|
|
[求助]求助北极星大牛的遍历通过EPROCESS结构的ActiveProcessLinks链表兼容其他系统的问题
win vista 的 这样有一个参考 希望以后大家少些麻烦 有 6000 RTM等多个版本 我也不知道 具体的版本 就发一个我下的 Windows VISTA X32 nt!_EPROCESS +0x000 Pcb : _KPROCESS +0x080 ProcessLock : _EX_PUSH_LOCK +0x088 CreateTime : _LARGE_INTEGER 0x1c87ec2`f35608ed +0x090 ExitTime : _LARGE_INTEGER 0x0 +0x098 RundownProtect : _EX_RUNDOWN_REF +0x09c UniqueProcessId : 0x00000768 +0x0a0 ActiveProcessLinks : _LIST_ENTRY [ 0x8532d260 - 0x8533d0c0 ] +0x0a8 QuotaUsage : [3] 0x4c88 +0x0b4 QuotaPeak : [3] 0x50e8 +0x0c0 CommitCharge : 0xd13 +0x0c4 PeakVirtualSize : 0xa09d000 +0x0c8 VirtualSize : 0x9445000 +0x0cc SessionProcessLinks : _LIST_ENTRY [ 0x85311b64 - 0x8533d0ec ] +0x0d4 DebugPort : (null) +0x0d8 ExceptionPortData : 0x851a5030 +0x0d8 ExceptionPortValue : 0x851a5030 +0x0d8 ExceptionPortState : 0y000 +0x0dc ObjectTable : 0x92ef1260 _HANDLE_TABLE +0x0e0 Token : _EX_FAST_REF +0x0e4 WorkingSetPage : 0x84c1 +0x0e8 AddressCreationLock : _EX_PUSH_LOCK +0x0ec RotateInProgress : (null) +0x0f0 ForkInProgress : (null) +0x0f4 HardwareTrigger : 0 +0x0f8 PhysicalVadRoot : (null) +0x0fc CloneRoot : (null) +0x100 NumberOfPrivatePages : 0x76e +0x104 NumberOfLockedPages : 0 +0x108 Win32Process : 0xfe6847c0 +0x10c Job : (null) +0x110 SectionObject : 0x92ef1030 +0x114 SectionBaseAddress : 0x006d0000 +0x118 QuotaBlock : 0x84fd6370 _EPROCESS_QUOTA_BLOCK +0x11c WorkingSetWatch : (null) +0x120 Win32WindowStation : 0x00000034 +0x124 InheritedFromUniqueProcessId : 0x00000728 +0x128 LdtInformation : (null) +0x12c Spare : (null) +0x130 VdmObjects : (null) +0x134 DeviceMap : 0x8f5d9990 +0x138 EtwDataSource : (null) +0x13c FreeTebHint : 0x7ffde000 +0x140 PageDirectoryPte : _HARDWARE_PTE +0x140 Filler : 0 +0x148 Session : 0x8970c000 +0x14c ImageFileName : [16] "explorer.exe" +0x15c JobLinks : _LIST_ENTRY [ 0x0 - 0x0 ] +0x164 LockedPagesList : (null) +0x168 ThreadListHead : _LIST_ENTRY [ 0x85308278 - 0x852f0950 ] +0x170 SecurityPort : (null) +0x174 PaeTop : 0x84b5b340 +0x178 ActiveThreads : 0x19 +0x17c ImagePathHash : 0x7a3328da +0x180 DefaultHardErrorProcessing : 0 +0x184 LastThreadExitStatus : 0 +0x188 Peb : 0x7ffd8000 _PEB +0x18c PrefetchTrace : _EX_FAST_REF +0x190 ReadOperationCount : _LARGE_INTEGER 0x2b0 +0x198 WriteOperationCount : _LARGE_INTEGER 0xa +0x1a0 OtherOperationCount : _LARGE_INTEGER 0x2f54 +0x1a8 ReadTransferCount : _LARGE_INTEGER 0x63ef8 +0x1b0 WriteTransferCount : _LARGE_INTEGER 0x420 +0x1b8 OtherTransferCount : _LARGE_INTEGER 0xaafc45 +0x1c0 CommitChargeLimit : 0 +0x1c4 CommitChargePeak : 0xd99 +0x1c8 AweInfo : (null) +0x1cc SeAuditProcessCreationInfo : _SE_AUDIT_PROCESS_CREATION_INFO +0x1d0 Vm : _MMSUPPORT +0x218 MmProcessLinks : _LIST_ENTRY [ 0x8532d3d8 - 0x8533d238 ] +0x220 ModifiedPageCount : 0x5a7 +0x224 Flags2 : 0xd000 +0x224 JobNotReallyActive : 0y0 +0x224 AccountingFolded : 0y0 +0x224 NewProcessReported : 0y0 +0x224 ExitProcessReported : 0y0 +0x224 ReportCommitChanges : 0y0 +0x224 LastReportMemory : 0y0 +0x224 ReportPhysicalPageChanges : 0y0 +0x224 HandleTableRundown : 0y0 +0x224 NeedsHandleRundown : 0y0 +0x224 RefTraceEnabled : 0y0 +0x224 NumaAware : 0y0 +0x224 ProtectedProcess : 0y0 +0x224 DefaultPagePriority : 0y101 +0x224 PrimaryTokenFrozen : 0y1 +0x224 ProcessVerifierTarget : 0y0 +0x224 StackRandomizationDisabled : 0y0 +0x224 AffinityPermanent : 0y0 +0x224 AffinityUpdateEnable : 0y0 +0x224 CrossSessionCreate : 0y0 +0x228 Flags : 0x144d0801 +0x228 CreateReported : 0y1 +0x228 NoDebugInherit : 0y0 +0x228 ProcessExiting : 0y0 +0x228 ProcessDelete : 0y0 +0x228 Wow64SplitPages : 0y0 +0x228 VmDeleted : 0y0 +0x228 OutswapEnabled : 0y0 +0x228 Outswapped : 0y0 +0x228 ForkFailed : 0y0 +0x228 Wow64VaSpace4Gb : 0y0 +0x228 AddressSpaceInitialized : 0y10 +0x228 SetTimerResolution : 0y0 +0x228 BreakOnTermination : 0y0 +0x228 DeprioritizeViews : 0y0 +0x228 WriteWatch : 0y0 +0x228 ProcessInSession : 0y1 +0x228 OverrideAddressSpace : 0y0 +0x228 HasAddressSpace : 0y1 +0x228 LaunchPrefetched : 0y1 +0x228 InjectInpageErrors : 0y0 +0x228 VmTopDown : 0y0 +0x228 ImageNotifyDone : 0y1 +0x228 PdeUpdateNeeded : 0y0 +0x228 VdmAllowed : 0y0 +0x228 SmapAllowed : 0y0 +0x228 ProcessInserted : 0y1 +0x228 DefaultIoPriority : 0y010 +0x228 ProcessSelfDelete : 0y0 +0x228 SpareProcessFlags : 0y0 +0x22c ExitStatus : 259 +0x230 Spare7 : 0 +0x232 SubSystemMinorVersion : 0 '' +0x233 SubSystemMajorVersion : 0x6 '' +0x232 SubSystemVersion : 0x600 +0x234 PriorityClass : 0x2 '' +0x238 VadRoot : _MM_AVL_TABLE +0x258 Cookie : 0x72607a1f +0x25c AlpcContext : _ALPC_PROCESS_CONTEXT kd> dt nt!_KPROCESS 8535f020 +0x000 Header : _DISPATCHER_HEADER +0x010 ProfileListHead : _LIST_ENTRY [ 0x8535f030 - 0x8535f030 ] +0x018 DirectoryTableBase : 0x1f75b340 +0x01c Unused0 : 0 +0x020 LdtDescriptor : _KGDTENTRY +0x028 Int21Descriptor : _KIDTENTRY +0x030 IopmOffset : 0x20ac +0x032 Unused1 : 0 '' +0x033 Unused2 : 0 '' +0x034 ActiveProcessors : 0 +0x038 KernelTime : 0x7e +0x03c UserTime : 0x22 +0x040 ReadyListHead : _LIST_ENTRY [ 0x8535f060 - 0x8535f060 ] +0x048 SwapListEntry : _SINGLE_LIST_ENTRY +0x04c VdmTrapcHandler : (null) +0x050 ThreadListHead : _LIST_ENTRY [ 0x853081f4 - 0x852f08cc ] +0x058 ProcessLock : 0 +0x05c Affinity : 1 +0x060 AutoAlignment : 0y0 +0x060 DisableBoost : 0y0 +0x060 DisableQuantum : 0y0 +0x060 ReservedFlags : 0y00000000000000000000000000000 (0) +0x060 ProcessFlags : 0 +0x064 BasePriority : 8 '' +0x065 QuantumReset : 6 '' +0x066 State : 0 '' +0x067 ThreadSeed : 0 '' +0x068 PowerState : 0 '' +0x069 IdealNode : 0 '' +0x06a Visited : 0 '' +0x06b Flags : _KEXECUTE_OPTIONS +0x06b ExecuteOptions : 0x72 'r' +0x06c StackCount : 0x19 +0x070 ProcessListEntry : _LIST_ENTRY [ 0x0 - 0x0 ] +0x078 CycleTime : 0x1`236c8e36 |
|
|
[求助]求助北极星大牛的遍历通过EPROCESS结构的ActiveProcessLinks链表兼容其他系统的问题
对照的是 2003的系统
Windows Server 2003 x32
+0x000 Pcb : _KPROCESS
+0x000 Header : _DISPATCHER_HEADER
+0x010 ProfileListHead : _LIST_ENTRY [ 0x8163cc00 - 0x8163cc00 ]
+0x018 DirectoryTableBase : [2] 0x249b000
+0x020 LdtDescriptor : _KGDTENTRY
+0x028 Int21Descriptor : _KIDTENTRY
+0x030 IopmOffset : 0x20ac
+0x032 Iopl : 0 ''
+0x033 Unused : 0 ''
+0x034 ActiveProcessors : 0
+0x038 KernelTime : 0
+0x03c UserTime : 0
+0x040 ReadyListHead : _LIST_ENTRY [ 0x8163cc30 - 0x8163cc30 ]
+0x048 SwapListEntry : _SINGLE_LIST_ENTRY
+0x04c VdmTrapcHandler : (null)
+0x050 ThreadListHead : _LIST_ENTRY [ 0x81204c00 - 0x811fed98 ]
+0x058 ProcessLock : 0
+0x05c Affinity : 1
+0x060 AutoAlignment : 0y0
+0x060 DisableBoost : 0y0
+0x060 DisableQuantum : 0y0
+0x060 ReservedFlags : 0y00000000000000000000000000000 (0)
+0x060 ProcessFlags : 0
+0x064 BasePriority : 13 ''
+0x065 QuantumReset : 36 '$'
+0x066 State : 0 ''
+0x067 ThreadSeed : 0 ''
+0x068 PowerState : 0 ''
+0x069 IdealNode : 0 ''
+0x06a Visited : 0 ''
+0x06b Flags : _KEXECUTE_OPTIONS
+0x06b ExecuteOptions : 0 ''
+0x06c StackCount : 4
+0x070 ProcessListEntry : _LIST_ENTRY [ 0x0 - 0x0 ]
+0x078 ProcessLock : _EX_PUSH_LOCK
+0x000 Locked : 0y0
+0x000 Waiting : 0y0
+0x000 Waking : 0y0
+0x000 MultipleShared : 0y0
+0x000 Shared : 0y0000000000000000000000000000 (0)
+0x000 Value : 0
+0x000 Ptr : (null)
+0x080 CreateTime : _LARGE_INTEGER 0x1c8aff2`273b0893
+0x000 LowPart : 0x273b0893
+0x004 HighPart : 29929458
+0x000 u : __unnamed
+0x000 QuadPart : 128546043955185811
+0x088 ExitTime : _LARGE_INTEGER 0x0
+0x000 LowPart : 0
+0x004 HighPart : 0
+0x000 u : __unnamed
+0x000 QuadPart : 0
+0x090 RundownProtect : _EX_RUNDOWN_REF
+0x000 Count : 0
+0x000 Ptr : (null)
+0x094 UniqueProcessId : 0x000007d4
+0x098 ActiveProcessLinks : _LIST_ENTRY [ 0x808af068 - 0x81297958 ]
+0x000 Flink : 0x808af068 _LIST_ENTRY [ 0x8179d878 - 0x8163cc88 ]
+0x004 Blink : 0x81297958 _LIST_ENTRY [ 0x8163cc88 - 0x8120cad8 ]
+0x0a0 QuotaUsage : [3] 0xd20
+0x0ac QuotaPeak : [3] 0xde8
+0x0b8 CommitCharge : 0x182
+0x0bc PeakVirtualSize : 0x20ea000
+0x0c0 VirtualSize : 0x206a000
+0x0c4 SessionProcessLinks : _LIST_ENTRY [ 0xfa119010 - 0x81297984 ]
+0x000 Flink : 0xfa119010 _LIST_ENTRY [ 0x815afc34 - 0x8163ccb4 ]
+0x004 Blink : 0x81297984 _LIST_ENTRY [ 0x8163ccb4 - 0x8120cb04 ]
+0x0cc DebugPort : (null)
+0x0d0 ExceptionPort : 0xe13e14d8
+0x0d4 ObjectTable : 0xe156c9d8 _HANDLE_TABLE
+0x000 TableCode : 0xe1103000
+0x004 QuotaProcess : 0x8163cbf0 _EPROCESS
+0x008 UniqueProcessId : 0x000007d4
+0x00c HandleTableLock : [4] _EX_PUSH_LOCK
+0x01c HandleTableList : _LIST_ENTRY [ 0x808b0928 - 0xe19f3e94 ]
+0x024 HandleContentionEvent : _EX_PUSH_LOCK
+0x028 DebugInfo : (null)
+0x02c ExtraInfoPages : 0
+0x030 FirstFree : 0x17c
+0x034 LastFree : 0
+0x038 NextHandleNeedingPool : 0x800
+0x03c HandleCount : 93
+0x040 Flags : 0
+0x040 StrictFIFO : 0y0
+0x0d8 Token : _EX_FAST_REF
+0x000 Object : 0xe10eb705
+0x000 RefCnt : 0y101
+0x000 Value : 0xe10eb705
+0x0dc WorkingSetPage : 0x279e
+0x0e0 AddressCreationLock : _KGUARDED_MUTEX
+0x000 Count : 1
+0x004 Owner : (null)
+0x008 Contention : 0
+0x00c Gate : _KGATE
+0x01c KernelApcDisable : 0
+0x01e SpecialApcDisable : 0
+0x01c CombinedApcDisable : 0
+0x100 HyperSpaceLock : 0
+0x104 ForkInProgress : (null)
+0x108 HardwareTrigger : 0
+0x10c PhysicalVadRoot : (null)
+0x110 CloneRoot : (null)
+0x114 NumberOfPrivatePages : 0xec
+0x118 NumberOfLockedPages : 0
+0x11c Win32Process : 0xe10fe898
+0x120 Job : (null)
+0x124 SectionObject : 0xe18996c0
+0x128 SectionBaseAddress : 0x01000000
+0x12c QuotaBlock : 0x812c3828 _EPROCESS_QUOTA_BLOCK
+0x000 QuotaEntry : [3] _EPROCESS_QUOTA_ENTRY
+0x030 QuotaList : _LIST_ENTRY [ 0x808af228 - 0x8124fbe0 ]
+0x038 ReferenceCount : 0x30c
+0x03c ProcessCount : 6
+0x130 WorkingSetWatch : (null)
+0x134 Win32WindowStation : 0x00000050
+0x138 InheritedFromUniqueProcessId : 0x000006e4
+0x13c LdtInformation : (null)
+0x140 VadFreeHint : (null)
+0x144 VdmObjects : (null)
+0x148 DeviceMap : 0xe16ef388
+0x14c Spare0 : [3] (null)
+0x158 PageDirectoryPte : _HARDWARE_PTE
+0x000 Valid : 0y0
+0x000 Write : 0y0
+0x000 Owner : 0y0
+0x000 WriteThrough : 0y0
+0x000 CacheDisable : 0y0
+0x000 Accessed : 0y0
+0x000 Dirty : 0y0
+0x000 LargePage : 0y0
+0x000 Global : 0y0
+0x000 CopyOnWrite : 0y0
+0x000 Prototype : 0y0
+0x000 reserved : 0y0
+0x000 PageFrameNumber : 0y00000000000000000000 (0)
+0x158 Filler : 0
+0x160 Session : 0xfa119000
+0x164 ImageFileName : [16] "taskmgr.exe"
+0x174 JobLinks : _LIST_ENTRY [ 0x0 - 0x0 ]
+0x000 Flink : (null)
+0x004 Blink : (null)
+0x17c LockedPagesList : (null)
+0x180 ThreadListHead : _LIST_ENTRY [ 0x81204c7c - 0x811fee14 ]
+0x000 Flink : 0x81204c7c _LIST_ENTRY [ 0x81202fd4 - 0x8163cd70 ]
+0x004 Blink : 0x811fee14 _LIST_ENTRY [ 0x8163cd70 - 0x8120477c ]
+0x188 SecurityPort : (null)
+0x18c PaeTop : (null)
+0x190 ActiveThreads : 4
+0x194 GrantedAccess : 0x1f0fff
+0x198 DefaultHardErrorProcessing : 0
+0x19c LastThreadExitStatus : 0
+0x1a0 Peb : 0x7ffd9000 _PEB
+0x000 InheritedAddressSpace : 0 ''
+0x001 ReadImageFileExecOptions : 0 ''
+0x002 BeingDebugged : 0 ''
+0x003 BitField : 0 ''
+0x003 ImageUsesLargePages : 0y0
+0x003 SpareBits : 0y0000000 (0)
+0x004 Mutant : 0xffffffff
+0x008 ImageBaseAddress : 0x01000000
+0x00c Ldr : 0x7c9b77e0 _PEB_LDR_DATA
+0x010 ProcessParameters : 0x00020000 _RTL_USER_PROCESS_PARAMETERS
+0x014 SubSystemData : (null)
+0x018 ProcessHeap : 0x000a0000
+0x01c FastPebLock : 0x7c9b7740 _RTL_CRITICAL_SECTION
+0x020 AtlThunkSListPtr : (null)
+0x024 SparePtr2 : (null)
+0x028 EnvironmentUpdateCount : 1
+0x02c KernelCallbackTable : 0x77e129b0
+0x030 SystemReserved : [1] 0
+0x034 SpareUlong : 0
+0x038 FreeList : (null)
+0x03c TlsExpansionCounter : 0
+0x040 TlsBitmap : 0x7c9b8fd8
+0x044 TlsBitmapBits : [2] 0xffff
+0x04c ReadOnlySharedMemoryBase : 0x7f6f0000
+0x050 ReadOnlySharedMemoryHeap : 0x7f6f0000
+0x054 ReadOnlyStaticServerData : 0x7f6f0688 -> (null)
+0x058 AnsiCodePageData : 0x7ffa0000
+0x05c OemCodePageData : 0x7ffa0000
+0x060 UnicodeCaseTableData : 0x7ffd1000
+0x064 NumberOfProcessors : 1
+0x068 NtGlobalFlag : 0
+0x070 CriticalSectionTimeout : _LARGE_INTEGER 0xffffe86d`079b8000
+0x078 HeapSegmentReserve : 0x100000
+0x07c HeapSegmentCommit : 0x2000
+0x080 HeapDeCommitTotalFreeThreshold : 0x10000
+0x084 HeapDeCommitFreeBlockThreshold : 0x1000
+0x088 NumberOfHeaps : 0xa
+0x08c MaximumNumberOfHeaps : 0x10
+0x090 ProcessHeaps : 0x7c9b8a20 -> 0x000a0000
+0x094 GdiSharedHandleTable : 0x00430000
+0x098 ProcessStarterHelper : (null)
+0x09c GdiDCAttributeList : 0x14
+0x0a0 LoaderLock : 0x7c9b77a0 _RTL_CRITICAL_SECTION
+0x0a4 OSMajorVersion : 5
+0x0a8 OSMinorVersion : 2
+0x0ac OSBuildNumber : 0xece
+0x0ae OSCSDVersion : 0x200
+0x0b0 OSPlatformId : 2
+0x0b4 ImageSubsystem : 2
+0x0b8 ImageSubsystemMajorVersion : 4
+0x0bc ImageSubsystemMinorVersion : 0
+0x0c0 ImageProcessAffinityMask : 0
+0x0c4 GdiHandleBuffer : [34] 0
+0x14c PostProcessInitRoutine : (null)
+0x150 TlsExpansionBitmap : 0x7c9b8fd0
+0x154 TlsExpansionBitmapBits : [32] 1
+0x1d4 SessionId : 0
+0x1d8 AppCompatFlags : _ULARGE_INTEGER 0x0
+0x1e0 AppCompatFlagsUser : _ULARGE_INTEGER 0x0
+0x1e8 pShimData : (null)
+0x1ec AppCompatInfo : (null)
+0x1f0 CSDVersion : _UNICODE_STRING "Service Pack 2"
+0x1f8 ActivationContextData : 0x00090000 _ACTIVATION_CONTEXT_DATA
+0x1fc ProcessAssemblyStorageMap : 0x000a3740 _ASSEMBLY_STORAGE_MAP
+0x200 SystemDefaultActivationContextData : 0x00080000 _ACTIVATION_CONTEXT_DATA
+0x204 SystemAssemblyStorageMap : (null)
+0x208 MinimumStackCommit : 0
+0x20c FlsCallback : 0x000a5408 -> (null)
+0x210 FlsListHead : _LIST_ENTRY [ 0xa1f60 - 0xb3c48 ]
+0x218 FlsBitmap : 0x7c9b8fc0
+0x21c FlsBitmapBits : [4] 0xf
+0x22c FlsHighIndex : 3
+0x1a4 PrefetchTrace : _EX_FAST_REF
+0x000 Object : (null)
+0x000 RefCnt : 0y000
+0x000 Value : 0
+0x1a8 ReadOperationCount : _LARGE_INTEGER 0x33
+0x000 LowPart : 0x33
+0x004 HighPart : 0
+0x000 u : __unnamed
+0x000 QuadPart : 51
+0x1b0 WriteOperationCount : _LARGE_INTEGER 0x33
+0x000 LowPart : 0x33
+0x004 HighPart : 0
+0x000 u : __unnamed
+0x000 QuadPart : 51
+0x1b8 OtherOperationCount : _LARGE_INTEGER 0x290
+0x000 LowPart : 0x290
+0x004 HighPart : 0
+0x000 u : __unnamed
+0x000 QuadPart : 656
+0x1c0 ReadTransferCount : _LARGE_INTEGER 0x1254
+0x000 LowPart : 0x1254
+0x004 HighPart : 0
+0x000 u : __unnamed
+0x000 QuadPart : 4692
+0x1c8 WriteTransferCount : _LARGE_INTEGER 0x171c
+0x000 LowPart : 0x171c
+0x004 HighPart : 0
+0x000 u : __unnamed
+0x000 QuadPart : 5916
+0x1d0 OtherTransferCount : _LARGE_INTEGER 0x5385
+0x000 LowPart : 0x5385
+0x004 HighPart : 0
+0x000 u : __unnamed
+0x000 QuadPart : 21381
+0x1d8 CommitChargeLimit : 0
+0x1dc CommitChargePeak : 0x182
+0x1e0 AweInfo : (null)
+0x1e4 SeAuditProcessCreationInfo : _SE_AUDIT_PROCESS_CREATION_INFO
+0x000 ImageFileName : 0x811f1b58 _OBJECT_NAME_INFORMATION
+0x1e8 Vm : _MMSUPPORT
+0x000 WorkingSetExpansionLinks : _LIST_ENTRY [ 0x808ad410 - 0x81297aa8 ]
+0x008 LastTrimTime : _LARGE_INTEGER 0x1c8aff2`273b0893
+0x010 Flags : _MMSUPPORT_FLAGS
+0x014 PageFaultCount : 0x584
+0x018 PeakWorkingSetSize : 0x481
+0x01c GrowthSinceLastEstimate : 0x584
+0x020 MinimumWorkingSetSize : 0x32
+0x024 MaximumWorkingSetSize : 0x159
+0x028 VmWorkingSetList : 0xc0502000 _MMWSL
+0x02c Claim : 0
+0x030 NextEstimationSlot : 0
+0x034 NextAgingSlot : 0
+0x038 EstimatedAvailable : 0
+0x03c WorkingSetSize : 0x481
+0x040 WorkingSetMutex : _EX_PUSH_LOCK
+0x230 MmProcessLinks : _LIST_ENTRY [ 0x808a8e08 - 0x81297af0 ]
+0x000 Flink : 0x808a8e08 _LIST_ENTRY [ 0x808a0230 - 0x8163ce20 ]
+0x004 Blink : 0x81297af0 _LIST_ENTRY [ 0x8163ce20 - 0x8120cc70 ]
+0x238 ModifiedPageCount : 0x764
+0x23c JobStatus : 0
+0x240 Flags : 0x450801
+0x240 CreateReported : 0y1
+0x240 NoDebugInherit : 0y0
+0x240 ProcessExiting : 0y0
+0x240 ProcessDelete : 0y0
+0x240 Wow64SplitPages : 0y0
+0x240 VmDeleted : 0y0
+0x240 OutswapEnabled : 0y0
+0x240 Outswapped : 0y0
+0x240 ForkFailed : 0y0
+0x240 Wow64VaSpace4Gb : 0y0
+0x240 AddressSpaceInitialized : 0y10
+0x240 SetTimerResolution : 0y0
+0x240 BreakOnTermination : 0y0
+0x240 SessionCreationUnderway : 0y0
+0x240 WriteWatch : 0y0
+0x240 ProcessInSession : 0y1
+0x240 OverrideAddressSpace : 0y0
+0x240 HasAddressSpace : 0y1
+0x240 LaunchPrefetched : 0y0
+0x240 InjectInpageErrors : 0y0
+0x240 VmTopDown : 0y0
+0x240 ImageNotifyDone : 0y1
+0x240 PdeUpdateNeeded : 0y0
+0x240 VdmAllowed : 0y0
+0x240 SmapAllowed : 0y0
+0x240 CreateFailed : 0y0
+0x240 DefaultIoPriority : 0y000
+0x240 Spare1 : 0y0
+0x240 Spare2 : 0y0
+0x244 ExitStatus : 259
+0x248 NextPageColor : 0xe4d2
+0x24a SubSystemMinorVersion : 0 ''
+0x24b SubSystemMajorVersion : 0x4 ''
+0x24a SubSystemVersion : 0x400
+0x24c PriorityClass : 0x3 ''
+0x250 VadRoot : _MM_AVL_TABLE
+0x000 BalancedRoot : _MMADDRESS_NODE
+0x014 DepthOfTree : 0y00111 (0x7)
+0x014 Unused : 0y000
+0x014 NumberGenericTableElements : 0y000000000000000001010100 (0x54)
+0x018 NodeHint : 0x811b2b80
+0x01c NodeFreeHint : (null)
+0x270 Cookie : 0x26f245ab
|
|
|
[求助]求助北极星大牛的遍历通过EPROCESS结构的ActiveProcessLinks链表兼容其他系统的问题
发下win7的 整个结构 build好象是 7600 以后节省大家精力 lkd> dt_eprocess nt!_EPROCESS +0x000 Pcb : _KPROCESS +0x098 ProcessLock : _EX_PUSH_LOCK +0x0a0 CreateTime : _LARGE_INTEGER +0x0a8 ExitTime : _LARGE_INTEGER +0x0b0 RundownProtect : _EX_RUNDOWN_REF +0x0b4 UniqueProcessId : Ptr32 Void +0x0b8 ActiveProcessLinks : _LIST_ENTRY +0x0c0 ProcessQuotaUsage : [2] Uint4B +0x0c8 ProcessQuotaPeak : [2] Uint4B +0x0d0 CommitCharge : Uint4B +0x0d4 QuotaBlock : Ptr32 _EPROCESS_QUOTA_BLOCK +0x0d8 CpuQuotaBlock : Ptr32 _PS_CPU_QUOTA_BLOCK +0x0dc PeakVirtualSize : Uint4B +0x0e0 VirtualSize : Uint4B +0x0e4 SessionProcessLinks : _LIST_ENTRY +0x0ec DebugPort : Ptr32 Void +0x0f0 ExceptionPortData : Ptr32 Void +0x0f0 ExceptionPortValue : Uint4B +0x0f0 ExceptionPortState : Pos 0, 3 Bits +0x0f4 ObjectTable : Ptr32 _HANDLE_TABLE +0x0f8 Token : _EX_FAST_REF +0x0fc WorkingSetPage : Uint4B +0x100 AddressCreationLock : _EX_PUSH_LOCK +0x104 RotateInProgress : Ptr32 _ETHREAD +0x108 ForkInProgress : Ptr32 _ETHREAD +0x10c HardwareTrigger : Uint4B +0x110 PhysicalVadRoot : Ptr32 _MM_AVL_TABLE +0x114 CloneRoot : Ptr32 Void +0x118 NumberOfPrivatePages : Uint4B +0x11c NumberOfLockedPages : Uint4B +0x120 Win32Process : Ptr32 Void +0x124 Job : Ptr32 _EJOB +0x128 SectionObject : Ptr32 Void +0x12c SectionBaseAddress : Ptr32 Void +0x130 Cookie : Uint4B +0x134 Spare8 : Uint4B +0x138 WorkingSetWatch : Ptr32 _PAGEFAULT_HISTORY +0x13c Win32WindowStation : Ptr32 Void +0x140 InheritedFromUniqueProcessId : Ptr32 Void +0x144 LdtInformation : Ptr32 Void +0x148 VdmObjects : Ptr32 Void +0x14c ConsoleHostProcess : Uint4B +0x150 DeviceMap : Ptr32 Void +0x154 EtwDataSource : Ptr32 Void +0x158 FreeTebHint : Ptr32 Void +0x160 PageDirectoryPte : _HARDWARE_PTE +0x160 Filler : Uint8B +0x168 Session : Ptr32 Void +0x16c ImageFileName : [15] UChar +0x17b PriorityClass : UChar +0x17c JobLinks : _LIST_ENTRY +0x184 LockedPagesList : Ptr32 Void +0x188 ThreadListHead : _LIST_ENTRY +0x190 SecurityPort : Ptr32 Void +0x194 PaeTop : Ptr32 Void +0x198 ActiveThreads : Uint4B +0x19c ImagePathHash : Uint4B +0x1a0 DefaultHardErrorProcessing : Uint4B +0x1a4 LastThreadExitStatus : Int4B +0x1a8 Peb : Ptr32 _PEB +0x1ac PrefetchTrace : _EX_FAST_REF +0x1b0 ReadOperationCount : _LARGE_INTEGER +0x1b8 WriteOperationCount : _LARGE_INTEGER +0x1c0 OtherOperationCount : _LARGE_INTEGER +0x1c8 ReadTransferCount : _LARGE_INTEGER +0x1d0 WriteTransferCount : _LARGE_INTEGER +0x1d8 OtherTransferCount : _LARGE_INTEGER +0x1e0 CommitChargeLimit : Uint4B +0x1e4 CommitChargePeak : Uint4B +0x1e8 AweInfo : Ptr32 Void +0x1ec SeAuditProcessCreationInfo : _SE_AUDIT_PROCESS_CREATION_INFO +0x1f0 Vm : _MMSUPPORT +0x25c MmProcessLinks : _LIST_ENTRY +0x264 HighestUserAddress : Ptr32 Void +0x268 ModifiedPageCount : Uint4B +0x26c Flags2 : Uint4B +0x26c JobNotReallyActive : Pos 0, 1 Bit +0x26c AccountingFolded : Pos 1, 1 Bit +0x26c NewProcessReported : Pos 2, 1 Bit +0x26c ExitProcessReported : Pos 3, 1 Bit +0x26c ReportCommitChanges : Pos 4, 1 Bit +0x26c LastReportMemory : Pos 5, 1 Bit +0x26c ReportPhysicalPageChanges : Pos 6, 1 Bit +0x26c HandleTableRundown : Pos 7, 1 Bit +0x26c NeedsHandleRundown : Pos 8, 1 Bit +0x26c RefTraceEnabled : Pos 9, 1 Bit +0x26c NumaAware : Pos 10, 1 Bit +0x26c ProtectedProcess : Pos 11, 1 Bit +0x26c DefaultPagePriority : Pos 12, 3 Bits +0x26c PrimaryTokenFrozen : Pos 15, 1 Bit +0x26c ProcessVerifierTarget : Pos 16, 1 Bit +0x26c StackRandomizationDisabled : Pos 17, 1 Bit +0x26c AffinityPermanent : Pos 18, 1 Bit +0x26c AffinityUpdateEnable : Pos 19, 1 Bit +0x26c PropagateNode : Pos 20, 1 Bit +0x26c ExplicitAffinity : Pos 21, 1 Bit +0x270 Flags : Uint4B +0x270 CreateReported : Pos 0, 1 Bit +0x270 NoDebugInherit : Pos 1, 1 Bit +0x270 ProcessExiting : Pos 2, 1 Bit +0x270 ProcessDelete : Pos 3, 1 Bit +0x270 Wow64SplitPages : Pos 4, 1 Bit +0x270 VmDeleted : Pos 5, 1 Bit +0x270 OutswapEnabled : Pos 6, 1 Bit +0x270 Outswapped : Pos 7, 1 Bit +0x270 ForkFailed : Pos 8, 1 Bit +0x270 Wow64VaSpace4Gb : Pos 9, 1 Bit +0x270 AddressSpaceInitialized : Pos 10, 2 Bits +0x270 SetTimerResolution : Pos 12, 1 Bit +0x270 BreakOnTermination : Pos 13, 1 Bit +0x270 DeprioritizeViews : Pos 14, 1 Bit +0x270 WriteWatch : Pos 15, 1 Bit +0x270 ProcessInSession : Pos 16, 1 Bit +0x270 OverrideAddressSpace : Pos 17, 1 Bit +0x270 HasAddressSpace : Pos 18, 1 Bit +0x270 LaunchPrefetched : Pos 19, 1 Bit +0x270 InjectInpageErrors : Pos 20, 1 Bit +0x270 VmTopDown : Pos 21, 1 Bit +0x270 ImageNotifyDone : Pos 22, 1 Bit +0x270 PdeUpdateNeeded : Pos 23, 1 Bit +0x270 VdmAllowed : Pos 24, 1 Bit +0x270 CrossSessionCreate : Pos 25, 1 Bit +0x270 ProcessInserted : Pos 26, 1 Bit +0x270 DefaultIoPriority : Pos 27, 3 Bits +0x270 ProcessSelfDelete : Pos 30, 1 Bit +0x270 SetTimerResolutionLink : Pos 31, 1 Bit +0x274 ExitStatus : Int4B +0x278 VadRoot : _MM_AVL_TABLE +0x298 AlpcContext : _ALPC_PROCESS_CONTEXT +0x2a8 TimerResolutionLink : _LIST_ENTRY +0x2b0 RequestedTimerResolution : Uint4B +0x2b4 ActiveThreadsHighWatermark : Uint4B +0x2b8 SmallestTimerResolution : Uint4B +0x2bc TimerResolutionStackRecord : Ptr32 _PO_DIAG_STACK_RECORD lkd> dt_ethread nt!_ETHREAD +0x000 Tcb : _KTHREAD +0x200 CreateTime : _LARGE_INTEGER +0x208 ExitTime : _LARGE_INTEGER +0x208 KeyedWaitChain : _LIST_ENTRY +0x210 ExitStatus : Int4B +0x214 PostBlockList : _LIST_ENTRY +0x214 ForwardLinkShadow : Ptr32 Void +0x218 StartAddress : Ptr32 Void +0x21c TerminationPort : Ptr32 _TERMINATION_PORT +0x21c ReaperLink : Ptr32 _ETHREAD +0x21c KeyedWaitValue : Ptr32 Void +0x220 ActiveTimerListLock : Uint4B +0x224 ActiveTimerListHead : _LIST_ENTRY +0x22c Cid : _CLIENT_ID +0x234 KeyedWaitSemaphore : _KSEMAPHORE +0x234 AlpcWaitSemaphore : _KSEMAPHORE +0x248 ClientSecurity : _PS_CLIENT_SECURITY_CONTEXT +0x24c IrpList : _LIST_ENTRY +0x254 TopLevelIrp : Uint4B +0x258 DeviceToVerify : Ptr32 _DEVICE_OBJECT +0x25c CpuQuotaApc : Ptr32 _PSP_CPU_QUOTA_APC +0x260 Win32StartAddress : Ptr32 Void +0x264 LegacyPowerObject : Ptr32 Void +0x268 ThreadListEntry : _LIST_ENTRY +0x270 RundownProtect : _EX_RUNDOWN_REF +0x274 ThreadLock : _EX_PUSH_LOCK +0x278 ReadClusterSize : Uint4B +0x27c MmLockOrdering : Int4B +0x280 CrossThreadFlags : Uint4B +0x280 Terminated : Pos 0, 1 Bit +0x280 ThreadInserted : Pos 1, 1 Bit +0x280 HideFromDebugger : Pos 2, 1 Bit +0x280 ActiveImpersonationInfo : Pos 3, 1 Bit +0x280 SystemThread : Pos 4, 1 Bit +0x280 HardErrorsAreDisabled : Pos 5, 1 Bit +0x280 BreakOnTermination : Pos 6, 1 Bit +0x280 SkipCreationMsg : Pos 7, 1 Bit +0x280 SkipTerminationMsg : Pos 8, 1 Bit +0x280 CopyTokenOnOpen : Pos 9, 1 Bit +0x280 ThreadIoPriority : Pos 10, 3 Bits +0x280 ThreadPagePriority : Pos 13, 3 Bits +0x280 RundownFail : Pos 16, 1 Bit +0x280 NeedsWorkingSetAging : Pos 17, 1 Bit +0x284 SameThreadPassiveFlags : Uint4B +0x284 ActiveExWorker : Pos 0, 1 Bit +0x284 ExWorkerCanWaitUser : Pos 1, 1 Bit +0x284 MemoryMaker : Pos 2, 1 Bit +0x284 ClonedThread : Pos 3, 1 Bit +0x284 KeyedEventInUse : Pos 4, 1 Bit +0x284 RateApcState : Pos 5, 2 Bits +0x284 SelfTerminate : Pos 7, 1 Bit +0x288 SameThreadApcFlags : Uint4B +0x288 Spare : Pos 0, 1 Bit +0x288 StartAddressInvalid : Pos 1, 1 Bit +0x288 EtwPageFaultCalloutActive : Pos 2, 1 Bit +0x288 OwnsProcessWorkingSetExclusive : Pos 3, 1 Bit +0x288 OwnsProcessWorkingSetShared : Pos 4, 1 Bit +0x288 OwnsSystemCacheWorkingSetExclusive : Pos 5, 1 Bit +0x288 OwnsSystemCacheWorkingSetShared : Pos 6, 1 Bit +0x288 OwnsSessionWorkingSetExclusive : Pos 7, 1 Bit +0x289 OwnsSessionWorkingSetShared : Pos 0, 1 Bit +0x289 OwnsProcessAddressSpaceExclusive : Pos 1, 1 Bit +0x289 OwnsProcessAddressSpaceShared : Pos 2, 1 Bit +0x289 SuppressSymbolLoad : Pos 3, 1 Bit +0x289 Prefetching : Pos 4, 1 Bit +0x289 OwnsDynamicMemoryShared : Pos 5, 1 Bit +0x289 OwnsChangeControlAreaExclusive : Pos 6, 1 Bit +0x289 OwnsChangeControlAreaShared : Pos 7, 1 Bit +0x28a OwnsPagedPoolWorkingSetExclusive : Pos 0, 1 Bit +0x28a OwnsPagedPoolWorkingSetShared : Pos 1, 1 Bit +0x28a OwnsSystemPtesWorkingSetExclusive : Pos 2, 1 Bit +0x28a OwnsSystemPtesWorkingSetShared : Pos 3, 1 Bit +0x28a TrimTrigger : Pos 4, 2 Bits +0x28a Spare1 : Pos 6, 2 Bits +0x28b PriorityRegionActive : UChar +0x28c CacheManagerActive : UChar +0x28d DisablePageFaultClustering : UChar +0x28e ActiveFaultCount : UChar +0x28f LockOrderState : UChar +0x290 AlpcMessageId : Uint4B +0x294 AlpcMessage : Ptr32 Void +0x294 AlpcReceiveAttributeSet : Uint4B +0x298 AlpcWaitListEntry : _LIST_ENTRY +0x2a0 CacheManagerCount : Uint4B +0x2a4 IoBoostCount : Uint4B +0x2a8 IrpListLock : Uint4B +0x2ac ReservedForSynchTracking : Ptr32 Void +0x2b0 CmCallbackListHead : _SINGLE_LIST_ENTRY lkd> dt_kprocess nt!_KPROCESS +0x000 Header : _DISPATCHER_HEADER +0x010 ProfileListHead : _LIST_ENTRY +0x018 DirectoryTableBase : Uint4B +0x01c LdtDescriptor : _KGDTENTRY +0x024 Int21Descriptor : _KIDTENTRY +0x02c ThreadListHead : _LIST_ENTRY +0x034 ProcessLock : Uint4B +0x038 Affinity : _KAFFINITY_EX +0x044 ReadyListHead : _LIST_ENTRY +0x04c SwapListEntry : _SINGLE_LIST_ENTRY +0x050 ActiveProcessors : _KAFFINITY_EX +0x05c AutoAlignment : Pos 0, 1 Bit +0x05c DisableBoost : Pos 1, 1 Bit +0x05c DisableQuantum : Pos 2, 1 Bit +0x05c ActiveGroupsMask : Pos 3, 1 Bit +0x05c ReservedFlags : Pos 4, 28 Bits +0x05c ProcessFlags : Int4B +0x060 BasePriority : Char +0x061 QuantumReset : Char +0x062 Visited : UChar +0x063 Unused3 : UChar +0x064 ThreadSeed : [1] Uint4B +0x068 IdealNode : [1] Uint2B +0x06a IdealGlobalNode : Uint2B +0x06c Flags : _KEXECUTE_OPTIONS +0x06d Unused1 : UChar +0x06e IopmOffset : Uint2B +0x070 Unused4 : Uint4B +0x074 StackCount : _KSTACK_COUNT +0x078 ProcessListEntry : _LIST_ENTRY +0x080 CycleTime : Uint8B +0x088 KernelTime : Uint4B +0x08c UserTime : Uint4B +0x090 VdmTrapcHandler : Ptr32 Void lkd> dt_kthread nt!_KTHREAD +0x000 Header : _DISPATCHER_HEADER +0x010 CycleTime : Uint8B +0x018 HighCycleTime : Uint4B +0x020 QuantumTarget : Uint8B +0x028 InitialStack : Ptr32 Void +0x02c StackLimit : Ptr32 Void +0x030 KernelStack : Ptr32 Void +0x034 ThreadLock : Uint4B +0x038 WaitRegister : _KWAIT_STATUS_REGISTER +0x039 Running : UChar +0x03a Alerted : [2] UChar +0x03c KernelStackResident : Pos 0, 1 Bit +0x03c ReadyTransition : Pos 1, 1 Bit +0x03c ProcessReadyQueue : Pos 2, 1 Bit +0x03c WaitNext : Pos 3, 1 Bit +0x03c SystemAffinityActive : Pos 4, 1 Bit +0x03c Alertable : Pos 5, 1 Bit +0x03c GdiFlushActive : Pos 6, 1 Bit +0x03c UserStackWalkActive : Pos 7, 1 Bit +0x03c ApcInterruptRequest : Pos 8, 1 Bit +0x03c ForceDeferSchedule : Pos 9, 1 Bit +0x03c QuantumEndMigrate : Pos 10, 1 Bit +0x03c UmsDirectedSwitchEnable : Pos 11, 1 Bit +0x03c TimerActive : Pos 12, 1 Bit +0x03c Reserved : Pos 13, 19 Bits +0x03c MiscFlags : Int4B +0x040 ApcState : _KAPC_STATE +0x040 ApcStateFill : [23] UChar +0x057 Priority : Char +0x058 NextProcessor : Uint4B +0x05c DeferredProcessor : Uint4B +0x060 ApcQueueLock : Uint4B +0x064 ContextSwitches : Uint4B +0x068 State : UChar +0x069 NpxState : Char +0x06a WaitIrql : UChar +0x06b WaitMode : Char +0x06c WaitStatus : Int4B +0x070 WaitBlockList : Ptr32 _KWAIT_BLOCK +0x074 WaitListEntry : _LIST_ENTRY +0x074 SwapListEntry : _SINGLE_LIST_ENTRY +0x07c Queue : Ptr32 _KQUEUE +0x080 WaitTime : Uint4B +0x084 KernelApcDisable : Int2B +0x086 SpecialApcDisable : Int2B +0x084 CombinedApcDisable : Uint4B +0x088 Teb : Ptr32 Void +0x090 Timer : _KTIMER +0x0b8 AutoAlignment : Pos 0, 1 Bit +0x0b8 DisableBoost : Pos 1, 1 Bit +0x0b8 EtwStackTraceApc1Inserted : Pos 2, 1 Bit +0x0b8 EtwStackTraceApc2Inserted : Pos 3, 1 Bit +0x0b8 CalloutActive : Pos 4, 1 Bit +0x0b8 ApcQueueable : Pos 5, 1 Bit +0x0b8 EnableStackSwap : Pos 6, 1 Bit +0x0b8 GuiThread : Pos 7, 1 Bit +0x0b8 UmsPerformingSyscall : Pos 8, 1 Bit +0x0b8 ReservedFlags : Pos 9, 23 Bits +0x0b8 ThreadFlags : Int4B +0x0bc ServiceTable : Ptr32 Void +0x0c0 WaitBlock : [4] _KWAIT_BLOCK +0x120 QueueListEntry : _LIST_ENTRY +0x128 TrapFrame : Ptr32 _KTRAP_FRAME +0x12c FirstArgument : Ptr32 Void +0x130 CallbackStack : Ptr32 Void +0x130 CallbackDepth : Uint4B +0x134 ApcStateIndex : UChar +0x135 BasePriority : Char +0x136 PriorityDecrement : Char +0x136 ForegroundBoost : Pos 0, 4 Bits +0x136 UnusualBoost : Pos 4, 4 Bits +0x137 Preempted : UChar +0x138 AdjustReason : UChar +0x139 AdjustIncrement : Char +0x13a PreviousMode : Char +0x13b Saturation : Char +0x13c SystemCallNumber : Uint4B +0x140 FreezeCount : Uint4B +0x144 UserAffinity : _GROUP_AFFINITY +0x150 Process : Ptr32 _KPROCESS +0x154 Affinity : _GROUP_AFFINITY +0x160 IdealProcessor : Uint4B +0x164 UserIdealProcessor : Uint4B +0x168 ApcStatePointer : [2] Ptr32 _KAPC_STATE +0x170 SavedApcState : _KAPC_STATE +0x170 SavedApcStateFill : [23] UChar +0x187 WaitReason : UChar +0x188 SuspendCount : Char +0x189 Spare1 : Char +0x18a OtherPlatformFill : UChar +0x18c Win32Thread : Ptr32 Void +0x190 StackBase : Ptr32 Void +0x194 SuspendApc : _KAPC +0x194 SuspendApcFill0 : [1] UChar +0x195 ResourceIndex : UChar +0x194 SuspendApcFill1 : [3] UChar +0x197 QuantumReset : UChar +0x194 SuspendApcFill2 : [4] UChar +0x198 KernelTime : Uint4B +0x194 SuspendApcFill3 : [36] UChar +0x1b8 WaitPrcb : Ptr32 _KPRCB +0x194 SuspendApcFill4 : [40] UChar +0x1bc LegoData : Ptr32 Void +0x194 SuspendApcFill5 : [47] UChar +0x1c3 LargeStack : UChar +0x1c4 UserTime : Uint4B +0x1c8 SuspendSemaphore : _KSEMAPHORE +0x1c8 SuspendSemaphorefill : [20] UChar +0x1dc SListFaultCount : Uint4B +0x1e0 ThreadListEntry : _LIST_ENTRY +0x1e8 MutantListHead : _LIST_ENTRY +0x1f0 SListFaultAddress : Ptr32 Void +0x1f4 ThreadCounters : Ptr32 _KTHREAD_COUNTERS +0x1f8 XStateSave : Ptr32 _XSTATE_SAVE lkd> dt_peb nt!_PEB +0x000 InheritedAddressSpace : UChar +0x001 ReadImageFileExecOptions : UChar +0x002 BeingDebugged : UChar +0x003 BitField : UChar +0x003 ImageUsesLargePages : Pos 0, 1 Bit +0x003 IsProtectedProcess : Pos 1, 1 Bit +0x003 IsLegacyProcess : Pos 2, 1 Bit +0x003 IsImageDynamicallyRelocated : Pos 3, 1 Bit +0x003 SkipPatchingUser32Forwarders : Pos 4, 1 Bit +0x003 SpareBits : Pos 5, 3 Bits +0x004 Mutant : Ptr32 Void +0x008 ImageBaseAddress : Ptr32 Void +0x00c Ldr : Ptr32 _PEB_LDR_DATA +0x010 ProcessParameters : Ptr32 _RTL_USER_PROCESS_PARAMETERS +0x014 SubSystemData : Ptr32 Void +0x018 ProcessHeap : Ptr32 Void +0x01c FastPebLock : Ptr32 _RTL_CRITICAL_SECTION +0x020 AtlThunkSListPtr : Ptr32 Void +0x024 IFEOKey : Ptr32 Void +0x028 CrossProcessFlags : Uint4B +0x028 ProcessInJob : Pos 0, 1 Bit +0x028 ProcessInitializing : Pos 1, 1 Bit +0x028 ProcessUsingVEH : Pos 2, 1 Bit +0x028 ProcessUsingVCH : Pos 3, 1 Bit +0x028 ProcessUsingFTH : Pos 4, 1 Bit +0x028 ReservedBits0 : Pos 5, 27 Bits +0x02c KernelCallbackTable : Ptr32 Void +0x02c UserSharedInfoPtr : Ptr32 Void +0x030 SystemReserved : [1] Uint4B +0x034 AtlThunkSListPtr32 : Uint4B +0x038 ApiSetMap : Ptr32 Void +0x03c TlsExpansionCounter : Uint4B +0x040 TlsBitmap : Ptr32 Void +0x044 TlsBitmapBits : [2] Uint4B +0x04c ReadOnlySharedMemoryBase : Ptr32 Void +0x050 HotpatchInformation : Ptr32 Void +0x054 ReadOnlyStaticServerData : Ptr32 Ptr32 Void +0x058 AnsiCodePageData : Ptr32 Void +0x05c OemCodePageData : Ptr32 Void +0x060 UnicodeCaseTableData : Ptr32 Void +0x064 NumberOfProcessors : Uint4B +0x068 NtGlobalFlag : Uint4B +0x070 CriticalSectionTimeout : _LARGE_INTEGER +0x078 HeapSegmentReserve : Uint4B +0x07c HeapSegmentCommit : Uint4B +0x080 HeapDeCommitTotalFreeThreshold : Uint4B +0x084 HeapDeCommitFreeBlockThreshold : Uint4B +0x088 NumberOfHeaps : Uint4B +0x08c MaximumNumberOfHeaps : Uint4B +0x090 ProcessHeaps : Ptr32 Ptr32 Void +0x094 GdiSharedHandleTable : Ptr32 Void +0x098 ProcessStarterHelper : Ptr32 Void +0x09c GdiDCAttributeList : Uint4B +0x0a0 LoaderLock : Ptr32 _RTL_CRITICAL_SECTION +0x0a4 OSMajorVersion : Uint4B +0x0a8 OSMinorVersion : Uint4B +0x0ac OSBuildNumber : Uint2B +0x0ae OSCSDVersion : Uint2B +0x0b0 OSPlatformId : Uint4B +0x0b4 ImageSubsystem : Uint4B +0x0b8 ImageSubsystemMajorVersion : Uint4B +0x0bc ImageSubsystemMinorVersion : Uint4B +0x0c0 ActiveProcessAffinityMask : Uint4B +0x0c4 GdiHandleBuffer : [34] Uint4B +0x14c PostProcessInitRoutine : Ptr32 void +0x150 TlsExpansionBitmap : Ptr32 Void +0x154 TlsExpansionBitmapBits : [32] Uint4B +0x1d4 SessionId : Uint4B +0x1d8 AppCompatFlags : _ULARGE_INTEGER +0x1e0 AppCompatFlagsUser : _ULARGE_INTEGER +0x1e8 pShimData : Ptr32 Void +0x1ec AppCompatInfo : Ptr32 Void +0x1f0 CSDVersion : _UNICODE_STRING +0x1f8 ActivationContextData : Ptr32 _ACTIVATION_CONTEXT_DATA +0x1fc ProcessAssemblyStorageMap : Ptr32 _ASSEMBLY_STORAGE_MAP +0x200 SystemDefaultActivationContextData : Ptr32 _ACTIVATION_CONTEXT_DATA +0x204 SystemAssemblyStorageMap : Ptr32 _ASSEMBLY_STORAGE_MAP +0x208 MinimumStackCommit : Uint4B +0x20c FlsCallback : Ptr32 _FLS_CALLBACK_INFO +0x210 FlsListHead : _LIST_ENTRY +0x218 FlsBitmap : Ptr32 Void +0x21c FlsBitmapBits : [4] Uint4B +0x22c FlsHighIndex : Uint4B +0x230 WerRegistrationData : Ptr32 Void +0x234 WerShipAssertPtr : Ptr32 Void +0x238 pContextData : Ptr32 Void +0x23c pImageHeaderHash : Ptr32 Void +0x240 TracingFlags : Uint4B +0x240 HeapTracingEnabled : Pos 0, 1 Bit +0x240 CritSecTracingEnabled : Pos 1, 1 Bit +0x240 SpareTracingBits : Pos 2, 30 Bits lkd> dt_teb nt!_TEB +0x000 NtTib : _NT_TIB +0x01c EnvironmentPointer : Ptr32 Void +0x020 ClientId : _CLIENT_ID +0x028 ActiveRpcHandle : Ptr32 Void +0x02c ThreadLocalStoragePointer : Ptr32 Void +0x030 ProcessEnvironmentBlock : Ptr32 _PEB +0x034 LastErrorValue : Uint4B +0x038 CountOfOwnedCriticalSections : Uint4B +0x03c CsrClientThread : Ptr32 Void +0x040 Win32ThreadInfo : Ptr32 Void +0x044 User32Reserved : [26] Uint4B +0x0ac UserReserved : [5] Uint4B +0x0c0 WOW32Reserved : Ptr32 Void +0x0c4 CurrentLocale : Uint4B +0x0c8 FpSoftwareStatusRegister : Uint4B +0x0cc SystemReserved1 : [54] Ptr32 Void +0x1a4 ExceptionCode : Int4B +0x1a8 ActivationContextStackPointer : Ptr32 _ACTIVATION_CONTEXT_STACK +0x1ac SpareBytes : [36] UChar +0x1d0 TxFsContext : Uint4B +0x1d4 GdiTebBatch : _GDI_TEB_BATCH +0x6b4 RealClientId : _CLIENT_ID +0x6bc GdiCachedProcessHandle : Ptr32 Void +0x6c0 GdiClientPID : Uint4B +0x6c4 GdiClientTID : Uint4B +0x6c8 GdiThreadLocalInfo : Ptr32 Void +0x6cc Win32ClientInfo : [62] Uint4B +0x7c4 glDispatchTable : [233] Ptr32 Void +0xb68 glReserved1 : [29] Uint4B +0xbdc glReserved2 : Ptr32 Void +0xbe0 glSectionInfo : Ptr32 Void +0xbe4 glSection : Ptr32 Void +0xbe8 glTable : Ptr32 Void +0xbec glCurrentRC : Ptr32 Void +0xbf0 glContext : Ptr32 Void +0xbf4 LastStatusValue : Uint4B +0xbf8 StaticUnicodeString : _UNICODE_STRING +0xc00 StaticUnicodeBuffer : [261] Wchar +0xe0c DeallocationStack : Ptr32 Void +0xe10 TlsSlots : [64] Ptr32 Void +0xf10 TlsLinks : _LIST_ENTRY +0xf18 Vdm : Ptr32 Void +0xf1c ReservedForNtRpc : Ptr32 Void +0xf20 DbgSsReserved : [2] Ptr32 Void +0xf28 HardErrorMode : Uint4B +0xf2c Instrumentation : [9] Ptr32 Void +0xf50 ActivityId : _GUID +0xf60 SubProcessTag : Ptr32 Void +0xf64 EtwLocalData : Ptr32 Void +0xf68 EtwTraceData : Ptr32 Void +0xf6c WinSockData : Ptr32 Void +0xf70 GdiBatchCount : Uint4B +0xf74 CurrentIdealProcessor : _PROCESSOR_NUMBER +0xf74 IdealProcessorValue : Uint4B +0xf74 ReservedPad0 : UChar +0xf75 ReservedPad1 : UChar +0xf76 ReservedPad2 : UChar +0xf77 IdealProcessor : UChar +0xf78 GuaranteedStackBytes : Uint4B +0xf7c ReservedForPerf : Ptr32 Void +0xf80 ReservedForOle : Ptr32 Void +0xf84 WaitingOnLoaderLock : Uint4B +0xf88 SavedPriorityState : Ptr32 Void +0xf8c SoftPatchPtr1 : Uint4B +0xf90 ThreadPoolData : Ptr32 Void +0xf94 TlsExpansionSlots : Ptr32 Ptr32 Void +0xf98 MuiGeneration : Uint4B +0xf9c IsImpersonating : Uint4B +0xfa0 NlsCache : Ptr32 Void +0xfa4 pShimData : Ptr32 Void +0xfa8 HeapVirtualAffinity : Uint4B +0xfac CurrentTransactionHandle : Ptr32 Void +0xfb0 ActiveFrame : Ptr32 _TEB_ACTIVE_FRAME +0xfb4 FlsData : Ptr32 Void +0xfb8 PreferredLanguages : Ptr32 Void +0xfbc UserPrefLanguages : Ptr32 Void +0xfc0 MergedPrefLanguages : Ptr32 Void +0xfc4 MuiImpersonation : Uint4B +0xfc8 CrossTebFlags : Uint2B +0xfc8 SpareCrossTebBits : Pos 0, 16 Bits +0xfca SameTebFlags : Uint2B +0xfca SafeThunkCall : Pos 0, 1 Bit +0xfca InDebugPrint : Pos 1, 1 Bit +0xfca HasFiberData : Pos 2, 1 Bit +0xfca SkipThreadAttach : Pos 3, 1 Bit +0xfca WerInShipAssertCode : Pos 4, 1 Bit +0xfca RanProcessInit : Pos 5, 1 Bit +0xfca ClonedThread : Pos 6, 1 Bit +0xfca SuppressDebugMsg : Pos 7, 1 Bit +0xfca DisableUserStackWalk : Pos 8, 1 Bit +0xfca RtlExceptionAttached : Pos 9, 1 Bit +0xfca InitialThread : Pos 10, 1 Bit +0xfca SpareSameTebBits : Pos 11, 5 Bits +0xfcc TxnScopeEnterCallback : Ptr32 Void +0xfd0 TxnScopeExitCallback : Ptr32 Void +0xfd4 TxnScopeContext : Ptr32 Void +0xfd8 LockCount : Uint4B +0xfdc SpareUlong0 : Uint4B +0xfe0 ResourceRetValue : Ptr32 Void |
|
|
[求助]求助北极星大牛的遍历通过EPROCESS结构的ActiveProcessLinks链表兼容其他系统的问题
查了下资料 不知道是不是这样。。 http://topic.csdn.net/u/20070904/09/caf913d4-8396-401a-8ba3-e2e24546a07f.html 如果想看偏移量,用Windbg-> Kernel Debug-> Local,然后 !symfix .reload -f nt dt _EPROCESS 就可以了, Vista 下: 0: kd> vertarget Windows Vista Kernel Version 6000 MP (2 procs) Free x86 compatible Built by: 6000.16386.x86fre.vista_rtm.061101-2205 Kernel base = 0x81800000 PsLoadedModuleList = 0x81908ab0 Debug session time: Fri Aug 31 16:16:35.457 2007 (GMT-7) System Uptime: 0 days 0:00:18.191 0: kd> dt _EPROCESS ntdll!_EPROCESS +0x000 Pcb : _KPROCESS +0x080 ProcessLock : _EX_PUSH_LOCK +0x088 CreateTime : _LARGE_INTEGER +0x090 ExitTime : _LARGE_INTEGER +0x098 RundownProtect : _EX_RUNDOWN_REF 怎么对应以上的参数呢? |
|
|
[求助]各个版本的EPROCESS 是有了 但是这个结构的SIZE不好搞啊
又要安装虚拟机 和windbg了。。。 |
|
|
|
|
|
|
|
|
求助 关于 ssdt hook NtWriteVirtualMemory NtReadVirtualMemory NtOpenProcess
居然没有人看上30kx 在一夜奋斗之后 修改了整个 通讯过程 终于 成功的实现了保护(虽然是用易语言) 只能在xp 2003系统下 又要解决兼容性 问题 。。。。。。。。。。。。。 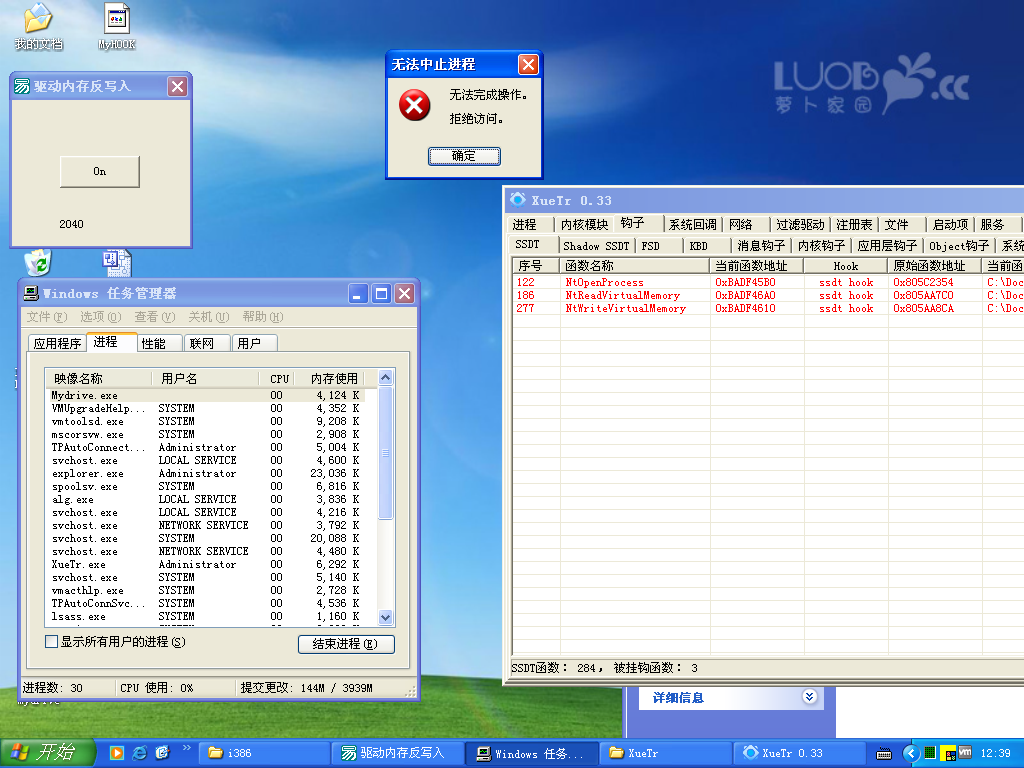 |
|
|
求助 关于 ssdt hook NtWriteVirtualMemory NtReadVirtualMemory NtOpenProcess
你写写看 保护demo.exe 驱动可编译的 弄好了我给你30 kx 悬赏的30kx是一定有的 我现在的kx是被暂时扣的 你加油试试 算是你贴子的完善 精华混不了 可以混点眼球 |
|
|
求助 关于 ssdt hook NtWriteVirtualMemory NtReadVirtualMemory NtOpenProcess
直接用内核函数读txt exe把pid写在txt上 txt里面保存pid也可以的 所以现在就是sys读txt |
|
|
求助 关于 ssdt hook NtWriteVirtualMemory NtReadVirtualMemory NtOpenProcess
大哥 现在就缺一个 exe跟sys通讯 或者 内核下 进程名转化为进程id |
|
|
求助 关于 ssdt hook NtWriteVirtualMemory NtReadVirtualMemory NtOpenProcess
vc 6也可以 应该怎么写 通讯。。。 |
|
|
求助 关于 ssdt hook NtWriteVirtualMemory NtReadVirtualMemory NtOpenProcess
现在我已经搞定了 这个驱动 要怎么写r0和r3下的进程通讯啊 delphi7的 ring0和ring3 下的 进程通讯 #include <ntddk.h>
#include "struct.h"
//int pos_CreateFile; /* 保存这些函数的服务号 */
int pos_ReadVirtualMemory;
int pos_NtOpenProcess;
int pos_NtWriteVirtualMemory;
UNICODE_STRING uProcessName;
UNICODE_STRING MyuProcessName;
ANSI_STRING aProcessName;
//特殊的值,目标进程的ID
DWORD dwTargetProcessID;
#define MY_CONTROL_CODE 0x4021
#define IOCTL_SET_TARGET_PROCESS_ID (ULONG)CTL_CODE( FILE_DEVICE_UNKNOWN, MY_CONTROL_CODE, METHOD_BUFFERED, FILE_READ_DATA | FILE_WRITE_DATA )
//一些常量定义
#define EPROCESS_SIZE 1
#define PEB_OFFSET 2
#define FILE_NAME_OFFSET 3
#define PROCESS_LINK_OFFSET 4
#define PROCESS_ID_OFFSET 5
#define EXIT_TIME_OFFSET 6
DWORD GetPlantformDependentInfo ( DWORD dwFlag )
{
DWORD current_build;
DWORD ans = 0;
PsGetVersion(NULL, NULL,¤t_build, NULL);
switch ( dwFlag )
{
case EPROCESS_SIZE:
if (current_build == 2195) ans = 0 ; // 2000,当前不支持2000,下同
if (current_build == 2600) ans = 0x25C; // xp
if (current_build == 3790) ans = 0x270; // 2003
break;
case PEB_OFFSET:
if (current_build == 2195) ans = 0;
if (current_build == 2600) ans = 0x1b0;
if (current_build == 3790) ans = 0x1a0;
break;
case FILE_NAME_OFFSET:
if (current_build == 2195) ans = 0;
if (current_build == 2600) ans = 0x174;
if (current_build == 3790) ans = 0x164;
break;
case PROCESS_LINK_OFFSET:
if (current_build == 2195) ans = 0;
if (current_build == 2600) ans = 0x088;
if (current_build == 3790) ans = 0x098;
break;
case PROCESS_ID_OFFSET:
if (current_build == 2195) ans = 0;
if (current_build == 2600) ans = 0x084;
if (current_build == 3790) ans = 0x094;
break;
case EXIT_TIME_OFFSET:
if (current_build == 2195) ans = 0;
if (current_build == 2600) ans = 0x078;
if (current_build == 3790) ans = 0x088;
break;
}
return ans;
}
NTSTATUS NewNtOpenProcess(PHANDLE ProcessHandle,
ACCESS_MASK DesiredAccess,
POBJECT_ATTRIBUTES ObjectAttributes,
PCLIENT_ID ClientId)
{
NTSTATUS ntStatus;
DWORD dwProcessId = NULL;
ntStatus = ((ZWCREATEFILE)(OldNtOpenProcess))(
ProcessHandle,
DesiredAccess,
ObjectAttributes,
ClientId);
if((ClientId != NULL))
{
dwProcessId = (HANDLE)ClientId->UniqueProcess;
if (dwProcessId == dwTargetProcessID)
{
ntStatus = STATUS_ACCESS_DENIED;
}
}
return ntStatus;
}
NTSTATUS
NewNtWriteVirtualMemory(IN HANDLE ProcessHandle,
IN PVOID BaseAddress,
IN PVOID Buffer,
IN ULONG BufferLength,
OUT PULONG ReturnLength OPTIONAL)
{
NTSTATUS ntStatus;
NTSTATUS ret;
PVOID pEprocess;
DWORD dwProcessId;
ntStatus = ((NTWRITEVIRTUALMEMORY)(OldNtWriteVitualMemory)) (
ProcessHandle,
BaseAddress,
Buffer,
BufferLength,
ReturnLength);
pEprocess = NULL;
dwProcessId = GetPlantformDependentInfo(PROCESS_ID_OFFSET);
ret = ObReferenceObjectByHandle(ProcessHandle , 0, NULL, KernelMode, &pEprocess, NULL);
if(STATUS_SUCCESS == ret)
{
dwProcessId = *(DWORD*)((BYTE*)pEprocess+dwProcessId); //被扫描进程的PID
if (dwProcessId == dwTargetProcessID)
{
if(dwTargetProcessID == (DWORD)PsGetCurrentProcessId())
{
goto Next;
}
return STATUS_ACCESS_DENIED;
}
}
Next:
return ntStatus;
}
NTSTATUS
NewNtReadVirtualMemory(
IN HANDLE ProcessHandle,
IN PVOID BaseAddress,
OUT PVOID Buffer,
IN ULONG BufferLength,
OUT PULONG ReturnLength OPTIONAL
)
{
NTSTATUS ret;
PVOID pEprocess; //通过进程句柄得到ID
PVOID pExplorer_Eprocess; //过滤掉桌面进程explorer时用到的一个EPROCESS类型临时变量
DWORD dwCurrentPID; //当前ProcessHandle句柄对应的进程号
DWORD dwProcessId;
DWORD dwFileName;
pEprocess = NULL;
dwProcessId = GetPlantformDependentInfo(PROCESS_ID_OFFSET);
dwFileName = GetPlantformDependentInfo(FILE_NAME_OFFSET);
ret = ObReferenceObjectByHandle(ProcessHandle , 0, NULL, KernelMode, &pEprocess, NULL);
if(STATUS_SUCCESS == ret)
{
//DbgPrint("the caller ProcessName is %s\n",(PUCHAR)((BYTE*)pEprocess + dwFileName));
dwCurrentPID = *(DWORD*)((BYTE*)pEprocess+dwProcessId); //得到被扫描的进程的PID
if(dwCurrentPID == dwTargetProcessID) //dwTargetProcessID //如果被扫描的进程PID跟预定的一样,那么就开始bypass
{
DbgPrint("call NtReadVirtualMemory!Target Process is %d. The Caller is %d\n",dwTargetProcessID, PsGetCurrentProcessId());
if(dwTargetProcessID == (DWORD)PsGetCurrentProcessId()) //排除自己调用NtReadVirtualMemory来读取自己内存的情况
{
DbgPrint("call NtReadVirtualMemory by myself\n");
goto Next;
}
pExplorer_Eprocess = PsGetCurrentProcess(); //得到当前进程eprocess结构
RtlInitUnicodeString(&uProcessName,L"explorer.exe");
RtlInitAnsiString(&aProcessName,(PUCHAR)((BYTE*)pExplorer_Eprocess + dwFileName));
RtlAnsiStringToUnicodeString(&MyuProcessName,&aProcessName,TRUE);
DbgPrint("call NtReadVirtualMemory by %wZ ---%wZ\n",&MyuProcessName,&uProcessName);
if(RtlCompareUnicodeString(&uProcessName,&MyuProcessName, TRUE) == 0) //不区分大小写的对比!
{
DbgPrint("call NtReadVirtualMemory by explorer process\n"); //排除explorer调用NtReadVirtualMemory来读取自己内存的情况
goto Next;
}
DbgPrint("call NtReadVirtualMemory by other process %d\n",PsGetCurrentProcessId());
//排除了自己对自己的内存操作,桌面进程对所关心的进程的操作之外,其他的一切进程对多关心的进程进行操作,一律pass
ret = ((NTREADVIRTUALMEMORY)(OldNtReadVirtualMemory))(
ProcessHandle,
BaseAddress,
L"Is By PopSky", //自定义的垃圾数据
BufferLength,
ReturnLength
);
return ret;
}
}
Next:
ret = ((NTREADVIRTUALMEMORY)(OldNtReadVirtualMemory))(
ProcessHandle,
BaseAddress,
Buffer,
BufferLength,
ReturnLength
);
return ret;
}
///////////////////////////////////////////////////////////////// -- --
//+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++// -- - - --
//+ +// -- - - --
//+ 下面2个函数用于得到部分SDT函数的地址 +// -- - --
//+ +// - sudami -
//+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++// -- --
///////////////////////////////////////////////////////////////// -- --
// -- --
// --
DWORD GetDllFunctionAddress (
char* lpFunctionName,
PUNICODE_STRING pDllName
)
{
HANDLE hThread, hSection, hFile, hMod;
SECTION_IMAGE_INFORMATION sii;
IMAGE_DOS_HEADER* dosheader;
IMAGE_OPTIONAL_HEADER* opthdr;
IMAGE_EXPORT_DIRECTORY* pExportTable;
DWORD* arrayOfFunctionAddresses;
DWORD* arrayOfFunctionNames;
WORD* arrayOfFunctionOrdinals;
DWORD functionOrdinal;
DWORD Base, x, functionAddress;
char* functionName;
STRING ntFunctionName, ntFunctionNameSearch;
PVOID BaseAddress = NULL;
SIZE_T size=0;
OBJECT_ATTRIBUTES oa = {sizeof oa, 0, pDllName, OBJ_CASE_INSENSITIVE};
IO_STATUS_BLOCK iosb;
//_asm int 3;
ZwOpenFile(&hFile, FILE_EXECUTE | SYNCHRONIZE, &oa, &iosb, FILE_SHARE_READ, FILE_SYNCHRONOUS_IO_NONALERT);
oa.ObjectName = 0;
ZwCreateSection(&hSection, SECTION_ALL_ACCESS, &oa, 0,PAGE_EXECUTE, SEC_IMAGE, hFile);
ZwMapViewOfSection(hSection, NtCurrentProcess(), &BaseAddress, 0, 1000, 0, &size, (SECTION_INHERIT)1, MEM_TOP_DOWN, PAGE_READWRITE);
ZwClose(hFile);
hMod = BaseAddress;
dosheader = (IMAGE_DOS_HEADER *)hMod;
opthdr =(IMAGE_OPTIONAL_HEADER *) ((BYTE*)hMod+dosheader->e_lfanew+24);
pExportTable =(IMAGE_EXPORT_DIRECTORY*)((BYTE*) hMod + opthdr->DataDirectory[ IMAGE_DIRECTORY_ENTRY_EXPORT]. VirtualAddress);
arrayOfFunctionAddresses = (DWORD*)( (BYTE*)hMod + pExportTable->AddressOfFunctions);
arrayOfFunctionNames = (DWORD*)( (BYTE*)hMod + pExportTable->AddressOfNames);
arrayOfFunctionOrdinals = (WORD*)( (BYTE*)hMod + pExportTable->AddressOfNameOrdinals);
Base = pExportTable->Base;
RtlInitString(&ntFunctionNameSearch, lpFunctionName);
for(x = 0; x < pExportTable->NumberOfFunctions; x++) {
functionName = (char*)( (BYTE*)hMod + arrayOfFunctionNames[x]);
RtlInitString(&ntFunctionName, functionName);
functionOrdinal = arrayOfFunctionOrdinals[x] + Base - 1;
functionAddress = (DWORD)( (BYTE*)hMod + arrayOfFunctionAddresses[functionOrdinal]);
if (RtlCompareString(&ntFunctionName, &ntFunctionNameSearch, TRUE) == 0) {
ZwClose(hSection);
return functionAddress;
}
}
ZwClose(hSection);
return 0;
}
VOID IoTimeRoutine(
IN PDEVICE_OBJECT DeviceObject,
IN PVOID Context )
{
int cnt = 0;
DbgPrint("IoTimerRoutine() is Called!\n");
}
NTSTATUS
DispatchCreate(
IN PDEVICE_OBJECT DeviceObject,
IN PIRP Irp
)
{
NTSTATUS status = STATUS_SUCCESS;
Irp->IoStatus.Information = 0;
//dprintf("[KsBinSword] IRP_MJ_CREATE\n");
Irp->IoStatus.Status = status;
IoCompleteRequest(Irp, IO_NO_INCREMENT);
return status;
}
NTSTATUS
DispatchClose(
IN PDEVICE_OBJECT DeviceObject,
IN PIRP Irp
)
{
NTSTATUS status = STATUS_SUCCESS;
//DbgBreakPoint();
Irp->IoStatus.Information = 0;
//dprintf("[KsBinSword] IRP_MJ_CLOSE\n");
Irp->IoStatus.Status = status;
IoCompleteRequest(Irp, IO_NO_INCREMENT);
return status;
}
NTSTATUS
DispatchDeviceControl(
IN PDEVICE_OBJECT DeviceObject,
IN PIRP Irp
)
{
NTSTATUS status = STATUS_SUCCESS;
ULONG controlCode;
PIO_STACK_LOCATION irpStack;
HANDLE hEvent;
OBJECT_HANDLE_INFORMATION objHandleInfo;
ULONG outputLength, inputLength;
PVOID inputBuffer;
irpStack = IoGetCurrentIrpStackLocation(Irp);
outputLength = irpStack->Parameters.DeviceIoControl.OutputBufferLength;
inputLength=irpStack->Parameters.DeviceIoControl.InputBufferLength;
controlCode = irpStack->Parameters.DeviceIoControl.IoControlCode;
switch(controlCode)
{
case IO_PROTECT:
dwTargetProcessID = (HANDLE)irpStack->Parameters.DeviceIoControl.Type3InputBuffer;
break;
default:
break;
}
Irp->IoStatus.Status = STATUS_SUCCESS;
Irp->IoStatus.Information = 0;
IoCompleteRequest(Irp, IO_NO_INCREMENT);
return status;
}
// 驱动入口
NTSTATUS DriverEntry( IN PDRIVER_OBJECT DriverObject, PUNICODE_STRING RegistryPath )
{
NTSTATUS ntStatus = STATUS_SUCCESS;
PDEVICE_OBJECT Device;
UNICODE_STRING DeviceName, DeviceLink; //设备名,符号链接名
DbgPrint("[MyDriver] DriverEntry\n");
RtlInitUnicodeString(&DeviceName, L"\\Device\\MyDriver"); //初始化设备名
RtlInitUnicodeString(&DeviceLink, L"\\DosDevices\\MyDriver"); //初始化符号链接名
/* IoCreateDevice 生成设备对象 */
ntStatus = IoCreateDevice(DriverObject, //生成设备的驱动对象
0, //设备扩展区内存大小
&DeviceName, //设备名,\Device\MyDriver
FILE_DEVICE_UNKNOWN, //设备类型
0, //填写0即可
FALSE, //必须为FALSE
&Device); //设备对象指针返回到DeviceObject中
if (!NT_SUCCESS(ntStatus))
{
DbgPrint("[MyDriver] IoCreateDevice FALSE: %.8X\n", ntStatus);
return ntStatus; //生成失败就返回
}
else
DbgPrint("[MyDriver] IoCreateDevice SUCCESS\n");
/* IoCreateSymbolicLink 生成符号链接 */
ntStatus = IoCreateSymbolicLink(&DeviceLink, &DeviceName);
if (!NT_SUCCESS(ntStatus))
{
DbgPrint("[MyDriver] IoCreateSymbolicLink FALSE: %.8X\n", ntStatus);
IoDeleteDevice(Device); //删除设备
return ntStatus;
}
else
DbgPrint("[MyDriver] IoCreateSymbolicLink SUCCESS\n");
Device->Flags &= ~DO_DEVICE_INITIALIZING; //设备初始化完成标记
DriverObject->MajorFunction[IRP_MJ_CREATE] = DispatchCreate;
DriverObject->MajorFunction[IRP_MJ_CLOSE] = DispatchClose;
DriverObject->MajorFunction[IRP_MJ_DEVICE_CONTROL] = DispatchDeviceControl;
DriverObject->DriverUnload = OnUnload;
Hook(); //SSDT hook
return ntStatus;
}
// 驱动卸载
VOID OnUnload(IN PDRIVER_OBJECT DriverObject)
{
UNICODE_STRING dosDeviceName;
Unhook();
RtlInitUnicodeString(&dosDeviceName, L"\\DosDevices\\MyDriver");
IoDeleteSymbolicLink(&dosDeviceName);
if (DriverObject->DeviceObject != NULL)
{
IoDeleteDevice(DriverObject->DeviceObject); //删除设备
}
}
// 此处修改SSDT中的NtCreateFile服务地址
VOID Hook()
{
UNICODE_STRING dllName;
DWORD functionAddress;
DWORD NtOpenProcessAddress;
DWORD NtWriteVirtualMemoryAddress;
int position;
int NtOpenProcessposition;
int NtWriteVirtualMemoryposinion;
PDEVICE_OBJECT pDeviceObject = NULL;
RtlInitUnicodeString( &dllName, L"\\Device\\HarddiskVolume1\\Windows\\System32\\ntdll.dll" );
//获取NtReadVirtualMemory的服务号完毕!
functionAddress = GetDllFunctionAddress("NtReadVirtualMemory", &dllName);
NtOpenProcessAddress = GetDllFunctionAddress("NtOpenProcess", &dllName);
NtWriteVirtualMemoryAddress = GetDllFunctionAddress("NtWriteVirtualMemory", &dllName);
position = *((WORD*)( functionAddress + 1 ));
NtOpenProcessposition = *((WORD*)( NtOpenProcessAddress + 1 ));
NtWriteVirtualMemoryposinion = *((WORD*)( NtWriteVirtualMemoryAddress + 1 ));
pos_ReadVirtualMemory = position;
pos_NtOpenProcess = NtOpenProcessposition;
pos_NtWriteVirtualMemory = NtWriteVirtualMemoryposinion;
//>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>
OldNtReadVirtualMemory = (NTREADVIRTUALMEMORY) (*(((PServiceDescriptorTableEntry)KeServiceDescriptorTable)->ServiceTableBase + pos_ReadVirtualMemory)); //得到NtReadVirtualMemory函数的原始地址
OldNtOpenProcess = (ZWCREATEFILE) (*(((PServiceDescriptorTableEntry)KeServiceDescriptorTable)->ServiceTableBase + pos_NtOpenProcess));
OldNtWriteVitualMemory = (NTWRITEVIRTUALMEMORY) (*(((PServiceDescriptorTableEntry)KeServiceDescriptorTable)->ServiceTableBase + pos_NtWriteVirtualMemory));
DbgPrint( "Address of Real OldNtReadVirtualMemory: 0x%08X\n", OldNtReadVirtualMemory );
// 去掉内存保护
__asm
{
cli
mov eax, cr0
and eax, not 10000h
mov cr0, eax
}
(NTREADVIRTUALMEMORY) (*(((PServiceDescriptorTableEntry)KeServiceDescriptorTable)->ServiceTableBase + pos_ReadVirtualMemory)) = NewNtReadVirtualMemory;
(ZWCREATEFILE) (*(((PServiceDescriptorTableEntry)KeServiceDescriptorTable)->ServiceTableBase + pos_NtOpenProcess)) = NewNtOpenProcess;//SSDT HOOK NtReadVirtualMemory
(NTWRITEVIRTUALMEMORY) (*(((PServiceDescriptorTableEntry)KeServiceDescriptorTable)->ServiceTableBase + pos_NtWriteVirtualMemory)) = NewNtWriteVirtualMemory;
DbgPrint(" Address of NewNtReadVirtualMemory: 0x%08X\n", NewNtReadVirtualMemory );
// 恢复内存保护
__asm
{
mov eax, cr0
or eax, 10000h
mov cr0, eax
sti
}
}
//////////////////////////////////////////////////////
VOID Unhook()
{
__asm
{
cli
mov eax, cr0
and eax, not 10000h
mov cr0, eax
}
// 还原SSDT
(NTREADVIRTUALMEMORY) (*(((PServiceDescriptorTableEntry)KeServiceDescriptorTable)->ServiceTableBase + pos_ReadVirtualMemory)) = OldNtReadVirtualMemory;
(ZWCREATEFILE) (*(((PServiceDescriptorTableEntry)KeServiceDescriptorTable)->ServiceTableBase + pos_NtOpenProcess)) = OldNtOpenProcess;
(NTWRITEVIRTUALMEMORY) (*(((PServiceDescriptorTableEntry)KeServiceDescriptorTable)->ServiceTableBase + pos_NtWriteVirtualMemory)) = OldNtWriteVitualMemory;
__asm
{
mov eax, cr0
or eax, 10000h
mov cr0, eax
sti
}
DbgPrint("Unhook");
}
|
|
|
[已有邀请码]新手写的SSDT_HOOK例子.
要是有不是硬件编码的就好了正需要 |
|
|
[求助]微点竟然认为《看雪五周年精华》是病毒,而且每个还不一样。
非病毒。。。。。。。 |
操作理由
RANk
{{ user_info.golds == '' ? 0 : user_info.golds }}
雪币
{{ experience }}
课程经验
{{ score }}
学习收益
{{study_duration_fmt}}
学习时长
基本信息
荣誉称号:
{{ honorary_title }}
勋章
兑换勋章

证书
证书查询 >
能力值


