这是一个免费、公开的在线PDB解析接口交流群:878316370
接口地址(二选一)
67aK9s2c8@1M7q4)9K6b7g2)9J5c8W2)9J5c8X3#2K6k6r3I4Q4x3X3g2K6j5h3W2D9k6h3q4^5K9q4)9J5k6h3y4G2L8g2)9J5c8Y4m8S2M7Y4y4W2
712K9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6E0M7$3c8D9i4K6u0W2M7$3q4A6L8r3g2S2P5r3S2Q4x3X3g2U0L8$3#2Q4x3V1k6H3j5i4u0K6k6b7`.`.
接口限制:
- 只允许POST类型请求
- 一次请求只能查询1个文件
- 一次请求只能附带最多200条查询符号
——————————————————————————————————
这段介绍文本摘抄一下 @鬼才zxy 的文章(感谢!)。
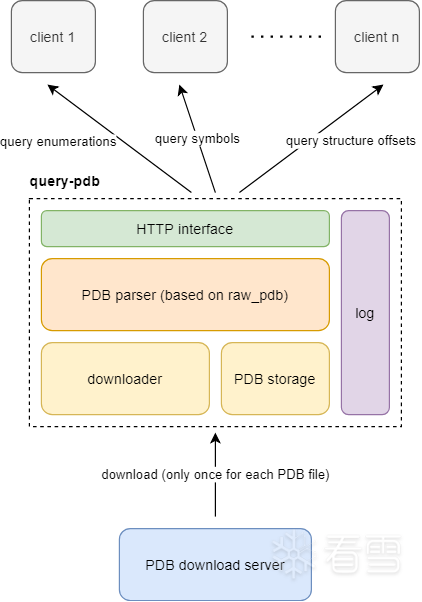
这是一个用于在服务端解析PDB文件的工具,客户端只需要向服务端发送要查询程序文件的版本信息和所需的全局变量、函数名称、结构体属性名,即可得到对应的偏移量。
——————————————————————————————————
使用方式简介(和query-pdb项目不同)
客户端发送如下请求:
{
"pdb": "ntdll.pdb",
"guid": "0AF9B92CB2856CFB0C54EC42CE8E3377",
"age": 1,
"symbols": [
"RtlInitUnicodeString",
"NtCreateFile",
"NtClose",
"totally_nonexistent_symbol"
],
"structs": {
"_PEB": [
"BeingDebugged",
"Ldr",
"ProcessParameters"
],
"_TEB": [
"ProcessEnvironmentBlock",
"ClientId"
],
"_KTHREAD": [
"Running",
"Alerted",
"KernelStackResident"
]
},
"enums": {
"_FILE_INFORMATION_CLASS": [
"FileDirectoryInformation",
"FileBasicInformation"
],
"_EVENT_TYPE": [
"NotificationEvent",
"SynchronizationEvent"
]
}
}
服务端响应如下:
{
"status": 0,
"message": "ok",
"data": {
"symbols": {
"NtClose": 644800,
"NtCreateFile": 647040,
"RtlInitUnicodeString": 244288,
"totally_nonexistent_symbol": -1
},
"structs": {
"_KTHREAD": {
"Alerted": {
"offset": 114,
"length": 2,
"bitfield_offset": 0,
"bitfield_length": 0
},
"KernelStackResident": {
"offset": 120,
"length": 1,
"bitfield_offset": 17,
"bitfield_length": 1
},
"Running": {
"offset": 113,
"length": 1,
"bitfield_offset": 0,
"bitfield_length": 0
}
},
"_PEB": {
"BeingDebugged": {
"offset": 2,
"length": 1,
"bitfield_offset": 0,
"bitfield_length": 0
},
"Ldr": {
"offset": 24,
"length": 8,
"bitfield_offset": 0,
"bitfield_length": 0
},
"ProcessParameters": {
"offset": 32,
"length": 8,
"bitfield_offset": 0,
"bitfield_length": 0
}
},
"_TEB": {
"ClientId": {
"offset": 64,
"length": 0,
"bitfield_offset": 0,
"bitfield_length": 0
},
"ProcessEnvironmentBlock": {
"offset": 96,
"length": 8,
"bitfield_offset": 0,
"bitfield_length": 0
}
}
},
"enums": {
"_EVENT_TYPE": {
"NotificationEvent": 0,
"SynchronizationEvent": 1
},
"_FILE_INFORMATION_CLASS": {
"FileBasicInformation": 4,
"FileDirectoryInformation": 1
}
}
}
}
如果需要结构体的完整定义,可以在structs类型查询时直接传空数组,接口将完整返回结构体所有成员及偏移+大小。(需要注意的是,采用的是无序返回,如果需要顺序需要自行按照offset来排列)
输入:
{
"pdb": "ntdll.pdb",
"guid": "0AF9B92CB2856CFB0C54EC42CE8E3377",
"age": 1,
"structs": {
"_CLIENT_ID": []
}
}
输出:
{
"status": 0,
"message": "ok",
"data": {
"structs": {
"_CLIENT_ID": {
"UniqueProcess": {
"offset": 0,
"length": 8,
"bitfield_offset": 0,
"bitfield_length": 0
},
"UniqueThread": {
"offset": 8,
"length": 8,
"bitfield_offset": 0,
"bitfield_length": 0
}
}
}
}
}
如果结构体不存在,则返回null
输入:
{
"pdb": "ntdll.pdb",
"guid": "0AF9B92CB2856CFB0C54EC42CE8E3377",
"age": 1,
"structs": {
"NONEXISTENT_STRUCT": []
}
}
输出:
{
"status": 0,
"message": "ok",
"data": {
"structs": {
"NONEXISTENT_STRUCT": null
}
}
}
有时会遇到C++函数定义,比如
?FindHotKey@@YAHPEAUtagTHREADINFO@@PEAUtagWND@@HIIPEAPEAUtagHOTKEY@@@Z
可以直接输入FindHotKey来匹配,接口会自动获取第一个匹配该函数名的结果来返回。也可以输入完整的C++定义
?FindHotKey@@YAHPEAUtagTHREADINFO@@PEAUtagWND@@HIIPEAPEAUtagHOTKEY@@@Z
来精确匹配,但是要注意不同版本间同一个函数的C++定义可能不同的。
服务端可能返回的状态码:| 0 | 成功 | data 中包含查询结果 || 1 | 方法不允许 | 未使用 POST 方法 || 2 | 读取失败 | 无法读取请求体 || 3 | JSON 无效 | JSON 格式错误或无法解析 || 4 | 缺少必填字段 | pdb 和 guid 为必填项,或含无效字符 || 5 | 无查询项 | symbols/structs/enums 至少提供一个且不为空 || 6 | 超过查询上限 | 查询项总数超过 200 || 7 | PDB 不可用 | PDB 回源失败 || 8 | 解析失败 | PDB 文件损坏或格式不支持 |
[培训]《冰与火的战歌:Windows内核攻防实战》!从零到实战,融合AI与Windows内核攻防全技术栈,打造具备自动化能力的内核开发高手。
最后于 2026-4-10 11:56
被Saileaxh编辑
,原因: