|
|
[原创]MFC程序逆向 – 消息篇(上)+(下) 11楼
...... |
|
|
[求助]关于寄存器断点
设置条件断点就行了,如 eax==110 |
|
|
|
|
|
|
|
|
[求助]去除Shell.exe 病毒(附病毒样本)
怎么有这么多弟兄下载,却没有一个弟兄发表一下解决方案呢? ... ... 其实,这个病毒很容易去掉的。现在,我不到一分钟就可以将这个病毒干掉! 完全可以不用瑞星。像它那样在那里慢吞吞地查毒和杀毒,急死了 |
|
|
[求助]去除Shell.exe 病毒(附病毒样本)
我将病毒样本传给瑞星后,没想到瑞星动作很快,马上给了我回复,并且更新了病毒库,我更新瑞星杀毒软件后,经全盘杀毒,已完全去除此毒。 但不幸的是,C:\Windows\system32\spoolsv.exe下的这个文件,由于受病毒感染,也被瑞星清了,我的机子仍然无法加载打印驱动程序,不知哪位好心的兄弟能你机子上的此文件传一份给我(最好是XP系统的spoolsv.exe文件),小弟不甚感激! |
|
|
[求助]去除Shell.exe 病毒(附病毒样本)
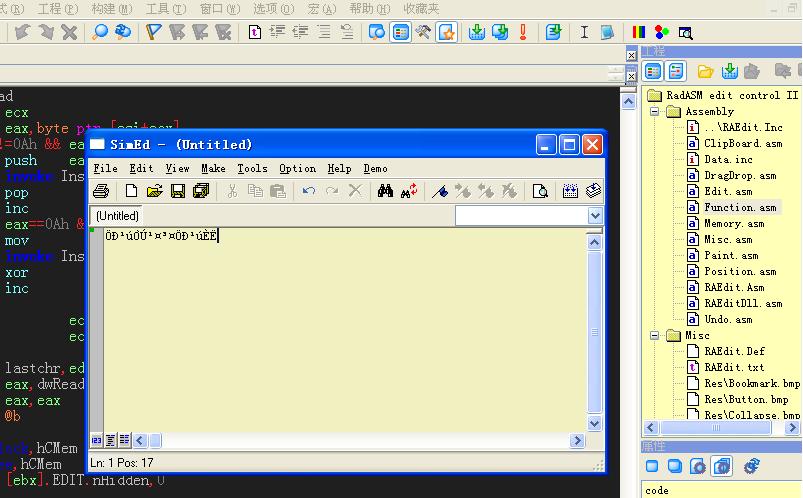
此毒用UPX加的壳,可以用OD加载调试,我想手动脱壳,但末成功,于是带壳分析: OD加载此毒后,跟踪来到OEP处,随后代码如下: 1315AABC 55 PUSH EBP 1315AABD 8BEC MOV EBP,ESP 1315AABF B9 0F000000 MOV ECX,0F 1315AAC4 6A 00 PUSH 0 1315AAC6 6A 00 PUSH 0 1315AAC8 49 DEC ECX 1315AAC9 ^ 75 F9 JNZ SHORT Shell.1315AAC4 1315AACB 53 PUSH EBX 1315AACC 56 PUSH ESI 1315AACD B8 CCA91513 MOV EAX,Shell.1315A9CC 1315AAD2 E8 DDB2FEFF CALL Shell.13145DB4 1315AAD7 33C0 XOR EAX,EAX 1315AAD9 55 PUSH EBP 1315AADA 68 7EAF1513 PUSH Shell.1315AF7E 1315AADF 64:FF30 PUSH DWORD PTR FS:[EAX] 1315AAE2 64:8920 MOV DWORD PTR FS:[EAX],ESP 1315AAE5 90 NOP 1315AAE6 90 NOP 1315AAE7 90 NOP 1315AAE8 90 NOP 1315AAE9 90 NOP 1315AAEA B8 04010000 MOV EAX,104 1315AAEF E8 E0D1FEFF CALL Shell.13147CD4 1315AAF4 A3 A8D91513 MOV DWORD PTR DS:[1315D9A8],EAX 1315AAF9 68 04010000 PUSH 104 1315AAFE A1 A8D91513 MOV EAX,DWORD PTR DS:[1315D9A8] 1315AB03 50 PUSH EAX 1315AB04 E8 CFB4FEFF CALL Shell.13145FD8 ; JMP 到 kernel32.GetSystemDirectoryA 1315AB09 8D55 EC LEA EDX,DWORD PTR SS:[EBP-14] 1315AB0C A1 A8D91513 MOV EAX,DWORD PTR DS:[1315D9A8] 1315AB11 E8 AAD1FEFF CALL Shell.13147CC0 1315AB16 8B55 EC MOV EDX,DWORD PTR SS:[EBP-14] 1315AB19 B8 1CDA1513 MOV EAX,Shell.1315DA1C 1315AB1E E8 5994FEFF CALL Shell.13143F7C 1315AB23 8D45 E8 LEA EAX,DWORD PTR SS:[EBP-18] 1315AB26 50 PUSH EAX 1315AB27 B9 03000000 MOV ECX,3 1315AB2C BA 01000000 MOV EDX,1 1315AB31 A1 1CDA1513 MOV EAX,DWORD PTR DS:[1315DA1C] 1315AB36 E8 E998FEFF CALL Shell.13144424 1315AB3B 8B55 E8 MOV EDX,DWORD PTR SS:[EBP-18] 1315AB3E B8 20DA1513 MOV EAX,Shell.1315DA20 1315AB43 B9 94AF1513 MOV ECX,Shell.1315AF94 ; ASCII "Program Files\Internet Explorer\IEXPLORE.EXE" 1315AB48 E8 C396FEFF CALL Shell.13144210 1315AB4D 8D55 E4 LEA EDX,DWORD PTR SS:[EBP-1C] 1315AB50 33C0 XOR EAX,EAX 1315AB52 E8 C57DFEFF CALL Shell.1314291C 1315AB57 8B45 E4 MOV EAX,DWORD PTR SS:[EBP-1C] 1315AB5A E8 EDF8FFFF CALL Shell.1315A44C 1315AB5F 8BD8 MOV EBX,EAX 1315AB61 8D45 E0 LEA EAX,DWORD PTR SS:[EBP-20] 1315AB64 B9 CCAF1513 MOV ECX,Shell.1315AFCC ; ASCII "\spoolsv.exe" 1315AB69 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315AB6F E8 9C96FEFF CALL Shell.13144210 1315AB74 8B45 E0 MOV EAX,DWORD PTR SS:[EBP-20] 1315AB77 E8 D0F8FFFF CALL Shell.1315A44C 1315AB7C 8BF0 MOV ESI,EAX 1315AB7E E8 61F9FFFF CALL Shell.1315A4E4 1315AB83 E8 B098FFFF CALL Shell.13154438 1315AB88 6A 00 PUSH 0 1315AB8A 68 DCAF1513 PUSH Shell.1315AFDC ; ASCII "net stop server /y" 1315AB8F E8 64D6FFFF CALL Shell.131581F8 ; JMP 到 kernel32.WinExec 1315AB94 E8 0BEFFFFF CALL Shell.13159AA4 1315AB99 8D45 DC LEA EAX,DWORD PTR SS:[EBP-24] 1315AB9C BA F0AF1513 MOV EDX,Shell.1315AFF0 ; ASCII "c:\pass.dic" 1315ABA1 E8 7A95FEFF CALL Shell.13144120 1315ABA6 8B4D DC MOV ECX,DWORD PTR SS:[EBP-24] 1315ABA9 BA 04B01513 MOV EDX,Shell.1315B004 ; ASCII "Dedll1" 1315ABAE B8 14B01513 MOV EAX,Shell.1315B014 ; ASCII "dllfile1" 1315ABB3 E8 14D8FFFF CALL Shell.131583CC 1315ABB8 E8 1BE0FFFF CALL Shell.13158BD8 1315ABBD 81FB 00FC0000 CMP EBX,0FC00 1315ABC3 0F85 5F020000 JNZ Shell.1315AE28 1315ABC9 E8 06FDFFFF CALL Shell.1315A8D4 1315ABCE 84C0 TEST AL,AL 1315ABD0 0F84 8D030000 JE Shell.1315AF63 1315ABD6 68 98D91513 PUSH Shell.1315D998 1315ABDB 68 54D91513 PUSH Shell.1315D954 1315ABE0 6A 00 PUSH 0 1315ABE2 6A 00 PUSH 0 1315ABE4 6A 04 PUSH 4 1315ABE6 6A 00 PUSH 0 1315ABE8 6A 00 PUSH 0 1315ABEA 6A 00 PUSH 0 1315ABEC A1 A8D91513 MOV EAX,DWORD PTR DS:[1315D9A8] 1315ABF1 50 PUSH EAX 1315ABF2 6A 00 PUSH 0 1315ABF4 E8 E7B2FEFF CALL Shell.13145EE0 ; JMP 到 kernel32.CreateProcessA 1315ABF9 68 F4010000 PUSH 1F4 1315ABFE E8 7510FFFF CALL Shell.1314BC78 ; JMP 到 kernel32.Sleep 1315AC03 A1 A0D91513 MOV EAX,DWORD PTR DS:[1315D9A0] 1315AC08 50 PUSH EAX 1315AC09 6A 00 PUSH 0 1315AC0B 68 FF0F1F00 PUSH 1F0FFF 1315AC10 E8 3BB4FEFF CALL Shell.13146050 ; JMP 到 kernel32.OpenProcess 1315AC15 8BD8 MOV EBX,EAX 1315AC17 BA 24A71513 MOV EDX,Shell.1315A724 1315AC1C 8BC3 MOV EAX,EBX 1315AC1E E8 41FCFFFF CALL Shell.1315A864 1315AC23 53 PUSH EBX 1315AC24 E8 8FB2FEFF CALL Shell.13145EB8 ; JMP 到 kernel32.CloseHandle 1315AC29 68 20030000 PUSH 320 1315AC2E E8 4510FFFF CALL Shell.1314BC78 ; JMP 到 kernel32.Sleep 1315AC33 8D55 D8 LEA EDX,DWORD PTR SS:[EBP-28] 1315AC36 33C0 XOR EAX,EAX 1315AC38 E8 DF7CFEFF CALL Shell.1314291C 1315AC3D 8B45 D8 MOV EAX,DWORD PTR SS:[EBP-28] 1315AC40 E8 7F97FEFF CALL Shell.131443C4 1315AC45 8BD8 MOV EBX,EAX 1315AC47 8D45 D4 LEA EAX,DWORD PTR SS:[EBP-2C] 1315AC4A B9 28B01513 MOV ECX,Shell.1315B028 ; ASCII "\Shell.exe" 1315AC4F 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315AC55 E8 B695FEFF CALL Shell.13144210 1315AC5A 8B45 D4 MOV EAX,DWORD PTR SS:[EBP-2C] 1315AC5D E8 6297FEFF CALL Shell.131443C4 1315AC62 3BD8 CMP EBX,EAX 1315AC64 0F84 B4010000 JE Shell.1315AE1E 1315AC6A 81FE 00FC0000 CMP ESI,0FC00 1315AC70 0F84 36010000 JE Shell.1315ADAC 1315AC76 833D B0D91513 0>CMP DWORD PTR DS:[1315D9B0],1 1315AC7D 1BC0 SBB EAX,EAX 1315AC7F 40 INC EAX 1315AC80 3C 01 CMP AL,1 1315AC82 0F85 AD000000 JNZ Shell.1315AD35 1315AC88 E8 8FD4FFFF CALL Shell.1315811C 1315AC8D B8 3CB01513 MOV EAX,Shell.1315B03C ; ASCII "spoolsv.exe" 1315AC92 E8 69D5FFFF CALL Shell.13158200 1315AC97 68 90010000 PUSH 190 1315AC9C E8 D70FFFFF CALL Shell.1314BC78 ; JMP 到 kernel32.Sleep 1315ACA1 8D45 D0 LEA EAX,DWORD PTR SS:[EBP-30] 1315ACA4 B9 CCAF1513 MOV ECX,Shell.1315AFCC ; ASCII "\spoolsv.exe" 1315ACA9 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315ACAF E8 5C95FEFF CALL Shell.13144210 1315ACB4 8B45 D0 MOV EAX,DWORD PTR SS:[EBP-30] 1315ACB7 E8 40CDFEFF CALL Shell.131479FC 1315ACBC 6A 64 PUSH 64 1315ACBE E8 B50FFFFF CALL Shell.1314BC78 ; JMP 到 kernel32.Sleep 1315ACC3 6A 00 PUSH 0 1315ACC5 8D45 CC LEA EAX,DWORD PTR SS:[EBP-34] 1315ACC8 B9 CCAF1513 MOV ECX,Shell.1315AFCC ; ASCII "\spoolsv.exe" 1315ACCD 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315ACD3 E8 3895FEFF CALL Shell.13144210 1315ACD8 8B45 CC MOV EAX,DWORD PTR SS:[EBP-34] 1315ACDB E8 E496FEFF CALL Shell.131443C4 1315ACE0 50 PUSH EAX 1315ACE1 8D55 C8 LEA EDX,DWORD PTR SS:[EBP-38] 1315ACE4 33C0 XOR EAX,EAX 1315ACE6 E8 317CFEFF CALL Shell.1314291C 1315ACEB 8B45 C8 MOV EAX,DWORD PTR SS:[EBP-38] 1315ACEE E8 D196FEFF CALL Shell.131443C4 1315ACF3 50 PUSH EAX 1315ACF4 E8 CFB1FEFF CALL Shell.13145EC8 ; JMP 到 kernel32.CopyFileA 1315ACF9 8D45 C0 LEA EAX,DWORD PTR SS:[EBP-40] 1315ACFC B9 CCAF1513 MOV ECX,Shell.1315AFCC ; ASCII "\spoolsv.exe" 1315AD01 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315AD07 E8 0495FEFF CALL Shell.13144210 1315AD0C 8B45 C0 MOV EAX,DWORD PTR SS:[EBP-40] 1315AD0F E8 B096FEFF CALL Shell.131443C4 1315AD14 8BD0 MOV EDX,EAX 1315AD16 8D45 C4 LEA EAX,DWORD PTR SS:[EBP-3C] 1315AD19 E8 0294FEFF CALL Shell.13144120 1315AD1E 8B45 C4 MOV EAX,DWORD PTR SS:[EBP-3C] 1315AD21 BA 02000000 MOV EDX,2 1315AD26 E8 B5CBFEFF CALL Shell.131478E0 1315AD2B E8 5CF6FFFF CALL Shell.1315A38C 1315AD30 E9 2E020000 JMP Shell.1315AF63 1315AD35 6A 00 PUSH 0 1315AD37 8D45 BC LEA EAX,DWORD PTR SS:[EBP-44] 1315AD3A B9 28B01513 MOV ECX,Shell.1315B028 ; ASCII "\Shell.exe" 1315AD3F 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315AD45 E8 C694FEFF CALL Shell.13144210 1315AD4A 8B45 BC MOV EAX,DWORD PTR SS:[EBP-44] 1315AD4D E8 7296FEFF CALL Shell.131443C4 1315AD52 50 PUSH EAX 1315AD53 8D55 B8 LEA EDX,DWORD PTR SS:[EBP-48] 1315AD56 33C0 XOR EAX,EAX 1315AD58 E8 BF7BFEFF CALL Shell.1314291C 1315AD5D 8B45 B8 MOV EAX,DWORD PTR SS:[EBP-48] 1315AD60 E8 5F96FEFF CALL Shell.131443C4 1315AD65 50 PUSH EAX 1315AD66 E8 5DB1FEFF CALL Shell.13145EC8 ; JMP 到 kernel32.CopyFileA 1315AD6B 8D45 B0 LEA EAX,DWORD PTR SS:[EBP-50] 1315AD6E B9 28B01513 MOV ECX,Shell.1315B028 ; ASCII "\Shell.exe" 1315AD73 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315AD79 E8 9294FEFF CALL Shell.13144210 1315AD7E 8B45 B0 MOV EAX,DWORD PTR SS:[EBP-50] 1315AD81 E8 3E96FEFF CALL Shell.131443C4 1315AD86 8BD0 MOV EDX,EAX 1315AD88 8D45 B4 LEA EAX,DWORD PTR SS:[EBP-4C] 1315AD8B E8 9093FEFF CALL Shell.13144120 1315AD90 8B45 B4 MOV EAX,DWORD PTR SS:[EBP-4C] 1315AD93 BA 02000000 MOV EDX,2 1315AD98 E8 43CBFEFF CALL Shell.131478E0 1315AD9D E8 92E9FFFF CALL Shell.13159734 1315ADA2 E8 E5F5FFFF CALL Shell.1315A38C 1315ADA7 E9 B7010000 JMP Shell.1315AF63 1315ADAC 6A 00 PUSH 0 1315ADAE 8D45 AC LEA EAX,DWORD PTR SS:[EBP-54] 1315ADB1 B9 28B01513 MOV ECX,Shell.1315B028 ; ASCII "\Shell.exe" 1315ADB6 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315ADBC E8 4F94FEFF CALL Shell.13144210 1315ADC1 8B45 AC MOV EAX,DWORD PTR SS:[EBP-54] 1315ADC4 E8 FB95FEFF CALL Shell.131443C4 1315ADC9 50 PUSH EAX 1315ADCA 8D55 A8 LEA EDX,DWORD PTR SS:[EBP-58] 1315ADCD 33C0 XOR EAX,EAX 1315ADCF E8 487BFEFF CALL Shell.1314291C 1315ADD4 8B45 A8 MOV EAX,DWORD PTR SS:[EBP-58] 1315ADD7 E8 E895FEFF CALL Shell.131443C4 1315ADDC 50 PUSH EAX 1315ADDD E8 E6B0FEFF CALL Shell.13145EC8 ; JMP 到 kernel32.CopyFileA 1315ADE2 8D45 A0 LEA EAX,DWORD PTR SS:[EBP-60] 1315ADE5 B9 28B01513 MOV ECX,Shell.1315B028 ; ASCII "\Shell.exe" 1315ADEA 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315ADF0 E8 1B94FEFF CALL Shell.13144210 1315ADF5 8B45 A0 MOV EAX,DWORD PTR SS:[EBP-60] 1315ADF8 E8 C795FEFF CALL Shell.131443C4 1315ADFD 8BD0 MOV EDX,EAX 1315ADFF 8D45 A4 LEA EAX,DWORD PTR SS:[EBP-5C] 1315AE02 E8 1993FEFF CALL Shell.13144120 1315AE07 8B45 A4 MOV EAX,DWORD PTR SS:[EBP-5C] 1315AE0A BA 02000000 MOV EDX,2 1315AE0F E8 CCCAFEFF CALL Shell.131478E0 1315AE14 E8 73F5FFFF CALL Shell.1315A38C 1315AE19 E9 45010000 JMP Shell.1315AF63 1315AE1E E8 69F5FFFF CALL Shell.1315A38C 1315AE23 E9 3B010000 JMP Shell.1315AF63 1315AE28 BA 18DA1513 MOV EDX,Shell.1315DA18 1315AE2D 33C0 XOR EAX,EAX 1315AE2F E8 E87AFEFF CALL Shell.1314291C 1315AE34 A1 18DA1513 MOV EAX,DWORD PTR DS:[1315DA18] 1315AE39 E8 8693FEFF CALL Shell.131441C4 1315AE3E 8BD0 MOV EDX,EAX 1315AE40 83EA 04 SUB EDX,4 1315AE43 B8 18DA1513 MOV EAX,Shell.1315DA18 1315AE48 B9 04000000 MOV ECX,4 1315AE4D E8 1296FEFF CALL Shell.13144464 1315AE52 FF35 18DA1513 PUSH DWORD PTR DS:[1315DA18] 1315AE58 68 50B01513 PUSH Shell.1315B050 ; ASCII "1L1~" 1315AE5D 68 60B01513 PUSH Shell.1315B060 ; ASCII ".exe" 1315AE62 B8 18DA1513 MOV EAX,Shell.1315DA18 1315AE67 BA 03000000 MOV EDX,3 1315AE6C E8 1394FEFF CALL Shell.13144284 1315AE71 A1 18DA1513 MOV EAX,DWORD PTR DS:[1315DA18] 1315AE76 E8 CDD6FFFF CALL Shell.13158548 1315AE7B 6A 64 PUSH 64 1315AE7D E8 F60DFFFF CALL Shell.1314BC78 ; JMP 到 kernel32.Sleep 1315AE82 A1 18DA1513 MOV EAX,DWORD PTR DS:[1315DA18] 1315AE87 E8 3895FEFF CALL Shell.131443C4 1315AE8C 8BD0 MOV EDX,EAX 1315AE8E 8D45 9C LEA EAX,DWORD PTR SS:[EBP-64] 1315AE91 E8 8A92FEFF CALL Shell.13144120 1315AE96 8B45 9C MOV EAX,DWORD PTR SS:[EBP-64] 1315AE99 BA 02000000 MOV EDX,2 1315AE9E E8 3DCAFEFF CALL Shell.131478E0 1315AEA3 6A 0A PUSH 0A 1315AEA5 A1 18DA1513 MOV EAX,DWORD PTR DS:[1315DA18] 1315AEAA E8 1595FEFF CALL Shell.131443C4 1315AEAF 50 PUSH EAX 1315AEB0 E8 43D3FFFF CALL Shell.131581F8 ; JMP 到 kernel32.WinExec 1315AEB5 833D ACD91513 0>CMP DWORD PTR DS:[1315D9AC],1 1315AEBC 1BC0 SBB EAX,EAX 1315AEBE 40 INC EAX 1315AEBF 3C 01 CMP AL,1 1315AEC1 0F84 9C000000 JE Shell.1315AF63 1315AEC7 8D45 98 LEA EAX,DWORD PTR SS:[EBP-68] 1315AECA B9 28B01513 MOV ECX,Shell.1315B028 ; ASCII "\Shell.exe" 1315AECF 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315AED5 E8 3693FEFF CALL Shell.13144210 1315AEDA 8B45 98 MOV EAX,DWORD PTR SS:[EBP-68] 1315AEDD E8 1ACBFEFF CALL Shell.131479FC 1315AEE2 68 C8000000 PUSH 0C8 1315AEE7 E8 8C0DFFFF CALL Shell.1314BC78 ; JMP 到 kernel32.Sleep 1315AEEC 8D45 94 LEA EAX,DWORD PTR SS:[EBP-6C] 1315AEEF B9 28B01513 MOV ECX,Shell.1315B028 ; ASCII "\Shell.exe" 1315AEF4 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315AEFA E8 1193FEFF CALL Shell.13144210 1315AEFF 8B45 94 MOV EAX,DWORD PTR SS:[EBP-6C] 1315AF02 E8 6DD7FFFF CALL Shell.13158674 1315AF07 6A 64 PUSH 64 1315AF09 E8 6A0DFFFF CALL Shell.1314BC78 ; JMP 到 kernel32.Sleep 1315AF0E 8D45 8C LEA EAX,DWORD PTR SS:[EBP-74] 1315AF11 B9 28B01513 MOV ECX,Shell.1315B028 ; ASCII "\Shell.exe" 1315AF16 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315AF1C E8 EF92FEFF CALL Shell.13144210 1315AF21 8B45 8C MOV EAX,DWORD PTR SS:[EBP-74] 1315AF24 E8 9B94FEFF CALL Shell.131443C4 1315AF29 8BD0 MOV EDX,EAX 1315AF2B 8D45 90 LEA EAX,DWORD PTR SS:[EBP-70] 1315AF2E E8 ED91FEFF CALL Shell.13144120 1315AF33 8B45 90 MOV EAX,DWORD PTR SS:[EBP-70] 1315AF36 BA 02000000 MOV EDX,2 1315AF3B E8 A0C9FEFF CALL Shell.131478E0 1315AF40 6A 00 PUSH 0 1315AF42 8D45 88 LEA EAX,DWORD PTR SS:[EBP-78] 1315AF45 B9 70B01513 MOV ECX,Shell.1315B070 ; ASCII "\Shell.Exe" 1315AF4A 8B15 1CDA1513 MOV EDX,DWORD PTR DS:[1315DA1C] 1315AF50 E8 BB92FEFF CALL Shell.13144210 1315AF55 8B45 88 MOV EAX,DWORD PTR SS:[EBP-78] 1315AF58 E8 6794FEFF CALL Shell.131443C4 1315AF5D 50 PUSH EAX 1315AF5E E8 95D2FFFF CALL Shell.131581F8 ; JMP 到 kernel32.WinExec 1315AF63 33C0 XOR EAX,EAX 1315AF65 5A POP EDX 1315AF66 59 POP ECX 1315AF67 59 POP ECX 1315AF68 64:8910 MOV DWORD PTR FS:[EAX],EDX 1315AF6B 68 85AF1513 PUSH Shell.1315AF85 1315AF70 8D45 88 LEA EAX,DWORD PTR SS:[EBP-78] 1315AF73 BA 1A000000 MOV EDX,1A 1315AF78 E8 CF8FFEFF CALL Shell.13143F4C 1315AF7D C3 RETN 1315AF7E ^ E9 CD89FEFF JMP Shell.13143950 1315AF83 ^ EB EB JMP SHORT Shell.1315AF70 1315AF85 5E POP ESI 1315AF86 5B POP EBX 1315AF87 E8 AC8EFEFF CALL Shell.13143E38 从上面代码可以看出个大概,运行时病毒会在系统目录下会创建如下文件:spoolsv.exe,Shell.exe,shell.pci,还会在C盘根目录下创建:pass.dic文件。 我想,可能正是这个spoolsv.exe文件造成了计算机无法加载打印驱动程序!由于我的水平实在太菜,无法继续往下分析,恳请高手指点,如何杀掉此毒, 这几天,我正急用打印机! 万分感谢!!! |
|
|
求助,如何用程序获得其它进程的窗口中一个edit控件的句柄
控件的ID值是不会变化的 |
|
|
[求助]这两个断有什么区别,菜鸟问题?
两个不同的函数,一个是生成对话框,一个是弹出消息框,两者消息处理机制不一样 |
|
|
[求助]OD堆栈区上为什么不能设内存断点?
没人回答,我就自已解决: 一、先用汇编写一段最简单的测试程序: start: nop nop push eax <=== 1 pop ebx <=== 2 nop nop ret end start OD加载后,ESP=0012FFC4 在0012FFC0处设置内存访问断点,F9运行,OD中断在push eax语句上,再F9,OD中断在 pop ebx 上,这都很正确。再F9,问题就来了,OD出现“访问违规,正在执行[00000000] - 使用 Shift+F7/F8/F9来忽略异常" OD重新加载上述程序:在0012FFC0处设置内存写入断点,F9运行,OD中断在 push eax 上,这很正确。再F9,程序正常退出。 有点怪:在堆栈区可以设置“内存写入”断点,而不能设置“内存访问”断点??? ======================================================================================= 再来一段测试程序: start: nop nop mov eax,[esp] mov [esp],eax nop ret end start 同样进行上述测试,由于这段程序是直接对[esp]操作,所以,应在0012FFC4上进行断点设置,经测试,发现在0012FFC4上设置“内存写入”断点和设置“内存访问”断点,都很正常, 程序均能按预想方式中断,并能正常退出。 这就把我弄糊涂了,难道是 push指令 和 move指令不同造成了上述现象?但这两个条指令都是访问内存指令啊? 请对内存断点有深切理解的高手们来探讨一下这个问题 |
|
|
|
|
|
我要定时刷新一个窗口怎么编程
网上资料大把 |
|
|
[求助]为什么窗口不能置前 (VC编程)?
很简单,对记事本发送一条WM_SYSCOMMAND消息,让它恢复窗口不就行了 |
|
|
[求助]编程什么语言好
为什么大家都说用VB开发界面好,我个人认为用C++更好,用好C++对于类和对象的封装功能,在界面,开发速度更快 |
|
|
.Net 程序的困惑
目前,我实在是不想转入.Net中来, 因为装vista系统的用户实在不多,用VC编译出来的程序短小精焊,维护也很容易. 我担心的是,MS老大们哪一天突发神经, 他们为了全面促进.Net, 而在新的操作系统上不理会VC或VB的编译出来的程序,从而会引起不兼容. 我有过这样的经历:几年前,辛辛苦苦用EVB开发出PDA上的一套程序,用户用到不到半年,PDA的WinCE4.0系统出来了,居然不支持EVB的程序,于是我又花了一两个月的时间用EVC进行开发.现在,PDA上已经是WinCE5.0系统了,那套EVC程序在WinCE5.0系统运行经常有些问题.看来,需要用.Net来开发PDA的程序了!!! 如果,MS长期这样, 我们做程序员的还不累死! |
|
|
[原创]Super Knife 升级了 (V1.02
哇,太好了,多谢老大! |
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值