-
-
[原创]第二题 初窥门径day2wp
-
发表于: 2025-8-17 11:05 5477
-
下面的分析因为是做完题写的所以已经有部分恢复的符号和变量名.
主函数中输入长度小于0x70时会进入check:
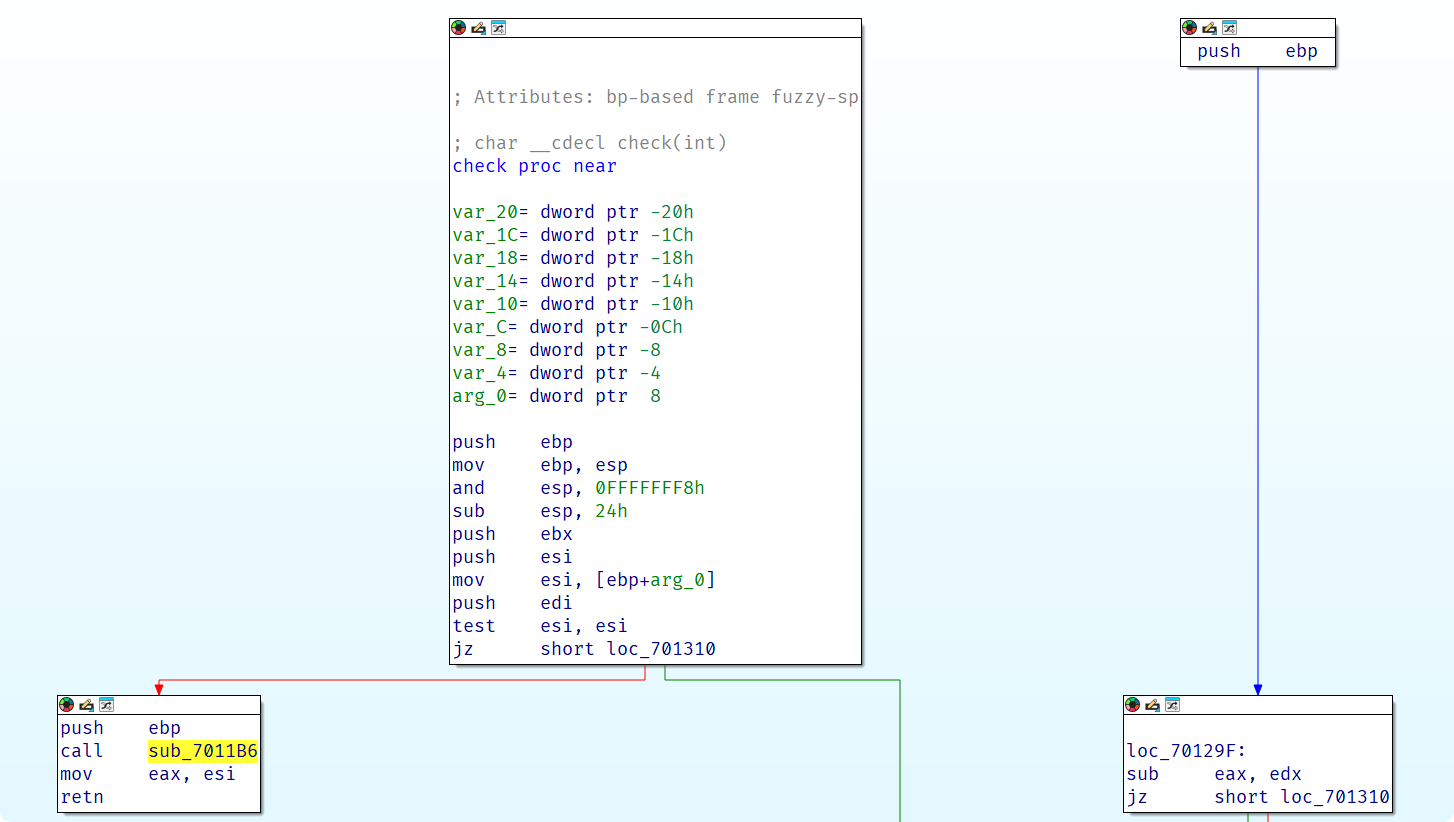
但是函数结构很奇怪, push ebp后进入7011b6执行了:
也就是调整栈指针然后直接修改返回地址, 这是一个跳板, 进入跳板跳到地函数, 先是又执行了一个strlen然后push edi又进入了一个跳板:
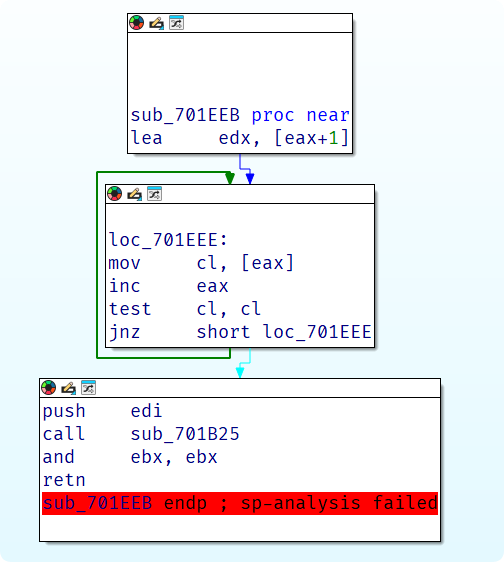
新的跳板跳向了loc_70129F:
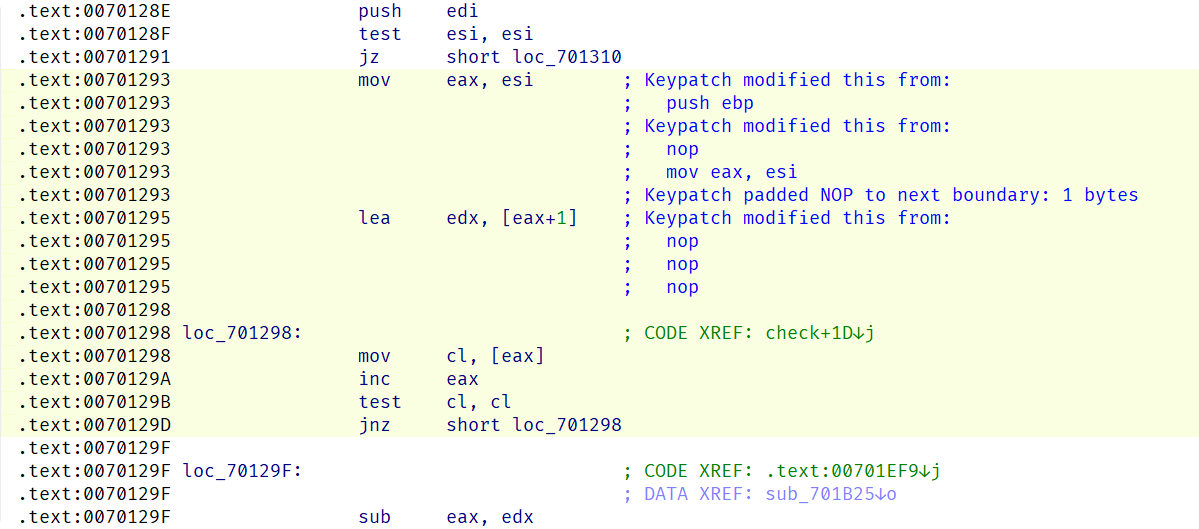
所以实际上check函数先是通过跳板的方法执行了一个strlen然后跳回check来达成控制流混淆, patch成下面的样子就能让IDA正常反编译了:
然后分析check的功能, 先是根据当前位的输入在一个0-9a-z的表里取idx:
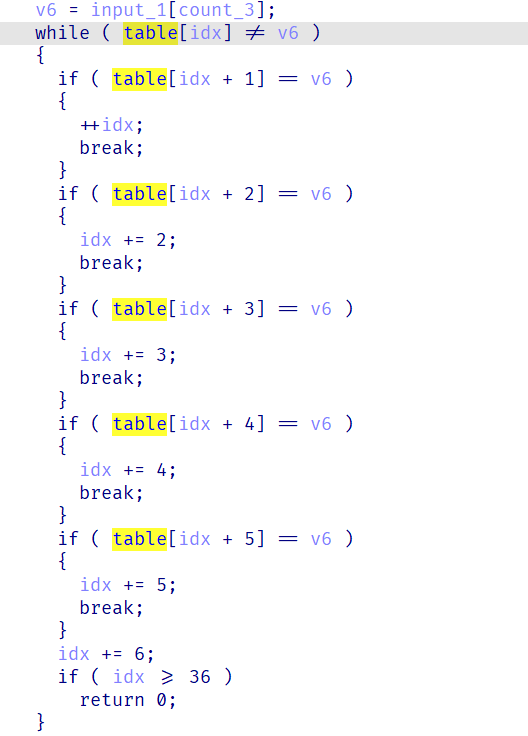
然后根据这个idx以及当前所在是奇偶位来确定三个变量x, y, z, 很容易联想到是一个迷宫程序:
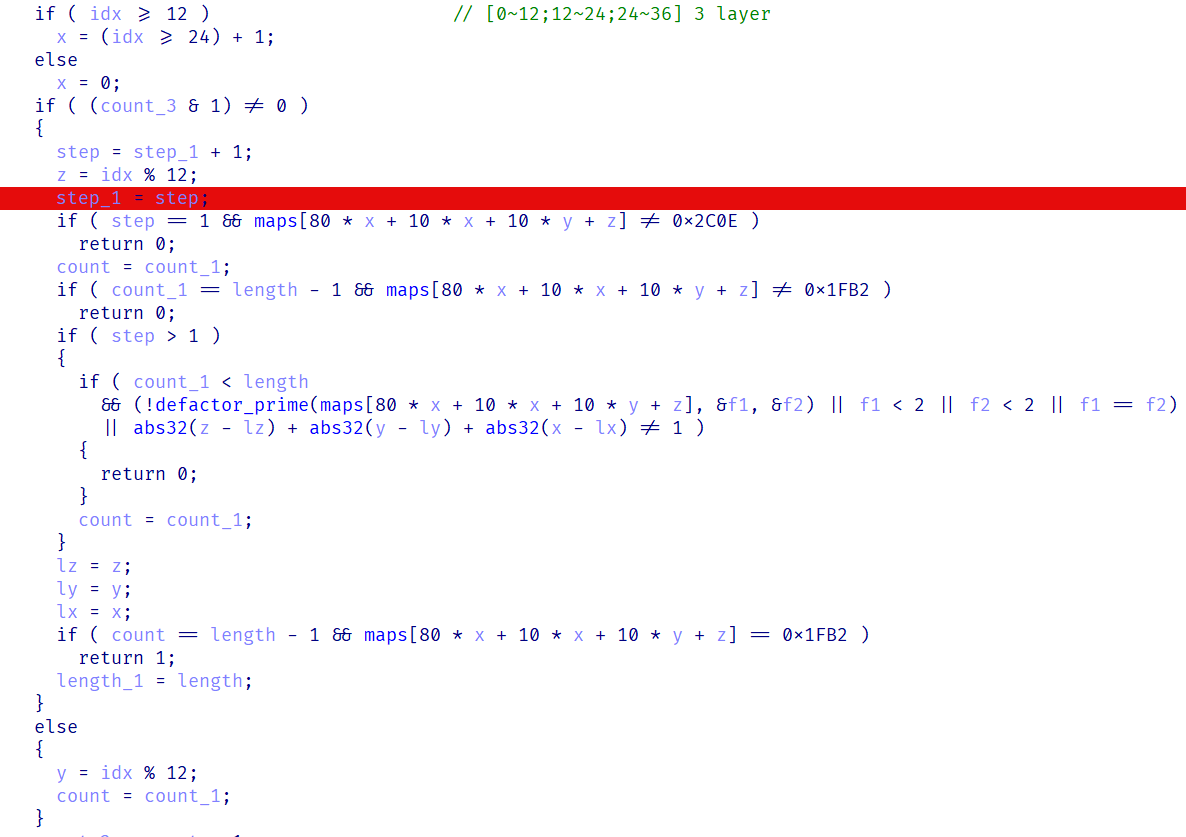
也就是每一步由输入的2个字节来确定, 第一个确定y, 第二个确定x, z, 同时限定起点是0x2c0e终点是0x1fb2, 每次行动完的位置与上一次的位置曼哈顿距离必须是1, 剩下的一个限制就在defactor_prime中:
其中sqrt是牛顿法求根, 猜测这是分解质因数的程序, 调试也可以验证确实是, 接下来就是写程序打印地图:
得到地图后手动解出:
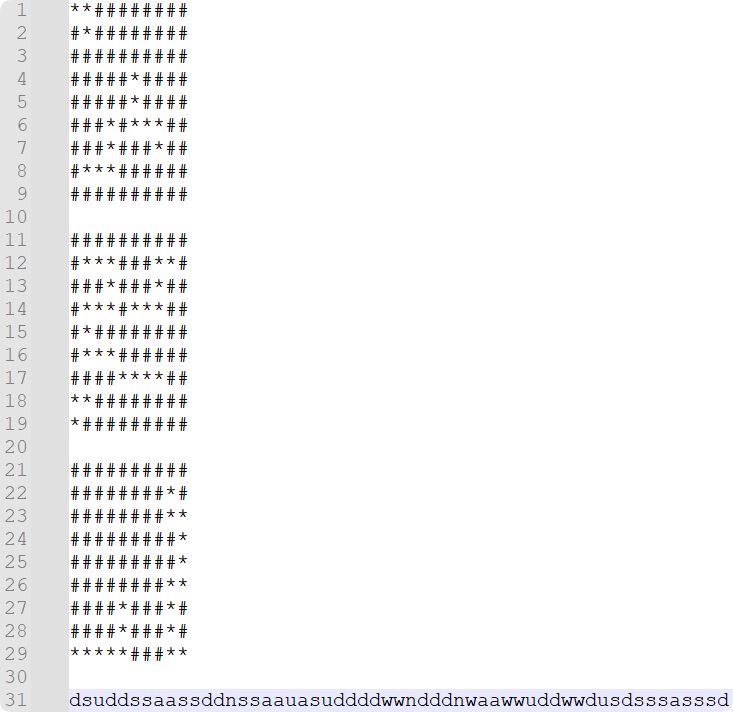
根据路径生成key:
char __cdecl defactor_prime(int n4_1, int *p_n2, int *p_n3){ int n2; // edi int n4_2; // ecx int n2_3; // esi int n2_2; // ecx int n2_1; // [esp+1Ch] [ebp-4h] int n4_3; // [esp+24h] [ebp+4h] if ( n4_1 < 4 ) return 0; n2 = 2; n2_1 = 2; n4_2 = (int)sqrt((double)n4_1); n4_3 = n4_2; if ( n4_2 < 2 ) return 0; while ( 1 ) { if ( n4_1 % n2 || n2 < 2 ) goto LABEL_10; n2_3 = 2; n2_2 = (int)sqrt((double)n2_1); if ( n2_2 >= 2 ) { while ( n2 % n2_3 ) { if ( ++n2_3 > n2_2 ) goto LABEL_8; } goto LABEL_9; }LABEL_8: if ( is_prime(n4_1 / n2) ) break;LABEL_9: n4_2 = n4_3;LABEL_10: n2_1 = ++n2; if ( n2 > n4_2 ) return 0; } if ( p_n2 ) *p_n2 = n2; if ( p_n3 ) *p_n3 = n4_1 / n2; return 1;}char __cdecl defactor_prime(int n4_1, int *p_n2, int *p_n3){ int n2; // edi int n4_2; // ecx int n2_3; // esi int n2_2; // ecx int n2_1; // [esp+1Ch] [ebp-4h] int n4_3; // [esp+24h] [ebp+4h] if ( n4_1 < 4 ) return 0; n2 = 2; n2_1 = 2; n4_2 = (int)sqrt((double)n4_1); n4_3 = n4_2; if ( n4_2 < 2 ) return 0; while ( 1 ) { if ( n4_1 % n2 || n2 < 2 ) goto LABEL_10; n2_3 = 2; n2_2 = (int)sqrt((double)n2_1); if ( n2_2 >= 2 ) { while ( n2 % n2_3 ) { if ( ++n2_3 > n2_2 ) goto LABEL_8; } goto LABEL_9; }LABEL_8: if ( is_prime(n4_1 / n2) ) break;LABEL_9: n4_2 = n4_3;LABEL_10: n2_1 = ++n2; if ( n2 > n4_2 ) return 0; } if ( p_n2 ) *p_n2 = n2; if ( p_n3 ) *p_n3 = n4_1 / n2; return 1;}import mathdef is_prime(n: int) -> bool: if n < 2: return False if n == 2: return True for i in range(2, round(math.sqrt(n)) + 1): if n % i == 0: return False return Truedef defactor_prime(n: int): if n < 4: return False limit = round(math.sqrt(n)) if limit < 2: return False for p in range(2, limit + 1): if n % p == 0: q = n // p if is_prime(p) and is_prime(q): return True return Falsemap = [0x2C0E, 0x1312, 0x7F44, 0x4C2B, 0x966, 0x1E12, 0x1263, 0x1828, 0x31A1, 0x52AE, 0x1DC6, 0x4019, 0x3D89, 0x614D, 0x1A4A, 0x3A24, 0x5406, 0xE61, 0x658, 0xD4C, 0x5423, 0x4860, 0x7988, 0x1FA3, 0x705B, 0x4464, 0x63EF, 0x403E, 0x50CB, 0x1676, 0x5132, 0x68B5, 0x4A38, 0x6FF5, 0x189B, 0x170B, 0x2704, 0x20ED, 0x4938, 0x47F6, 0x7512, 0x5196, 0x2B7C, 0x4A50, 0x2E54, 0x6FBE, 0x3532, 0x7B54, 0xABD, 0x2889, 0x56C0, 0x323B, 0x3698, 0x31CF, 0x435A, 0x75FA, 0xA2B, 0x200B, 0x45ED, 0x163F, 0x2554, 0x62BB, 0x3393, 0x2A31, 0x2956, 0x3004, 0x3684, 0x3DEE, 0x47AC, 0x2267, 0x629E, 0x1E93, 0x7943, 0x661B, 0x7FB4, 0x255A, 0x3D37, 0x1804, 0x69E1, 0x312C, 0x3999, 0x293F, 0x2F0E, 0x743A, 0x117, 0x64CD, 0x7C76, 0x5CBF, 0x6AB0, 0x585, 0x6CFC, 0x3CE6, 0x6FAB, 0xF81, 0x511C, 0x24E4, 0x785, 0x5AEB, 0x2977, 0xBFB, 0x55F8, 0x39, 0x29DD, 0x4987, 0x133B, 0x5E2F, 0x7F4D, 0x6497, 0x62C2, 0x3774, 0x1826, 0x78C, 0x20BB, 0x5473, 0x68B6, 0x27FB, 0x7321, 0x1B0E, 0x6280, 0x54E2, 0x5133, 0x61E7, 0x2F6B, 0x5AE2, 0x1B09, 0x64BB, 0x71B, 0x6272, 0x453F, 0x22BD, 0xD68, 0x52A9, 0x3116, 0x19AD, 0x28F6, 0x141E, 0x6B10, 0x32AC, 0x2394, 0x353D, 0x6A40, 0x697, 0x80E, 0x6883, 0x4297, 0x175D, 0xB3A, 0x4584, 0x4FB8, 0x55D2, 0x2592, 0x5F99, 0x5986, 0x5A84, 0x71A3, 0x3975, 0x525, 0x3E15, 0x823, 0x12D7, 0x78EF, 0x636B, 0x471A, 0x531C, 0x23F8, 0x38D7, 0x7E64, 0x18DB, 0x344E, 0x5655, 0x1C69, 0xEE8, 0x23C, 0x25C8, 0x684, 0x776D, 0xB65, 0x7855, 0x602D, 0x277E, 0x60AC, 0x1885, 0x6E40, 0x3EEC, 0x175C, 0xD2B, 0x4F2E, 0x645, 0x6C70, 0x457D, 0x5CD8, 0x2B12, 0x11C, 0x7AAD, 0x2E5E, 0x37CB, 0x5CF8, 0x5C48, 0x648F, 0x3841, 0x6344, 0x7F63, 0x5C2, 0xBE2, 0x717A, 0x7317, 0x711A, 0x4344, 0x319, 0x756E, 0x2F5E, 0x6EF2, 0x23B0, 0x1ED5, 0x5A1B, 0x5FFF, 0x7494, 0x5C4C, 0x7D2C, 0x2C51, 0x4BE4, 0x5197, 0x2384, 0x64DD, 0x62E9, 0x5019, 0x447E, 0x1DA1, 0x70B3, 0x5B03, 0x17BC, 0x4ED4, 0x3E1F, 0x26F8, 0x2AF2, 0x7B64, 0x4634, 0x69D9, 0x75A, 0x344B, 0x27D0, 0xC9C, 0x385E, 0x2496, 0x5635, 0x57AA, 0x44A8, 0x62AF, 0x65E7, 0x3284, 0x7A73, 0x1CCF, 0x25F4, 0x5DCD, 0x5CDE, 0x109B, 0x7890, 0x45CF, 0x5FEF, 0x4ABB, 0x26, 0x47D, 0x6121, 0x3A42, 0x5519, 0x32AF, 0x2096, 0x18E7, 0x4181, 0x1FB2]bitmap = [[0] * 90 for _ in range(3)]for i in range(3): for j in range(90): bitmap[i][j] = '*' if defactor_prime(map[i * 90 + j]) else '#'for i in range(3): for j in range(9): for z in range(10): print(bitmap[i][j * 10 + z], end='') print() print()[培训]《冰与火的战歌:Windows内核攻防实战》!从零到实战,融合AI与Windows内核攻防全技术栈,打造具备自动化能力的内核开发高手。
最后于 2025-8-18 13:37
被kanxue编辑
,原因:
赞赏
他的文章
- [原创]KCTF2025 day10 wp 941
- [原创]KCTF2025 day9 wp 8266
- [原创]KCTF2025 day8 wp 7836
- [原创]KCTF2025 day7 wp 6724
- [原创]KCTF2025 day6 wp 6801
赞赏
雪币:
留言:




