-
-
[原创]KCTF 2021秋季赛 第九题 万事俱备
-
发表于: 2021-12-9 12:41 21188
-
易语言?
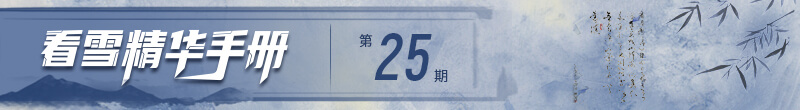
拿到程序,发现是易语言写的,还有点奇怪,直接x64dbg调试先看,跑起来发现易语言只是套了个外壳: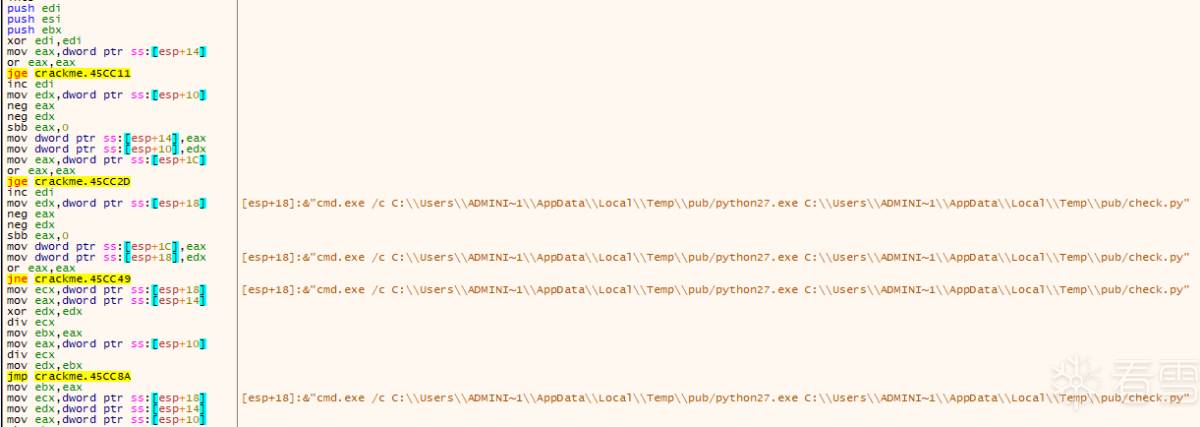
Py脚本
从temp目录找到check.py和对应的CPython2.7解释器,不用想解释器肯定是改过的,先定位到程序版本: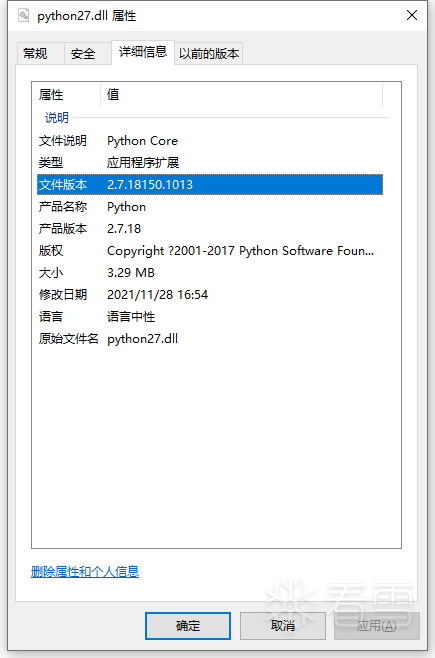
程序版本是2.7.18,从官网下载源码编译,e6eK9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6%4N6%4N6Q4x3X3g2H3P5i4c8Z5L8$3&6Q4x3X3g2G2M7X3N6Q4x3V1k6X3N6s2m8Q4x3V1k6H3P5i4c8Z5L8$3&6Q4x3V1j5J5i4K6u0W2y4#2)9J5k6e0p5^5i4K6u0r3f1s2W2@1K9r3!0F1i4K6u0V1x3W2)9J5k6e0N6Q4x3X3f1I4z5q4)9J5k6i4c8Y4P5R3`.`.
Python执行原理
温顾一遍解释器原理也是有必要的,首先定位到几个关键点:
处理Opcode
目前还没找到很简单的方法,目前用了两种方式:
1、编写测试代码生成,用两个解释器生成pyc,再用dis模块反汇编对比,这里可写个脚本提高下效率,这种方式能找到到绝大部分。
2、对于方式1不好生成的指令,通过IDA对比PyEval_EvalFrameEx函数,手动识别特征代码(字符串、关系调用等)
重新编译python
替换了源码中的Include/opcode.h和Lib/opcode.py,最终生成python可以执行check.py,开始以为作者在解释器上做了大量工作,事实上并没有。
名称混淆:
指令switch平坦 + 花指令:
switch:每一条指令通过XOR跳往switch判断下一条指令
花指令:这里的opcode当NOP处理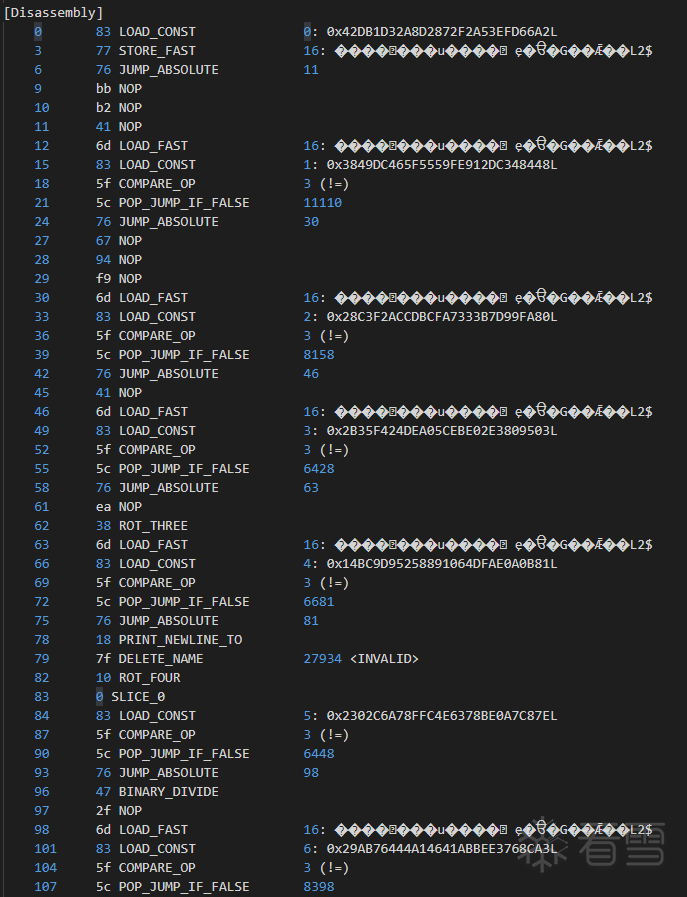
字符串加密(这里是后面Trace发现的),通过base64、zlib、xor等解密
因为指令switch那块比较固定,静态还原代码也不是很难,考虑效率问题,最后还是找到了不错的动态跟踪的工具:
x-python仓库:fbdK9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6Y4K9i4c8Z5N6h3u0Q4x3X3g2U0L8$3#2Q4x3V1k6J5L8$3y4C8P5g2)9J5c8Y4S2Q4x3X3c8H3P5i4c8Z5L8$3^5`.
做了如下改动:
最后执行python_d.exe xpy.py -v check.pyc,几分钟后到了raw_input输入,看了下之前代码如下:
执行效果还不错,看到了具体代码,以后有空再改造下把栈的信息拿出来,方便分析。
直接逆推不出来,注意到m、n、j、k的初始值和最后运算方式一致,因此可以把mnjk推导出来,至于k的值(最多是0-15),因此跑个16次计算,再把结果校验,最后得到KCTF的flag:
//恢复的opcode如下
#define NOP 65#define STOP_CODE 61#define POP_TOP 30#define ROT_TWO 52#define ROT_THREE 56#define DUP_TOP 13#define ROT_FOUR 16#define UNARY_POSITIVE 32#define UNARY_NEGATIVE 89#define UNARY_NOT 57#define UNARY_CONVERT 87#define UNARY_INVERT 25#define BINARY_POWER 77#define BINARY_MULTIPLY 69#define BINARY_DIVIDE 71#define BINARY_MODULO 14#define BINARY_ADD 81#define BINARY_SUBTRACT 53#define BINARY_SUBSCR 40#define BINARY_FLOOR_DIVIDE 76#define BINARY_TRUE_DIVIDE 48#define INPLACE_FLOOR_DIVIDE 26#define INPLACE_TRUE_DIVIDE 63#define SLICE 0#define SLICE_1 1#define SLICE_2 2#define SLICE_3 3#define STORE_SLICE 4#define STORE_SLICE_1 5#define STORE_SLICE_2 6#define STORE_SLICE_3 7#define DELETE_SLICE 8#define DELETE_SLICE_1 9#define DELETE_SLICE_2 10#define DELETE_SLICE_3 11#define STORE_MAP 64#define INPLACE_ADD 17#define INPLACE_SUBTRACT 86#define INPLACE_MULTIPLY 20#define INPLACE_DIVIDE 74#define INPLACE_MODULO 67#define STORE_SUBSCR 73#define DELETE_SUBSCR 23#define BINARY_LSHIFT 66#define BINARY_RSHIFT 19#define BINARY_AND 18#define BINARY_XOR 88#define BINARY_OR 85#define INPLACE_POWER 33#define GET_ITER 70#define PRINT_EXPR 39#define PRINT_ITEM 59#define PRINT_NEWLINE 15#define PRINT_ITEM_TO 62#define PRINT_NEWLINE_TO 24#define INPLACE_LSHIFT 41#define INPLACE_RSHIFT 72#define INPLACE_AND 45#define INPLACE_XOR 37#define INPLACE_OR 29#define BREAK_LOOP 50#define WITH_CLEANUP 42#define LOAD_LOCALS 83#define RETURN_VALUE 46#define IMPORT_STAR 28#define EXEC_STMT 51#define YIELD_VALUE 60#define POP_BLOCK 22#define END_FINALLY 31#define BUILD_CLASS 54#define HAVE_ARGUMENT 90 /* Opcodes from here have an argument: */#define STORE_NAME 112#define DELETE_NAME 127#define UNPACK_SEQUENCE 107#define FOR_ITER 108#define LIST_APPEND 141#define STORE_ATTR 102#define DELETE_ATTR 137#define STORE_GLOBAL 98#define DELETE_GLOBAL 114#define DUP_TOPX 110#define LOAD_CONST 131#define LOAD_NAME 94#define BUILD_TUPLE 106#define BUILD_LIST 133#define BUILD_SET 116#define BUILD_MAP 139#define LOAD_ATTR 140#define COMPARE_OP 95#define IMPORT_NAME 124#define IMPORT_FROM 135#define JUMP_FORWARD 115#define JUMP_IF_FALSE_OR_POP 123#define JUMP_IF_TRUE_OR_POP 128#define JUMP_ABSOLUTE 118#define POP_JUMP_IF_FALSE 92#define POP_JUMP_IF_TRUE 120#define LOAD_GLOBAL 138#define CONTINUE_LOOP 113#define SETUP_LOOP 93#define SETUP_EXCEPT 111#define SETUP_FINALLY 130#define LOAD_FAST 109#define STORE_FAST 119#define DELETE_FAST 142#define RAISE_VARARGS 134#define CALL_FUNCTION 90#define MAKE_FUNCTION 126#define BUILD_SLICE 105#define MAKE_CLOSURE 136#define LOAD_CLOSURE 132#define LOAD_DEREF 125#define STORE_DEREF 122#define CALL_FUNCTION_VAR 99#define CALL_FUNCTION_KW 100#define CALL_FUNCTION_VAR_KW 101#define SETUP_WITH 143#define EXTENDED_ARG 145#define SET_ADD 146#define MAP_ADD 147//恢复的opcode如下
#define NOP 65#define STOP_CODE 61#define POP_TOP 30#define ROT_TWO 52#define ROT_THREE 56#define DUP_TOP 13#define ROT_FOUR 16#define UNARY_POSITIVE 32#define UNARY_NEGATIVE 89#define UNARY_NOT 57#define UNARY_CONVERT 87#define UNARY_INVERT 25#define BINARY_POWER 77#define BINARY_MULTIPLY 69#define BINARY_DIVIDE 71#define BINARY_MODULO 14#define BINARY_ADD 81#define BINARY_SUBTRACT 53#define BINARY_SUBSCR 40#define BINARY_FLOOR_DIVIDE 76#define BINARY_TRUE_DIVIDE 48#define INPLACE_FLOOR_DIVIDE 26#define INPLACE_TRUE_DIVIDE 63#define SLICE 0#define SLICE_1 1#define SLICE_2 2#define SLICE_3 3#define STORE_SLICE 4#define STORE_SLICE_1 5#define STORE_SLICE_2 6#define STORE_SLICE_3 7#define DELETE_SLICE 8#define DELETE_SLICE_1 9#define DELETE_SLICE_2 10#define DELETE_SLICE_3 11#define STORE_MAP 64#define INPLACE_ADD 17#define INPLACE_SUBTRACT 86#define INPLACE_MULTIPLY 20#define INPLACE_DIVIDE 74#define INPLACE_MODULO 67#define STORE_SUBSCR 73#define DELETE_SUBSCR 23#define BINARY_LSHIFT 66#define BINARY_RSHIFT 19#define BINARY_AND 18#define BINARY_XOR 88#define BINARY_OR 85#define INPLACE_POWER 33#define GET_ITER 70#define PRINT_EXPR 39#define PRINT_ITEM 59#define PRINT_NEWLINE 15#define PRINT_ITEM_TO 62#define PRINT_NEWLINE_TO 24#define INPLACE_LSHIFT 41#define INPLACE_RSHIFT 72#define INPLACE_AND 45#define INPLACE_XOR 37#define INPLACE_OR 29#define BREAK_LOOP 50#define WITH_CLEANUP 42#define LOAD_LOCALS 83#define RETURN_VALUE 46#define IMPORT_STAR 28#define EXEC_STMT 51#define YIELD_VALUE 60#define POP_BLOCK 22#define END_FINALLY 31#define BUILD_CLASS 54#define HAVE_ARGUMENT 90 /* Opcodes from here have an argument: */#define STORE_NAME 112#define DELETE_NAME 127#define UNPACK_SEQUENCE 107#define FOR_ITER 108#define LIST_APPEND 141#define STORE_ATTR 102#define DELETE_ATTR 137#define STORE_GLOBAL 98#define DELETE_GLOBAL 114#define DUP_TOPX 110#define LOAD_CONST 131#define LOAD_NAME 94#define BUILD_TUPLE 106#define BUILD_LIST 133#define BUILD_SET 116#define BUILD_MAP 139#define LOAD_ATTR 140#define COMPARE_OP 95#define IMPORT_NAME 124#define IMPORT_FROM 135#define JUMP_FORWARD 115#define JUMP_IF_FALSE_OR_POP 123#define JUMP_IF_TRUE_OR_POP 128#define JUMP_ABSOLUTE 118#define POP_JUMP_IF_FALSE 92#define POP_JUMP_IF_TRUE 120#define LOAD_GLOBAL 138#define CONTINUE_LOOP 113#define SETUP_LOOP 93#define SETUP_EXCEPT 111#define SETUP_FINALLY 130#define LOAD_FAST 109#define STORE_FAST 119#define DELETE_FAST 142#define RAISE_VARARGS 134#define CALL_FUNCTION 90#define MAKE_FUNCTION 126#define BUILD_SLICE 105#define MAKE_CLOSURE 136#define LOAD_CLOSURE 132#define LOAD_DEREF 125#define STORE_DEREF 122#define CALL_FUNCTION_VAR 99#define CALL_FUNCTION_KW 100#define CALL_FUNCTION_VAR_KW 101#define SETUP_WITH 143#define EXTENDED_ARG 145#define SET_ADD 146#define MAP_ADD 147eNpVlq+LImEYx/Xu9g6GxbDBIGLYsCwiGwz+AQO3YRCDwXAHEwwHLmIweN1gEDEYDCIGg0HEYNg/wGAYlglymA+DYVgmHGI+n1nm8/KUL+/M+7zPj+/zfZ+ZnzeJROLx0xUav5PXVVJWt7y7+XxdfZPVq0BPoCLgC6R5V+LE9ys+fpGVG280xgLPmOzF6df43YeDyN9CoClQwPhOjP8m4902GTwIvAh4AlMBSyCMS2h0BXYE2hHIFvghcBLY4OWAyUWgzmMeiFzNKatHoKjefwIjCNvyLvKcEThismJjRn6OTrKPscfjEA76cBDwuKWiJRtDYtzH7H7kXKCOPjHudJJbTCLCcpz1qWihV1mBMv2IWraHtS05/8JkxtkWG+90dUqmAxrfxPMU7s9U3kQHDr2M+pEitXt6OSGrOYqw2XV1e0LOjiBiTi6vqMRChANChtpzl7hF7eqNaGeOFWnABNVddFY2mUa9XLMRciwi9g92BWCCvxPdr+ir0aPyPMdGNL6N5z4hPYpZQ8mFUgdcjYB2b5FADTpPxB2wWsJGR6DKCRu1L7BbINY62jhiZ+E5RPzmuhjGl2yMGX0W9/cJpweq3CABF65KUOLQPI9ALfLbUH4bmjxGhqNvtwNNAYkbjZvrZ0b4kHQXekp1YdLXQtpQWxoh5aBuSZVFcikTsstQCCh6j0kRDdXhdEWgHYS1Ma6itR3EHvHiIgtbT8IenktsbLhlVYKfaWiHcZPHX4r7G+rm1eGqS1ZZiC1rO4vJ9cyqxjUYE2iNF5tdn9aaqdKmHwd9IqWH1pGmmA9Lh5AuSQ4he4zCamykqXyNBExDz5x9oSlmmhlKmoj1nSQrWu1rzYFHkj7+WggkpL97/T2q6q+puY0jGpCjSgsTcw1M0Q/MiCqdDnjMkOkFDZ2p0kyGgv6gTTQRTzA5o/wVArZgKMsJc89LqCmjf6gc7swEwm4JJKn9B4X61ks=', 866: '0', 715: 'marshal', 341: 'zlib', 203: 'base64'}, 866)
eNpVlq+LImEYx/Xu9g6GxbDBIGLYsCwiGwz+AQO3YRCDwXAHEwwHLmIweN1gEDEYDCIGg0HEYNg/wGAYlglymA+DYVgmHGI+n1nm8/KUL+/M+7zPj+/zfZ+ZnzeJROLx0xUav5PXVVJWt7y7+XxdfZPVq0BPoCLgC6R5V+LE9ys+fpGVG280xgLPmOzF6df43YeDyN9CoClQwPhOjP8m4902GTwIvAh4AlMBSyCMS2h0BXYE2hHIFvghcBLY4OWAyUWgzmMeiFzNKatHoKjefwIjCNvyLvKcEThismJjRn6OTrKPscfjEA76cBDwuKWiJRtDYtzH7H7kXKCOPjHudJJbTCLCcpz1qWihV1mBMv2IWraHtS05/8JkxtkWG+90dUqmAxrfxPMU7s9U3kQHDr2M+pEitXt6OSGrOYqw2XV1e0LOjiBiTi6vqMRChANChtpzl7hF7eqNaGeOFWnABNVddFY2mUa9XLMRciwi9g92BWCCvxPdr+ir0aPyPMdGNL6N5z4hPYpZQ8mFUgdcjYB2b5FADTpPxB2wWsJGR6DKCRu1L7BbINY62jhiZ+E5RPzmuhjGl2yMGX0W9/cJpweq3CABF65KUOLQPI9ALfLbUH4bmjxGhqNvtwNNAYkbjZvrZ0b4kHQXekp1YdLXQtpQWxoh5aBuSZVFcikTsstQCCh6j0kRDdXhdEWgHYS1Ma6itR3EHvHiIgtbT8IenktsbLhlVYKfaWiHcZPHX4r7G+rm1eGqS1ZZiC1rO4vJ9cyqxjUYE2iNF5tdn9aaqdKmHwd9IqWH1pGmmA9Lh5AuSQ4he4zCamykqXyNBExDz5x9oSlmmhlKmoj1nSQrWu1rzYFHkj7+WggkpL97/T2q6q+puY0jGpCjSgsTcw1M0Q/MiCqdDnjMkOkFDZ2p0kyGgv6gTTQRTzA5o/wVArZgKMsJc89LqCmjf6gc7swEwm4JJKn9B4X61ks=', 866: '0', 715: 'marshal', 341: 'zlib', 203: 'base64'}, 866)
#eval_frame函数 if (bytecode_name not in ['COMPARE_OP','POP_JUMP_IF_FALSE','JUMP_ABSOLUTE','NOP','LOAD_FAST','STORE_FAST']):
if len(arguments) > 0:
if isinstance(arguments[0],long):
if arguments[0] < 111111183538799472:
self.log(bytecode_name, int_arg, arguments, offset, line_number)
else:
self.log(bytecode_name, int_arg, arguments, offset, line_number)
else:
self.log(bytecode_name, int_arg, arguments, offset, line_number)
#eval_frame函数 if (bytecode_name not in ['COMPARE_OP','POP_JUMP_IF_FALSE','JUMP_ABSOLUTE','NOP','LOAD_FAST','STORE_FAST']):
if len(arguments) > 0:
if isinstance(arguments[0],long):
if arguments[0] < 111111183538799472:
self.log(bytecode_name, int_arg, arguments, offset, line_number)
else:
self.log(bytecode_name, int_arg, arguments, offset, line_number)
else:
self.log(bytecode_name, int_arg, arguments, offset, line_number)
#format_instruction函数 if vm and bytecode_name in vm.byteop.stack_fmt:
stack_args = vm.byteop.stack_fmt[bytecode_name](vm, int_arg, repr)
if (bytecode_name == 'INPLACE_XOR'):
pos = stack_args.find('L')
if pos != -1:
if long(stack_args[stack_args.find('(')+1:pos])>111111111111111111111:
return ""
#format_instruction函数 if vm and bytecode_name in vm.byteop.stack_fmt:
stack_args = vm.byteop.stack_fmt[bytecode_name](vm, int_arg, repr)
if (bytecode_name == 'INPLACE_XOR'):
pos = stack_args.find('L')
if pos != -1:
if long(stack_args[stack_args.find('(')+1:pos])>111111111111111111111:
return ""
INFO:xpython.vm: @7266: LOAD_NAME dict
INFO:xpython.vm: @7637: BUILD_LIST 0
INFO:xpython.vm: @5069: LOAD_NAME __import__
INFO:xpython.vm: @6232: LOAD_CONST marshal
INFO:xpython.vm: @4648: CALL_FUNCTION (__import__) 1 positional, 0 named
INFO:xpython.vm: @8028: LOAD_ATTR loads
INFO:xpython.vm: @6832: LOAD_CONST eNpdmD2LKkkUhmf37geIGPSCgQwGBjKIdGDgDzAwkMFggg5c6MBAuCIGBv4AAwNxO5igA5EODAwGMTAwWDYyMJCLLCL9Aww6EOlAlonX8uJz9mxyqLKqznnPez6q2t9/fnp6evnxJr7++eU2+sGMkvz2202+/GpGayOGRtSN2BuR5reynDCjX8yoyup989yIjhFFNv9xM/fykxm5Dy1f/cfZ71sKZvT3l4eCnhEpI9qc8Iw4GlEy4h24MyMmRmSN+MeIjBFLI6ZGRKA6se8OPGdEBX0n1E/waGNEDOYTUxdAAyNGRlyN+IaCGgpyHMtwwgJ9jLBAsAZV/KR4GePRDM3CQQ6T4lH0CPd/TE7QF8FazIkBW8psuY8CoA1wP8fmNpvXWDuB5b65jwt99j2D4GDEBxwcWVgxvcB9wghH77svtIxosNDAmguTb4TnirUsNGWBcc/srhELTGZwtY2qsxE2+AJGR07cleY1vgRaPIxXWPgkliWI3ZDKNVC1dWnMyPuALD5iN0VQ2oxeiYK4H6EvQaCukNgEhnhU1Mk/JzcCcm2KC+JbmeqJsZbGmsNvz8AooioJ+tOjjXzX8k7cBugrMi2TUneyd4DcsLBDc1pHJoODM73Fwm4T4xGrWxRIfyni5RloAal3RoGL5yuI9THkwu6BjLUB9MmCw9mWpsnB8x7AA5B2UbDF6QJu+WTYmlpwyM4+WXLlWB19Cc5uQeVgY0AJdTR/0kqXqDqDRQrb1r3JhisLzTIKCe0BNq66yViYzGPojZukoGt1A+YUdsfUucBNU4hjSKwQ6S4Z9s6xOkG2cGtHii7ohM/gC6lpm+mZmjnqYsqTf55u9VmMt5gmQPoBk3v0fdAPQkrcIih1fJPeniL6PnAzjCSRdqCv89sEzDGaM5rdOV6WdH/xod0nlj4mu2he6Us9DTk9/ZutA1+GnDRVewGQh4Ihbs3B1yRafaxVONEmZHk2T3B/ra+xKZSUtDNb/JV3jrybpuirgGWD6OpkyBOUI6rq0D5kX6DTJ4/nPfB1mC5gsgiJCVxNcZuO9DXRxP0IG1tiPsGjV4p4wbEBeVrARgJX5VgMJXvq7QSxHbRIV6nRRsa4ekFplWLvAbKDNUf3XXnizEBfA6ncGkuOOeArozQgCicSJIlbUxrKFgdT+lXqUecbnaLySFjox528uUbAfcfagNUWoypnLfKgioMOkTnhqqcvNBvMPYS8ckP0ORDbJXcbUFLFeAiWEazNWUgR3wmpV2LfSPeIEWRnubHTsDaEziWtr0HtN3X9hmTsHmFjY6O7VAd/k5ytkbF54KaZzvS7xMLBHf6uwNzRfbxGlsw422XkkwIRJ+RefWZ1TicM2bdncwm4ZRiakHotoMn9a8GfvMctPC+SAhd9X9ZJPblYTmSdsNFA+HA/1vdWESLeqIAtdemRFg4V8L/Hp08+N0kam5D1UTpEeKwe9LdazMIUxuXBYoFeviHW+pEw1VFYsCC5O9J9fM7UhaEhSgMi7REU+ZqoQESWtHWxmwXQJ8bLGrOkihDxCdnylSrA67Cx1LF0iUwTrkJUyaegVE+ku0UJuBdaboEge1SUp19LS+wmdYNPQaeDCxHlUiDNYl26SVyV727JXcmcHOQ47AtJ6hAiclTAK6ik3QT6P4ouXkaALACoxtQlrxaETP7BaLMq3TsiyCt9WW/pL5K7Hv7K7dLS0Lb6vRvrv3LkK1W+Eg66GitsyaB5DC93pX/dxL//a4kn
INFO:xpython.vm: @4908: LOAD_ATTR decode
INFO:xpython.vm: @4959: LOAD_CONST base64
INFO:xpython.vm: @6483: CALL_FUNCTION (decode) 1 positional, 0 named
INFO:xpython.vm: @7383: LOAD_ATTR decode
INFO:xpython.vm: @8232: LOAD_CONST zlib
INFO:xpython.vm: @4318: CALL_FUNCTION (decode) 1 positional, 0 named
INFO:xpython.vm: @5568: CALL_FUNCTION (loads) 1 positional, 0 named
INFO:xpython.vm: @4207: FOR_ITER 7304
INFO:xpython.vm: @5658: STORE_NAME ((954, (12,))) ooo00o
INFO:xpython.vm: @5122: LOAD_NAME ooo00o
INFO:xpython.vm: @8417: LOAD_CONST 0
INFO:xpython.vm: @5897: BINARY_SUBSCR ((954, (12,)), 0)
INFO:xpython.vm: @8584: LOAD_CONST 216
INFO:xpython.vm: @8639: BINARY_XOR (954, 216)
INFO:xpython.vm: @7266: LOAD_NAME dict
INFO:xpython.vm: @7637: BUILD_LIST 0
INFO:xpython.vm: @5069: LOAD_NAME __import__
INFO:xpython.vm: @6232: LOAD_CONST marshal
INFO:xpython.vm: @4648: CALL_FUNCTION (__import__) 1 positional, 0 named
INFO:xpython.vm: @8028: LOAD_ATTR loads
INFO:xpython.vm: @6832: LOAD_CONST eNpdmD2LKkkUhmf37geIGPSCgQwGBjKIdGDgDzAwkMFggg5c6MBAuCIGBv4AAwNxO5igA5EODAwGMTAwWDYyMJCLLCL9Aww6EOlAlonX8uJz9mxyqLKqznnPez6q2t9/fnp6evnxJr7++eU2+sGMkvz2202+/GpGayOGRtSN2BuR5reynDCjX8yoyup989yIjhFFNv9xM/fykxm5Dy1f/cfZ71sKZvT3l4eCnhEpI9qc8Iw4GlEy4h24MyMmRmSN+MeIjBFLI6ZGRKA6se8OPGdEBX0n1E/waGNEDOYTUxdAAyNGRlyN+IaCGgpyHMtwwgJ9jLBAsAZV/KR4GePRDM3CQQ6T4lH0CPd/TE7QF8FazIkBW8psuY8CoA1wP8fmNpvXWDuB5b65jwt99j2D4GDEBxwcWVgxvcB9wghH77svtIxosNDAmguTb4TnirUsNGWBcc/srhELTGZwtY2qsxE2+AJGR07cleY1vgRaPIxXWPgkliWI3ZDKNVC1dWnMyPuALD5iN0VQ2oxeiYK4H6EvQaCukNgEhnhU1Mk/JzcCcm2KC+JbmeqJsZbGmsNvz8AooioJ+tOjjXzX8k7cBugrMi2TUneyd4DcsLBDc1pHJoODM73Fwm4T4xGrWxRIfyni5RloAal3RoGL5yuI9THkwu6BjLUB9MmCw9mWpsnB8x7AA5B2UbDF6QJu+WTYmlpwyM4+WXLlWB19Cc5uQeVgY0AJdTR/0kqXqDqDRQrb1r3JhisLzTIKCe0BNq66yViYzGPojZukoGt1A+YUdsfUucBNU4hjSKwQ6S4Z9s6xOkG2cGtHii7ohM/gC6lpm+mZmjnqYsqTf55u9VmMt5gmQPoBk3v0fdAPQkrcIih1fJPeniL6PnAzjCSRdqCv89sEzDGaM5rdOV6WdH/xod0nlj4mu2he6Us9DTk9/ZutA1+GnDRVewGQh4Ihbs3B1yRafaxVONEmZHk2T3B/ra+xKZSUtDNb/JV3jrybpuirgGWD6OpkyBOUI6rq0D5kX6DTJ4/nPfB1mC5gsgiJCVxNcZuO9DXRxP0IG1tiPsGjV4p4wbEBeVrARgJX5VgMJXvq7QSxHbRIV6nRRsa4ekFplWLvAbKDNUf3XXnizEBfA6ncGkuOOeArozQgCicSJIlbUxrKFgdT+lXqUecbnaLySFjox528uUbAfcfagNUWoypnLfKgioMOkTnhqqcvNBvMPYS8ckP0ORDbJXcbUFLFeAiWEazNWUgR3wmpV2LfSPeIEWRnubHTsDaEziWtr0HtN3X9hmTsHmFjY6O7VAd/k5ytkbF54KaZzvS7xMLBHf6uwNzRfbxGlsw422XkkwIRJ+RefWZ1TicM2bdncwm4ZRiakHotoMn9a8GfvMctPC+SAhd9X9ZJPblYTmSdsNFA+HA/1vdWESLeqIAtdemRFg4V8L/Hp08+N0kam5D1UTpEeKwe9LdazMIUxuXBYoFeviHW+pEw1VFYsCC5O9J9fM7UhaEhSgMi7REU+ZqoQESWtHWxmwXQJ8bLGrOkihDxCdnylSrA67Cx1LF0iUwTrkJUyaegVE+ku0UJuBdaboEge1SUp19LS+wmdYNPQaeDCxHlUiDNYl26SVyV727JXcmcHOQ47AtJ6hAiclTAK6ik3QT6P4ouXkaALACoxtQlrxaETP7BaLMq3TsiyCt9WW/pL5K7Hv7K7dLS0Lb6vRvrv3LkK1W+Eg66GitsyaB5DC93pX/dxL//a4kn
INFO:xpython.vm: @4908: LOAD_ATTR decode
INFO:xpython.vm: @4959: LOAD_CONST base64
INFO:xpython.vm: @6483: CALL_FUNCTION (decode) 1 positional, 0 named
INFO:xpython.vm: @7383: LOAD_ATTR decode
[培训]传播安全知识、拓宽行业人脉——看雪讲师团队等你加入!
赞赏
- [原创]Brute Ratel C4 Keygen 17847
- [原创]KCTF 2022春季赛 第九题 同归于尽 6873
- [原创]KCTF 2022春季赛 第四题 飞蛾扑火 4445
- [原创]KCTF 2021秋季赛 第九题 万事俱备 21189
- [原创]KCTF 2021秋季赛 第七题 声名远扬 20632