|
|
|
|
|
|
|
|
|
|
|
[求助]PE-Armor 0.46 -> China Cracking Group *脱壳之道
那位大哥能帮主一下!! |
|
|
[求助]写脱壳机中,脱FSG2.0想到的导入表新建问题
感觉我正要学的就是以上的东西啊 ,真的一点都不懂啊! |
|
|
[求助]PE-Armor 0.46 -> China Cracking Group *脱壳之道
脱壳后程序可以运行,用peid查看如下: 但是但.RSS,.iData.....等等没有正确显示,所以看不到资源。 不知道是脱的不对,还是应该怎么处理。 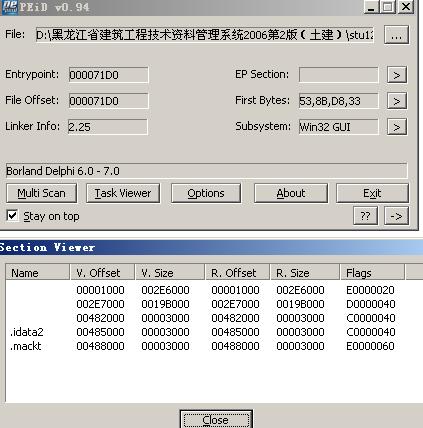
|
|
|
[求助]PE-Armor 0.46 -> China Cracking Group *脱壳之道
用OD载入程序,ALT+M,在代码断下断,取消断点 下命令bp GetProcAddress, F9运行,中断后取消断点. 来到: 00361BE6 0BC0 or eax, eax ; kernel32.7C800000 00361BE8 75 07 jnz short 00361BF1 00361BEA 56 push esi 00361BEB FF95 AC020000 call dword ptr [ebp+2AC] 00361BF1 0FB64E FF movzx ecx, byte ptr [esi-1] 00361BF5 03F1 add esi, ecx 00361BF7 8BD6 mov edx, esi 00361BF9 8BF0 mov esi, eax 00361BFB 42 inc edx 00361BFC 8B0A mov ecx, dword ptr [edx] 00361BFE 83C2 04 add edx, 4 00361C01 51 push ecx 00361C02 0FB602 movzx eax, byte ptr [edx] 00361C05 0BC0 or eax, eax 00361C07 75 14 jnz short 00361C1D 00361C09 42 inc edx 00361C0A 52 push edx 00361C0B 8B02 mov eax, dword ptr [edx] 00361C0D 50 push eax 00361C0E 56 push esi 00361C0F FF95 A4020000 call dword ptr [ebp+2A4] 00361C15 8907 mov dword ptr [edi], eax 00361C17 5A pop edx 00361C18 83C2 04 add edx, 4 00361C1B EB 13 jmp short 00361C30 00361C1D 42 inc edx 00361C1E 52 push edx 00361C1F 52 push edx 00361C20 56 push esi 00361C21 FF95 A4020000 call dword ptr [ebp+2A4] 00361C27 8907 mov dword ptr [edi], eax 00361C29 5A pop edx 00361C2A 0FB642 FF movzx eax, byte ptr [edx-1] 00361C2E 03D0 add edx, eax 00361C30 42 inc edx 00361C31 83C7 04 add edi, 4 00361C34 59 pop ecx 00361C35 ^ E2 CA loopd short 00361C01 00361C37 ^ EB 93 jmp short 00361BCC 00361C39 8B85 BC020000 mov eax, dword ptr [ebp+2BC] 00361C3F 83F8 01 cmp eax, 1 00361C42 75 27 jnz short 00361C6B 00361C44 8BBD C4020000 mov edi, dword ptr [ebp+2C4] 00361C4A 03FD add edi, ebp 00361C4C 8DB5 4D020000 lea esi, dword ptr [ebp+24D] 00361C52 8B07 mov eax, dword ptr [edi] 00361C54 0BC0 or eax, eax 00361C56 75 02 jnz short 00361C5A 00361C58 EB 11 jmp short 00361C6B 00361C5A 25 FFFFFF7F and eax, 7FFFFFFF 在此处打补丁 00361C5F 8BDE mov ebx, esi 00361C61 2BD8 sub ebx, eax 00361C63 8958 FC mov dword ptr [eax-4], ebx 00361C66 83C7 08 add edi, 8 补丁后返回这 00361C69 ^ EB E7 jmp short 00361C52 00361C6B 64:FF35 3000000>push dword ptr fs:[30] 00361C72 58 pop eax 00361C73 85C0 test eax, eax 00361C75 78 0F js short 00361C86 00361C77 8B40 0C mov eax, dword ptr [eax+C] 00361C7A 8B40 0C mov eax, dword ptr [eax+C] 00361C7D C740 20 0010000>mov dword ptr [eax+20], 1000 00361C84 EB 1C jmp short 00361CA2 00361C86 6A 00 push 0 00361C88 FF95 A8020000 call dword ptr [ebp+2A8] 00361C8E 85D2 test edx, edx 00361C90 79 10 jns short 00361CA2 00361C92 837A 08 FF cmp dword ptr [edx+8], -1 00361C96 75 0A jnz short 00361CA2 00361C98 8B52 04 mov edx, dword ptr [edx+4] 00361C9B C742 50 0010000>mov dword ptr [edx+50], 1000 00361CA2 89AD 58020000 mov dword ptr [ebp+258], ebp 00361CA8 8B85 C8020000 mov eax, dword ptr [ebp+2C8] 00361CAE 0385 B4020000 add eax, dword ptr [ebp+2B4] 00361CB4 FFE0 jmp eax 这里是OEP 00361CB6 50 push eax 00361CB7 8BC4 mov eax, esp 00361CB9 60 pushad 00361CBA 8BD8 mov ebx, eax 00361CBC E8 04000000 call 00361CC5 00361CC1 0000 add byte ptr [eax], al 00361CC3 0000 add byte ptr [eax], al 00361CC5 5D pop ebp 00361CC6 8B6D 00 mov ebp, dword ptr [ebp] 00361CC9 8B7B 04 mov edi, dword ptr [ebx+4] 00361CCC 8BB5 C4020000 mov esi, dword ptr [ebp+2C4] 00361CD2 03F5 add esi, ebp 00361CD4 8B06 mov eax, dword ptr [esi] 00361CD6 33D2 xor edx, edx 00361CD8 B9 02000000 mov ecx, 2 00361CDD F7E1 mul ecx 00361CDF D1E8 shr eax, 1 00361CE1 3BF8 cmp edi, eax 00361CE3 75 0A jnz short 00361CEF 00361CE5 0AD2 or dl, dl 00361CE7 75 04 jnz short 00361CED 00361CE9 EB 09 jmp short 00361CF4 00361CEB EB 02 jmp short 00361CEF 00361CED EB 10 jmp short 00361CFF 00361CEF 83C6 08 add esi, 8 00361CF2 ^ EB E0 jmp short 00361CD4 00361CF4 8B46 04 mov eax, dword ptr [esi+4] 00361CF7 8903 mov dword ptr [ebx], eax 补丁代码: 00384E00 807F 03 01 CMP BYTE PTR DS:[EDI+3],1////比较最高位是否为1。 00384E04 75 11 JNZ SHORT 00384E17 00384E06 8B5F 04 MOV EBX,DWORD PTR DS:[EDI+4]////正确的函数地址指针移入EBX。 00384E09 66:C740 FA FF15 MOV WORD PTR DS:[EAX-6],15FF 00384E0F 8958 FC MOV DWORD PTR DS:[EAX-4],EBX 00384E12 ^ E9 0AD7FFFF JMP 00361C66////跳回继续。 00384E17 25 FFFFFF7F AND EAX,7FFFFFFF////取消最高位。 00384E1C 8B5F 04 MOV EBX,DWORD PTR DS:[EDI+4] 00384E1F 66:C740 FA FF25 MOV WORD PTR DS:[EAX-6],25FF 00384E25 8958 FC MOV DWORD PTR DS:[EAX-4],EBX 00384E28 ^ E9 F4D6FFFF JMP 00361C66////跳回继续。 00384E2D 90 NOP 以上是简单的脱壳步骤 |
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值


