|
|
|
|
|
[原创]PEInfo_v0.04 开源
不好意思,文档真没有,原来只是想练练手的。 |
|
|
|
|
|
|
|
|
[原创]PEInfo_v0.04 开源
[QUOTE=xnop;1078849]少了个头文件: ProcessManager.h pPack_Imp_Desc[i].pFirstThunk[j].Thunk_Data.u1.Function = (ULONG ×)m_pPeFile->OffsetToRva cannot convert from 'unsigned lon...[/QUOTE] 需要行编译ProcessManager工程,再编译CommonControls,最后再编译PEInfo工程即可。 ProcessManager工程本来是想做个进程外组件以供调用的,但是还存在些问题,暂时没用。 用VC6.0 + sp6编译的。 |
|
|
[原创]PEInfo_v0.04 开源
“痴心绝对X.txt是用来做字幕玩的 符号配置文件只是想有这么个功能。 mfc80,mfc80D,mfc90,mfc90D,mfc10,mfc10D的符号配置文件,你有吗? 提供一份 |
|
|
|
|
|
[原创]PEInfo模拟版 v0.04
代码比较乱,整理下,以后开源。 |
|
|
[原创]PEInfo模拟版 v0.03
写程序时一直用的debug版,release没怎么测试,崩在了mfc42.dll中。谢谢你的反馈! |
|
|
[原创]PEInfo模拟版 v0.03
发现了xp下PETools v1.5.600.2005 下进程解析的bug LordPE v1.4 与本系统解析的系统进程名为空的进程 其中ImageBase、ImageSize均为00000000,而PETools v1.5.600.2005所获同PID进程的ImageBase、ImageSize与上个进程相同 |
|
|
[讨论]如何检测一个字符中 是否有乱码 VC++ 代码
下面的代码只可以处理ascii或unicode 西文字符 摘自PEInfo模拟版V0.03 我是这样处理的:
int j=0;
byte *pTempByte = pByte;
while( !( *pTempByte==NULL && *(pTempByte+1)==NULL ) )
{
pTempByte++;
}
j = pTempByte - pByte;
if( j==0 )//二进制
{
SetRelcationSectionItemDetailData(i,pByte);
}
else
{
if( j%2==1 )//为UNICODE凑为字节双数
j++;
if( IsTextUnicode(pByte,j,NULL) )
{
UINT strSize = wcslen((LPWSTR)pByte);
LPSTR pAnsiStr = UnicodeToAnsi((LPWSTR)pByte);
if( pAnsiStr )
{
if( ByteIsCanView((wchar_t *)pByte) )
{
if( ByteIsCanView((byte *)pAnsiStr) )//首字节在此范围内才显示ascii(只支持西文)
{
s.Format("%s (Unicode string) %dbytes",pAnsiStr,strSize*2);
pRelcationSectionItemList->SetItemText(i,5,s);
TRACE("%s\n",s);
delete pAnsiStr;
}
}
else
{
SetRelcationSectionItemDetailData(i,pByte);
}
}
else
{
SetRelcationSectionItemDetailData(i,pByte);
}
}
else
{
if( ByteIsCanView(pByte) )//首字节在此范围内才显示ascii(只支持西文)
{
s.Format("%s (string) %dbytes",pByte,strlen((char*)pByte));
pRelcationSectionItemList->SetItemText(i,5,s);
TRACE("%s\n",s);
}
else
{
SetRelcationSectionItemDetailData(i,pByte);
}
}
}
LPSTR UnicodeToAnsi(LPWSTR lpszWideStr)
{
BOOL bUsed;
LPSTR lpAnsiStr;
if (lpszWideStr)
{
int len = WideCharToMultiByte(CP_ACP, 0, lpszWideStr, -1, NULL, 0,NULL, &bUsed);
if (len == 0)
return NULL;
lpAnsiStr = new char[len + 1];
if (lpAnsiStr == NULL)
return NULL;
if (WideCharToMultiByte(CP_ACP, 0, lpszWideStr, -1, lpAnsiStr, len,NULL, &bUsed))
return lpAnsiStr;
}
return NULL;
}
template<class T>
bool ByteIsCanView(T *pStr)
{
if( *pStr==0 )
return false;
while(*pStr)
{
if( !((*pStr>=T(0x20)) && (*pStr<=T(0x7E))) )
return false;
pStr++;
}
return true;
}
void CPE_Relocation::SetRelcationSectionItemDetailData(int index,byte *pByte)
{
CString str;
str.Format("%02X %02X %02X %02X %02X %02X %02X %02X %02X %02X",
*pByte,*(pByte+1),*(pByte+2),*(pByte+3),*(pByte+4),*(pByte+5),
*(pByte+6),*(pByte+7),*(pByte+8),*(pByte+9));
pRelcationSectionItemList->SetItemText(index,5,str);
//CListCtrl
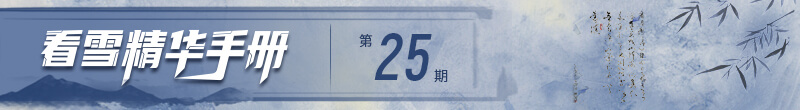
}以下是PEInfo模拟版重定位表字符显示示例 LordPE v1.4只显示10个字符(ascii or unicode) 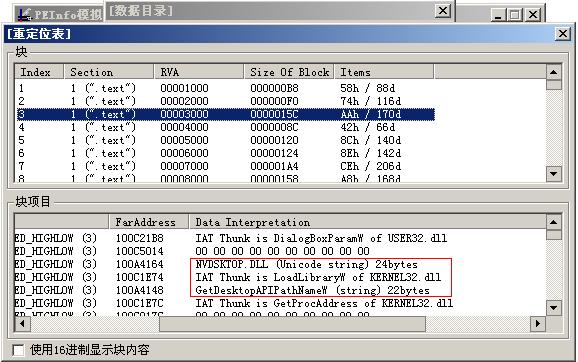  |
|
|
[原创]c32asm动态连接库解析配置文件及更新工具
压缩包内的INI文件倒是不错,原来手里的还都是C++编码过的函数名,谢谢分享! |
|
|
[原创]PEInfo模拟版V0.02
只找到这篇 转自vcer.net by windy 我们只要知道PE的入口点地址.就可以进行匹配,我以经用它做了一个像stud_PE那样能检测PE文件外壳信息的程序,能有效检测170多种 //定义特征码结构体 ///////////////////////////////////////////////////////////////////////////// typedef struct _Feature { public: LPCTSTR Pos; //相对于入口点的偏移 LPCTSTR Fea; //特征码 LPCTSTR Info; //壳信息 bool IsOrdered; //是否是顺序的. }Feature,*PFeature; Feature g_ShellInfoTab[] = { {"01020304050607090B0C","8B4424085683E8744875","Microsoft Visual C++ Private Version 2",0}, {"010203040508","8B4424088374","Microsoft Visual C++ Private Version 1",0}, {"0102030408090D","6A00FF1500A300","FASM 1.3x",0}, {"01020307080C","6A00E800A300","MASM32 / TASM32",0}, {"0102030405060708090E0F10111213","558BEC83EC4456FF156A018BF0FF15","Microsoft Visual C++ 6.0 SPx Method 2",0}, {"0102030405060708090E0F101213","558BEC83EC4456FF158BF08A3C22","Microsoft Visual C++ 6.0 SPx Method 1",0}, {"010203040708090A0B0C0D0E15161718191A1B1C1D1E1F20","EB16A8544741424C4B43474352495300FC684C704000FF15","WARNING -> VIRUS -> I-Worm HYBRIS",0}, {"010203040506070809","60E8000000005DEB26","PE-Crypter -> Zero Coder",0}, {"0102030405121314151617181D1E1F","E912000000E9FBFFFFFFC36864FF35","ZCode 1.01 -> Giuliano Bertoletti",0}, {"0102030405060708090E11121314191A1B","60E8000000005D81EDB900008DBD8BF7AC","yoda's cryptor 1.x / modified",0}, {"0102030C0D0E0F1415161B1C1D222324252628292A2B2C2D2E2F34353A3B3C3D424344","9371088BD878E29C33C36079CEE80100000083C404E8ABFFFFFF2BE803C5FF30C600EB","XCR 0.13 -> X-Lock",0}, {"0102030405060708090A0B0C1112","609CE8000000008BDD5D81ED899D","XCR 0.12 -> X-Lock",0}, {"0102030405060708090B0C0D0E0F101112131415161718191A1B1C1D1E1F2021222324252628292A2B","558BEC83EC4456FF151000018BF08A063C2275148A46014684C074043C2275F4803E22750DEB0A3C20","Microsoft CAB SFX module",0}, {"0102030708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F202122232425262728292E2F","53FF1500B3223818740380C3FE8A48014033D23ACA740A3ACB74068A480140EBF23810740140FF15","WinZip 32-bit SFX 8.x module",0}, {"0102060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F202122232425262B2C","FF1500B12238087402B120408038007410380874064080380075F680380074014033C9FF15","WinZip 32-bit SFX 6.x module",0}, {"0102030405090A0B0F101112131415161718191A1B1C1D1E1F202122232425262728","33C08BB8008B900485FF741B33C950EB0C8A0439C0C804341B880439413BCA72F058","Winkript 1.0 -> Mr. Crimson/WKT",0}, {"01060B0C0D0E0F101112131415161718191A1B1C1D1E1F2021","B8B933D2EB010F56EB010FE803000000EB010FEB010F5EEB01","UPX + ECLiPSE layer -> TEAM ECLiPSE",0}, {"0102030405060708090A0B0C0D0E0F1011131415161718191A1B1C1D1E1F202122242526272B","79070FB707475047B95748F2AE55FF9684000009C07407890383C304EBD8FF9688000061E9FF","UPX modified stub -> SAC/uNPACKinG gODS",0}, {"01020405060708090A0B0C0D0F1011121314151618191A1B1C1D1E1F202122232425","01DB078B1E83EEFC11DB8A07EBB80100000001DB078B1E83EEFC11DB11C001DB73EF","UPX 1.03 - 1.04 modified -> Markus & Lazlo",0}, {"01020405060708090A0B0D0E0F1011121314161718191A1B1C1D1E1F20212224","01DB078B1E83EEFC11DBEDB80100000001DB078B1E83EEFC11DB11C001DB7375","UPX 0.89.6 - 1.02 / 1.05 - 1.22 modified -> Markus & Lazlo",0}, {"01020405060708090A0B0D0E0F1011121314161718191A1B1C1D1E1F20212223","01DB078B1E83EEFC11DBEDB80100000001DB078B1E83EEFC11DB11C001DB77EF","UPX 0.81 - 0.84 modified -> Markus & Lazlo",0}, {"010207080D0E1718191A1B1C2122232425262728292A2B","60BE8DBEC7875783CDFFEB0E8A064688074701DB75078B","UPX 0.89.6 - 1.02 / 1.05 - 1.22 (Delphi) stub -> Markus & Lazlo",0}, {"191A1B1C1D1E1F202122232425262728292A2B2C2D2E2F303132333435363738393A3B3C3D3E3F40414244464748494A","8A064688074701DB75078B1E83EEFC11DB8A0772EBB80100000001DB75078B1E83EEFC11DB11C001DB73758B1E83EEFC","UPX 1.03 - 1.04 -> Markus & Lazlo",0}, {"191A1B1C1D1E1F202122232425262728292A2B2C2D3132333435363738393A3B3C3D3E3F40424445464748","8A064688074701DB75078B1E83EEFC11DB72EDB80101DB75078B1E83EEFC11DB11C001DB73758B1E83EEFC","UPX 0.89.6 - 1.02 / 1.05 - 1.22 -> Markus & Lazlo",0}, {"191A1B1C1D1E1F202122232425262728292A2B2C2D3132333435363738393A3B3C3D3E3F404142434445464748","8A064688074701DB75078B1E83EEFC11DB72EDB80101DB75078B1E83EEFC11DB11C001DB77EF75098B1E83EEFC","UPX 0.80 - 0.84 -> Markus & Lazlo",0}, {"010203040506070B0C0D121318191A1B","807C2408010F850060BE8DBE5783CDFF","UPX 0.89.6 - 1.02 / 1.05 - 1.22 DLL -> Markus & Lazlo",0}, {"01020708090A0B0C0D0E0F10","EBEC8A064688074701DB7507","UPX Protector 1.0x -> BlindAngel/TMG",0}, {"010207080D0E0F","50BE8DBE5783CD","UPX MODifier 0.1x -> snaker",0}, {"01020308090E0F1011","9061BE8DBE5783CDFF","UPX-Scrambler RC1.x -> ",0}, {"0102030405060708090A0B0C0D0E0F12131415161D1E1F202324292A2B2C2D2E2F303132","60E80000000083CDFF31DB5E8DBEFAFF5766818781C6B301EB0A8A064688074701DB7507","UPX 0.71 - 0.72 -> Markus & Lazlo",0}, {"0102030405060708090A0B0C0D11121314151C1D1E1F22232425262728292A2B2C2D2E2F30313233","60E8000000005883E83D508DB8FF576681878DB0EC0183CDFF31DBEB07908A064688074701DB7507","UPX 0.70 -> Markus & Lazlo",0}, {"0102030405060708090A0B0C0D11121314151C1D1E1F22232425262728292A2B2C2D2E2F3031323334353637","60E8000000005883E83D508DB8FF576681878DB0F00183CDFF31DB909090EB0890908A064688074701DB7507","UPX 0.62 -> Markus & Lazlo",0}, {"0102030405060708090A0B0C0D111213141516191A1B1C1D22232425262728292A2B2C2D2E2F3031323334353637","60E8000000005883E83D508DB8FF578DB0D80183CDFF31DB01DB75078B1E83EEFC11DB730B8A0646880747EBEB90","UPX 0.51 -> Markus & Lazlo",0}, {"010203040510131C","E97EE9FFFFC80018","tElock 0.92 -> tE!",0}, {"030405060708090A0B0C0F101112131415161718191A","E802000000E800E800005E2BC9587402CD20B9FF1000","tElock 0.90 -> tE!",0}, {"010205060708","60E80000C383","tElock 0.7x - 0.84 -> tE!",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F202122232425262728292A2B2C2D2E2F30","E90000000060E8000000005883C008F3EBFFE083C02850E8000000005EB3338D460E8D76312818F87300C38BFEB9BE01","tElock 0.60 -> tE!tElock 0.61 -> tE!tElock 0.6x -> tE!tElock 0.70 -> tE!",0}, {"0102030405060708090A0B0C0D0E0F1011121314151618191A1B1C1F2021","C1EE00668BC9EB01EB60EB01EB9CE8000000005E83C68BFE68790159EB01","tElock 0.4x - 0.5x -> tE!",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1F202122232425262A2B2C","668BC08D2424EB01EB60EB01EB9CE8000000005E83C6508BFE68780159EB01EBAC54E8035CEB08","tElock 0.41x -> tE!",0}, {"01020308090A0B0C0D10111215161718191A1F202122232425262728292A2B","648B05558BEC6AFF6840006840005064892583EC08505356578965E8C745FC","Symantec Visual Cafe 3.0",0}, {"0102030405060708090A0B0C0D0E0F10111314151617191A1B1C1E1F2021222324262728292A2C","535152565755E8000000005D81ED423040FF95323540B837304003C52B851B3440898527344083","Stone's PE Encryptor 2.0",0}, {"0102030405060708090A0B0C0D0E0F1011121315161718191B1C1D1E1F20212224252627282A2B2C","555756525153E8000000005D8BD581ED633A402B95C23A4083EA0B8995CB3A408DB5CA3A400FB636","Stone's PE Encryptor 1.0",0}, {"0102030405060708090A0B0C0D0E131415161718191A1B1C","9C608B442424E8000000005D81ED50E8ED0200008CC00F84","Spalsher 1.0 - 3.0 Tola/Amok",0}, {"010206070B0C0D0E0F10121314151617191A","60B800B8008A140880F28814084183F975F1","SmokesCrypt 1.2 -> Smoke",0}, {"01020308090A0B0C0D0E0F1011121314161718191A1B1C1D1E1F202425262728292A2B2C2D2E2F","833DB4558BEC5657756B6800010000E80B000083C4048B7508A3B485F67423837D0C03771D68FF","Shrinker 3.4 -> Blink Inc.",0}, {"0102060708090A0B0C0D0E0F1011121314","833D0000558BEC565775656800010000E8","Shrinker 3.3 -> Blink Inc.",0}, {"010208090A0B0C0D0E0F101114161718191A1B1C1D1E1F242526272829","833D558BEC56577565680001E8E6FFFF83C4048B7508A385F6741D68FF","Shrinker 3.2 -> Blink Inc.",0}, {"0102030405060708090A0B0C0D0E0F1011121315161718191B1C1D1E1F2021222425262728292A2B2C","5B535045435DE8000000005D8BC581ED4124402B8589264083E80B89858D26400FB6B5912640008BFD","SPEC b3 -> Hayras",0}, {"0102030405060708090A0B0C0D0E1314191A1B1C1D2223","55575153E8000000005D8BC581ED2B8583E80989850FB6","SPEC b2 -> Hayras",0}, {"0102030405060708090A0C0D0E0F10111213141516","4020FF00000000000000BE006040008DBE00B0FFFF","RatPacker (glue) stub",0}, {"01020304090A0B0C0D0E0F101112131415161718191A1B1C1D1E","558BECA185C07409B8010000005DC20C008B450C5756538B5D10","PKLITE32 1.1 -> PKWARE Inc.",0}, {"01020304050608090A0B0C0D0E0F1112","60E80100000083C404E8010000005D81","PEX 0.99 -> baRT^CrackPl",0}, {"01060B0C0D0E0F101112131415161718191A1B1C","B86864FF350000000064892500000000669C6050","PEtite 2.2 -> Ian Luck",0}, {"010607080D0E0F101112131415161718191A1B1C1D1E","B86A006864FF350000000064892500000000669C6050","PEtite 2.1 -> Ian Luck",0}, {"01060708090A0B0C0E0F10131415161718191A1B1C1D20212223242528","B8669C60508BD8036854BC6A00FF50188BCC8DA054BC8BC38D90E01568","PEtite 2.0 -> Ian Luck",0}, {"060708090A0B0C0D0E0F10111213141516171819","669C60508BD803006854BC00006A00FF50148BCC","PEtite 1.4 -> Ian Luck",0}, {"01060B0C0D0E0F1011131415161A","B8B983F9007E06803040E2F5E9FF","PEShit -> snaker",0}, {"060708090A0B0C0D0E0F101112131415161718191A1F20212223242526272829","669C60508D8800F000008D90041600008BDC8BE1685350800424085080042442","PEtite 1.3 -> Ian Luck",0}, {"01020304051C1D1E1F2021","E800000000B91B010000D1","PESHiELD 0.1b MTE -> ANAKiN",0}, {"01020308090A0B","7400E900000000","PE Pack 1.0 -> ANAKiN",0}, {"0102030405060708090A0B0C0D0E131415161719","525155576467A1300085C0780DE85883C007C6C3","PE Protect 0.9 -> Christoph Gabler",0}, {"0102030405060708090A0B0C0D0E0F101112131415161B1C1D1E1F20212224252627282A2B2C2D2E3031","E8040000008BEC5DC333C05D8BFD81ED3326400081EF83EF0589AD8827408D9D0729408DB56228404680","PE Password 0.2 SMT/SMF",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F20212223","5D8BC581EDB22C40002B85943E40002D710200008985983E40000FB6B59C3E40008BFD","PENinja modified -> +DZA",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F2021222324","909090909090909090909090909090909090909090909090909090909090909090909090","PENinja -> +DZA Kracker/TNT!",0}, {"01020708090A0B0C0D0E0F10111213141516","60E9EF4003A7078F071C375D43A704B92C3A","PENightMare 2 Beta -> FreddyK",0}, {"01020304050607080D0E0F101112","60E8000000005DB98031154181F9","PENightMare 1.3 -> FreddyK",0}, {"0105060708","E900F00FC6","PEncrypt 3.1 -> junkcode",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1F20212223","E8000000005D81ED051040008DB5241040008BFEB90F000000BBAD33C3E2FA","PEncrypt 3.0 -> junkcode",0}, {"01020308090A0F10111213141516","609CBE8BFEB9BB44524F4CAD33C3","PEMangle -> Lord Julus",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C","EB03CD20C71EEB03CD20EA9CEB02EB01EB01EB60EB03CD20EBEB01EB","PE Lock NT 2.04 -> :MARQUiS:",0}, {"01020308090A0B0C0D0E0F101112131415161718191A1B1C1D1E222324","9C60BD01AD543A4000FFB5503A40006A40FF95883A400050502D008985","PC Shrinker 0.71 -> Virogen",0}, {"020708090A0B0C0D0E0F1011","BD01AD553940008DB5353940","PC Shrinker 0.29 -> Virogen",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E","5D8BD581EDA23040002B959133400081EA0B00000089959A33400080BD99","PEDiminisher 0.1 -> Teraphy",0}, {"01020308090A0B0C101112131415161718191A1B1C1D","EB0668C39C60E80233C08BC483C004938BE38B5BFC81","PECompact 1.4x or above -> Jeremy Collake",0}, {"01020308090A0B0C101112131415161718191A1B1C1D1E1F2021232425262728292B2C2D2E2F313233353638393A3B3C3D3E4041424344464748494A4C4D4E","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB3F904087DD8B85E69040018533904066C785904090900185DA90400185DE90400185E29040BB5B11","PECompact 1.66 -> Jeremy Collake",0}, {"01020308090A0B0C101112131415161718191A1B1C1D1E1F2021232425262728292B2C2D2E2F31323334353638393A3B3C3D3E404142","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F804087DD8B85A68040018503804066C785008040909001859E8040BBE80E","PECompact 1.33 -> Jeremy Collake",0}, {"01020308090A0B0C101112131415161718191A1B1C1D1E1F2021232425262728292B2C2D2E2F313233353638393A3B3C3D3E404142","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F704087DD8B85A67040018503704066C7857040909001859E7040BBF308","PECompact 1.22 -> Jeremy Collake",0}, {"01020308090A0B0C101112131415161718191A1B1C1D1E1F202123242526272829","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F704087DD8B859A7040","PECompact 1.20 - 1.20.1 -> Jeremy Collake",0}, {"01020308090A0B0C101112131415161718191A1B1C1D1E1F2021232425262728292B2C2D2E2F313233353638393A3B3C3D3E4041","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F604087DD8B859A6040018503604066C785604090900185926040BB14","PECompact 1.10b7 -> Jeremy Collake",0}, {"01020308090A0B0C101112131415161718191A1B1C1D1E1F2022232425262728292B2C2D2E2F313233353638393A3B3C3D3E4041","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F600087DD8B859A6040018503604066C785604090900185926040BBB7","PECompact 1.10b6 -> Jeremy Collake",0}, {"01020308090A0B0C101112131415161718191A1B1C1D1E1F2021232425262728292B2C2D2E2F313233353638393A3B","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F604087DD8B85956040018503604066C78560409090BB95","PECompact 1.10b3 -> Jeremy Collake",0}, {"01020308090A0B0C101112131415161718191A1B1C1D1E1F2021232425262728","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EBA0864087DD8B852A87","PECompact 0.977 -> Jeremy Collake",0}, {"01020308090A0B1011121314191A1F20252627","EB0668C39C60E85D555881ED2B85018550B902","PECompact 0.94 -> Jeremy Collake",0}, {"01020308090A0B101115161718191A1B1D1E1F202122232526","EB0668C39C60BDB902B0908DBDA54F40F3AA01AD045140FFB5","PECompact 0.92 -> Jeremy Collake",0}, {"0102030405060708090A0B0C0D0E0F10111213141516191A1B1C1D1E2324","9C60E80200000033C08BC483C004938BE38B5BFC81EB400087DD01AD01AD","PEBundle 2.0b5 - 2.0x -> Jeremy Collake",0}, {"0102030405060708090A0B0C0D0E0F10111213141516191A1B1C1D1E1F202122232425262728292A2B2C","9C60E80200000033C08BC483C004938BE38B5BFC81EB400087DD6A04680010000068000200006A00FF95","PEBundle 0.2 - 2.0x -> Jeremy Collake",0}, {"0102030405060708090A0B0C0D0E0F1011121315161718191A1B1C1D1E1F20212224252627282A2B2C","535152565755E8000000005D8BCD81ED3330402B8DEE32400083E90B898DF2324080BDD13240010F84","PC PE Encryptor alpha preview -> The +Q, Plushmm & Mr. Nop",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F202122232425262728292A2B","60E801000000E883C404E801000000E95D81EDD3224000E804020000E8EB08EB02CD20FF24249A66BE4746","Pack Master 1.0 -> WebtoolMaster (PEX Clone)",0}, {"0102030405060708090D","83EC5C53555657FF1500","Nullsoft PiMP 1.x",0}, {"010203040508090A0B0C0E131415","558BEC81EC000056576ABE598DBD","Nullsoft PiMP 1.3x",0}, {"0102030405060708090A0B0C0D0E0F101112","8D50122BC9B11E8A023477880242E2F7C88C","NFO 1.0 -> Bart^CrackPL",0}, {"0102030405","E9A6000000","Neolite 2.0 -> Neoworx Inc.",0}, {"01020304090A0B0C0D0E0F101112131415161718","60669CBB80B300104000904B83FBFF75F3669D61","LameCrypt -> LaZaRus",0}, {"0102030405060708090A0B0C0D0F1011121315161718","54E8000000005D8BC581ED6134002B8560370083E806","Krypton 0.4 -> Yado/Lockless",0}, {"0102030405060708090A0B0C0D0E0F10","8B0C24E90A7C0100AD4240BDBE9D7A04","Krypton 0.2 -> Yado/Lockless",0}, {"0102030405060708090A0B0C","E803000000E9EB6C5840FFE0","kryptor 5 -> r!sc",0}, {"010203040508090A0B0C0D","558BEC81EC00005356576A","GLBS Install Stub 32-bit -> Wise",0}, {"01020304050608090A0B0C0D0E0F10151A1B20212223","558BEC81EC1400005356576A00FF1568FF1585C07429","Install Stub 32-bit -> InstallShield",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A","496E6E6F53657475704C647257696E646F770000535441544943","Inno-Setup Module",0}, {"01020304","496E6E6F","Inno Setup Module",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F202122232425262728292A2B2D2E2F303132","4B45524E454C33322E646C6C00004C6F61644C69627261727941000047657450726F634164647265737300000000000000","FSG 1.2 Heuristic Mode -> dulek/xt",0}, {"0102030405060708090A0B101112131415161718191A1B1C1D1E1F20212223242526","BBD0014000BF00104000BE53E80A00000002D275058A164612D2C3FCB280A46A025B","FSG 1.0 -> dulek/xt",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F20","E919320000E97C2A0000E919240000E9FF230000E91E2E0000E9882E0000E92C","EZIP 1.0 -> Jonathan Clark",0}, {"0102030405060708090A0B0C0D0E0F10111213141516171C212223","68001040006804010000E83903000005001040C6005C68686A00E8","EXEJoiner 1.0 -> y0da",0}, {"0102030405060708090A0B0C0D0E0F1011191A1B1C1D1E1F202122","E8240000008B4C240CC70117000100C78131C089411489411880A1","EXECryptor 1.3.0.45 -> SoftLab MIL-TEC Ltd.",0}, {"0102030405060708090A0B0C0D0E0F101112131415","60E8000000005D81EDFB1D4000B97B0900008BF7AC","EXEStealth 1.1 -> WebtoolMaster (y0da's Cryptor Clone)",0}, {"0102030405060708090A0B0C0D0E0F1011121318191D202122232425262728292A","3BC074028183553BC074028183533BC97401BC028100003BDB7401BE5D8BD581ED","EXE32Pack 1.3x -> SteelBytes",0}, {"0102030405060708090A0B0C0D0E0F1011121318191D202122232425262728292A2B2C2D2E","3BC074028183553BC074028183533BC97401BC028100003BDB7401BE5D8BD581EDCC8D4000","EXE32Pack 1.36 -> SteelBytes",0}, {"0102030405060708090A0B0C0D0E0F101516","55E8000000005D83ED068BC5556089AD2B85","Crunch/PE -> BitArts",0}, {"0102030405060708090A0B0C0D0E0F10111213141516171819","E92E030000EB02833D58EB02FF1D5BEB020FC75FEB03FF1D34","CodeCrypt 0.164 -> defiler",0}, {"010203040506070A0B0C0D101112131415161718191A1B1C1D1E202122232425262728292A2B2C2D2E2F3031","558BEC81EC0C0256BE04018D85F8FEFFFF56506A00FF155410408A8DF8FEFFFF33D284C98D85F8FEFFFF7416","CExe 1.0a -> Tinyware Inc.",0}, {"0102030405060708090A0B0C0D0E0F10111213","558BEC81C4E4FEFFFF53565733C08945F08985","Blade Joiner 1.5",0}, {"0102030405060708090A0B0C0D0E0F1011121314","EB01EA9CEB01EA53EB01EA51EB01EA52EB01EA56","BJFNT 1.1b -> :MARQUiS:",0}, {"0102060708090A0B0C","6801E801000000C3C3","ASProtect 1.2x [New Strain] -> Alexey Solodovnikov",0}, {"0102060708090A0B0C","6801E801000000C3C3","ASProtect 1.2x [New Strain] -> Alexey Solodovnikov",0}, {"010203040809","00006801C3AA","ASProtect 1.2x -> Alexey Solodovnikov",0}, {"010206","6801C3","ASProtect 1.2 -> Alexey Solodovnikov",0}, {"0102040506","60E9050000","ASProtect 1.1 brs -> Alexey Solodovnikov",0}, {"01020708090A0B0C","60E99178797979E9","ASProtect 1.1 MTE -> Alexey Solodovnikov",0}, {"0102040506070F","60E9040000E9EE","ASProtect 1.1 -> Alexey Solodovnikov",0}, {"0102030405060708090A0E0F1314151617","60E801000000905D81ED00BB0003DD2B9D","ASProtect 1.0 -> Alexey Solodovnikov",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D","60E803000000E9EB045D4555C3E801000000EB5DBBEDFFFFFF03DD81EB","ASPack 2.12 -> Alexey Solodovnikov",0}, {"0102030405060708090A","60E802000000EB095D55","ASPack 2.11d -> Alexey Solodovnikov",0}, {"0102030405060708090A0B0C0D0E0F10111213141516","60E802000000EB095D5581ED39394400C3E93D040000","ASPack 2.11b -> Alexey Solodovnikov",0}, {"010203040506","60E93D040000","ASPack 2.11 -> Alexey Solodovnikov",0}, {"0102030405060708","60E841060000EB41","ASPack 1.08.04 -> Alexey Solodovnikov",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1D1E1F20212223","60EB0A5DEB02FF2545FFE5E8E9E8F1FFFFFFE981ED236A4400BB10440003DD2B9D72","ASPack 1.08.02 -> Alexey Solodovnikov",0}, {"0102030405060708090A0B0C0D0E0F101112131418191A1B1D1E1F202122","60EB0A5DEB02FF2545FFE5E8E9E8F1FFFFFFE9814400BB10440003DD2B9D","ASPack 1.08.01 -> Alexey Solodovnikov",0}, {"0102030405060708090D0E121314151618191B1C1D1E20212223242627","60E8000000005D81ED00B80003C52B85129D89851E9D0080BD089D0000","ASPack 1.04b -> Alexey Solodovnikov",0}, {"0102030405060708090A0B0C0D0E0F12131415161718191A1B1C1D1E1F202122232425262728292A2B2C2D2E2F303132333435363738393A3B3C3D3E3F404142434445464748494A4B4C4D4E4F50","60E8000000005D81ED3ED94300B8380003C52B850BDE4300898517DE430080BD01DE4300007515FE8501DE4300E81D000000E879020000E8120300008B8503DE4300038517DE43008944241C61FF","ASPack 1.02a -> Alexey Solodovnikov",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F202122232425","60E8000000005D81ED921A4400B88C1A440003C52B85CD1D44008985D91D440080BDC41D44","ASPack 1.00b -> ALexey Solodovnikov",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F2021242526292A2B2C2D2E2F31","9C60E80200000033C08BC483C004938BE38B5BFC81EB0720400087DD6A046800106800026A00FF954623400B","Alloy 1.x.2000 -> Prakash Gautam",0}, {"010206070B0C101112131415161718191A1B1C1D1E","60B900BA00BE000238404E75FA8BC28A1832DFC0CB","AcidCrypt -> AciDLeo",0}, {"0102030405060B0C0D0E0F12","6006FC1E07BE6A0468001068","32Lite 0.03a -> Oleg Prokhorov",0}, {"01020304090A0D0E0F","5589E5E8C9C3455845","MingWin32 GCC 2.x",0}, {"0102070C0D10","5A686852E9FF","Microsoft Visual Basic 6.0 DLL",0}, {"0102030405060B101112131415161718191A1B1C1D","558BEC6AFF686864A1000000005064892500000000","Microsoft Visual C++ 6.0",0}, {"0102030405060708090A0B0C0D","558BEC5657BF010000008B750C","Microsoft Visual C++ DLL Method 4",0}, {"0102030405060708090A0B0C0D0E0F10111213191A1B1C","53B8010000008B5C240C565785DB557512833D750933C0","Microsoft Visual C++ DLL Method 3",0}, {"0102030405090B0C","535657BB018B2414","Microsoft Visual C++ DLL Method 2",0}, {"0102030405060708090A0B0C0D0E0F","5355568B74241485F657B801000000","Microsoft Visual C++ DLL Method 1",0}, {"0102030405060708090A0B","558BEC538B5D08568B750C","Microsoft Visual C++ 7.0 DLL Method 3",0}, {"0102030405060708090A0B0C0D0E0F12","558BEC538B5D08568B750C578B7D1083","Microsoft Visual C++ 7.0 DLL Method 2",0}, {"01020306070C0D0F1011121314191A1B1C","558D6C81EC8B4583F801560F8485C00F84","Microsoft Visual C++ 7.0 DLL Method 1\nMicrosoft Visual C++ 6.0 DLL",0}, {"010308","6A68E8","Micorsoft Visual C++ 7.0 Method2",0}, {"0103080D121314191A1C1D1E1F20212227282A2B303133","6A68E8BF8BC7E889658BF4893E56FF158B4E890D8B46A3","Microsoft Visual C++ 7.0",0}, {"0102030405060708090A0F10111213141516","558BEC83EC50535657BE8D7DF4A5A566A58B","Microsoft Visual C++ 6.20",0}, {"0102030405060708090A0B0C11161718191A1B1C1D1E1F212223","64A100000000558BEC6AFF6868506489250000000083EC535657","Microsoft Visual C++ 4.x",0}, {"0102030405060B101112131415161718191A1B1C1D1E1F212223","558BEC6AFF686864A100000000506489250000000083C4535657","InstallShield 2000 stub",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B","5589E5535657837D0C017505E817000000FF7510FF750CFF7508A1","LCC Win32 DLL -> Jacob Navia",0}, {"0102030405060708090A0B0C10111213141516","64A1000000005589E56AFF6800689A10400050","LCC Win32 1.x -> Jacob Navia",0}, {"01020304050708090A0B0C0D0E0F101112131415","558BEC83C453565733C08945F08945D48945D0E8","Borland Delphi Setup Module",0}, {"01060708090A0C0D0E0F15161718191E1F20","BA837D0C01755052C6058B4D08890D894A04","0102030405060B0C0D1112171C21222328292A2F",0}, {"010203040708090E0F1015161718191A1B1C1D1E1F202122232425262B2C2D32","506A00E8FFFFBA528905894204C7420800000000C7420C00000000E85A58E8C3","Borland Delphi 4.0 - 5.0",0}, {"010203040708090E0F10151617181D1E1F242526272829","506A00E8FFFFBA528905894204E85A58E8C3558BEC33C0","Borland Delphi 3.0",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F202122232425262728292A2E2F3031323337","558BEC83C4F053565733C08945F0B8CC3A4000E8E0FCFFFF33C05568EA3C400064FF306489206A0068806A036A006A0180","SecuPack 1.5 -> SC Soft",0}, {"010607080D0E1318191E1F24282D","E86A00E88905E88905C7050AB8C3","Borland Delphi 2.0",0}, {"010203040506070C111617","558BEC83C4B4B8E8E88D40","Borland Delphi DLL",0}, {"0102030405060708090A0B0C0D0E","EB1066623A432B2B484F4F4B90E9","Borland C++ DLL Method 2",0}, {"0106070809","A1C1E002A3","Borland C++ DLL Method 1",0}, {"0102030405060708090A0B0C0D0E1318191A1B20","EB1066623A432B2B484F4F4B90E9A1C1E002A352","Borland C++ 1999",0}, {"01060708090E0F101112171C1D1E1F20212223242526","A1C1E002A3575133C0BFB93BCF76052BCFFCF3AA595F","Borland C++",0}, {"0102030405060708090A0B0C0D0E0F101112131415161718191A1B1C1D1E1F202122232425262728292A","558BEC6AFF6840D240006804AC400064A100000000506489250000000083EC585356578965E8FF15BCD0","WARNING -> VIRUS -> I-Worm KLEZ",0}, {"0102030405060708090A0B0C0D0E0F1011","558BEC538B5D08568B750C578B7D1085F6","WARNING -> VIRUS -> W32@NimDA_mm",0}, {"010203040506070B0C101112131415161718191A1B1C1D1E1F20212223242526272829","558BEC6AFF68B868D064A100000000506489250000000083EC585356578965E8FF1520","Armadillo 2.51 -> Silicon Realms Toolworks",0}, {"010203040506070B0C101112131415161718191A1B1C1D1E1F202122232425262728292D2E2F30313233","558BEC6AFF68B868F864A100000000506489250000000083EC585356578965E8FF152033D28AD48915D0","Armadillo -> Silicon Realms Toolworks",0}, {"0102030405060B1011121314","558BEC6AFF686864A1000000","Armadillo 1.71 -> Silicon Realms Toolworks",0}, {"0105090A0B","E900005741","Watcom C/C++",0}, {"0102030405060B101112131415161718191A1B1C1D1E1F202122232425262728292D2E2F30313233","558BEC6AFF686864A100000000506489250000000083EC585356578965E8FF155833D28AD48915EC","Armadillo 2.5x - 2.6x -> Silicon Realms Toolworks",0}, {"","5D83ED06EB02EA048D","PESHiELD 0.251 -> ANAKiN",1}, {"","60E82B000000","PESHiELD 0.25 -> ANAKiN",1}, {"","E800000000","WIN32 PE packed / crypted -> δ?",1}, {"","60E8000000005D81EDF31D4000B97B0900008DBD3B1E40008BF7AC","yoda's cryptor 1.2",1}, {"","60E8000000005D81ED8A1C4000B99E0000008DBD4C2340008BF733","yoda's cryptor 1.1",1}, {"","60E8000000005D81EDE71A4000E8A1000000E8D1000000E885010000F785","yoda's cryptor 1.0",1}, {"","E8000000005D8BCD81ED7A29400089AD0F6D4000","X-PEOR 0.99b -> MadMax",1}, {"","608BF033DB83C30183C001","XCR 0.11 -> X-Lock",1}, {"","53558BE833DBEB60","WWPack32 1.x -> Piotr Warezak",1}, {"","5354554233322E455845005F4D61696E576E6450726F63403136005F53","Wise Installer stub",1}, {"","9C55E8EC00000087D55D6087D580BD1527400001","Virogen Crypt 0.75",1}, {"","0BC00BC00BC00BC00BC00BC00BC00BC0","VBOX 4.3 MTE -> WeijunLi",1}, {"","8CE00BC58CE00BC403C5740074008BC5","VBOX 4.2 MTE -> WeijunLi",1}, {"","01DB078B1E83EEFC11DBEDB80100000001DB078B1E83EEFC11DB11C001DB730B","UPX alternative stub -> Markus & Lazlo",1}, {"","60E8000000005883E83D508DB8FF578DB0E80183CDFF31DB01DB75078B1E83EEFC11DB730B8A0646880747EBEB90","UPX 0.60 - 0.61 -> Markus & Lazlo",1}, {"","50E800000000582500F0FFFF8BC883C1605183C04083EA0652FF209DC3","The Guard Library",1}, {"","E90DE4FFFF","tElock 0.99 -> tE!",1}, {"","E91BE4FFFF","tElock 0.98b2 -> tE!",1}, {"","E925E4FFFF","tElock 0.98b1 -> tE!",1}, {"","E959E4FFFF","tElock 0.96 -> tE!",1}, {"","E9DDE4FFFF","tElock 0.95 build 2 -> tE!",1}, {"","E9D5E4FFFF","tElock 0.95 build 1 -> tE!",1}, {"","E96EE7FFFF","tElock 0.92a -> tE!",1}, {"","60E802000000CD20E8000000005E2BC9587402CD20B9","tElock 0.85f -> tE!",1}, {"","60E8F9110000C383","tElock 0.80 -> tE!",1}, {"","60E848110000C383","tElock 0.71b7 -> tE!",1}, {"","60E844110000C383","tElock 0.71b2 -> tE!",1}, {"","60E872110000C383","tElock 0.71b1 -> tE!",1}, {"","60E8ED100000C383","tElock 0.71 -> tE!",1}, {"","60E8BD100000C383","tElock 0.70 -> tE!",1}, {"","E90000000060E8000000005883C008F3EBFF","tElock 0.6x -> tE!tElock 0.70 -> tE!",1}, {"","E90000000060E8000000005883C008F3EBFFE083C02850E8000000005EB3338D460E8D76312818F87300C38BFEB93C02","tElock 0.61 -> tE!tElock 0.6x -> tE!tElock 0.70 -> tE!",1}, {"","C1EE00668BC9EB01EB60EB01EB9CE8000000005E83C65E8BFE68790159EB01EBAC54E8035CEB08","tElock 0.51 -> tE!",1}, {"","C1EE00668BC9EB01EB60EB01EB9CE8000000005E83C6528BFE68790159EB01EBAC54E8035CEB08","tElock 0.42 -> tE!",1}, {"","555756525153E8000000005D8BD581ED973B402B952D3C4083EA0B8995363C400195243C40019528","Stone's PE Encryptor 1.13",1}, {"","53E8000000005B8BC32D","Private Exe 2.0a",1}, {"","9C60E8CA000000030004000500060007000800","PEtite 1.2 -> Ian Luck",1}, {"","60E800000000414E414B494E5D83ED06EB02EA04","PESHiELD 0.2 / 0.2b / 0.2b2 -> ANAKiN",1}, {"","60E8000000005D83ED0680BDE0040000010F84F2","PE Pack 0.99 -> ANAKiN",1}, {"","FC8B357001400083EE406A4068003010","PE Packer -> Vecna",1}, {"","609CBE001040008BFEB928030000BB78563412AD33C3ABE2FA9D61","PEncrypt 1.0 -> junkcode",1}, {"","EB02C7851EEB03CD20EBEB01EB9CEB01EBEB02CD","PE Lock NT 2.02c -> :MARQUiS:",1}, {"","EB03CD20EBEB01EB1EEB01EBEB02CD209CEB03CD","PE Lock NT 2.01 -> :MARQUiS:",1}, {"","BD01ADE3384000FFB5DF3840","PC Shrinker 0.45 -> Virogen",1}, {"","E8E80100006001ADB327400068","PC Shrinker 0.20 -> Virogen",1}, {"","8B04249C60E8000000005D81ED0A45400080BD67444000000F8548","PE Intro 1.0 -> Predator NLS",1}, {"","E8000000005B83EB05EB04524E44","PE Crypt 1.02 -> random, killa & acpizer",1}, {"","E8000000005B83EB05EB04524E4421EB02CD20EB","PE Crypt 1.00/1.01/Console -> random, killa & acpizer",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB3F904087DD8B85E69040018533904066C785904090900185DA90400185DE90400185E29040BB7B11","PECompact 1.68 - 1.84 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB3F904087DD8B85E69040018533904066C785904090900185DA90400185DE90400185E29040BB8B11","PECompact 1.67 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB3F804087DD8B85D28040018533804066C785804090900185CE8040BBBB12","PECompact 1.60 - 1.65 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F904087DD8B85A29040018503904066C7859040909001859E9040BB2D12","PECompact 1.56 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F804087DD8B85A28040018503804066C7858040909001859E8040BB2D12","PECompact 1.55 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0FA04087DD8B85A6A040018503A04066C785A040909001859EA040BB5B12","PECompact 1.47 - 1.50 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0FA04087DD8B85A6A040018503A04066C785A040909001859EA040BB6012","PECompact 1.46 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0FA04087DD8B85A6A040018503A04066C785A040909001859EA040BBC311","PECompact 1.40 - 1.45 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0FA04087DD8B85A6A040018503A04066C785A040909001859EA040BB8A11","PECompact 1.40b5 - 1.40b6 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0FA04087DD8B85A6A040018503A04066C785A040909001859EA040BB8611","PECompact 1.40b2 - 1.40b4 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F804087DD8B85A68040018503804066C785008040909001859E8040BBF810","PECompact 1.34 - 1.40b1 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F704087DD8B85A67040018503704066C7857040909001859E7040BB050E","PECompact 1.26b1 - 1.26b2 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F704087DD8B85A67040018503704066C7857040909001859E7040BBF30D","PECompact 1.25 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F704087DD8B85A67040018503704066C7857040909001859E7040BBD209","PECompact 1.24.2 - 1.24.3 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F704087DD8B85A67040018503704066C7857040909001859E7040BBD208","PECompact 1.23b3 - 1.24.1 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F604087DD8B85956040018503604066C78560409090BB49","PECompact 1.10b5 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F604087DD8B85956040018503604066C78560409090BB44","PECompact 1.10b4 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB0F604087DD8B859460","PECompact 1.10b2 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB28634087DD8B85AD63","PECompact 1.10b1 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EBC4844087DD8B854985","PECompact 1.00 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB2F854087DD8B85B485","PECompact 0.99 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EBD7844087DD8B855C85","PECompact 0.98 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EBD1844087DD8B855685","PECompact 0.978.2 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB49874087DD8B85CE87","PECompact 0.978.1 -> Jeremy Collake",1}, {"","EB0668C39C60E80233C08BC483C004938BE38B5BFC81EB24884087DD8B85A988","PECompact 0.978 -> Jeremy Collake",1}, {"","EB0668C39C60E85D555B81ED8B85018566C785","PECompact 0.971 - 0.976 -> Jeremy Collake",1}, {"","5550E8000000005DEB01E360E803000000D2EB0B58EB014840EB01","PC-Guard 3.03d -> Blagoje Ceklic",1}, {"","EB019AE83D000000EB019AE8EB010000EB019AE82C040000EB01","NoodleCrypt 2.0 -> noodlespa",1}, {"","8B0C24E9C08D0100C13A6ECA5D7E796DB3645A71EA","Krypton 0.3 -> Yado/Lockless",1}, {"","60E8000000005EB9470800002BC002040ED3C04979F8418D7E2C3346F666B91B","kryptor 9 / kryptor a -> r!sc & noodlespa",1}, {"","EB6A87DB00000000","kryptor 8 -> r!sc & noodlespa",1}, {"","6A0060E901010000","EP v2.0 -> CoDe_Inside",1}, {"","5083C0178BF09733C033C9B124ACAA86C4","EP v1.0 -> CoDe_Inside",1}, {"","3BC074028183553BC074028183533BC97401BC028100003BDB7401BE5D8BD581EDEC8D4000","EXE32Pack 1.39 -> SteelBytes",1}, {"","3BC074028183553BC074028183533BC97401BC028100003BDB7401BE5D8BD581EDDC8D4000","EXE32Pack 1.38 -> SteelBytes",1}, {"","3BC074028183553BC074028183533BC97401BC028100003BDB7401BE5D8BD581ED4C8E4000","EXE32Pack 1.37 -> SteelBytes",1}, {"","9CFE030060BE000041008DBE0010FFFF5783CDFFEB10","ExeSmasher",1}, {"","EB033A4D3A1EEB02CD209CEB02CD20EB02CD2060","BJFNT 1.3 -> :MARQUiS:",1}, {"","EB0269B183EC04EB03CD20EBEB01EB9CEB01EBEB","BJFNT 1.2rc -> :MARQUiS:",1}, {"","A8030000617508B801000000C20C006800000000C38B85260400008D8D3B0400005150FF95","ASPack 2.xx Heuristic Mode -> Alexey Solodovnikov",1}, {"","60E802000000EB095D5581ED39394400C3E959040000","ASPack 2.11c -> Alexey Solodovnikov",1}, {"","60E8000000005D81ED0A4A4400BB044A440003DD2B9DB150440083BDAC50440000899DBB4E","ASPack 1.08.03 -> Alexey Solodovnikov",1}, {"","60EB035DFFE5E8F8FFFFFF81ED1B6A4400BB106A440003DD2B9D2A","ASPack 1.08.x -> Alexey Solodovnikov",1}, {"","60E8000000005D81ED00B80003C52B850BDE898517DE0080BD01DE0000","ASPack 1.07b -> Alexey Solodovnikov",1}, {"","60E8000000005D81EDEAA84300B8E4A8430003C52B8578AD4300898584AD430080BD6EAD43","ASPack 1.061b -> Alexey Solodovnikov",1}, {"","60E8000000005D81EDCE3A4400B8C83A440003C52B85B53E44008985C13E440080BDAC3E44","ASPack 1.05b -> Alexey Solodovnikov",1}, {"","60E8000000005D81EDAE984300B8A898430003C52B85189D43008985249D430080BD0E9D43","ASPack 1.03b -> Alexey Solodovnikov",1}, {"","60E8000000005D81ED96784300B89078430003C52B857D7C43008985897C430080BD747C43","ASPack 1.02b -> Alexey Solodovnikov",1}, {"","60E8000000005D81EDD22A4400B8CC2A440003C52B85A52E44008985B12E440080BD9C2E44","ASPack 1.01b -> Alexey Solodovnikov",1}, {"","558BEC6AFF686864A100000000506489250000000083EC535657","Microsoft Visual C++ 6.0",1}, {"","538BD833C0A36A00E8FFA3A1A333C0A333C0A3E8","Borland Delphi 6.0",1}, {"","EB1066623A432B2B484F4F4B90E9A1C1E002A38B","Borland C++ DLL Method 3",1}, {"","558BEC6AFF6850687464A100000000506489250000000083EC585356578965E8FF155833D28AD48915FC","Armadillo 2.60 beta1 -> Silicon Realms Toolworks",1}, {"","558BEC6AFF6840685464A100000000506489250000000083EC585356578965E8FF155833D28AD48915EC","Armadillo 2.53 -> Silicon Realms Toolworks",1}, {"","558BEC6AFF68E068D464A100000000506489250000000083EC585356578965E8FF1538","Armadillo 2.52 -> Silicon Realms Toolworks",1}, {"","558BEC6AFF68B0686064A100000000506489250000000083EC585356578965E8FF1524","Armadillo 2.52 beta2 -> Silicon Realms Toolworks",1}, }; |
|
|
[原创]PEInfo模拟版V0.02
本想下一版将加入类似PEID的编译器和已加壳特征码扫描功能,但现在还没有头绪,希望有经验的兄弟能提供些资料。谢谢! |
|
|
|
|
|
|
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值