|
|
[推荐][分享]Synopsys Static Analysis (Coverity) 2019.3 for linux64
cov-analysis-linux64-2022.6.2.sh https://mega.nz/file/r1hkRCIY#gXfRyWa57ApxPcDsei3Dph-KjlMcb2zvChMqou5YR2E |
|
|
叠楼活动 | 看雪23岁,生日快乐!送新年礼物啦
祝看雪23岁生日快乐!新的一年,大展宏“兔”!!! |
|
|
|
|
|
[分享]Fortify SCA 22.1 Linux
Mirror https://gofile.io/d/Vyi2MW |
|
|
[分享]Source Insight 4.0.0096 Patched
Source Insight 4 - Latest Version Version 4.0.0125 - November 22, 2022 https://s3-us-west-2.amazonaws.com/assets.sourceinsight.com/download/v4/release/sourceinsight40125-setup.exe |
|
|
[调查]VMProtect Source Code Leak
#ESETResearch discovered that #LuckyMouse/#APT27 used a code-signing certificate belonging to VMPsoft, the developer of the VMProtect packer. The signed file is a loader for the SysUpdate backdoor (aka Soldier). We notified VMPSoft of this compromise https://twitter.com/ESETresearch/status/1594937054303236096 https://www.virustotal.com/gui/file/a8527a88fb9a48f043a0b762c7431fb52e601b72ff2fa0d35327e5cc72404edc Pivoting on the certificate, we found genuine VMPsoft binaries and a sample of SysUpdate signed and packed with VMProtect. Since LuckyMouse rarely use VMProtect, it is possible that they also stole VMProtect packer when they got the digi certificate. While the certificate is still valid, we have notified GlobalSign. Thumbprint: 6EF192CBD6E540F1D740D1BD96317ACAE8C6AF9D Subject: Permyakov Ivan Yurievich IP, Ekaterinburg, Sverdlovskaya oblast, RU Valid from: 2022-05-17 11:18:43 Valid to: 2023-05-18 11:18:43 Interestingly, in August 2022 a tweet claimed that the source code of VMProtect was leaked. However, we could not find the leak nor link it to the LuckyMouse incident. https://www.virustotal.com/gui/file/cc196ee155bf864071cbeec3ddcd3e2451a37d4296f53a024142c70193b9691d 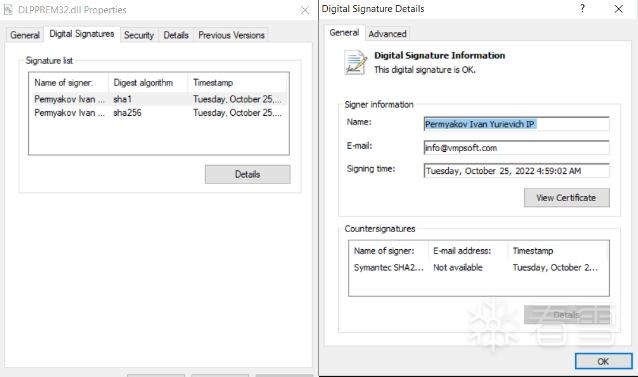
最后于 2022-11-24 02:02
被Alfik编辑
,原因:
|
|
|
[推荐][分享]Synopsys Static Analysis (Coverity) 2019.3 for linux64
Coverity Wizard removed in 2021.12 - Synopsys Community Solution In 2021.9 release note: https://community.synopsys.com/s/article/Coverity-Wizard-removed-in-2021-12 1.3.4. Coverity Wizard 2021.9.0 1.3.4.1. Deprecated products and features PRD-12524 Cov-Wizard is deprecated as of 2021.9.0 and scheduled to be removed in a 2021.9 hotfix release and in the 2021.12 release. |
|
|
|
|
|
|
|
|
[分享]Fortify SCA 22.1 Linux
Fortify_SCA_and_Apps_22.1.0 - Fortify_SCA_and_Apps_22.1.1 (MAC OS - Linux - Windows) http://1.13.79.120:5244/%E8%B5%84%E6%BA%90%E5%BA%93(%E7%A8%B3%E5%AE%9A%E9%80%9A%E9%81%93)/%E7%BD%91%E7%BB%9C%E5%AE%89%E5%85%A8/%E6%BC%8F%E6%B4%9E%E6%89%AB%E6%8F%8F/Fortify |
|
|
[推荐][分享]Synopsys Static Analysis (Coverity) 2019.3 for linux64
https://bbs.pediy.com/thread-250847-3.htm#1725526 
|
|
|
[分享]CheckMarx 9.5.0 &crack
http://1.13.79.120:5244/%E8%B5%84%E6%BA%90%E5%BA%93(%E7%A8%B3%E5%AE%9A%E9%80%9A%E9%81%93)/%E7%BD%91%E7%BB%9C%E5%AE%89%E5%85%A8/%E6%BC%8F%E6%B4%9E%E6%89%AB%E6%8F%8F/Checkmarx%20CxSAST |
|
|
[推荐][分享]Synopsys Static Analysis (Coverity) 2019.3 for linux64
Title Coverity does not start after improper shutdown Details Coverity does not start correctly after an outage on the server. $cov-im-ctl maint Stopping Coverity Connect Application ... [ERROR] Caught at top level: null See log file for details. java.io.EOFException at java.base/java.io.ObjectInputStream$BlockDataInputStream.peekByte(Unknown Source) at java.base/java.io.ObjectInputStream.readObject0(Unknown Source) at java.base/java.io.ObjectInputStream.readObject(Unknown Source) at java.base/java.io.ObjectInputStream.readObject(Unknown Source) at com.coverity.ces.launcher.CIMDaemonClient.command(CIMDaemonClient.java:96) at com.coverity.ces.launcher.CovImCtl.go(CovImCtl.java:251) at com.coverity.ces.launcher.CovImCtl.main(CovImCtl.java:343) at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method) at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(Unknown Source) at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(Unknown Source) at java.base/java.lang.reflect.Method.invoke(Unknown Source) at com.exe4j.runtime.LauncherEngine.launch(LauncherEngine.java:85) at com.install4j.runtime.launcher.UnixLauncher.start(UnixLauncher.java:66) at install4j.com.coverity.ces.launcher.CovImCtl3320932810.main(Unknown Source) Solution If the issue is caused by database corruption, you may need to re-install Coverity Connect and restore the database from a backup achieve. The easiest solution is to re-install Coverity Connect. 1. Generate a backup file if not already: $cov-admin-db maint $cov-admin-db backup /path/to/<backup_file> 2. Turn off the old Coverity Connect: $cov-im-ctl stop 3. Launch the installer and choose "Fresh Installation". You may pick the same ports as the existing Coverity Connect. 4. After the installation finished, restore the backup: $<new_CC>/bin/cov-admin-db maint $<new_CC>/bin/cov-admin-db restore /path/to/<backup_file> 5. After the restore finishes, try to start the new Coverity Connect: $<new_CC>/bin/cov-im-ctl start 6. If you have SSO, keystore configured, please copy the related settings to the new installation. If not, please ignore this step. 7. If the new installation worked great, you now can uninstall the old Coverity Connect. If not, you can try to manually start the DB server to bypass the daemon: $<Coverity_connect_dir>/bin/postgres/pg_ctl -o "-F -p <DB_port>" -D "<Coverity_connect_dir>/database" -N localhost -U coverity -P <DB_password> start Please replace: -<Coverity_connect_dir> as the path of your Coverity Connect installation directory -<DB_port> is "maindb.password" listed in <Coverity_connect_dir>/config/cim.properties If the command succeeds, below command will let you know that the database is already running: $cov-im-ctl maint Then you can start Coverity Connect using: $cov-im-ctl start |
操作理由



