually consists of three parts and has more to do with assembly language and reverse engineering skills than cryptography (in fact, the only time you come across a cryptographic function, you can completely ignore it). The cat is completely out of the bag now because some spoilsport published complete details on the web showing how to break it, but I think there may be one more mystery worth investigating. Part 2 of the challenge involves writing a virtual machine that executes some code to decrypt an in memory buffer containing an HTTP command. Here's a dump of the memory of the virtual machine after execution: 0000: 31 04 33 aa 40 02 80 03 52 00 72 01 73 01 b2 50 1.3.@...R.r.s..P 0010: 30 14 c0 01 80 00 10 10 00 00 00 00 00 00 00 00 0............... 0020: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0030: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0040: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0050: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0060: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0070: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0080: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0090: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00a0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00b0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00c0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00d0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00e0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 00f0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0100: 32 00 75 0c 31 08 33 32 40 02 80 03 52 00 72 01 2.u.1.32@...R.r. 0110: 73 03 b2 00 c3 b0 00 30 1b c0 01 ff 00 00 00 00 s......0........ 0120: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0130: 00 00 75 10 01 00 00 00 00 00 00 00 00 00 00 00 ..u............. 0140: cc 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 0150: 7d 1f 15 60 4d 4d 52 7d 0e 27 6d 10 6d 5a 06 56 }..`MMR}.'m.mZ.V 0160: 47 14 42 0e b6 b2 b2 e6 eb b4 83 8e d7 e5 d4 d9 G.B............. 0170: c3 f0 80 95 f1 82 82 9a bd 95 a4 8d 9a 2b 30 69 .............+0i 0180: 4a 69 65 55 1c 7b 69 1c 6e 04 74 35 21 26 2f 60 JieU.{i.n.t5!&/` 0190: 03 4e 37 1e 33 54 39 e6 ba b4 a2 ad a4 c5 95 c8 .N7.3T9......... 01a0: c1 e4 8a ec e7 92 8b e8 81 f0 ad 98 a4 d0 c0 8d ................ 01b0: ac 22 52 65 7e 27 2b 5a 12 61 0a 01 7a 6b 1d 67 ."Re~'+Z.a..zk.g 01c0: 47 45 54 20 2f 64 61 37 35 33 37 30 66 65 31 35 GET /da75370fe15 01d0: 63 34 31 34 38 62 64 34 63 65 65 63 38 36 31 66 c4148bd4ceec861f 01e0: 62 64 61 61 35 2e 65 78 65 20 48 54 54 50 2f 31 bdaa5.exe HTTP/1 01f0: 2e 30 00 00 00 00 00 00 00 00 00 00 00 00 00 00 .0.............. 0200: 37 7a 07 11 1f 1d 68 25 32 77 1e 62 23 5b 47 55 7z....h%2w.b#[GU 0210: 53 30 11 42 f6 f1 b1 e6 c3 cc f8 c5 e4 cc c0 d3 S0.B............ 0220: 85 fd 9a e3 e6 81 b5 bb d7 cd 87 a3 d3 6b 36 6f .............k6o 0230: 6f 66 55 30 16 45 5e 09 74 5c 3f 29 2b 66 3d 0d ofU0.E^.t\?)+f=. 0240: 02 30 28 35 15 09 15 dd ec b8 e2 fb d8 cb d8 d1 .0(5............ 0250: 8b d5 82 d9 9a f1 92 ab e8 a6 d6 d0 8c aa d2 94 ................ 0260: cf 45 46 67 20 7d 44 14 6b 45 6d 54 03 17 60 62 .EFg }D.kEmT..`b 0270: 55 5a 4a 66 61 11 57 68 75 05 62 36 7d 02 10 4b UZJfa.Whu.b6}..K 0280: 08 22 42 32 ba e2 b9 e2 d6 b9 ff c3 e9 8a 8f c1 ."B2............ 0290: 8f e1 b8 a4 96 f1 8f 81 b1 8d 89 cc d4 78 76 61 .............xva 02a0: 72 3e 37 23 56 73 71 79 63 7c 08 11 20 69 7a 14 r>7#Vsqyc|.. iz. 02b0: 68 05 21 1e 32 27 59 b7 cf ab dd d5 cc 97 93 f2 h.!.2'Y......... 02c0: e7 c0 eb ff e9 a3 bf a1 ab 8b bb 9e 9e 8c a0 c1 ................ 02d0: 9b 5a 2f 2f 4e 4e 00 00 00 00 00 00 00 00 00 00 .Z//NN.......... 02e0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 02f0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ There are three colors used there to highlight areas: memory in blue was executed, memory in red was both read and written, memory in green was read, written and executed. As you can see the program starts running at 0x0000. There there's small program that decrypts the block of memory between 0x100 and 0x14F and jumps to 0x100. The decrypted program decrypts the memory at 0x1C0 to reveal the HTTP command that is used to execute part 3 of the GCHQ challenge. But what about all the rest of the unused memory? No other part of the GCHQ challenge wastes bytes, they are all used for something, but here there's a ton of memory that's filled with data and that isn't referred to anywhere else. Is this a hidden fourth part of the GCHQ challenge? Perhaps even the real challenge? If you look into the first block of data that's been decrypted there are two intriguing pieces of additional information. At 0x132 there are three bytes: 75 10 01. Those three bytes are actually valid code in the virtual machine. They mean 75 10 add ds, 0x10 01 jmpr r1 This seems like perfectly reasonable code. It moves the data segment forward by 0x10 and then jumps to R1. At the end of execution of the original program the data segment is at 0x1c. Thus moving it forward puts it at 0x2c (i.e. the block starting at 0x02c0 above). An alternative explanation is that based on the initial conditions of the VM that data segment would now be 0x20 (i.e. pointing immediately after the decrypted HTTP command at 0x0200). Also at the end of running the program R1 contains 0x08. Doing the jump would drop straight into the decryption loop just past the initialization and into the XOR portion. That could be totally valid. The jump would take the instruction pointer to: 10:08 movm r0, [ds:r2] 10:0a xor r0, r3 10:0c movm [ds:r2], r0 10:0e add r2, 01 10:10 add r3, 03 10:12 cmp r2, 00 10:14 jmpe r3 10:15 cmp r0, 00 10:17 movr r0, 1b 10:19 jmpe r0 10:1a jmpr r1 The only other clue is that there's the byte 0xCC in the decrypted memory. And one more thing. Notice the 10:14 jmpe r3. That never gets taken because r2 is never 00. But if you investigate the circumstances under which r2 would be 00 you find that it's when r3 would be 0x32 (i.e. when that jump would take you right to the 75 10 01 sequence that's been decrypted). I haven't had enough free time to investigate this further. Perhaps it's a red herring, but it looks awfully suspicious. Especially given that the main loop will take that jump instruction when it's completely exhaused 0x100 bytes of data. This little 'subroutine' then moves the data segment on by 0x10 (i.e. 0x100 bytes) and the decryption will continue until a 00 byte is written. So it looks valid and is designed to cope with not having hit a 00 before the end of a segment. PS It's been pointed out to me that the Can You Crack It? web site has been altered since the beginning to add the words "The challenge continues". Labels: security If you enjoyed this blog post, you might enjoy my travel book for people interested in science and technology: The Geek Atlas. Signed copies of The Geek Atlas are available. Looking for a new job? Try UseTheSource. posted by John Graham-Cumming at 06:13 Permalink 1 Comments: Phlash said... Hi John, According to my understanding, the code at offset 0x132 is already used as part of the 2nd decryption loop: [entry to here by long jump to 0x10:0, thus cs==0x10] 0x100: movr r2,#0 0x102: add r5,#12 <-- move ds to encrypted block 0x104: movr r1,#8 <-- preload r1 with return address 0x106: movr r3,#50 <-- preload XOR value *and jump address* 0x108: movm r0,[ds:r2] <-- return from jump here 0x10A: xor r0,r3 0x10C: movm [ds:r2],r0 0x10E: add r2,#1 <-- increment pointer 0x110: add r3,#3 <-- increment XOR 0x112: cmp r2,#0 <-- rollover? 0x114: jmpe [r3] <-- when r2==0, r3==50, thus cs:50 == 0x132 :) 0x115: cmp r0,#0 <-- terminate at zero decrypted value 0x117: movr r0,#27 0x119: jmpe [r0] 0x11A: jmp [r1] 0x11B: hlt ... 0x132: add r5,#16 0x134: jmp [r1] of course it terminates early (at the first decrypted zero value), but what woudl happen if we let it continue to the end of mem[] array? 2:52 PM 代码解释 在这三个阶段的挑战是设计,使参加者能证明分析的shellcode和模糊处理机制,逆向工程恶意的二进制代码和漏洞分析的基础。这些技术在网络安全专家GCHQ的基本技能。 第1阶段 这将启动canyoucrackit.co.uk网站的主要形象。为了解决这一阶段是必要的,以确定这是由英特尔x86兼容处理器可以运行的代码。经过分析,这是明确的,本机代码实现RC4解密算法,并且能够解密的PNG文件中的注释标记,隐藏在的数据块。一旦解密,这个数据揭示的挑战第2阶段的位置。 第2阶段 这是一个JavaScript编程的挑战,网络安全的角度。为了解决这一阶段实施一个简单的虚拟处理器是必需的。在体系结构上的一些注意事项提供可分析的数据块。解决这个阶段,就会发现最后阶段所面临的挑战。 第3阶段 最后一个阶段是逆向工程的挑战。可以下载一个可执行文件的位置显示在第2阶段。此可执行文件解析的许可证文件 - 面临的挑战是,如果它得到正确的输入,显示超过,和“成功”页面的链接提供给参与者。 我们包括许多方面,这个阶段是可以解决的,因为我们有兴趣,看到人们如何将攻击的问题 - 未来与创新的解决方案看似不可能的问题是在GCHQ的日常工作。例如,有一些安全专家评论fscanf缓冲区溢出,我们在此可执行文件包括 - 解决问题的一个选项,将使用这个溢出来跳过某些检查可执行。这个阶段的其他替代品涉及打破弱的地穴,修补的可执行文件,直接绕过检查,或分析的汇编指令,并意识到这是一个完整的引水。 这一挑战的三个阶段突出不同的机器代码分析技术 - GCHQ为何不关心这些技术(确实是其他类型的机器代码分析)? GCHQ网络安全专家花时间分析来自许多源的可执行代码。有时可以从恶意软件已经被发现,工作它做什么,以及它从何而来。在其他场合,它可以协助,在安全产品的评估,以确保,开发商已经打算这样做实际上是什么,他们已经在实践中实现。 显然,寻找一个解决方案在线 - 甚至完成页面 - 的是最简单的方法来解决挑战各种提示,联系,并已放置部分解决方案的在线挑战开始以来的各个阶段,但我们真的很高兴看到有多少人独立解决这一挑战,并显示在这个社会中存在的技能,深度和广度。 本次招聘的挑战是制定我们的技术人员,行使需要的关键技能,以帮助抵御网络攻击英国网络:“设计这一挑战,把我们离我们的日常工作中极少量的时间,还使我们有机会工程师是既有趣和技术上复杂的东西,虽然我们每天所做的工作非常相似,这是令人难以置信的回报后续的挑战,产生的外部关注和分析。“ 该活动已经结束。不过,如果你喜欢运用这些技能,并希望能帮助维护国家安全,注册您在我们通过下面的按钮的网络角色的兴趣。 |
|
|
[推荐]英国情报机构GCHQ推出“破密码招特工”活动
网络安全专家 参考CYBER/SEC/SPEC/11第2期 西南部的 位置切尔滕纳姆 薪酬英镑25,446(GC10)三万一千一百五十二英镑(GC9) |
|
|
[推荐]英国情报机构GCHQ推出“破密码招特工”活动
Part 5 Part 6 都填字母游戏,,,,得花大时间 最后答案是数独 INTEGRALS Part one: 143, 189, 429 Part two: 859, 265 Part three: 451, 756, 912 Part four: 448, 131, 813 Part five: 324, 242, 692 Part six: 781, 774, 675 这一挑战是在六个部分,每个包含三个难题,和所有领先的9个字母的单词的形式,用数学的连接到一个单一的答案。 尽管三重挑战的性质,没有三角形的知识是必要的。它不会很清楚,第一个整体结构所面临的挑战是什么,但通过六个部分,你的工作会透露给你。 ,虽然一个完美的答案涉及解决每一个难题,它可能是有可能得到整体的答案,而无需解决每一个难题,并后的难题很可能投在早期的光(换句话说,如果你深陷在初期,不放弃)。 在一般情况下,已用于整个英国的拼写和格式的日期和美国拼写只有被使用时,它可以帮助,或添加有趣的混乱。说到这是一个特定的拼图,专业'Americanisms“。总体来说有很多(但没有太深的逻辑,一个公平的语言和数学smidgeon,我们不希望看到任何答案,使用积分或三角)。 网络安全专家 参考CYBER/SEC/SPEC/11第2期 西南部的 位置切尔滕纳姆 薪酬英镑25,446(GC10)三万一千一百五十二英镑(GC9) 纪律数码 级GC10/GC9 申请截止日期是2011年12月12日 职位空缺描述 网络安全专家 - GC10 高级网络安全专家 - GC9 GCHQ是在全国的网络安全战略的最前沿,并致力于确保我们的政府可以在网络空间与信心。我们致力于保持领先由不断变化的数字世界要求奇快。 在游戏中我们的对手没有规则和未知的边界线,你将探索的可能性,并发明了看似不可能的。我们需要可以推动技术边界和应付未知的先驱。我们的工作涉及到操作系统,复杂的网络和IT安全基础的深处的旅程。 要求 我们正在寻找高素质,具有雄厚的技术技能的热情和创新的个人。你必须要善于解决问题的步伐提供,并有工作能力,作为一个团队的一部分。 资格 研究生层次:我们正在为2:1最小程度在干相关的主题(科学,技术,工程和数学)的毕业生,最好是一个重要的IT组件。 经历了:我们的专业知识,专业资格和/或在正式或非正式的的环境中获得的实际经验的人。 请确保如果您是现有的公务员或已被以任何名义在政府工作的参与,您的应用程序,并在您的简历内容的反应仍然未分类水平。 责任 成功的候选人将从事各种各样的角色,他们解决问题的能力将是关键。跨GCHQ的网络任务范围内的角色,这是由于广泛的职权范围,我们要在保护和防御的HMG和重要的国家基础设施协助。职权范围包括政府资讯科技系统的保护,开展研究和开发,发现新的威胁,提供法医,恶意软件和入侵分析,以及今天在网络世界中使用的技术种类繁多,在未来的专家。 我们不只是寻找优秀的人才,我们正在寻找的人,或有可能成为专家,在各自的领域。您将使用您的技术专长的先驱解决复杂问题,而不是只提供规范,因此,你经常会需要你的技术技能结合起来,虚心的态度。 附加信息 薪酬 GC10位置的起薪是25,446英镑。 GC9位置起薪三万一千一百五十二英镑。 GCHQ保留权利,以评估在两个年级的候选人。 你的工资将根据工作5天工作周42小时,包括午餐间隔1小时(37小时)。弹性工时制度在大部分地区,依赖于业务需求。在可用的情况下,允许个人不同的时间,他们开始和完成工作的每一天,使他们采取长达4天,每4周期间的额外假期(“弹性”)。 GCHQ经营非综合性能相关付款计划,使工作人员达到规定的性能水平,以吸引非综合性能付款支付。每月转移支付拖欠的薪酬。每年10月检讨薪级。 年假 GCHQ新加入者有一个基本的每年22天假期的权利(否则为“假”),上升至25天,经过一年的服务。 经过10年的服务,你的年假将上升到每年30天。 GCHQ是灵活,在离开的权责发生制,使人员进行或预期年假,从一年到另一台。 此外,有10.5天,为公众和特权假期。 退休金 当你加入GCHQ时,你有资格加入公务员长俸安排。我们提供两种类型的养老: NUVOS - 这是一个职业养老金计划,目前有会员3.5%的贡献率。作为你的雇主,我们满足成本计划的其余部分。 合伙养老金账户 - 这是从你的雇主的贡献与利益相关者养老金。我们付出的多少是根据你的年龄。我们付出这样无论您是否选择作出贡献什么。您不必作出贡献,但如果你这样做,我们也将匹配您的贡献,你的长俸收入的3%。除了上面提到的与年龄有关的贡献的贡献。 申请流程 注意:应用程序上线仅。我们鼓励您彻底,为下一阶段的邀请是根据这些信息来填写申请表。不幸的是,我们不能追求的申请人不提供申请表格上的所有相关信息。 还请确保您保持您的“主要细节”节到您的联系人的任何更改的详细信息,尤其是您的电子邮件地址 - 因为这将是我们与您沟通的主要方法。 填写完整的应用程序,然后在选拔过程中下面一节中描述的过程。候选人的开支可能会支付给参加评估中心或面试的候选人。 候选人的开支 申请人参加评估中心,将有他们的排位赛英国发生的费用支付,合理过夜,最高55英镑,铁路票价标准的唯一或基本里程津贴(每英里15便士),如果乘车。如何索赔的详细信息将提供工作人员,当你参加评估中心或采访。 GCHQ不支付测试活动的索赔。 您的公开个人资料 GCHQ是一个组织,具有至关重要的秘密的安全,国防和英国的经济福祉。外国情报机构活跃在这个国家,并针对这些秘密。他们感兴趣的是在安全或情报机构的成员,尤其是,那些在其职业生涯的开始。 为了保护自己和英国的秘密,不采取按面值的每一个人。要特别警惕任何人显示在你的未来工作计划的不当利益;想想你做什么安全方面的问题。例如,你如何在因特网上展示自己铭记 - 不后已应用于GCHQ在社交网站!告诉任何人,你可能会去上班前请三思!点击这里阅读有关你应该如何管理你的公众形象进一步。 如果您想多一些安全停留在社交网站上的意见,请点击这里。 选拔过程 应用 应用上线仅运动的截止日期是2011年12月12日。 纸筛 招聘小组完成的应用程序的初始文件会进行筛选,以确保申请人符合的最低标准和国籍/居留权的要求。 (此筛选也需要考虑候选人宣布残疾和满足的最低标准)。 测试 在筛选阶段,成功的候选人将被邀请参加能力测试。测试将在曼彻斯特举行的2012年1月10日和2012年1月14日在切尔滕纳姆 评估中心 在测试阶段成功的申请人将被邀请出席GCHQ评估中心。评估中心定于2012年2月20日至03月09日。作为正常选择和审批过程的一部分,你还谈评审主任,你将被要求在这个时候采取了药检。 注:选择参加评估中心,将有望与他们带来他们的学位,或在上述最低入学要求的详细的职业资格证书的申请人。等待鉴定结果的申请人必须提供证据证明其结果前可委任的正式报价。 您的邀请来参加评估中心也将包含有关如何获取信用检查参考机构的报告的指导。请把你的报告,以评估中心的阶段,因为这将有助于加快的背景查询过程,你应该是成功的。 背景资料查询过程 如果成功的话,你会进步的招聘过程中,我们调查国籍,健康,安全和其他事项的下一阶段。委任的一个正式的报价不能直到这些调查已经圆满完成。这个阶段,平均需要3 - 5个月(但可以更长)。 GCHQ经营非法药品和误用或滥用合法药物的使用有严格的政策。 联系你的雇主 作为背景调查过程中的一部分,在给予任何安全检查,可以认为,从我们的人员的安全的代表将需要联络您当前的雇主。这是对您的同意后的背景调查过程通常与他们联络,一直寻求。 加入 成功完成背景调查后,考生将得到一份正式工作的提供。招聘小组将电话或电子邮件安排一个双方都方便的的日期开始GCHQ工作,会发出有关的文书。所有新入行开始自己的职业生涯,参加入职课程(运行按月)。 部署 部门的角色是广泛和多样。 GCHQ将致力于从招聘过程的最初阶段,以确定人们在具体领域的工作。因此,你需要确保你诚实和全面,你可以回答所有的问题。招聘过程中的每一个阶段的目的是确定的技能和能力,GCHQ可以最好地利用。这可能意味着你有一个特定领域的工作,但GCHQ的地方,在另一个您的偏好。这是事实,GCHQ已确定您已在其他业务领域的需求相匹配的技能,资质认可。因此,你的第一个发布部门标准,可能是至少3年;在此之后,您将能够表达为后续角色的偏爱。 |
|
|
[推荐]英国情报机构GCHQ推出“破密码招特工”活动
Part four 第一行: 7+8+3 “Banshee”在爱尔兰盖尔语中被称为“bean sidhe”,意思是“拥有超能力的女人”。她拥有露出的牙齿,红色的眼睛,只有一个鼻孔。脚部长有青蛙般的蹼,外貌令人不安的雌性妖精。 她不会做甚么大奸大恶的事情,她的眼睛红肿是因为知道有人死了所以才哭至红肿的。但是人类以为她的存在是代表不吉利,固对她仍存在着恐惧。 Banshee只针对五个主要家族:奥尼尔、奥布莱恩、奥康诺、奥格拉迪斯、卡瓦奈(the O'Neills, the O'Briens, the O'Connors, the O'Gradys and the Kavanaghs)及与这五个大家族有联姻关系的其他家族。 Banshee通常以下面3种形象中的一种出现在世人面前:年轻的女子、神情庄严的妇人、或邋遢的老巫婆,象征凯尔特神话中拥有3种不同样貌的战争与死亡女神,即Badhbh(又做“Badb”),Macha和Mor-Rioghain(又做“Morrigan”)。Banshee一般穿着灰色斗篷或缠绕的碎布、抑或死者的尸布;她也会以一名洗衣妇的形象出现,在河边清洗染满鲜血的被预言将死之人的衣物。在爱尔兰,相传她会以一名穿著绿色长裙的妙龄少女出现。在沼地出现时,会以恐怖的哭声告诉人类死亡的来临。 Banshee是一群无配偶的孤独生物,她们都是以个体而非团体生活。当多个Banshee聚集在一起恸哭则代表某位拥有崇高或神圣地位的人类即将离去。 egomania 极端利己 ebb and flow 潮的涨落 第九列: Gaius Baltar 在背叛殖民地之前,巴塔伯爵是其中一个殖民地的代表,不过他从来没有透露过他来自何处。第一集的剧本中说他来自奥利昂,不过在正式拍制的时候并没有这段剧情。在小说版中则说他是一个有钱的货品商人,赛隆人第一个找上他,寻求和平。他的“伯爵”称谓是自己加上去的。但这些资讯不在电视系列剧中被承认。 http://zh.wikipedia.org/zh-cn/%E5%8D%81%E4%BA%8C%E6%AE%96%E6%B0%91%E5%9C%B0 艾利隆星主要是一个农业殖民地,并被盖斯·巴塔称为十二殖民地的“食物篮”(foodbasket)。当描述巴塔的“原生”口音时,詹姆斯·柯利斯(James Callis)采用了约克夏口音(Yorkshire accent),因为讲这口音是美国人对来自劳动阶级的人的刻板印象,因此相当符合这个试图掩饰自己来自农业行星的角色。 http://en.wikipedia.org/wiki/Gaius_Baltar 9) Georgia, first in itinerary for US Emperor, "The Little Boot." (5) 美利坚合众国皇帝和墨西哥摄政王,诺顿一世陛下(约书亚·亚伯拉罕·诺顿,1819-1880). http://zh.wikipedia.org/wiki/%E8%AF%BA%E9%A1%BF%E4%B8%80%E4%B8%96 还把美国当殖民地。。。。。。。。。。。真要英国文化才行。。。。。 My beginning (or end if you prefer) is nowhere in particular, one greater than my parent. Splitting the great from the little I skirt somewhere where Alain De Botton would not like to live. Before I can reach an intelligent plant I lose my identity, and eleven. Ninety degrees later I recover and visit a tautological attic, then meet an orthogonal nine hundred and ninety three greater. A transition indicates that going consistently northeast leads to passing from east to south just before the origin of an eponymous bishop who made a Thatcherian mistake for which he paid even more dearly. Just after this I finish (or start, if you prefer) when three greater, though lesser, subsumes me. 我開始(或結束,如果你願意)無處,尤其是大於我父。分割小我的裙子,阿蘭德波頓不會喜歡住的地方。之前,我可以達到我失去了我的身份,智能工廠和11個。 90度後恢復訪問一個同義反复的閣樓裡,然後滿足一個正交9百九十三個更大。一個過渡表示,會始終東北之前一個同名的主教,誰做一個 Thatcherian為他支付更高昂的錯誤的起源從東到南。這方面,我剛完成(或啟動,如果你喜歡)三個較大,雖然較小,歸入我 CM3 1GS: Great and Little Leighs, Chelmsford District, Essex County, England (英格兰 埃塞克斯郡 切姆斯福德区 Great and Little Leighs) Address: Great and Little Leighs, Chelmsford District, Essex County, England (地址: 英格兰 埃塞克斯郡 切姆斯福德区 Great and Little Leighs) Postcode (邮编): CM3 1GS Latitude (纬度): 51.8271 Longitude (经度): 0.5048 Accuracy (精度): 6 阿兰·德波顿(Alain de Botton),作家,生于1969年,毕业于剑桥大学,现住伦敦。著有小说《爱情笔记》、《爱上浪漫》及散文作品《拥抱逝水年华》、《哲学的慰藉》等。 Great Notley, or formerly Great Notley Garden Village is a suburban development, mostly by Countryside Properties on the fringe of Braintree, Essex in England with an approximate population of 5,500. It became an independent civil parish on 1 April 2000 as a result of The Great Notley Parish Council Order 2000. 131-11=120 131+993=1124 Essex to Sussex埃塞克斯苏塞克斯 填字母成词 就第三部分还有点戏 448, 131 813. |
|
|
[推荐]英国情报机构GCHQ推出“破密码招特工”活动
Part TREEE: 最常 英语单词 1 the 126 name 2 of 127 very 3 to 128 through 4 and 129 just 5 a 130 form 6 in 131 much 7 is 132 great 8 it 133 think 9 you 134 say 10 that 135 help 11 he 136 low 12 was 137 line 13 for 138 before 14 on 139 turn 15 are 140 cause 16 with 141 same 17 as 142 mean 18 I 143 differ 19 his 144 move 20 they 145 right 21 be 146 boy 22 at 147 old 23 one 148 too 24 have 149 does 25 this 150 tell 26 from 151 sentence 27 or 152 set 28 had 153 three 29 by 154 want 30 hot 155 air 31 but 156 well 32 some 157 also 33 what 158 play 34 there 159 small 35 we 160 end 36 can 161 put 37 out 162 home 38 other 163 read 39 were 164 hand 40 all 165 port 41 your 166 large 42 when 167 spell 43 up 168 add 44 use 169 even 45 word 170 land 46 how 171 here 47 said 172 must 48 an 173 big 49 each 174 high 50 she 175 such 51 which 176 follow 52 do 177 act 53 their 178 why 54 time 179 ask 55 if 180 men 56 will 181 change 57 way 182 went 58 about 183 light 59 many 184 kind 60 then 185 off 61 them 186 need 62 would 187 house 63 write 188 picture 64 like 189 try 65 so 190 us 66 these 191 again 67 her 192 animal 68 long 193 point 69 make 194 mother 70 thing 195 world 71 see 196 near 72 him 197 build 73 two 198 self 74 has 199 earth 75 look 200 father 76 more 201 head 77 day 202 stand 78 could 203 own 79 go 204 page 80 come 205 should 81 did 206 country 82 my 207 found 83 sound 208 answer 84 no 209 school 85 most 210 grow 86 number 211 study 87 who 212 still 88 over 213 learn 89 know 214 plant 90 water 215 cover 91 than 216 food 92 call 217 sun 93 first 218 four 94 people 219 thought 95 may 220 let 96 down 221 keep 97 side 222 eye 98 been 223 never 99 now 224 last 100 find 225 door 101 any 226 between 102 new 227 city 103 work 228 tree 104 part 229 cross 105 take 230 since 106 get 231 hard 107 place 232 start 108 made 233 might 109 live 234 story 110 where 235 saw 111 after 236 far 112 back 237 sea 113 little 238 draw 114 only 239 left 115 round 240 late 116 man 241 run 117 year 242 don't 118 came 243 while 119 show 244 press 120 every 245 close 121 good 246 night 122 me 247 real 123 give 248 life 124 our 249 few 125 under 250 stop Rank Word Rank Word 251 open 376 ten 252 seem 377 simple 253 together 378 several 254 next 379 vowel 255 white 380 toward 256 children 381 war 257 begin 382 lay 258 got 383 against 259 walk 384 pattern 260 example 385 slow 261 ease 386 center 262 paper 387 love 263 often 388 person 264 always 389 money 265 music 390 serve 266 those 391 appear 267 both 392 road 268 mark 393 map 269 book 394 science 270 letter 395 rule 271 until 396 govern 272 mile 397 pull 273 river 398 cold 274 car 399 notice 275 feet 400 voice 276 care 401 fall 277 second 402 power 278 group 403 town 279 carry 404 fine 280 took 405 certain 281 rain 406 fly 282 eat 407 unit 283 room 408 lead 284 friend 409 cry 285 began 410 dark 286 idea 411 machine 287 fish 412 note 288 mountain 413 wait 289 north 414 plan 290 once 415 figure 291 base 416 star 292 hear 417 box 293 horse 418 noun 294 cut 419 field 295 sure 420 rest 296 watch 421 correct 297 color 422 able 298 face 423 pound 299 wood 424 done 300 main 425 beauty 301 enough 426 drive 302 plain 427 stood 303 girl 428 contain 304 usual 429 front 305 young 430 teach 306 ready 431 week 307 above 432 final 308 ever 433 gave 309 red 434 green 310 list 435 oh 311 though 436 quick 312 feel 437 develop 313 talk 438 sleep 314 bird 439 warm 315 soon 440 free 316 body 441 minute 317 dog 442 strong 318 family 443 special 319 direct 444 mind 320 pose 445 behind 321 leave 446 clear 322 song 447 tail 323 measure 448 produce 324 state 449 fact 325 product 450 street 326 black 451 inch 327 short 452 lot 328 numeral 453 nothing 329 class 454 course 330 wind 455 stay 331 question 456 wheel 332 happen 457 full 333 complete 458 force 334 ship 459 blue 335 area 460 object 336 half 461 decide 337 rock 462 surface 338 order 463 deep 339 fire 464 moon 340 south 465 island 341 problem 466 foot 342 piece 467 yet 343 told 468 busy 344 knew 469 test 345 pass 470 record 346 farm 471 boat 347 top 472 common 348 whole 473 gold 349 king 474 possible 350 size 475 plane 351 heard 476 age 352 best 477 dry 353 hour 478 wonder 354 better 479 laugh 355 true . 480 thousand 356 during 481 ago 357 hundred 482 ran 358 am 483 check 359 remember 484 game 360 step 485 shape 361 early 486 yes 362 hold 487 hot 363 west 488 miss 364 ground 489 brought 365 interest 490 heat 366 reach 491 snow 367 fast 492 bed 368 five 493 bring 369 sing 494 sit 370 listen 495 perhaps 371 six 496 fill 372 table 497 east 373 travel 498 weight 374 less 499 language 375 morning 500 among ZIT LXF WXKFZ TCTKNRQN OZ WXKFZ ZODT ZIT VGKSR KXLITR OF Q EOKEST QFR ZXKFTR GF OZL QBOL QFR ZODT VQL WXLN WXKFOFU ZIT NTQKL QFR ZIT HTGHST QFNVQN VOZIGXZ QFN ITSH YKGD IOD LG OY IT WXKFZ ZIOFUL VOZI ZIT YOKTDTF QFR ZIT LXF WXKFZ ZODT ZIQZ DTQFZ ZIQZ TCTKNZIOFU WXKFZ WN KQN WKQRWXKN ZIT多次出现,THE 或are ,在句首。。猜THE the LXF WXKFt eCeKNRQN Ot WXKFt tODe the VGKSR KXLheR OF Q EOKESe QFR tXKFeR GF OtL QBOL QFR tODe VQL WXLN WXKFOFU the NeQKL QFR the HeGHSe QFNVQN VOthGXt QFN heSH YKGD hOD LG OY he WXKFt thOFUL VOth the YOKeDeF QFR the LXF WXKFt tODe thQt DeQFt thQt eCeKNthOFU WXKFt WN KQN WKQRWXKN thQt" -----------“Q”猜A the LXF WXKFt eCeKNRaN Ot WXKFt tODe the VGKSR KXLheR OF a EOKESe aFR tXKFeR GF OtL aBOL aFR tODe VaL WXLN WXKFOFU the NeaKL aFR the HeGHSe aFNVaN VOthGXt aFN heSH YKGD hOD LG OY he WXKFt thOFUL VOth the YOKeDeF aFR the LXF WXKFt tODe that DeaFt that eCeKNthOFU WXKFt WN KaN WKaRWXKN AFR多次出现,AND 或are , the NeaKL aFR the HeGHSe 应AND Deant” ------------------------- “meant”,D-------M the LXn WXKnt eCeKNdaN it WXKnt time the VGKSd KXLhed in a EiKESe and tXKned Gn itL aBiL and time VaL WXLN WXKninU the NeaKL and the HeGHSe anNVaN VithGXt anN heSH YKGm him LG iY he WXKnt thinUL Vith the YiKemen and the LXn WXKnt time that meant that eCeKNthinU WXKnt WN KaN WKadWXKN eCeKNthinU” -------“everything” or that “VithGXt” ----------- “without” the sun burnt everyday it burnt time the world rushed in a circle and turned on its axis and time was busy burning the years and the people anyway without any help from him so if he burnt things with the firemen and the sun burnt time that meant that everything burnt by ray bradbury 《华氏451》是一部典型的反乌托邦小说。华氏451度,也就是令纸张燃烧的温度,而小说中描写的人类社会,就是一个以消灭书籍作为发展停滞代表性作为的社会。Ray Bradbury 在《华氏451》反乌托邦作品典范的小说:《我们》,《美丽新世界》,《动物庄园》,《1984》,《华氏451》。可以的话,我还想加上《发条橙子》,以及《Brazil》 WIGUW WEYUP UKDGU BMEBP CHBVP VZOUG WNKZP VPFZC YJHGK WGDMX GSGBW FAVZU LFPVM VTGEK UCOGX LVGYC YIVTE DBTOM PPUNG EJCSV GPEAL FUGRR NGEWZ DCZYK WKPWV CSDKL OXHTQ OMNPU UQNJF DZAQW ULQOJ WXKTH XMGMO TNUKP FSLUJ MAWVK CTOVA PQFBM ICSGC RBYNH ZJXMT BUJIT MGDTQ WCEAC DIWDM EVTA 5字一组,但内容一样,对着 the sun burnt everyday it burnt time the world rushed in a circle and turned on its axis and time was busy burning the years and the people anyway without any help from him so if he burnt things with the firemen and the sun burnt time that meant that everything burnt by ray bradbury WIGUW WEYUP UKDGU BMEBP。。。。。。。。。 t he su nburn tev er ydayi。。。。。。。。。 上下按26字母序相减:大于13就-26 31222 92432 16823 39437。。。。。。。。。。 THESE MESSA GESTE LLYOU WHATT HECOD EWORD ISALL BUTON EGIVE SYOUT HREED IGITS THEFI RSTTW OAREC OORDI NATES OFWHE RETOP UTTHE THIRD INANI NEBYN INEGR IDWHE NYOUH AVEAL LSEVE NTEEN DIGIT SSOLV ETHES UDOKU THEEI GHTEE NTHAN SWERI SNINE LETTE RSWHI CHYOU USETO REPLA CEONE TONI 信息三比密匙长,从头再循环 THESE MESSAGES TELL YOU WHAT THE CODEWORD IS. ALL BUT ONE GIVES YOU THREE DIGITS. THE FIRST TWO ARE COORDINATES OF WHERE TO PUT THE THIRD IN A NINE BY NINE GRID. WHEN YOU HAVE ALL SEVENTEEN DIGITS, SOLVE THE SUDOKU. THE EIGHTEENTH ANSWER IS NINE LETTERS WHICH YOU USE TO REPLACE ONE TO NINE IN THE GRID. YOU WILL THEN SEE THE CODEWORD IN THE MIDDLE. "The author of that favourite novel of yours? Well he shares his surname with another who came from Sheffield and who wrote a novel set in a fictional seaside town that shares its name with a real one in Devon. That town has a castle that isn't a castle, and the architect of that worked with another architect in Plymouth and this second architect died on the same day that an author first gave a lecture on manners. He gave part seven of the series on the same day as someone else became famous for surviving. The husband of the artist who painted this event wrote the biography of a man who was killed in a battle that ended a war. The peace treaty was signed on the same day as two Nobel Laureates were born. The one of these who wasn't a writer was born in a town where a famous conference took place and the man who presided over this had been crowned king only recently in a cathedral that was built by, and is the resting place of, a man who was the son of a king who made a famous gift. When was that?" 你喜爱的小说的作者,他与另一位来自谢菲尔德和写在一个虚构的海滨小镇,与它的名字在德文郡的一个真实的一种新型他的姓,这城里有城堡,ISN'T一座城堡,和建筑师,与其他建筑师在普利茅斯,这第二个建筑师工作死在同一天,一个作者首先介绍了关于礼仪的讲座系列7部分,在同一天,他给别人成为尚存的著名艺术家的丈夫是谁画的这个事件写了一个谁是在一次战斗中,结束了战争中丧生的人的传记。两个诺贝尔奖获得者出生在同一天签署的和平条约。其中之一谁没有一个作家是其中一个著名的会议和主持的人在这个地方已经在建大教堂加冕国王最近才在一个小镇出生,是休息的地方,一个人谁是一个国王,他提出了著名的礼物的儿子是什么时候吗 丕平(Pippin,714年-768年9月24日),又称丕平三世(Pepin III),矮子丕平(Pepin the Short),是公元751至768年在位的法兰克国王,是查理曼大帝的父亲,加洛林王朝的创建者。 丕平更是竭力谋求同教会和教皇的友好关系。753年,罗马教皇受到伦巴底国王的威胁,派人向丕平求救。754、756年丕平两次出兵意大利,打败了伦巴底人,将从伦巴底王国夺来的意大利中部地区赠给罗马教皇。这一赠礼,奠定了世俗教皇国的基础,史称“丕平献土”。由丕平巩固起来的这种政教合作关系,在他的儿子查理曼手中得到了更进一步的发展。 Songs Of Queen 中文名称:Songs Of Queen 别名:Gregorian Chants 资源类型:MP3! 发行时间:2000年 专辑歌手:Auscultate 地区:英国 语言:英语 简介: 专辑介绍: 稍微介绍一下这个系列的专集,这一套由Auscultate演唱的Gregorian Chants系列[Gregorian Chants Performed By Avsculate]一共八张(Songs Of The Beatles,Songs Of Celine Dion,Love Songs,Rock Ballads,Songs Of Queen,Songs Of Simon & Garfunkel,Rock Anthems ,Love Ballads)是由Avscvltate吸取流行音乐的元素,结合宗教圣咏的方式,将流行音乐进行重新制作的专集,外面很少见,想来一方面除了有继续延伸或者传播这种古老的音乐方式外,还有渐渐与潮流靠拢的倾向,而作为宗教歌曲的某些特性与newage似乎不谋而合,所以随处可见newage的点点融合在音乐中…… 本张专辑均为皇后乐队的经典名曲。 歌剧院之夜A Night At The Opera Songs Of Queen 中文名称:Songs Of Queen 别名:Gregorian Chants 资源类型:MP3! 发行时间:2000年 专辑歌手:Auscultate 地区:英国 语言:英语 简介: 专辑介绍: 稍微介绍一下这个系列的专集,这一套由Auscultate演唱的Gregorian Chants系列[Gregorian Chants Performed By Avsculate]一共八张(Songs Of The Beatles,Songs Of Celine Dion,Love Songs,Rock Ballads,Songs Of Queen,Songs Of Simon & Garfunkel,Rock Anthems ,Love Ballads)是由Avscvltate吸取流行音乐的元素,结合宗教圣咏的方式,将流行音乐进行重新制作的专集,外面很少见,想来一方面除了有继续延伸或者传播这种古老的音乐方式外,还有渐渐与潮流靠拢的倾向,而作为宗教歌曲的某些特性与newage似乎不谋而合,所以随处可见newage的点点融合在音乐中…… 本张专辑均为皇后乐队的经典名曲。 歌剧院之夜A Night At The Opera The Supremacy of THE BOURNE SUPREMACY 《谍影重重II:伯恩的霸权》 英国地名 ANGLESEY 音乐Life of Riley Season 安逸生活 音乐 » A Head of Steam FRONT of HOUSE Magazine (abbreviated FOH) is a worldwide news service for live audio professionals. Published by Timeless Communications, Corp a Nevada corporation. Tim Koch – Seven Ate Nine (3:03) 谷安格爾西鎮 器官氬元素 離子堡壘埃及 HERB班納特花 拖走賦予埃及 返回別樣的X Ÿ 賽自行車女皇 語言機構皇后 RHAPSODY波希米亞女皇 至上BOURNE三部曲 毒蛇牛舌草花 蛋糕X片的Y MISCUE銫元素(變種拼寫) 甜CICELLY花 宿舍關閉三部曲 玉米拾貝花 港CORNWALL鎮 啟動坎布里亞郡鎮 阿比DEVON鎮 銀行英格蘭的X Ÿ 北GLEAM三部曲 火星綠色三部曲“ 自HEAL花 前置樓的X Ÿ 天獨三部曲 新政建德城市 皇后殺手皇后 處理鉛元素 麝香錦葵花 使用減號埃及 無 NEON元 700 9 Y X 方法NUTTIER埃及 視覺一張大號 靜脈貪婪的埃及 裝飾氡元素 雪茄盒銠元素 生活RILEY的X Ÿ 衣衫襤褸的羅賓花 我保存皇后 ATE穩重埃及 TEE的沙發埃及 EDGE什羅普郡鎮 肝臟銀元素 井SOMERSET城市 頭的Y蒸汽X 刀微妙的三部曲 塔雙三部曲 壓力下皇后  |
|
|
[推荐]英国情报机构GCHQ推出“破密码招特工”活动
Part TWO: 日本数独?-------------4+1+2+1 1+2+2 3+2+1+3---------------8 5 9 就能一个American born author who became British -------HENRY JAMES 亨利·詹姆斯(Henry James, 1843年4月15日- 1916年2月28日、享年73岁),英国-美国作家。 姓名接龙--------PENELOPE KEITH--------KEITH JOSEPH--------------JOSEPH CONRAD--------CONRAD BLACK----------。。。。。。。。。。 有向图 EASIEST + RESTARTS + TERSEST = LINGERER 5914513 + 75139731 + 3571513 = 84625757 T+S+T=R S+T+S=E 或 E+1 E+R+E=R 或 R+1 I+A+S=E或 E+1 ..... .........  |
|
|
[推荐]英国情报机构GCHQ推出“破密码招特工”活动
Answers to the 2011 GCHQ Challenge Part One: From the east comes a family member Oriental Relation Smooth peaches have briefness Nectarine Transience Grave messages are the most cheerful Epitaphs Happiest To disturb leads to being peaceful Fluster Restful Excessive suaveness causes omissions Oiliness Elisions Being dismounted results in preparation for burial Unhorsed Enshroud GOOGLE。COM 来自东方的家庭成员 东方的关系 光滑的桃子有短促 油桃顷刻 严重的消息是最开朗 墓志铭最幸福 扰乱,导致被和平 慌乱的RESTful 过度suaveness原因遗漏 含油Elisions 作为卸除准备殓葬 Unhorsed覆盖 各挑第一个字母--------ONE FOUR THREE---------------143 Aire and the Leeds & Liverpool Canal. 艾尔和利兹利物浦运河。 George Orwell 1984 real name Eric Blair Wigan码头 If Paul Weller is recording at 2A Stanley Road Changeline Bridge No 2A molesworths friend (his pater is a general) is at 40 Gillibrand Bridge No 40 Blair's road finishes between 50 and 51 Wigan Pier is between Seven Stars Bridge No 50 & Pottery Changeline Bridge No 51 a great physicist is at 164 Newton Bridge No 164 an adjacent equine is at 180 Horse Close Bridge No 180 200 is 2 more than 201 Five Rise Locks Swing Bridge No 200 and Three Rise Locks Swing Bridge No 201 Titus' world heritage site is at 207A Saltaire Bridge No 207A where is Lanehouse (it moves)? Lanehouse Swing Bridge is Bridge 189 如果保罗韦勒是记录在2A 赤柱路Changeline桥无2A molesworths朋友(他的佩特是一个普遍的)是在40 Gillibrand桥40号 布莱尔的道路,完成50和51之间 Wigan码头之间的七星桥50陶器Changeline大桥51 一个伟大的物理学家是在164 牛顿桥无164 相邻的马是在180 关闭马大桥没有180 200是比201多2 五上升锁秋千桥200和三上升锁秋千桥无201 提图斯“世界遗产在207A Saltaire桥无207A 在哪里Lanehouse(移动)? Lanehouse秋千桥是桥189------------------ “Whiten largest Egyptian ruler; finely chop temporary bidirectional bleach biggest pharaoh mince interim twoway amphibian apeman; ground (scottish equipment) mathematician, newt yeti earth graith godel architrave, frieze and cornice.” entablature “洗白最大的埃及统治者;切碎临时双向 漂白剂最大的法老讳言中期双向 两栖动物apeman;地面(苏格兰设备)的数学家, 蝾螈雪人地球graith哥德尔 楣梁,楣和挑檐。“ entablature 数学家GODEL/TWOWAY 好认 143 429 还有可能,189桥对利物埔运河不熟的没戏--------GOOGLE---MAP http://www.geograph.org.uk/mapper/?t=tolJ5oOXXJ0oOXJFoOXXJfobXNJqoOOXJL5405oXtu4VVNVwbujXZtu&gridref_from=SE0245¢i=1 http://www.canalplan.org.uk/waterway/71jn  |
|
|
[求助]密钥容器安全
---- BEGIN SSH2 PUBLIC KEY ---- Comment: "rsa-key-20111207" AAAAB3NzaC1yc2EAAAABJQAAACEAsL2MwYNNi2zvzqgSaeN2dEys2V9ifJxXaK8I CqpUPwM= ---- END SSH2 PUBLIC KEY ---- PuTTY-User-Key-File-2: ssh-rsa Encryption: none Comment: rsa-key-20111207 Public-Lines: 2 AAAAB3NzaC1yc2EAAAABJQAAACEAsL2MwYNNi2zvzqgSaeN2dEys2V9ifJxXaK8I CqpUPwM= Private-Lines: 3 AAAAIHwyK47mpTGK0gbW+C67g6p93mECwbHBQnNmoqhXi/YdAAAAEQDzN7cbNn3s iNkcBkKEqek1AAAAEQC6B3DT8PfhtOtZkHYfO8ZXAAAAEB0gdB9YC4PISop1Ip4W 77A= Private-MAC: 1f9deb2efa8505c6ef3b3ba3ac291f1b796759c4 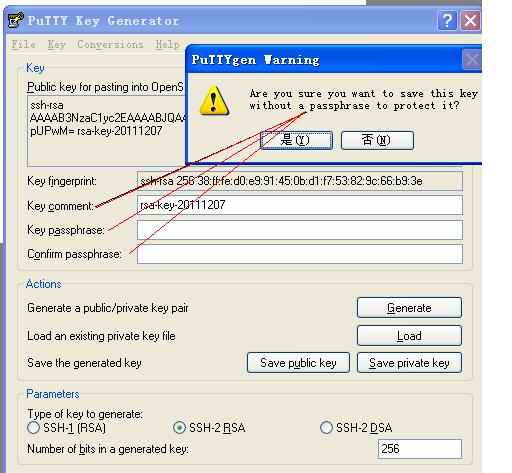 |
|
|
[求助]密钥容器安全
openssh/OOENSSL文挡:应该都是软硬件产生随机数参盐等:私匙再怎麽层层加密,最后总要主人用自己的一些特征去先取得私匙,假定私匙被主人用5个不同特征加密,同态加密就想主人只用1个(或2-4个)特征去解密,这时解密的私匙还是4个特征加密,保险多了,这种4个特征加密私匙数据还保同态映射----RSA DH两种同态映射2009年被发现,不太难懂 D:\OpenSSH\bin>ssh-keygen --help ssh-keygen: unknown option -- - Usage: ssh-keygen [options] Options: -b bits Number of bits in the key to create. -c Change comment in private and public key files. -e Convert OpenSSH to IETF SECSH key file. -f filename Filename of the key file. -g Use generic DNS resource record format. -i Convert IETF SECSH to OpenSSH key file. -l Show fingerprint of key file. -p Change passphrase of private key file. -q Quiet. -y Read private key file and print public key. -t type Specify type of key to create. -B Show bubblebabble digest of key file. -C comment Provide new comment. -N phrase Provide new passphrase. -P phrase Provide old passphrase. -r hostname Print DNS resource record. -G file Generate candidates for DH-GEX moduli -T file Screen candidates for DH-GEX moduli D:\OpenSSH\bin>ssh-keygen -t rsa Generating public/private rsa key pair. Enter file in which to save the key (/cygdrive/c/Documents and Settings/Administ rator/.ssh/id_rsa): OPENSSL OPENSSH OpenSSL> dsaparam -genkey -text 123.txt -outform PEM Loading 'screen' into random state - done Generating DSA parameters, 123 bit long prime This could take some time ......+.......+.+......+......................+.+......................+........ ..+.+..............+++++++++++++++++++++++++++++++++++++++++++++++++++* .....+..........+....+.......................................................... ...+...+....................+...+.....+........+.........+................+....+ ......+++++++++++++++++++++++++++++++++++++++++++++++++++* DSA-Parameters: (512 bit) p: 00:ca:10:54:1b:5d:fc:78:cc:7c:bd:a6:7d:2d:a1: 6b:67:12:c3:23:c0:56:93:71:8b:a7:54:84:a4:85: df:0f:46:63:e5:6d:4c:94:d1:f6:32:02:36:04:b8: 88:a6:dc:db:56:f3:6b:92:7d:34:4e:af:ff:a6:5a: d6:38:93:b8:e7 q: 00:e2:31:06:81:e5:80:32:d6:a6:86:9b:e9:2f:41: 65:9d:7e:6a:a7:1f g: 14:54:3a:94:70:42:58:fa:95:20:c9:c9:4f:4a:dc: 6d:dc:41:e2:b0:8e:10:c5:68:8d:a9:aa:c0:27:39: c4:e3:76:54:b9:7b:54:4a:ea:d6:dd:41:06:dd:63: 6f:07:84:56:7c:45:b0:c6:a2:9d:37:e8:62:12:f7: 23:29:ac:e6 -----BEGIN DSA PARAMETERS----- MIGcAkEAyhBUG138eMx8vaZ9LaFrZxLDI8BWk3GLp1SEpIXfD0Zj5W1MlNH2MgI2 BLiIptzbVvNrkn00Tq//plrWOJO45wIVAOIxBoHlgDLWpoab6S9BZZ1+aqcfAkAU VDqUcEJY+pUgyclPStxt3EHisI4QxWiNqarAJznE43ZUuXtUSurW3UEG3WNvB4RW fEWwxqKdN+hiEvcjKazm -----END DSA PARAMETERS----- -----BEGIN DSA PRIVATE KEY----- MIH3AgEAAkEAyhBUG138eMx8vaZ9LaFrZxLDI8BWk3GLp1SEpIXfD0Zj5W1MlNH2 MgI2BLiIptzbVvNrkn00Tq//plrWOJO45wIVAOIxBoHlgDLWpoab6S9BZZ1+aqcf AkAUVDqUcEJY+pUgyclPStxt3EHisI4QxWiNqarAJznE43ZUuXtUSurW3UEG3WNv B4RWfEWwxqKdN+hiEvcjKazmAkA1MwoGXnfEXM0kS+b49MV/hp8CR6ZgBQZ7wmCk k6nkAp4bEmqaLXzvljeP5GlK3osREOZ1UZ6O1nm0d6mjQL6pAhR4h+3jPizhUPTJ Hakn9Eb5s+xaVQ== -----END DSA PRIVATE KEY----- -out file - output the key to 'file' -des - encrypt the generated key with DES in cbc mode -des3 - encrypt the generated key with DES in ede cbc mode (168 bit key) -idea - encrypt the generated key with IDEA in cbc mode -aes128, -aes192, -aes256 encrypt PEM output with cbc aes -engine e - use engine e, possibly a hardware device. -rand file;file;... - load the file (or the files in the directory) into the random number generatordsaparam-file - a DSA parameter file as generated by the dsaparam command |
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值


