手机:Google Pixel 6,Aosp android13
cpu架构:Arm64
Frida:16.1.10
爱奇艺:15.2.5
这段时间在研究爱奇艺的一些功能,当用Frida调试时发现有反Frida检测,现象是执行frida -l index.js -U -f com.qiyi.video时进程重启,下面是对Frida检测的一些分析,并通过hook绕过Frida检测。
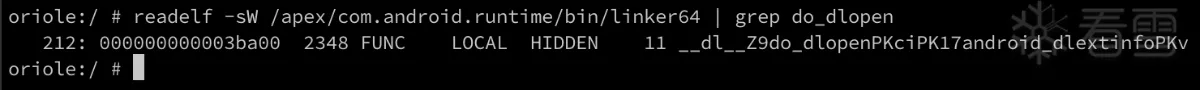
用Frida hook do_dlopen函数看加载哪个so时崩溃的,hook之前先获取do_dlopen在linker64中的相对偏移

从结果可以看出加载的最后一个so是:libmsaoaidsec.so,并且没有调用onLeave,由此可断定崩溃点在libmsaoaidsec.so中,并且在JNI_OnLoad之前检测的,检测点应该是在init_array初始化函数中。
<br/>
既然挂上Frida后进程就退出,那么我们就来分析是调用哪个系统调用退出的,可以通过strace查看系统调用,但在执行strace时需要在dlopen加载libmsaoaidsec.so之前让线程sleep 10秒,以便留出strace执行时机。


我们看这一行[pid 15576] [000000751926c008] exit_group(0 <unfinished ...>,显示15576线程是在0x751926c008地址处调用exit_group退出的,通过proc/15534/maps查看libc.so的地址范围是0x7509b9c000 - 0x7509c70000,很明显0x751926c008不是libc.so的地址,由此可以断定exit_group的代码是动态释放的。
<br/>
动态释放代码一定是要操作内存的,接下来我们用前面相同的逻辑,用strace查看调用了哪些和内存相关的系统调用
<br/>
strace -e trace=process,memory -i -f -p 25947

注意这行:[pid 25990] [0000007509c48ab8] mmap(NULL, 28, PROT_READ|PROT_WRITE|PROT_EXEC, MAP_PRIVATE|MAP_ANONYMOUS, -1, 0) = 0x751926c000
<br/>
上面这行mmap申请的内存返回的地址是:0x751926c000,正好匹配后面exit_group前面的地址:000000751926c008
<br/>
由mmap的地址可以看出mmap是libc.so中的函数,于是我们可以hook mmap打印一下调用栈




解决方案就是replace掉这个无返回值的函数 void sub_1B924()
<br/>
由于这个检测逻辑在.init_函数中,所以得先找到hook时机,查看Aosp代码发现linker执行init_array类的函数是call_constructors:
所以直接hook call_constructors函数,在onEnter中replace掉sub_1b924
<br/>
查看call_constructors在linker64中的偏移

function hookDlopen() {
let linker64_base_addr = Module.getBaseAddress('linker64')
let offset = 0x3ba00 // __dl__Z9do_dlopenPKciPK17android_dlextinfoPKv
let android_dlopen_ext = linker64_base_addr.add(offset)
Interceptor.attach(android_dlopen_ext, {
onEnter: function(args){
this.name = args[0].readCString()
Log.log(`dlopen onEnter ${this.name}`)
}, onLeave: function(retval){
Log.log(`dlopen onLeave name: ${this.name}`)
if (this.name != null && this.name.indexOf('libmsaoaidsec.so') >= 0) {
let JNI_OnLoad = Module.getExportByName(this.name, 'JNI_OnLoad')
Log.log(`dlopen onLeave JNI_OnLoad: ${JNI_OnLoad}`)
}
}
})
}
function hookDlopen() {
let linker64_base_addr = Module.getBaseAddress('linker64')
let offset = 0x3ba00 // __dl__Z9do_dlopenPKciPK17android_dlextinfoPKv
let android_dlopen_ext = linker64_base_addr.add(offset)
Interceptor.attach(android_dlopen_ext, {
onEnter: function(args){
this.name = args[0].readCString()
Log.log(`dlopen onEnter ${this.name}`)
}, onLeave: function(retval){
Log.log(`dlopen onLeave name: ${this.name}`)
if (this.name != null && this.name.indexOf('libmsaoaidsec.so') >= 0) {
let JNI_OnLoad = Module.getExportByName(this.name, 'JNI_OnLoad')
Log.log(`dlopen onLeave JNI_OnLoad: ${JNI_OnLoad}`)
}
}
})
}
function hookDlopen() {
// 获取libc中的sleep函数
let sleep: Function = new NativeFunction(Module.getExportByName('libc.so', 'sleep'), 'uint', ['uint'])
let linker64_base_addr = Module.getBaseAddress('linker64')
let offset = 0x3ba00 // __dl__Z9do_dlopenPKciPK17android_dlextinfoPKv
let android_dlopen_ext = linker64_base_addr.add(offset)
Interceptor.attach(android_dlopen_ext, {
onEnter: function(args){
this.name = args[0].readCString()
Log.log(`dlopen onEnter ${this.name}`)
if (this.name != null && this.name.indexOf('libmsaoaidsec.so') >= 0) {
sleep(10) // sleep10秒留出strace执行时机
}
}, onLeave: function(retval){
Log.log(`dlopen onLeave name: ${this.name}`)
}
})
}
function hookDlopen() {
// 获取libc中的sleep函数
let sleep: Function = new NativeFunction(Module.getExportByName('libc.so', 'sleep'), 'uint', ['uint'])
let linker64_base_addr = Module.getBaseAddress('linker64')
let offset = 0x3ba00 // __dl__Z9do_dlopenPKciPK17android_dlextinfoPKv
let android_dlopen_ext = linker64_base_addr.add(offset)
Interceptor.attach(android_dlopen_ext, {
onEnter: function(args){
this.name = args[0].readCString()
Log.log(`dlopen onEnter ${this.name}`)
if (this.name != null && this.name.indexOf('libmsaoaidsec.so') >= 0) {
sleep(10) // sleep10秒留出strace执行时机
}
}, onLeave: function(retval){
Log.log(`dlopen onLeave name: ${this.name}`)
}
})
}
function hook_mmap() {
const mmap = Module.getExportByName("libc.so", "mmap");
Interceptor.attach(mmap, {
onEnter: function (args) {
let length = args[1].toString(16)
if (parseInt(length, 16) == 28) {
Log.log('backtrace:\n' + Thread.backtrace(this.context, Backtracer.ACCURATE)
.map(DebugSymbol.fromAddress).join('\n') + '\n');
}
}
})
}
function hookDlopen() {
let sleep: Function = new NativeFunction(Module.getExportByName('libc.so', 'sleep'), 'uint', ['uint'])
let linker64_base_addr = Module.getBaseAddress('linker64')
let offset = 0x3ba00 // __dl__Z9do_dlopenPKciPK17android_dlextinfoPKv
let android_dlopen_ext = linker64_base_addr.add(offset)
Interceptor.attach(android_dlopen_ext, {
onEnter: function(args){
this.name = args[0].readCString()
Log.log(`dlopen onEnter ${this.name}`)
if (this.name != null && this.name.indexOf('libmsaoaidsec.so') >= 0) {
// sleep(10)
hook_mmap()
}
}, onLeave: function(retval) {
Log.log(`dlopen onLeave name: ${this.name}`)
}
})
}
function hook_mmap() {
const mmap = Module.getExportByName("libc.so", "mmap");
Interceptor.attach(mmap, {
onEnter: function (args) {
let length = args[1].toString(16)
if (parseInt(length, 16) == 28) {
Log.log('backtrace:\n' + Thread.backtrace(this.context, Backtracer.ACCURATE)
.map(DebugSymbol.fromAddress).join('\n') + '\n');
}
}
})
}
function hookDlopen() {
let sleep: Function = new NativeFunction(Module.getExportByName('libc.so', 'sleep'), 'uint', ['uint'])
let linker64_base_addr = Module.getBaseAddress('linker64')
let offset = 0x3ba00 // __dl__Z9do_dlopenPKciPK17android_dlextinfoPKv
let android_dlopen_ext = linker64_base_addr.add(offset)
Interceptor.attach(android_dlopen_ext, {
onEnter: function(args){
this.name = args[0].readCString()
Log.log(`dlopen onEnter ${this.name}`)
if (this.name != null && this.name.indexOf('libmsaoaidsec.so') >= 0) {
// sleep(10)
hook_mmap()
}
}, onLeave: function(retval) {
[培训]《冰与火的战歌:Windows内核攻防实战》!从零到实战,融合AI与Windows内核攻防全技术栈,打造具备自动化能力的内核开发高手。
最后于 2024-3-4 13:01
被yyy123编辑
,原因: 上传libmsaoaidsec.so文件