|
|
[公告]成立看雪Web安全小组通告
报名,留qq,方便联系 |
|
|
[分享][原创]服务器文件监测脚本
1、邮箱帐号可以临时设置个普通的,没什么价值信息; 2、如果是网站直接root权限,能ps干掉这个进程,是通过webshell也好,其他口令破解登录系统也好,这个过程中或多或少已经有文件异常触发告急行为了,已经有预警邮件发出,py这个进程可以弄个守护进程;非root权限网站,提取过程中,本地溢出提权,也会有文件异常,这个小脚本只是预警..不要奢望过高 |
|
|
[注意]走进企业看安全(第5站)-“中国平安”站活动预告
可以,先报名、人数有限 |
|
|
[求助]安全小白
web安全可以重点看看handbook系列,the web application hackers handbook[黑客攻防技术宝典Web实战篇(第2版)。 |
|
|
[原创]J2EE漏洞与OWASP ESAPI修复方案之(URL_Redirection)
2.1、XSS跨站脚本漏洞介绍 XSS跨站脚本漏洞网上资料很多,就不具体名词介绍了,主要产生原因就是一些可输入的位置(多见用户交互功能页面,如留言板、论坛等等)插入了不可信的数据(html、js)内容,比如这些地方: <script>...NEVER PUT UNTRUSTED DATA HERE...</script> directly in a script <!--...NEVER PUT UNTRUSTED DATA HERE...--> inside an HTML comment <div ...NEVER PUT UNTRUSTED DATA HERE...=test /> in an attribute name <a NEVER PUT UNTRUSTED DATA HERE... href="/test" /> in a tag name <style>...NEVER PUT UNTRUSTED DATA HERE...</style> directly in CSS {"Message":"dev.net.ie/api/pay/.html?HouseNumber=9&AddressLine =The+Gardens"&NEVER PUT UNTRUSTED DATA H&AddressLine2=foxlodge+woods&TownName=Meath'.","MessageDetail":"No type was found that matches the controller named 'pay'."} in JSON, 2.2、安全修复方案 2.2.1、HTTP请求时进行专义 请求时进行转义处理下面介绍使用filter的编写: a)、重写Filter类doFilter方法 import java.io.IOException; import javax.servlet.Filter; import javax.servlet.FilterChain; import javax.servlet.FilterConfig; import javax.servlet.ServletException; import javax.servlet.ServletRequest; import javax.servlet.ServletResponse; import javax.servlet.http.HttpServletRequest; public class XSSFilter implements Filter { @Override public void init(FilterConfig filterConfig) throws ServletException { } @Override public void destroy() { } @Override public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain) throws IOException, ServletException { chain.doFilter(new XSSRequestWrapper((HttpServletRequest) request), response); } } b)、Wrapper编写 import javax.servlet.http.HttpServletRequest; import javax.servlet.http.HttpServletRequestWrapper; import org.owasp.esapi.ESAPI; public class XSSRequestWrapper extends HttpServletRequestWrapper { public XSSRequestWrapper(HttpServletRequest servletRequest) { super(servletRequest); } @Override public String[] getParameterValues(String parameter) { String[] values = super.getParameterValues(parameter); if (values == null) { return null; } int count = values.length; String[] encodedValues = new String[count]; for (int i = 0; i < count; i++) { encodedValues[i] = stripXSS(values[i]); } return encodedValues; } @Override public String getParameter(String parameter) { String value = super.getParameter(parameter); return stripXSS(value); } @Override public String getHeader(String name) { String value = super.getHeader(name); return stripXSS(value); } private String stripXSS(String value) { if (value != null) { // 强烈推荐使用esapi进行专义,不要通过正则去过滤非法标签 value = ESAPI.encoder().encodeForHTML(value); // Avoid null characters /** value = value.replaceAll("", ""); // Avoid anything between script tags Pattern scriptPattern = Pattern.compile("<script>(.*?)</script>",Pattern.CASE_INSENSITIVE); value = scriptPattern.matcher(value).replaceAll(""); // Avoid anything in a src='...' type of expression scriptPattern = Pattern.compile("src[\r\n]*=[\r\n]*\\\'(.*?)\\\'",Pattern.CASE_INSENSITIVE | Pattern.MULTILINE| Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // Remove any lonesome </script> tag scriptPattern = Pattern.compile("</script>",Pattern.CASE_INSENSITIVE); value = scriptPattern.matcher(value).replaceAll(""); // Remove any lonesome <script ...> tag scriptPattern = Pattern.compile("<script(.*?)>",Pattern.CASE_INSENSITIVE | Pattern.MULTILINE| Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // Remove any lonesome <input ...> tag scriptPattern = Pattern.compile("<input(.*?)>",Pattern.CASE_INSENSITIVE | Pattern.MULTILINE| Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // Remove any lonesome <iframe ...> tag scriptPattern = Pattern.compile("<iframe(.*?)>",Pattern.CASE_INSENSITIVE | Pattern.MULTILINE| Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // Avoid eval(...) expressions scriptPattern = Pattern.compile("eval\\((.*?)\\)",Pattern.CASE_INSENSITIVE | Pattern.MULTILINE| Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // Avoid expression(...) expressions scriptPattern = Pattern.compile("expression\\((.*?)\\)",Pattern.CASE_INSENSITIVE | Pattern.MULTILINE| Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // Avoid javascript:... expressions scriptPattern = Pattern.compile("javascript:",Pattern.CASE_INSENSITIVE); value = scriptPattern.matcher(value).replaceAll(""); // Avoid vbscript:... expressions scriptPattern = Pattern.compile("vbscript:",Pattern.CASE_INSENSITIVE); value = scriptPattern.matcher(value).replaceAll(""); // Avoid onload,onmouseover,onmouseout expressions scriptPattern = Pattern.compile("on(load|mouseover|mouseout|error)(.*?)=",Pattern.CASE_INSENSITIVE | Pattern.MULTILINE| Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // Avoid alert,confirm,prompt scriptPattern = Pattern.compile("(alert|confirm|prompt)(.*?)=",Pattern.CASE_INSENSITIVE | Pattern.MULTILINE| Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); **/ } return value; } } c)、配置web.xml <?xml version="1.0" encoding="UTF-8"?> <web-app xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns="http://java.sun.com/xml/ns/javaee" xmlns:web="http://java.sun.com/xml/ns/javaee/web-app_2_5.xsd" xsi:schemaLocation="http://java.sun.com/xml/ns/javaee http://java.sun.com/xml/ns/javaee/web-app_3_0.xsd" id="WebApp_ID" version="3.0"> <display-name>enterprise_security_esapi</display-name> <welcome-file-list> <welcome-file>index.html</welcome-file> <welcome-file>index.htm</welcome-file> <welcome-file>index.jsp</welcome-file> <welcome-file>default.html</welcome-file> <welcome-file>default.htm</welcome-file> <welcome-file>default.jsp</welcome-file> </welcome-file-list> <filter> <filter-name>demo1</filter-name> <filter-class>com.enterprise.security.XSSFilter</filter-class> </filter> <filter-mapping> <filter-name>demo1</filter-name> <url-pattern>/*</url-pattern> </filter-mapping> </web-app> 2.2.2、HTTP响应输出时转义 Http响应时可能输出在不同位置,分别调用不同ESAPI专义方法: 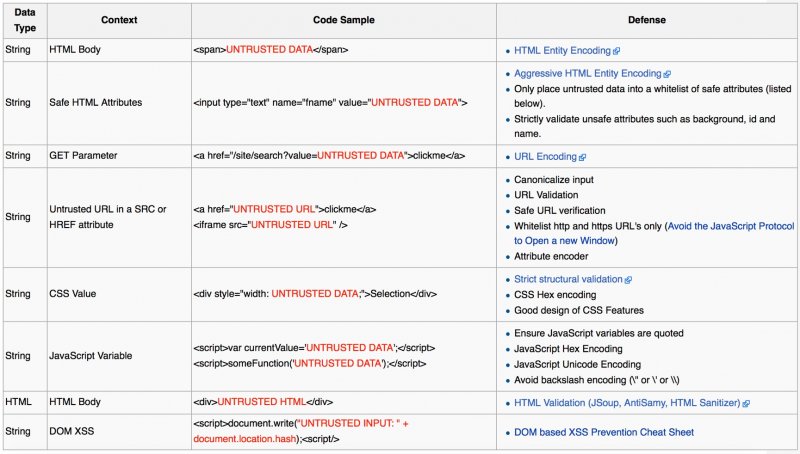 a)、HTML Escape Before Inserting Untrusted Data into HTML Element Content 输出内容在<body></div>等html元素范围: <body>...ESCAPE UNTRUSTED DATA BEFORE PUTTING HERE...</body> <div>...ESCAPE UNTRUSTED DATA BEFORE PUTTING HERE...</div> 对应ESAPI修复方案: String safe = ESAPI.encoder().encodeForHTML( request.getParameter( "input" ) ); b)、Attribute Escape Before Inserting Untrusted Data into HTML Common Attributes 输出内容在HTML Attributes属性值范围: <div attr=...ESCAPE UNTRUSTED DATA BEFORE PUTTING HERE...>content</div> inside UNquoted attribute <div attr='...ESCAPE UNTRUSTED DATA BEFORE PUTTING HERE...'>content</div> inside single quoted attribute <div attr="...ESCAPE UNTRUSTED DATA BEFORE PUTTING HERE...">content</div> inside double quoted attribute 对应ESAPI修复方案: String safe = ESAPI.encoder().encodeForHTMLAttribute( request.getParameter( "input" ) ); c)、JavaScript Escape Before Inserting Untrusted Data into JavaScript Data Values 输出内容在javascript data value范围: <script>alert('...ESCAPE UNTRUSTED DATA BEFORE PUTTING HERE...')</script> inside a quoted string <script>x='...ESCAPE UNTRUSTED DATA BEFORE PUTTING HERE...'</script> one side of a quoted expression <div onmouseover="x='...ESCAPE UNTRUSTED DATA BEFORE PUTTING HERE...'"</div> inside quoted event handler 对应ESAPI修复方案: String safe = ESAPI.encoder().encodeForJavaScript( request.getParameter( "input" ) ); d)、HTML escape JSON values in an HTML context and read the data with JSON.parse 输出内容为json模式: {"Message":"No HTTP resource was found that matches the request URI 'dev.net.ie/api/pay/.html?HouseNumber=9&AddressLine =The+Gardens<script>alert(1)</script>&AddressLine2=foxlodge+woods&TownName=Meath'.","MessageDetail":"No type was foundthat matches the controller named 'pay'."} <-- this script will pop!! 对应修复建议: 确保返回的Content-Type类型为application /JSON,而不是text / html的。从而确保不执行脚本注入。 response.setCharacterEncoding("UTF-8"); response.setContentType("application/json; charset=utf-8"); //response.setContentType("text/html; charset=utf-8"); String json = "{\"name\":\"piaox\",\"age\":\"30<script>alert(1)</script>\"}"; response.getWriter().println(json); e)、CSS Escape And Strictly Validate Before Inserting Untrusted Data into HTML Style 输出内容在html style部分: { background-url : "javascript:alert(1)"; } // and all other URLs { text-size: "expression(alert('XSS'))"; } // only in IE 对应修复建议: String safe = ESAPI.encoder().encodeForCSS( request.getParameter( "input" ) ); f)、URL Escape Before Inserting Untrusted Data into HTML URL Parameter Values 输出内容在html url标签属性部分: <a href="http://www.somesite.com?test=...ESCAPE UNTRUSTED DATA BEFORE PUTTING HERE...">link</a > 对应修复建议: String safe = ESAPI.encoder().encodeForURL( request.getParameter( "input" ) ); |
|
|
[公告]欢迎piaox任『WEB安全』见习版主
大家多多关照!!!互相交流,希望web安全版块质量越来越高,大家同进步共成长。 |
|
|
[原创][分享]中小企业网站漏洞自监测脚本
乌云对国内的整体信息安全发展促进很大,模式确实值得反思,漏洞实属敏感,没用户授权,白帽子就是游走于“临界线”,始终在法律上是个不受保护的弱者,保不准随时哪天出个什么事。 |
|
|
[原创]多线程WEB安全日志分析脚本
apache日志可以分析的,只是正则是从ngx_lua_waf提取而已,记录攻击源头,这个正则优化下即可。 |
|
|
[原创]J2EE_WEB安全测试系列文章
可以的,没问题 |
|
|
[原创]J2EE_WEB安全测试系列文章
可以的,没问题 |
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值

